Cybersecurity training for employees is essential in 2025, as evolving threats require an informed and vigilant workforce to protect sensitive information. Modern cybersecurity training programs equip teams with the knowledge to identify and prevent potential security breaches using engaging videos, interactive quizzes, and real-world phishing simulations.
To help you choose the best option for your organization, we’ve reviewed the top cybersecurity training programs, highlighting key features, benefits, and potential drawbacks for each.
Here are the top six cybersecurity training programs:
- KnowBe4: Best overall security training product
- ESET: Best for endpoint security and threat prevention
- Proofpoint: Best for small and midsize businesses
- Ninjio: Best option for employee engagement
- Infosec IQ: Best vendor for customer service
- SANS Institute: Best for skilled teams and IT pros
Featured PartnersFeatured Partners: Cybersecurity Training Software
eSecurity Planet may receive a commission from merchants for referrals from this website
Top Cybersecurity Training Products Compared
The following chart briefly overviews our six products’ feature availability. While some vendors don’t offer full free trials for their products, they may offer a few free phishing episodes or another type of demo, so consider those if you’re reviewing the product, too.
| Phishing Templates | Training Videos | Over 20 Languages Supported | Free Trial | |
|---|---|---|---|---|
| KnowBe4 | ✔️ | ✔️ | ✔️ | ❌ |
| ESET | ✔️ | ✔️ | ✔️ | ✔️ |
| Proofpoint | ✔️ | ✔️ | ❌ | ❌ |
| Ninjio | ✔️ | ✔️ | ✔️ | ✔️ |
| Infosec IQ | ✔️ | ✔️ | ❌ | ✔️ |
| SANS Institute | ✔️ | ✔️ | ✔️ | ✔️ |

KnowBe4: Best Overall Security Training Product
KnowBe4 is one of the most popular training products in the field, offering baseline testing to find out how phish-prone an organization is and a huge library of engaging network security awareness training content. Other features include automated training campaigns, simulated phishing attacks, and a tool for monitoring improvements in user behavior.
KnowBe4 is particularly good for midsize to large businesses that want reasonably priced, engaging training. Its laser focus on training and transparent pricing contribute to its spot on our list.
Pros
Cons
- Interactive browser-based training: Employee training is web-hosted.
- Skills-based and culture surveys: These focus on improving the overall team security culture.
- Phishing templates and landing pages: KnowBe4 makes these customizable.
- AI-driven training recommendations: Individual users know what they need to work on.
- USB-drive behavior testing: These tests analyze employees’ behavior toward unfamiliar storage devices.

ESET: Best for Endpoint Security & Threat Prevention
ESET is a well-established cybersecurity company known for its robust endpoint protection solutions. Offering a comprehensive suite of cybersecurity products, ESET focuses on providing businesses with proactive protection against a wide range of cyber threats. Their training programs are designed to help employees recognize and mitigate potential risks, enhancing overall organizational security.
Pros
Cons
ESET offers both free and paid training options to suit various organizational needs. The free training provides essential cybersecurity awareness content, while the paid training is $250 for 10 users annually, offering more comprehensive modules and features. For detailed pricing information and to explore the available options, it is recommended to contact ESET directly or visit their website.
- Interactive Learning Modules: ESET offers engaging training with videos, quizzes, and interactive scenarios to boost learning retention.
- Phishing Simulation: The platform features phishing simulation tools that help organizations test employees’ responses to simulated attacks, reinforcing real-world skills.
- Reporting and Analytics: ESET’s reporting capabilities enable administrators to track employee progress, identify knowledge gaps, and create compliance reports.
- Multi-Language Support: ESET’s training modules are available in multiple languages, making it accessible to diverse workforces.
- Regular Content Updates: The training content is regularly updated to address the latest threats and best practices, keeping employees informed about current risks.

Proofpoint: Best for Small & Midsize Businesses
Proofpoint offers a cybersecurity awareness training program with concise, digestible modules to create lasting improvements in user habits. Seamlessly integrating with other Proofpoint solutions, it’s an excellent choice for SMBs, particularly those new to a structured training approach.
While it may not be as comprehensive as some options for larger enterprises, Proofpoint provides a practical, accessible solution for small to mid-sized organizations looking to strengthen their security awareness.
Pros
Cons
Pricing for Proofpoint’s training is included as part of its Proofpoint Essentials service. Subscribers to that service can access its security awareness training. Proofpoint also offers a free trial for the training service. The company doesn’t list pricing info on its website, so interested buyers must contact the sales team directly.
- Consistent training around the globe: This includes multi-language support.
- Employee progress tracking: Dynamic reporting helps admins clearly view users’ progress.
- Integration with target attack protection (TAP): TAP helps prevent ransomware by detecting and blocking advanced threats.
- Detection for very attacked people (VAPs): This feature provides more detail on the types of threats your organization engages in, including the business’s top link clickers.
- ThreatSim phishing simulations: Help your team understand its susceptibility to various phishing attacks.

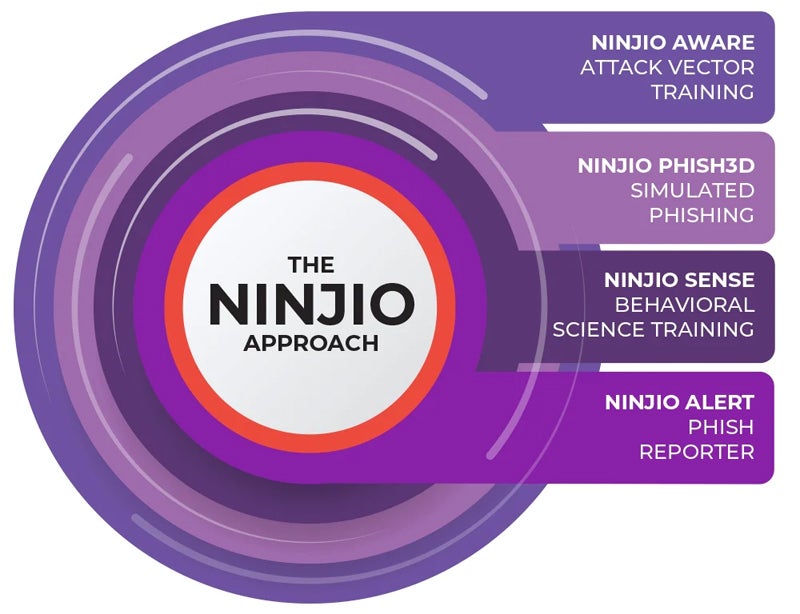
NINJIO: Best for Employee Engagement
NINJIO offers a highly engaging training solution through short, animated videos, each lasting 3–4 minutes, with fresh content released monthly. The videos are based on real-life security breaches, presenting relatable scenarios that teach employees how to respond effectively. A gamified leaderboard boosts engagement by fostering friendly competition among employees.
With consistently positive user reviews, NINJIO is a top choice for driving employee engagement in cybersecurity training.
Pros
Cons
NINJIO doesn’t offer pricing information publicly. If you’re interested in buying, contact Ninjio for pricing info or look at the monthly subscription plan for SMBs. Pricing is per user, per month, with an annual commitment.
- Hollywood-style storytelling: The brief videos and voice acting are designed for better connection and engagement.
- Real-life examples: NINJIO uses phishing examples that have actually happened.
- New training episodes: NINJIO releases new content each month.
- Private hosting portal available: This includes your business’s own branding and domain name.
- Interactive quizzes: Quizzes are available in multiple languages.

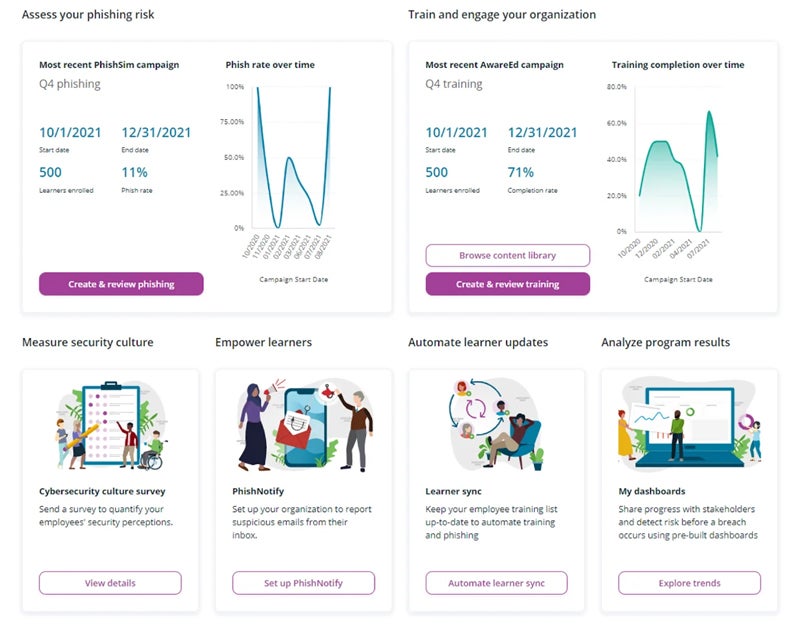
Infosec IQ: Best for Customer Service
Infosec IQ provides a flexible cybersecurity training solution with pre-built programs and customizable options from a vast library of industry- and role-specific modules. This allows companies to tailor training to focus on relevant topics for their employees.
Known for its responsive customer service, Infosec IQ is highly regarded for its strong sales and technical support. It is a top choice for businesses seeking comprehensive and adaptable training solutions.
Pros
Cons
Infosec IQ’s security awareness training has three tiers: Standard, Enterprise, and InfoSec IQ + Skills (for security, IT, and dev teams). Prices on these three tiers are not publicly available, so interested organizations must fill out a form on Infosec IQ’s website to receive pricing details.
- Phishing templates: New ones are added weekly based on new threat data.
- Phishing simulator: Infosec provides instant feedback when a user takes unsafe actions.
- Brief training videos: Videos are designed to improve employee learning retention.
- Single sign-on integrations: Supported products include Active Directory and Okta.
- Customizable reporting: Dashboards can be filtered by department and learning group.

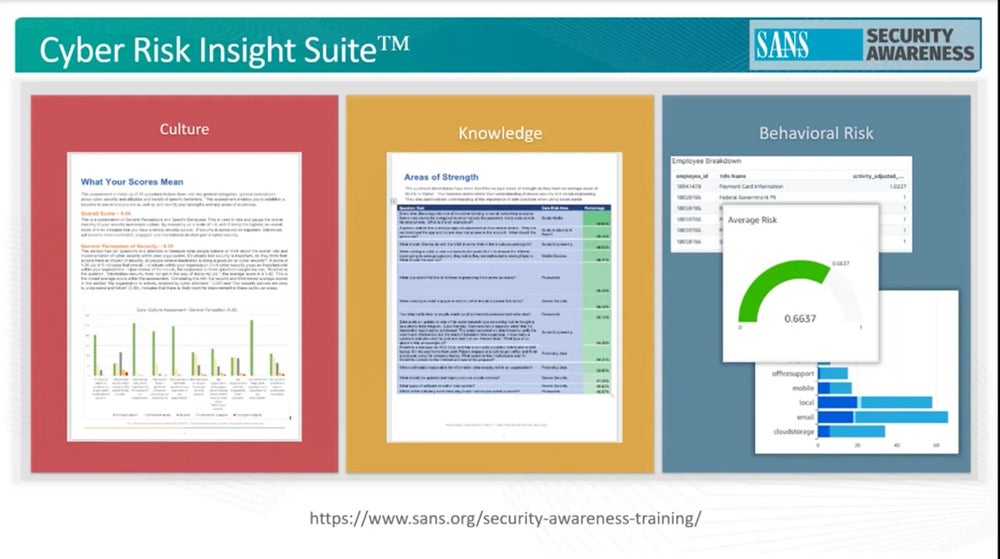
SANS Institute: Best for Advanced Teams and IT and Security Professionals
The SANS Technology Institute provides business employee training alongside full undergraduate and graduate cybersecurity programs. Its computer-based training adapts to diverse learning styles and corporate needs, featuring engaging, challenging games to enhance retention.
With additional courses available for advanced security professionals, SANS is ideal for teams seeking in-depth cybersecurity expertise and growth opportunities. It is a top choice for companies with advanced or ambitious cybersecurity goals.
Pros
Cons
SANS Technology Institute doesn’t make pricing information publicly available. Contact the Institute to learn more about its multiple training products, including the Phishing platform, EndUser training, PCI-DSS compliance training, and Cyber Risk Insight Suite for company assessments.
- Custom awareness programs: These are good for teams in specific industries that need specific cybersecurity training.
- Knowledge assessment: Avoid wasting time on skills your team has already mastered.
- Automated test delivery: Tests are scheduled over 12 months.
- Automated remedial training: Training is assigned to users when they need additional work on a simulation.
- More than 50 training modules: Six different tracks are available.
Essential Features of Effective Cybersecurity Training Tools
To build a resilient and security-aware workforce, choosing a cybersecurity training tool with features that effectively engage employees and adapt to evolving threats is essential. Here are the top five features that make a cybersecurity training solution truly effective:
Phishing Simulations
Phishing simulations are critical for hands-on learning, allowing employees to practice recognizing and responding to phishing attempts in a safe environment. These tools send simulated phishing emails to test employees’ awareness and response. By replicating real-world scenarios, phishing simulations help users become familiar with phishing tactics, preparing them to identify and avoid actual threats.
Engaging & Interactive Content
High-quality training tools use engaging, interactive content, including videos, quizzes, and real-world scenarios, to make learning enjoyable and memorable. Cybersecurity can be complex, and breaking down the content into short, engaging modules keeps employees’ attention and boosts retention. Quizzes and scenarios provide practical application, reinforcing lessons in a meaningful way.
Customizable Learning Paths
Every organization has unique security needs, and a customizable learning path feature allows training to be tailored accordingly. This feature allows administrators to assign different training modules based on employees’ roles, risk levels, or existing knowledge. This targeted approach ensures that employees receive relevant training, increasing the program’s effectiveness and minimizing unnecessary content.
Regular Content Updates
The cybersecurity landscape is constantly changing, with new threats emerging regularly. Training tools with continuously updated content ensure employees stay informed about the latest threats and best practices. Regular updates help keep training relevant, covering areas like ransomware, phishing, and social engineering as they evolve, which is essential for maintaining an informed and vigilant workforce.
Reporting & Analytics
Robust reporting and analytics provide valuable insights into training effectiveness, enabling administrators to monitor individual and team progress, identify knowledge gaps, and measure overall program success. This feature helps tailor the training experience to employees’ needs, ensuring continuous improvement in security awareness and reinforcing areas where more focus may be needed.
How to Choose a Cybersecurity Training Product
If your business is considering purchasing a security awareness training product, look at each solution’s main features, ease of management, pricing, support, other products, and the training content your team needs.
Review Their Core Features
Before shopping for a product, create a shortlist of 3–5 key features your team needs for your training course. The other features should be nice, but every product you consider should have those few core capabilities. Those might include short animated videos, a specific type of report, or quizzes after each training module. While your list shouldn’t be unattainable, make sure you’re keeping your team’s main needs front of mind.
Consider Ease of Management
How is user management handled? Is it a manual process? Assess the ease of administration of whatever vendor you choose. If there are multiple systems or consoles, ask about the degree of integration between those systems. It’s always best to ask as many questions as possible before committing to a product.
Consider Cost
Find out how many capabilities come with the subscription level, including what functionality is included versus required managed services and extra fees. Balancing budget with quality is always a fine line, but make sure you’re investing in a product that will last your business years, not a low-quality one that fits your budget but not a growing team.
Determine Customer Support Needs
Some teams may not need detailed reporting or 24/7 customer support, but make sure you communicate with the vendor and know your business’s expectations before making a decision. Additionally, look at existing customers’ reviews — while these don’t give the entire picture, they help your team spot potential weaknesses and gauge whether you’re willing to live with them.
Keep Integrations in Mind
While your business may only be looking for a training product, it could be beneficial if the training solution integrates with your existing security solutions. Some vendors, like Proofpoint, offer multiple security products. Others, like KnowBe4, offer only awareness training. Decide whether you want your cybersecurity training to integrate with other security products in your infrastructure before purchasing.
Know Your Content Expectations
Look at the volume and quality of training content provided for each product. How important is it to your organization to have an ongoing campaign with fresh content? A small training library means stale and infrequent training. Content needs to be engaging, so try it yourself to get a feel for the vendor’s approach.
Consider asking multiple employees what they consider engaging in training courses. You’ll get a more comprehensive picture if you poll more team members.
Frequently Asked Questions (FAQs)
Why Do We Need to Train Our Employees?
Employees and individual contributors are among the weakest links in enterprise cybersecurity. They’re susceptible to malicious email links, spoofed phone calls, and unsecured websites. Some of those scenarios happen because employees have never been taught to spot fakes, and recent cyberattack tactics can be highly sophisticated.
A simple employee mistake could cost your business thousands or millions of dollars. When done consistently and engagingly, cybersecurity training reduces these risks.
What Should Cybersecurity Training Include?
A thorough training program should include comprehensive coverage of common phishing trends, including email, text, and phone phishing. However, ensure you also cover strong password policies and password protection. What are a few basic security health items that your team can cover? Discussing those items with new and tenured employees is also important.
How Can You Promote Cybersecurity Awareness in the Workplace?
Developing a security culture in your organization won’t just happen by assigning training videos to your employees. Your leaders have to promote open communication, too. Talk with your team regularly, ensuring frank security conversations are commonplace. The more your employees expect these discussions, the less likely they’ll be to break your business’s security restrictions blatantly.
Bottom Line: Choosing the Best Employee Cybersecurity Training Service
Cybersecurity training solutions have become increasingly advanced in recent years, empowering businesses to prevent a single phishing email or malicious link from escalating into a major security breach. To find the right solution, create a shortlist of promising products and use demos or free trials to assess the user experience firsthand.
Once you choose a training solution, it’s crucial to implement it immediately. New employees are vulnerable to phishing and credential theft from day one, so early and consistent training is key to strengthening your organization’s security posture.
While training and technology are great tools, they are not enough to protect your team. Read more about the importance of a business cybersecurity culture next.