Next-generation firewalls (NGFWs) are network security solutions that go beyond traditional port and protocol inspection by incorporating application-level inspection, intrusion prevention, and threat intelligence.
NGFWs improve network security by handling application-level threats and combining traditional features with more advanced decision-making capabilities. They’re a core cybersecurity product and a foundational security tool to help protect business networks.
We surveyed the enterprise firewall market. In our analysis, nine NGFW vendors stand out:
- Palo Alto: Best for large enterprises
- Fortinet: Best for overall value
- Check Point: Best for sandboxing
- Barracuda CloudGen Firewall: Best for hybrid cloud environments
- Cisco: Best for consistent network policies
- Forcepoint: Best for cluster management
- Huawei: Best for cloud service providers
- Juniper Networks: Best for SMEs with distributed networks
- Sophos XGS: Best for small security teams
Top NGFW Solutions Comparison
The following table helps you overview our top picks to find a next-gen firewall that aligns with your organization’s security objectives, considering a few features and starting prices.
| Scalability | Threat Detection and Prevention | Advanced Sandboxing | Pricing | |
|---|---|---|---|---|
| Palo Alto | ✔️ | ✔️ | ✔️ | Starts around $1,000 |
| Fortinet | ✔️ | ✔️ | ✔️ | Starts around $500 |
| Check Point | ✔️ | ✔️ | ✔️ | Starts around $3,000 |
| Barracuda CloudGen Firewall | ✔️ | ✔️ | Limited | Contact for quote |
| Cisco | ✔️ | ✔️ | ✔️ | Contact for quote |
| Forcepoint | ✔️ | ✔️ | ✔️ | 300 Series starts around $1,000 |
| Huawei | ✔️ | ✔️ | ✔️ | Contact for quote |
| Juniper Networks | ✔️ | ✔️ | Limited | Starts around $300-600 |
| Sophos XGS | Limited | ✔️ | Limited | Starts around $500 |

Palo Alto Networks – Best for Large Enterprises
Palo Alto Networks is a top network security vendor offering physical (PA-Series), virtual (VM-Series), and container (CN-Series) firewall solutions. If you have complicated architectures, Palo Alto improves visibility and control across scattered network segments.
Palo Alto’s firewall series is famous for its comprehensive features, albeit at a premium cost, and it’s ideal for protecting virtual, on-prem, and container environments. It’s most beneficial for larger businesses with strong IT and security teams and for organizations that can fully utilize its potential.
Pros
Cons
- Pricing: Firewalls range from about $1,000 annually for the PA-410 to around $200,000 for the high-end PA-7000 series.
- Contact for quote: Ask the Palo Alto sales team or your reseller for more detailed pricing.
- Calculator: Palo Alto offers a cloud NGFW pricing estimator to help teams estimate their overall cost.
- User-based policies: User-based firewall policies limit application access by integrating existing user repositories.
- Machine learning for threat detection: These network firewalls use machine learning to locate security threats and prevent intrusions.
- Container security: Palo Alto also has a container firewall that integrates with Kubernetes environments and helps secure CI/CD procedures.
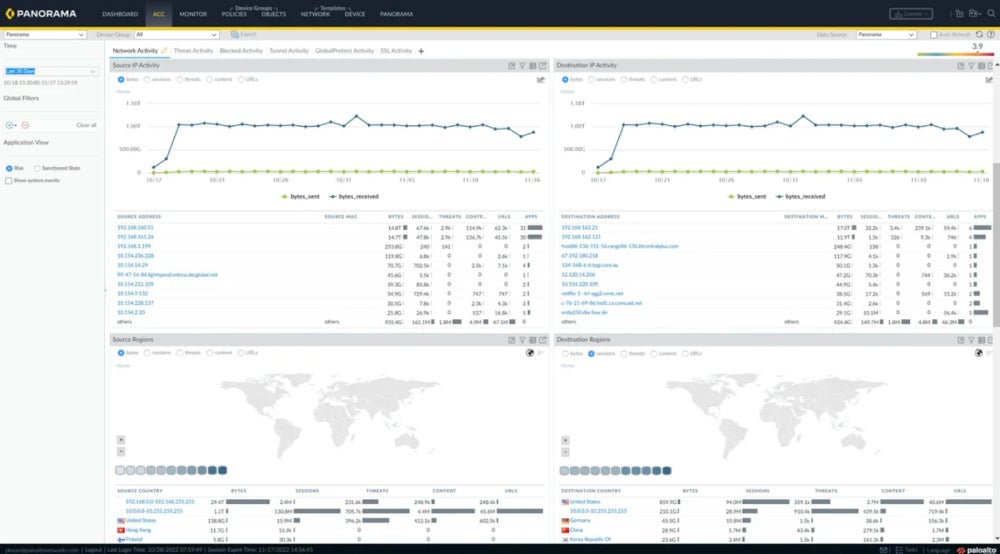
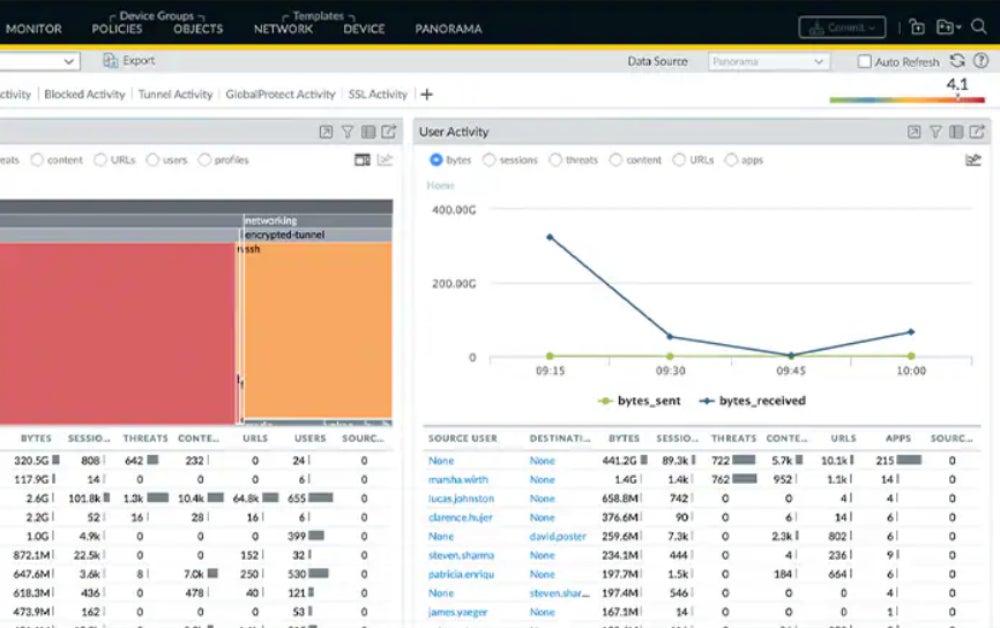
- Centralized management: Palo Alto firewalls use Panorama for central management, giving administrators a single point of contact to handle NGFWs.
Fortinet FortiGate – Best for the Value
Fortinet’s FortiGate next-gen firewalls provide powerful protection for home offices and large companies. FortiGate — which integrates SSL inspection, intrusion prevention, and web filtering — provides integrated security at a lower cost than Palo Alto. It’s an appealing option for smaller teams still needing enterprise-class protection — particularly businesses in high-security industries like finance and health care.
Pros
Cons
- Pricing range: Entry-level F series appliances start around $500, while the high-end FortiGate 7121F can cost close to $1 million with support and enterprise protection.
- Contact for quote: If you want a specific number for your business, contact Fortinet or your reseller.
- Free FortiGate-VM trial: 30 days.
- Security Processing Units (SPUs): SPUs and virtual SPUs (vSPUs) are used to speed up network security computing.
- FortiOS: Fortinet’s security-focused operating system offers federated firmware upgrades.
- Zero trust: FortiGate provides zero-trust capabilities for identifying and protecting suspicious users and devices.
- VPN tunneling: Scalable IPsec VPN tunneling helps your team secure a remote and distributed workforce.

Check Point – Best for Sandboxing
Check Point Software Technologies, an established firewall provider, provides a solid NGFW solution with Quantum Security Gateways. Check Point offers threat prevention solutions such as intrusion prevention systems (IPS), anti-bot, application control, and URL filtering to businesses of all sizes. Check Point’s cutting-edge technology is distinguished by its SandBlast Zero-Day Protection, which includes enhanced threat simulation and extraction. Consider Check Point if your company requires rigorous sandboxing for high-traffic applications.
Pros
Cons
- Pricing: Check Point Quantum Spark firewalls for small businesses start around $3,000-$4,000; Quantum Gateways can cost over $100,000.
- Contact for quote: Reach out to Check Point’s sales team or resellers for specific large business costs.
- Free trial: Contact for length.
- Compatibility with hybrid infrastructure: Check Point supports physical, virtual, cloud, and mobile segments.
- SandBlast zero-day protection: This product is notable for its extensive sandboxing features.
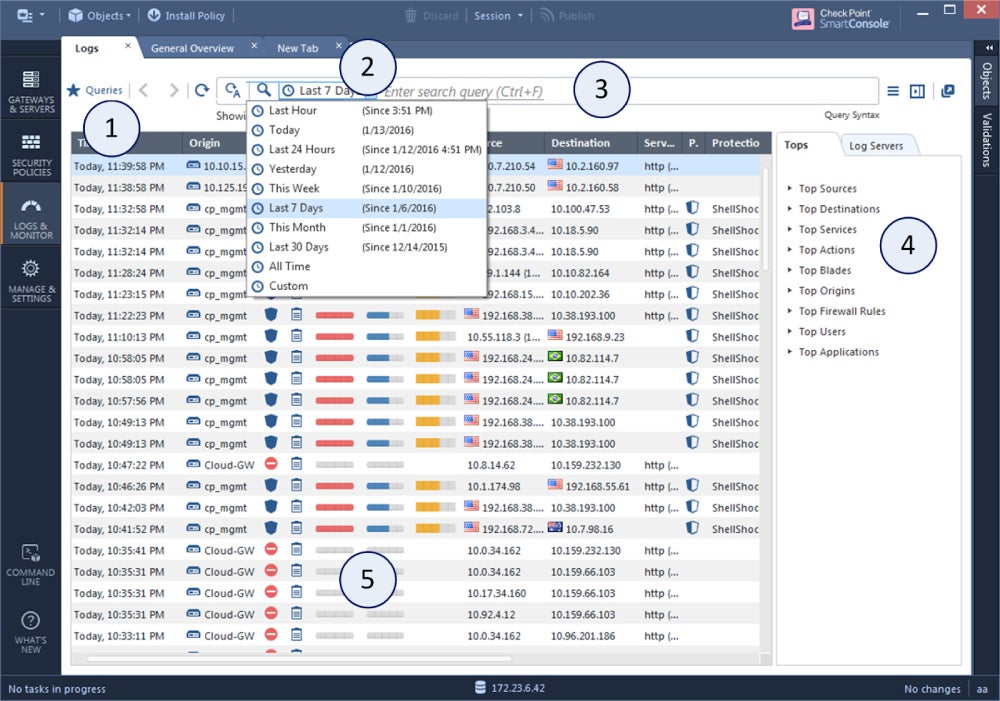
- Centralized management: Check Point provides policy configuration rollout and rollback options for security and IT managers.
- Maestro Orchestrator: Maestro is a network security solution for hyperscale firewall installations.

Barracuda CloudGen Firewall – Best for Hybrid Cloud Environments
The Barracuda CloudGen Firewall was designed with the hybrid era in mind: its F-Series is designed to preserve legacy hardware while meeting new challenges in hybrid network environments. Administrators have built-in SD-WAN, IDPS, and VPN capabilities.
Barracuda relies on multiple detection layers, including threat signatures and static code analysis, when signature-based defenses are increasingly unreliable. It’s a good choice for protecting hybrid cloud infrastructures, particularly if your business needs to monitor connections between multiple cloud environments.
Pros
Cons
- Pricing: Cloud costs are available through AWS Marketplace for small instance types.
- Contact for quote: Reach out to Barracuda’s sales team for direct enterprise costs.
- Free trial: 30 days through AWS.
- Advanced threat protection: Barracuda provides advanced threat protection through traffic management, SD-WAN, IDPS, and VPN.
- Stateful deep packet inspection: Stateful deep packet inspection prevents malformed packets and attacks.
- High availability: The Cloud Gen Firewall offers high availability through automatic load balancing and uplink options.
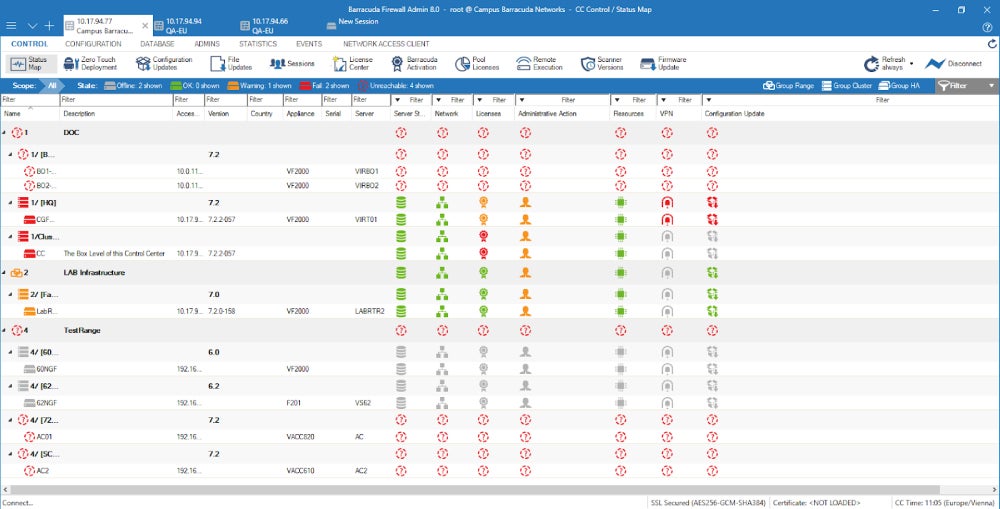
- Control over objects and configuration: Barracuda allows admins to manage objects, repositories, updates, privileges, and configuration.

Cisco – Best for Consistent Networking Policies
Cisco Secure Firewall provides real-time protection for workloads and networks in dynamic situations. Customers can migrate on-prem environments tothe cloud or multicloud using the Cisco Secure Workload integration. Cisco is an excellent solution for enterprises that need comprehensive security for all enterprise applications. It’s built for large-scale business policy enforcement in organizations with diverse application requirements.
Pros
Cons
- Pricing: Cloud pricing is available from AWS.
- Contact for quote: Fill out a form to speak with a Cisco representative about purchasing Secure Firewall.
- Free trial: 30 days through AWS; contact Cisco for length of trial through the vendor.
- Dynamic policy support: Cisco Secure Firewall supports tag-based policies and attributes.
- Cloud Native firewall: This Secure Firewall option, orchestrated by Kubernetes, is developer-friendly, extremely elastic, and cloud-native.
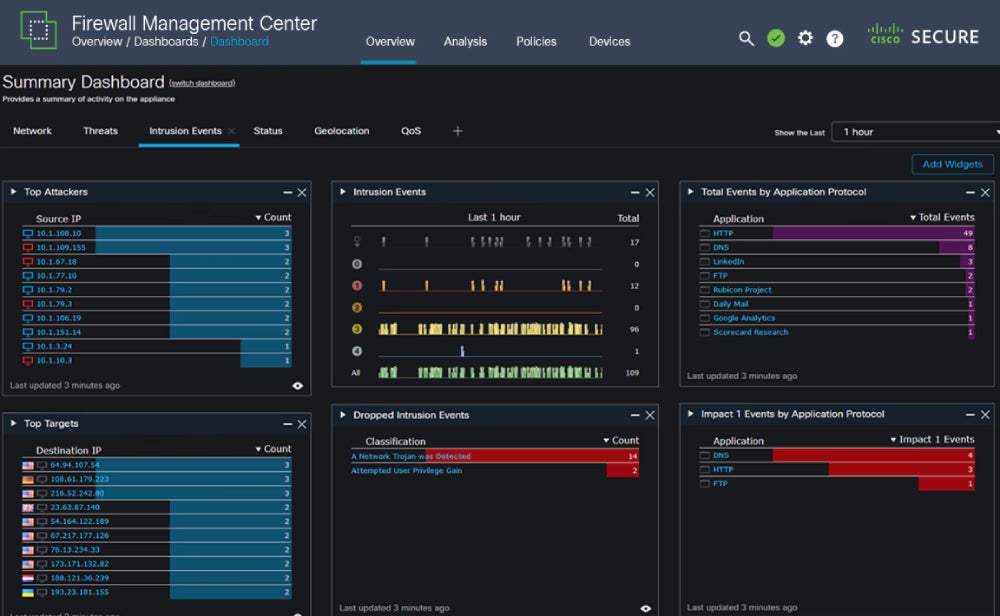
- Log management: Secure Firewall offers log management, security incidents, and behavioral analysis.
- Threat intelligence: The Cisco Talos Intelligence Group provides security teams with rapid and actionable threat intelligence.

Forcepoint – Best for Cluster Management
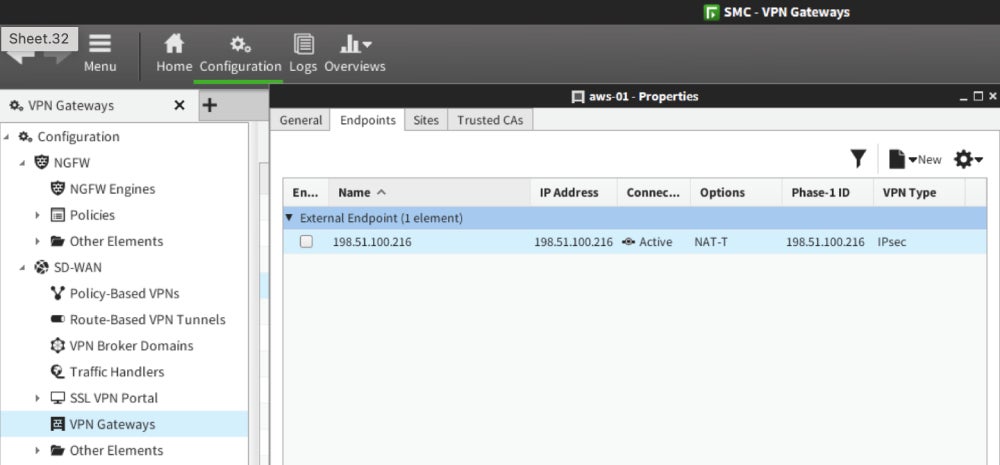
Forcepoint’s NGFW provides high availability, scalability, and security by combining an enterprise SD-WAN with industry-tested security technologies. Its powerful cluster management features offer the most significant benefit to large businesses. Forcepoint is a fantastic option for businesses looking for a full-featured network security platform that may be less expensive than other market leaders.
Pros
Cons
- Pricing: Appliances in Forcepoint’s 300 Series start around $1,000-8,000.
- Contact for quote: Fill out Forcepoint’s pricing form for enterprise-specific prices.
- Free demo: Contact to schedule.
- High-availability clustering: Forcepoint’s NGFW has high-availability clustering for device, VPN connection, and SD-WAN networks.
- Internal integrations: The NGFW integrates with Forcepoint’s CASB, online security, and anti-malware sandboxing solutions.
- Application-level traffic protection: Forcepoint’s app-focused security helps secure traffic to enterprise applications.
- Smooth policy upgrades: Forcepoint pushes policy updates and software upgrades to its firewall clusters while working to prevent downtime.
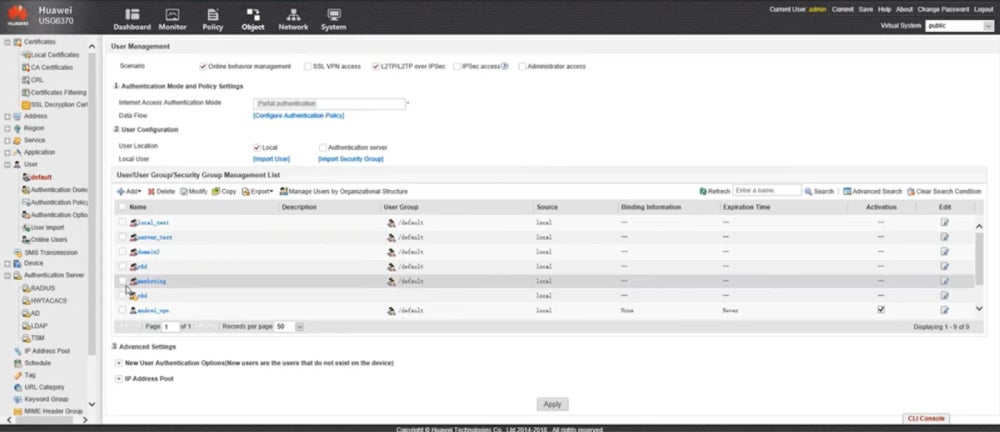
Huawei – Best for Cloud Service Providers
Huawei’s Unified Security Gateway Series suits modern data centers and large companies best. The USG6700E Series AI Firewall streamlines service deployment and policy modifications. The USG9500 Series Terabit-Level NGFW is designed for large data centers and cloud services. Huawei is a strong option for large-scale service providers and data center operations looking for consistent network security.
Pros
Cons
- Contact for quote: Fill out the form on Huawei’s website to contact a sales representative.
- Reseller options: Some appliances may also be available from resellers; check for legitimacy.
- Integration with cloud and local sandboxes: Huawei works with a local or cloud sandbox to detect, analyze, and prevent zero-day attacks.
- Policy-based routing: Through routing policies, Huawei manages bandwidth per user and IP address.
- Deception system: The firewalls include deception technology to help teams detect threat actor scans with lowered risk.
- Chip-level pattern matching: This technique improves antivirus and IPSec performance.

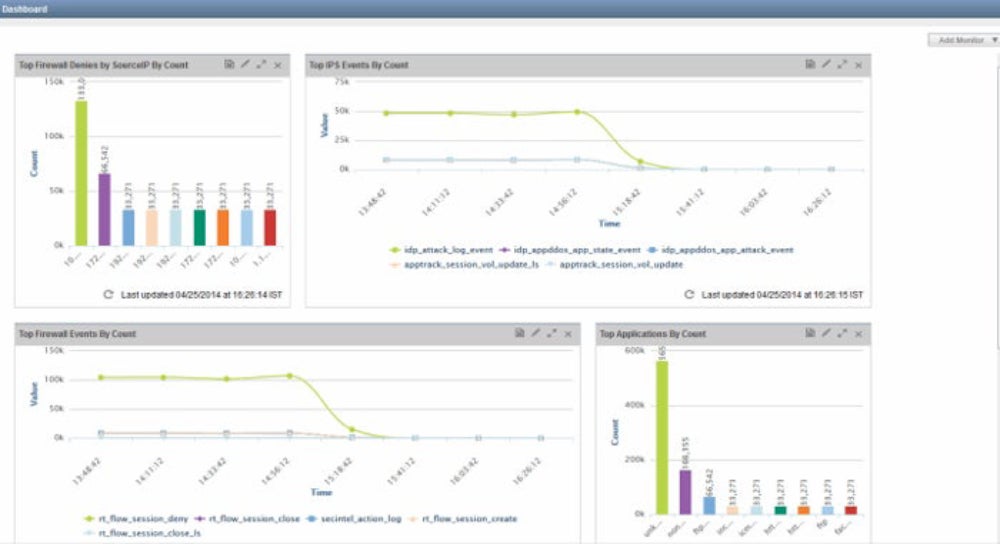
Juniper Networks – Best for SMEs with Distributed Networks
Juniper Networks offers firewalls powered by Juniper’s own operating system, Junos. The SRX Series Gateways provide centralized policy control for scalable operations, safeguarding network edges, data centers, virtual environments (vSRX), and containers (cSRX). Juniper is an excellent choice for smaller enterprises that use virtual environments and containers, particularly those looking for a firewall with SD-WAN features.
Pros
Cons
- Pricing: The SRX 300 model for small businesses and branch offices starts between $300-$600.
- Virtual pricing: AWS offers vSRX cloud usage costs.
- Contact for quote: Reach out to Juniper Networks’ sales team.
- Free trial of virtual firewall (vSRX): 60 days.
- AppSecure: Juniper uses AppSecure to identify, secure, and manage application and user traffic.
- Intrusion prevention: Juniper’s intrusion prevention system allows you to inspect SSL traffic and create your own IDP policies.
- SDN and policy-based routing: SRX performs SDN and policy-based routing across wired, wireless, and wide-area networks.
- Microsegmentation: Juniper’s NGFW services include network segmentation for improved protection.

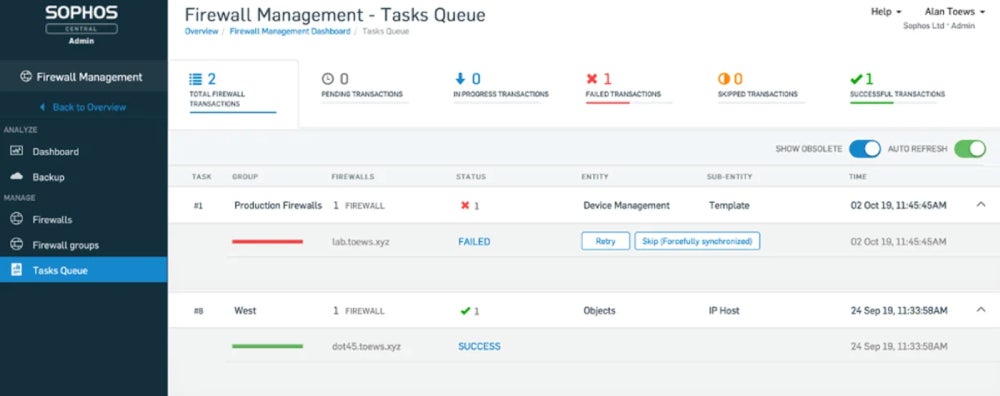
Sophos XGS – Best for Small Security Teams
Sophos’ XGS Series, intended for complicated network segments, provides current data protection for SaaS, SD-WAN, and cloud traffic. Data from SophosLabs is sent to the XGS Firewalls, which use global threat information for automated detection and response. The XGS firewall series is a strong choice for security teams that are less experienced in configuration and policy management. It provides a feature-rich yet understandable interface for IT and security staff.
Pros
Cons
- Pricing: Starts between $500-$700 for the XGS 87 and around $31,000 for the XGS 6500.
- Contact for quote: Fill out Sophos’ pricing form for a custom estimate.
- Free trial: Contact for length.
- Deep packet inspection: The XGS Series offers DPI, intrusion prevention, and proxy-based scanning.
- Threat-intelligent traffic selection: Sophos supports modern cipher suites and covers all ports.
- Deep learning and dynamic sandboxing: Sophos has a sandboxing option and deep learning for analyzing static files.
- Machine learning for threat identification: The XGS series uses machine learning models to identify advanced and unknown threats.
Key Features of NGFW Solutions
When considering NGFW vendors and products, look for features such as identity awareness, central firewall management, stateful inspection, deep packet inspection, and intrusion prevention features.
Application & Identity Awareness
A critical difference between traditional firewalls and NGFWs is the latter’s ability to offer application and user identity protection. Whereas traditional firewalls rely on standard application ports, NGFWs can identify, allow, block, and limit applications regardless of port or protocol. Recognizing identity improves NGFWs’ overall control by helping admins apply firewall rules more granularly to groups and users.
Centralized Management & Visibility
To actively manage a network’s defenses, administrators need an accessible and configurable dashboard to view and manage security systems like NGFWs. Most NGFWs contain log analysis, policy management, and a management dashboard. This dashboard allows admins to track security health, analyze traffic patterns, and set or create firewall rules.
Stateful Inspection
Traditional firewalls use stateful inspection, also known as dynamic packet filtering, to inspect traffic up to network Layer-4. NGFWs are built to track Layers 2-7. This advancement allows NGFWs to perform the same stateful inspection duties of a traditional firewall — distinguishing between safe and unsafe packets. The extension of dynamic packet filtering to the application layer is valuable as your critical business resources move toward the network edge.
Deep Packet Inspection
Deep packet inspection (DPI) goes a step further in inspecting traffic. Stateful inspection monitors all traffic and just the packet headers, while DPI inspects the data and header of transmitted packets. Executed at the application layer, DPI can locate, categorize, block, or reroute packets with problematic code or data payloads not detected in a stateful inspection.
Integrated Intrusion Prevention (IPS)
Intrusion prevention systems (IPS) once sat adjacent to the firewall, playing defender against new threats outside the protected network. While traditional firewalls manage traffic flows based on network information, IPS devices inspect, alert, and even actively rid the network of malware and intruders.
As cybersecurity products have evolved, NGFW products have gradually integrated IPS technology. While the distinction is growing narrower, the question for buyers becomes whether the IPS technology included with their NGFW is good enough to forego a standalone IPS product. Critically, IPS can prevent attacks like DDoS, brute force, and known vulnerabilities.
Frequently Asked Questions (FAQs)
What Firewall Is Deployed the Most?
Determining the most deployed firewall varies based on organizational needs. However, large organizations widely use firewall giants such as Palo Alto Networks, Fortinet, and Cisco. Your unique requirements, preferences, and the company’s size determine which firewalls would be a good fit.
How Many Firewalls Should You Have?
The number of firewalls your organization needs depends on its network architecture, security requirements, and segmentation strategy. Businesses typically deploy numerous firewalls for tiered protection. This could comprise perimeter firewalls, internal firewalls for network zone segmentation, and application-specific firewalls. The goal is to develop a defense-in-depth plan suited to your business’s specific security requirements.
Read more about the best practices to implement when deploying and using firewalls.
Which Is Better: UTM or NGFW?
If you’re debating between a unified threat management (UTM) solution or an NGFW, the answer mainly depends on your business size and needs: SMBs and startups often find a UTM sufficient. At the same time, larger teams may benefit more from an NGFW. UTMs have a lot of similar network protection features, but NGFWs are typically more comprehensive. Check out UTM features and see if those are sufficient or if you need more enterprise-focused protection.
Bottom Line: Secure Your Network with Next-Generation Firewall Solutions
Choosing an NGFW requires thoroughly understanding your company’s budget, requirements, and staff expertise. Once you’ve determined all these items, generate a shortlist with your most critical needs. While setting up next-generation firewalls is challenging, their increased protection often justifies the expense. Adequate training for IT and security teams is vital for improving corporate security and investing in overall team knowledge and future success.
Looking for another comprehensive network security solution? Read our list of best unified threat management tools next.
This article was updated in December 2023 by Maine Basan and in February 2025 by Jenna Phipps.