Critical infrastructure, industrial control (ICS) and supervisory control and data acquisition (SCADA) systems are under increasing threat of cyber attacks, according to a number of recent warnings from government agencies and private security researchers.
CERT-UA (Computer Emergency Response Team of Ukraine) reported a major attack on Ukrainian energy infrastructure last week. Researchers at ESET and Microsoft collaborated with CERT-UA to analyze the attacks and discovered evidence of a new variant of a known malware.
Sandworm, the advanced persistent threat (APT) group associated with the attack, attempted to disrupt high-voltage electrical substations, probably to destabilize critical energy infrastructures. The state-sponsored group used a new version of the malware “Industroyer,” dubbed “Industroyer2” (or “Industroyer reloaded”), that focuses on disk-wiping and data destruction.
They wrote advanced destructor scripts in Bash to erase traces of the attack and make the system unrecoverable. The ultimate objective was “decommissioning of several infrastructural elements,” according to CERT-UA.
While the CERT team declared that “the implementation of the malicious plan has so far been prevented,” the incident adds to the heightened state of alert that’s been in place since Russia’s imminent attack against Ukraine became apparent.
U.S. cybersecurity agencies yesterday encouraged U.S. critical infrastructure organizations to be on alert for similar threats against ICS/SCADA systems and to review recommended mitigations to prevent attacks.
Indeed, Sandworm’s tactics and procedures can be used to take down energy companies anywhere in the world, including U.S. and European facilities.
Also read: SANS Outlines Critical Infrastructure Security Steps as Russia, U.S. Trade Cyberthreats
Latest Sandworm Attack Against Ukraine
The Sandworm APT group has been behind a number of destructive attacks, especially against Ukraine’s power grid. For example:
- 2015: Sandworm cut the power grid in Ukraine for several hours with a malware called “BlackEnergy”
- Late 2016: Ukraine blamed Russian security services for thousands of cyber attacks against its infrastructure
- December 2016: Sandworm used Industroyer1 for a power outage that received some attention in Kyiv, Ukraine’s capital
Industroyer1 was specifically made to attack electric grids. ESET published a complete analysis in 2017 that stated: “Those behind the Win32/Industroyer malware have a deep knowledge and understanding of industrial control systems and, specifically, the industrial protocols used in electric power systems.”
High-profile and Multi-stage Attacks
According to ESET, “we don’t know how attackers compromised the initial victim nor how they moved from the IT network to the Industrial Control System (ICS) network,” but Sandworm is known for using LOTL (living-off-the-land techniques), job schedulers in Unix systems (cron jobs), and task schedulers in Windows.
Such lateral movements are often used to escalate privileges, for example, in Active Directory.
While we only know a few details about the malware and its capabilities, ESET discovered Sandworm used other destructive malware families like CaddyWiper, ORCSHRED, SOLOSHRED and AWFULSHRED. This multi-stage approach allows for deploying malware on various operating systems such as Windows, Linux, and Solaris:

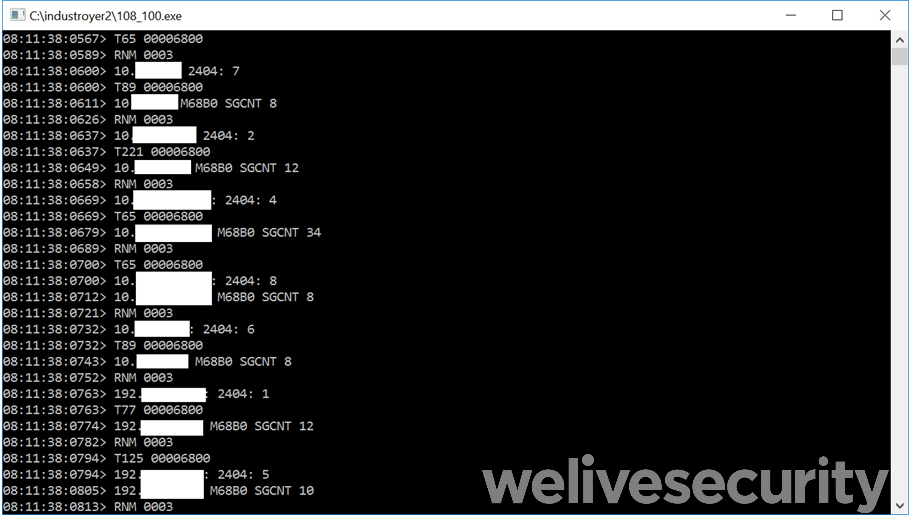
Industroyer2 is a Windows executable named 108_100.exe that implements very specific communication protocols designed for industrial equipment:
Also read: 10 Top Active Directory Security Tools
Industroyer’s New Capabilities
The researchers who analyzed the .exe file estimated it’s the same code base as the infamous Industroyer, hence the name Industroyer2.
However, the new malware contains hardcoded configurations in its body. On the one hand, it gives the hackers more capabilities. On the other hand, it needs to be recompiled for each new target, which might slow the attack significantly.
According to ESET, it’s not a major inconvenience, though, as “the Industroyer* malware family has only been deployed twice.”
The researchers have interpreted the weird error codes generated by the .exe in the prompt as an obfuscation attempt to jam forensic analysis.
Sandworm used Industroyer2 and other Linux/Solaris malware to schedule tasks and execute destructor scripts in parallel using sensitive commands such as shred. Hackers may have used that approach to minimize the time required to completely wipe disks, as such operations can take a while.
Researchers also noticed Industroyer2 was compiled two weeks before the attack at 16:10:00 UTC, the timestamp of the attack, so the attackers meticulously planned the operation.
The scripts were also designed to control ICS systems to prevent any rollback, and to ultimately self-destruct.
Also read: Best Digital Forensics Tools & Software
Defending Against Industroyer and ICS Threats
Defenders can inspect the sample available on VirusTotal for IoCs (indicators of compromise), and CERT-UA provided a detailed report that can help with evidence detection.
More generally, companies should protect critical infrastructure – and any infrastructure, really – against privilege escalations. There are effective ways to achieve that, such as:
- Least privilege (“zero trust“) approach and appropriate network segmentation
- Regular penetration tests and vulnerability assessments, especially with large Active Directory (global configurations, Group Policy Objects, Domain controllers, OUs, dormant accounts, etc.)
- Active endpoint monitoring (e.g., using EDR)
- Strong password policies and management
- Requiring 2FA (two-factor authentication) or MFA (multi-factor authentication) for all accounts
- Whitelisting third-party applications carefully and reviewing permissions
- Aggressive patch management
Organizations should prepare for post-exploitation techniques and lateral movements. In this case, the hackers presumably included in the Bash scripts lists stolen credentials they had prior the attack, which allowed iterating the operation over networks accessible through basic commands such as ip route or ifconfig -a.
These sophisticated hackers obviously can run multi-stage and high-profile attacks, wiping data in parallel and generating waves of destruction across different operating systems and equipment used in strategically important sectors.
However, this failed attempt might also encourage defenders somehow. While critical sectors such as energy still have to deal with bad practices and inadequate defenses in 2022, security awareness, forensic analysis, endpoint monitoring, threat hunting, threat emulation and other defensive techniques are sometimes rewarded.
While the incident could be the first step in a more massive disruptive campaign against Ukrainian infrastructures, it showed it’s still possible to learn from previous mistakes and mitigate further attacks, regardless of an adversary’s level of sophistication.
Read next: Best Incident Response Tools and Software







