Identity and access management (IAM) once helped IT departments in large enterprises manage employees in Microsoft Active Directory. In a modern IT environment, IAM plays a far more critical role in authorizing geographically dispersed workforces as they connect to internal resources, cloud resources, and especially software-as-a-service (SaaS) applications.
IT teams can no longer easily manage individual user rights and permissions with the rapid increase in SaaS applications and remote work. IAM offloads the burden of individual access management and automates the onboarding and offboarding processes as well.
Choosing the best software for IAM needs becomes even more complicated as developers, customers, and even access from other applications all enter the picture. Some organizations require a dedicated IAM solution while others may only need an IAM tool within a portfolio of other security products.We’ll review our picks for the top IAM solutions, their features, pricing, use cases, pros and cons, and more.
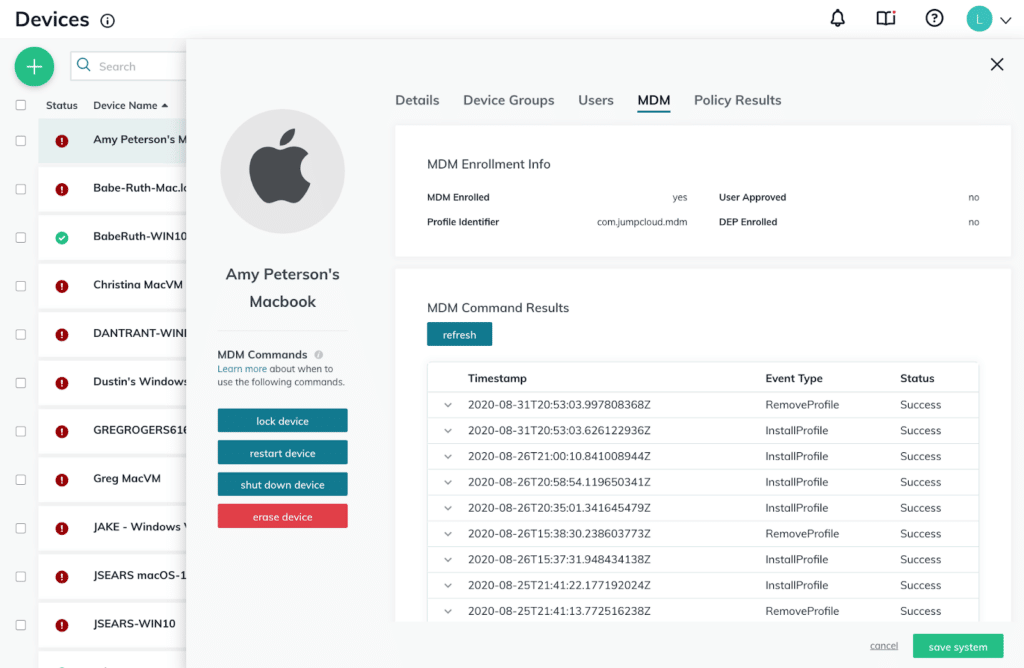
- JumpCloud: Best overall
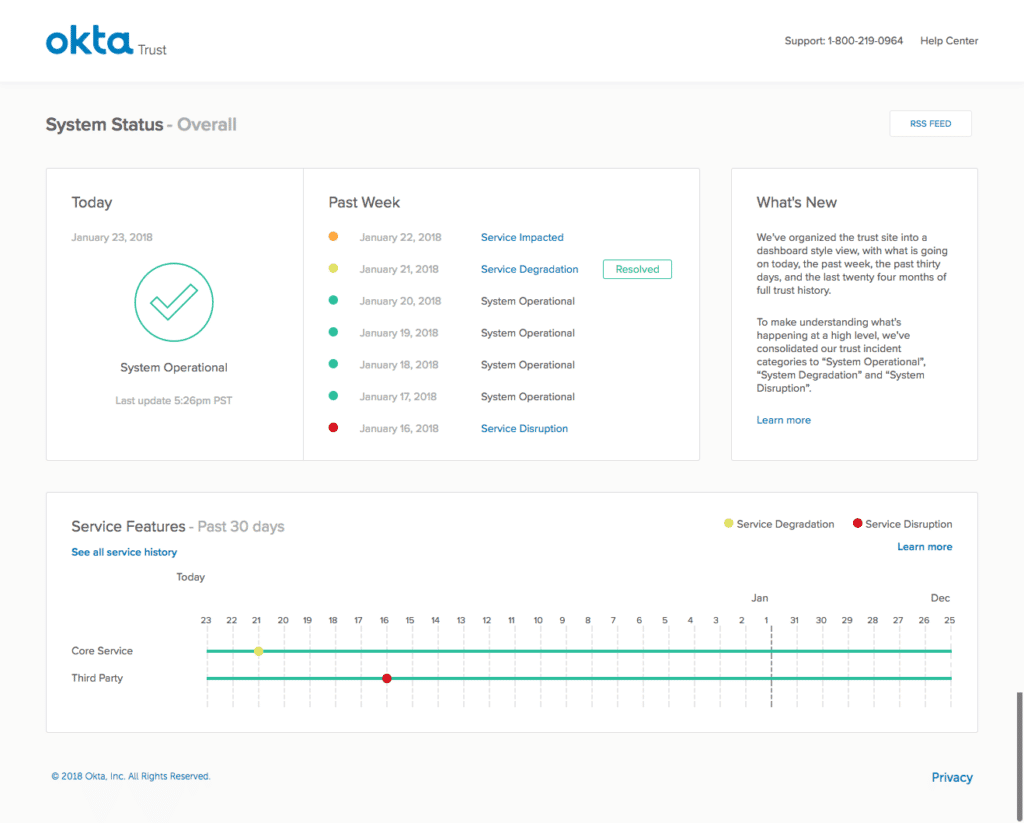
- Okta Workforce Identity: Best for large enterprises
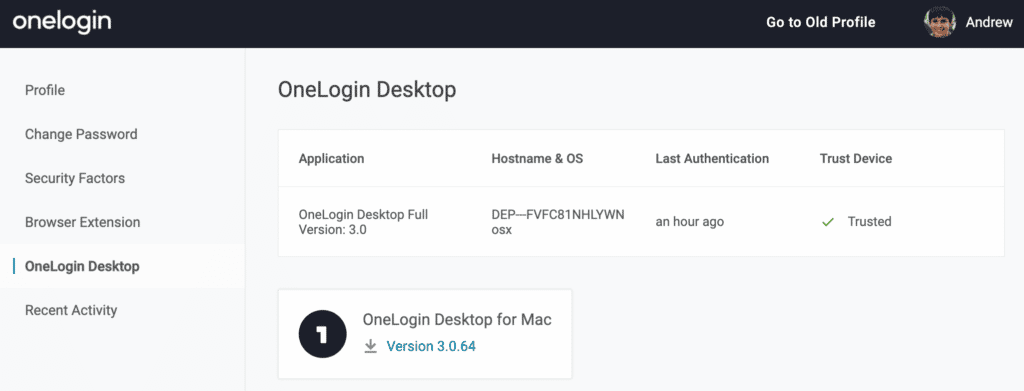
- OneLogin: Best for developers
- ManageEngine AD360: Best for teams seeking additional security
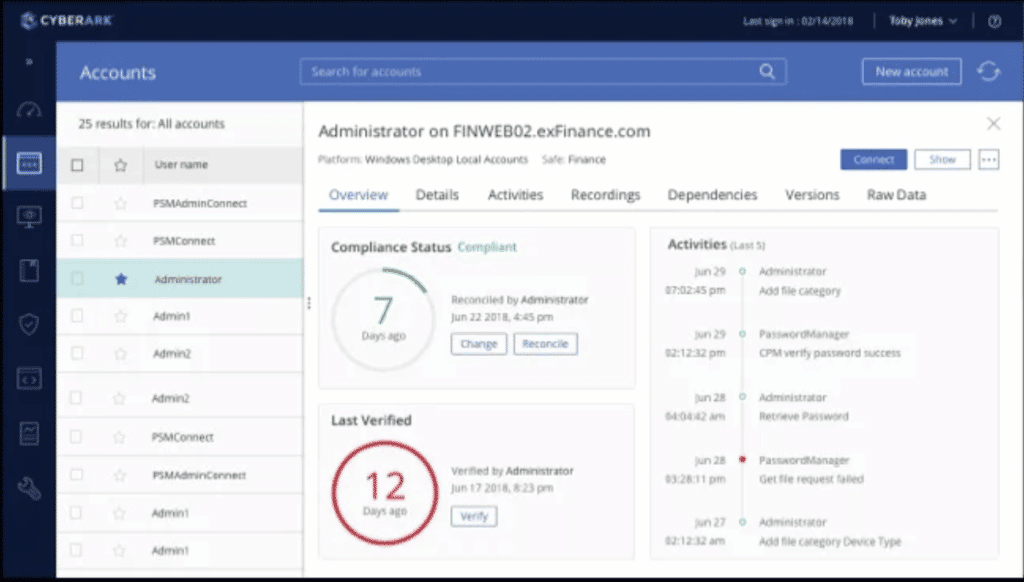
- CyberArk Workforce Identity: Best for behavioral analytics
- Microsoft Entra ID: Best for governance needs
- 5 Key Features of IAM Software
- How to Choose the Best IAM Solution for Your Business
- How We Evaluated IAM Solutions
- Frequently Asked Questions (FAQs)
- Bottom Line: Developing the IAM Ecosystem
Top Identity Access Management Solutions at a Glance
This chart compares some of the most basic features of IAM tools, as well as some less common capabilities like identity orchestration.
| MFA | Privilege access management | Identity orchestration / workflows | Secrets management | |
|---|---|---|---|---|
| CyberArk Workforce Identity | ✅ | ➕ | ✅ | ➕ |
| JumpCloud Platform | ✅ | ? | ? | ✅ |
| Okta | ✅ | ✅ | ✅ | ? |
| OneLogin | ✅ | ➕ | ➕ | ? |
| ManageEngine | ✅ | ✅ | ✅ | ? |
| Microsoft | ✅ | ✅ | ✅ | ? |
✅ = Has feature ?= Not offered ? = Unclear ➕= Available from vendor in another solution
JumpCloud – Best Overall
Pros
Cons

Okta – Best for Large Enterprises
Pros
Cons

OneLogin – Best for Developers
Pros
Cons

ManageEngine AD360 – Best for Teams Seeking Additional Security
Pros
Cons

CyberArk – Best for Behavioral Analytics
Pros
Cons

Microsoft Entra ID – Best for Governance Needs
Pros
Cons
Also read: A PowerShell Script to Mitigate Active Directory Security Risks
5 Key Features of IAM Software
When you’re shopping for an IAM tool, look for products that have the following features. While feature sets will differ somewhat among platforms, these are important for best managing identities and access. Not every tool has all these features, so make sure the product you choose at least has options for the features that are most important to you.
1. Multi-factor authentication
It’s becoming more common to require multiple methods of authentication because credentials can be stolen. If an attacker gains access to an account owner’s password, they can easily infiltrate an enterprise system. Requiring another means of authentication — like entering a passcode sent to a user’s phone — reduces attackers’ opportunities to access the application, making MFA a very important feature of IAM tools.
2. Single sign-on
SSO reduces the number of logins a user has to complete on their workstation. By logging into the IAM interface, users can access all integrated applications. This is not only more efficient but also more secure — there’s a reduced danger of password compromise because users won’t be writing passwords in insecure locations.
3. Identity lifecycle management
Managing user identity lifecycles is important for long-term security — it’s not enough to only set up someone’s access; it has to be properly maintained as their role changes. This can include de-provisioning of identities when a user leaves the company or privilege elevation when someone’s role changes.
4. Automated Workflows
The ability to use or customize automated workflows will reduce the long-term burden on IT and security teams. Workflows can manage users’ identities and access controls — when a certain step occurs, it triggers a set of sequential actions.
5. Privileged access management
Privileged access features specifically focus on highly privileged roles and accounts. These could include financial managers, executives, IT leaders, and users responsible for sensitive data management. Controls for PAM are especially important because of the abilities those accounts are typically granted and the amount of sensitive information they can access. Privileged access management is the feature most likely to cost you extra — or require an additional product — but the importance of these accounts merits additional security.
See the Best Privileged Access Management (PAM) Software
How to Choose the Best IAM Solution for Your Business
Each organization will need to verify that an IAM tool’s capabilities meet their needs, and they’ll need to estimate their accompanying resources and return on investment (ROI). Many tools provide trial periods for testing, but keep in mind that integrations can be time-consuming and should be reserved for finalists. Consider the following key factors when your team is shopping for and analyzing IAM products.
Integration capabilities
If you have a critical application, a superior IAM tool that does not integrate with or support that critical app will be useless. Actual usability is more important than potential capabilities. Before shopping, determine the apps for which you need secure access first. Once you have a shortlist, you can find IAM tools that support those apps.
User experience
How much hassle is introduced or reduced by implementing IAM? Many tools introduce self-service application requests, automated approvals, and single sign-on (SSO) capabilities that reduce friction for users to obtain and use internet-based resources.
Security needs
Organizations with advanced security requirements will need to deploy MFA options, execute granular control over access, and track and report on access by asset or by user. If your business has those advanced security needs, look for features like privileged access management and integrations with other security vendors.
Resources needed
Some products will be resource-light SaaS solutions, while others will require local system deployments. The cost of any required resources to run the tool will also need to be added to the potential personnel costs of installation, configuration, maintenance, and use.
Delivered value
Ideally, tools don’t just deliver features; they should deliver benefits too. The value of additional security and control may be difficult to quantify, but time savings compared to manual execution of IAM tasks has led to Return on Investment (ROI) estimates around 500%. Will it take time for these benefits to show? Sometimes. But consider the long-term benefits for your organization — including the fines, recovery costs and data loss you can avoid by better protecting your data and accounts.
See the Top Data Loss Prevention (DLP) Solutions
How We Evaluated IAM Solutions
To create the pool of candidates for this year’s top IAM solutions, we initially consulted a variety of sources such as Gartner’s Magic Quadrant for Access Management, the Forrester Wave for Identity as a Service (IDaas), the Identity Management Institute, and customer reviews on websites such as G2. We then reviewed each product’s capabilities and features.
To remain under consideration, the tool needed to deliver robust capabilities for both identity management as well as access management. Some otherwise capable tools did not make the cut because they might only deliver some of those capabilities.
We evaluated these IAM solutions using a product scoring rubric. In our rubric, we weighted criteria and features according to the percentages listed for each below, and that weighting factors into the total score for each product. The six products that scored highest in the rubric made our list. However, that doesn’t mean that one of these is automatically the best pick for you and that a good option can’t be found outside this list.
Note that the score each product receives is only based on whether it meets the criteria we set for the analysis rubric. All these products are successful in this category, and their score here is not an overall measure of their value. Rather, it analyzes how well they met our specific criteria.
Pricing Transparency & Trials | 10 Percent
We evaluated whether the vendor was transparent about pricing and whether the product had a free trial, including how long the trial lasted.
Core Features | 35 Percent
We evaluated each IAM tool’s most important features, like MFA, identity lifecycle management, and integrations with directory tools.
Additional Features | 20 Percent
We evaluated nice-to-have features like sandboxes, user permission templates, and integrations with HR management systems.
Functionality & Management | 20 Percent
We evaluated ease of use and management, availability of knowledge bases and training videos, and whether the product offers a native API.
Customer Support | 15 Percent
We evaluated phone and email availability, product demo availability, and whether technical support teams offered a 24/7 option.
Frequently Asked Questions (FAQs)
The following questions emphasize the importance of IAM tools in enterprise environments and the ways they work with other solutions.
Why Are IAM Tools So Popular?
Identity and access management mitigates some of the inherent risk of users accessing customer and proprietary data. It’s more organized than usernames and passwords for every account, especially when single sign-on allows users to input one password for all connected applications.
Because IAM tools help businesses manage employee access to data, they also help companies stay compliant with regulatory standards. Most data protection standards have access requirements, such as auditing which employees can access specific information. Using IAM tools helps businesses meet those requirements.
What Is The Difference Between IAM And Active Directory?
A directory service like Active Directory is only one component of an identity and access management platform. It records user data and stores it for IAM solutions to use. Many IAM tools integrate with AD because it’s one of the most popular directories.
AD is useful, but it’s not a substitute for an IAM solution. Directories don’t provide the level of access and policy management that many IAM tools do, and they won’t be able to protect applications and data on their own.
What Is An IAM Workflow?
Security teams design workflows to automate IAM processes like provisioning users and assigning roles and permissions. Workflows are useful because they reduce some of the manual burden on security teams. One action triggers a set of actions, which perform roles like automatic permission assignments.
Bottom Line: Developing the IAM Ecosystem
Selecting an identity and access management solution can dramatically improve security and control over SaaS and cloud resources. For organizations seeking to further improve security, there are many adjacent technologies that compliment and strengthen an IAM solution.
For example, privileged access management (PAM) provides specialized tools to manage administrator and other elevated and dangerous access levels. Active Directory security, machine identity security, password managers, and encryption key management also address key factors of identity and permissions security that could pose enormous risk to a breached organization.
Although it may seem that there will always be another tool needed to fully secure an organization, implementing broad, fundamental security layers will always be the first important steps to take, for network, cloud and application security. For today’s distributed IT environments, adopting an effective IAM tool should be one of those first steps.
Read next: 34 Most Common Types of Network Security Solutions
This updates a Jan. 26, 2023 article by Chad Kime