Network security is not just about keeping the bad guys out. It’s about having a system that’s constantly on guard, ready to spot threats, malicious trends, and suspicious activities before they wreak havoc on your system.
Intrusion detection systems (IDS) and intrusion prevention systems (IPS)—often combined as intrusion detection and prevention (IDPS)—play a key role in these network security defenses. They help teams detect suspicious activity, block malicious traffic and software, and examine system logs for potential threats.
This guide covers industry-leading IDPS solutions, along with key features and considerations as you evaluate products for your organization.
- Atomic OSSEC: Best overall for teams of multiple sizes
- Trellix IPS: Best option for core and advanced features
- Check Point Quantum: Best for NGFW environments
- SolarWinds SEM: Best for log management and reporting
- Trend Micro TippingPoint: Best for threat intelligence
- Alert Logic MDR: Best for managed enterprise services
Featured PartnersFeatured Partners: Intrusion Detection and Prevention (IDP) Software
eSecurity Planet may receive a commission from merchants for referrals from this website
What Is an intrusion detection & prevention system?
An intrusion detection and prevention system combines features from IDS and IPS to better detect and block malicious traffic, rather than just doing one of the two. IDPS products often have features like log analysis, alerts, and threat remediation to find suspicious activities and trends and help security teams stop threat actors. IDPS or IPS features often belong to a larger security suite or product a vendor offers, serving as one module of many.
Top IDPS solutions compared
The following comparison table compares our top IDPS products, including features like threat remediation as well as free trial and managed service availability:
| SSL/TLS Inspection | Threat Remediation | Available as Managed Service | Free Trial | |
|---|---|---|---|---|
| OSSEC | ❌ | ✔️ | ✔️ | 14 days |
| Trellix IPS | ✔️ | ✔️ | ❌ | ❌ |
| Check Point | ✔️ | ❌ | ❌ | Contact for length |
| SolarWinds SEM | ❌ | ✔️ | ❌ | 30 days |
| Trend Micro TippingPoint | ✔️ | ✔️ | ❌ | ❌ |
| Alert Logic MDR | ✔️ | ✔️ | ✔️ | ❌ |

OSSEC – Best Overall for Teams of Multiple Sizes
Overall Reviewer Score
3.6/5
Core Features
3.5/5
Advanced Features
3.3/5
Deployment & Usability
4.4/5
Pricing
4/5
Customer Support
3.2/5
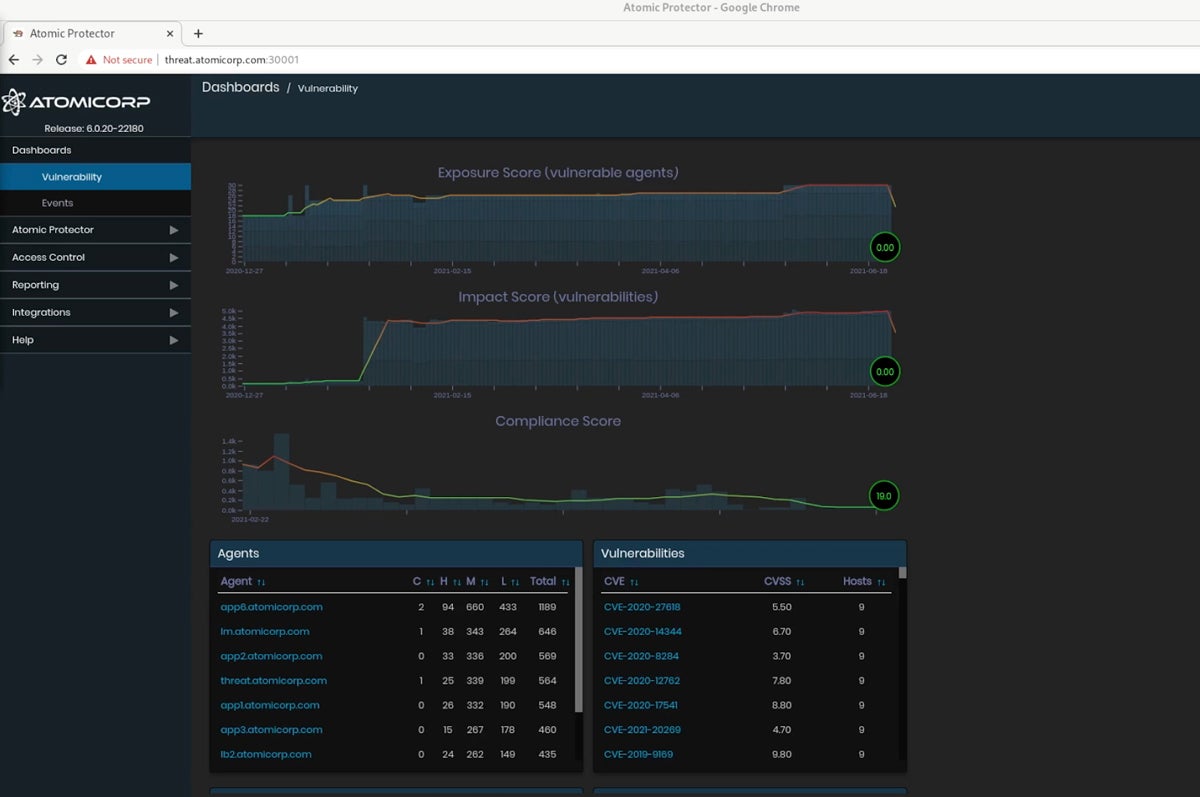
OSSEC is an IDPS product for teams of all sizes, notable for its feature range and transparent sales team. It offers threat remediation, quarantine capabilities, log analysis, and file integrity monitoring.
OSSEC also offers a free, open-source IDS, which is a good choice for SMBs; consider that product if your team is smaller. But here we’ve focused on Atomic OSSEC, the enterprise offering — it’s a strong option for medium and large businesses.
Pros
Cons
- Contact for quote: Custom pricing available; approximately $55 per endpoint or system in a year-long license but may vary depending on numbers and environment
- Free trial: 14 days
- File integrity monitoring: Examine the integrity of application files and operating systems.
- Log management: Centralize log data from different sources and send it to SIEMs for further analysis.
- Agent management: Perform agent and server configurations in a central management console.
- Threat intelligence: OSSEC gathers threat data from global nodes for broader security information.

Trellix IPS – Best Option for Core & Advanced Features
Overall Reviewer Score
3.4/5
Core Features
3.9/5
Advanced Features
3.7/5
Deployment & Usability
3.2/5
Pricing
2.8/5
Customer Support
3.2/5
Trellix Network Security is a security platform that includes IPS and offers threat blocking, integrations, and policy management to handle sophisticated threats. Trellix IPS is designed for enterprise-level security, offering features like DDoS prevention, heuristic bot detection, and host quarantining.
If you’re a large enterprise or have an experienced security team, consider Trellix — its range of basic and advanced IDPS features will give teams plenty of functionality.
Pros
Cons
- Contact for quote: Custom pricing available; some pricing info available from resellers like AWS
- DDoS prevention: Rate limiting, DNS protection, and connection limiting help prevent DDoS attacks.
- Threat intelligence: IPS integrates with Trellix Global Threat Intelligence for comprehensive threat info.
- Advanced callback detection: Trellix IPS identifies attack data that could come from botnets.
- Sandboxing: Integration with Trellix Intelligent Sandbox enables deep traffic inspection.

Check Point Quantum – Best for NGFW Environments
Overall Reviewer Score
3.3/5
Core Features
3.2/5
Advanced Features
2.4/5
Deployment & Usability
3.2/5
Pricing
3.8/5
Customer Support
4.7/5
Check Point Quantum, the product family that includes Check Point’s next-gen firewalls and security gateways, also offers IPS that integrates with other platform members.
Check Point IPS can detect and block DNS tunneling attempts, signature-less attacks, protocol misuse, and known CVEs. If you’re already a Check Point customer, the IPS fits particularly well; if you’re considering investing in an NGFW with built-in IPS, Quantum is also a strong option.
Pros
Cons
- Contact for quote: Custom pricing available
- Free trial: Contact for length
- Customizable reports: View critical security events and needed remediation in a single interface.
- Vulnerability detection: Supported network and mail protocols include HTTP, POP, IMAP, and SMTP.
- Policy configuration: Develop policies based on tags for vendor, protocol, file type, and threat year.
- Virtual patching: Security updates happen automatically every two hours via the Check Point security gateway.

SolarWinds Security Event Manager – Best for Log Management & Reporting
Overall Reviewer Score
3.2/5
Core Features
3.7/5
Advanced Features
0.7/5
Deployment & Usability
2.8/5
Pricing
4.8/5
Customer Support
4.7/5
SolarWinds Security Event Manager combines multiple security technologies, serving as a hub for insider threat management, incident response software, and log analytics, just to name a few.
Consequently, it has plenty of IDPS capabilities, but SolarWinds SEM really shines is its log management and reporting capabilities. Features include compliance reporting software and log analytics, making SEM a great choice for compliance-focused teams.
Pros
Cons
- Subscription-based plan: Starts at $3,292
- Perpetual plan: Starts at $6,168
- Free trial: 30 days
- Network-based IDS: Network visibility integrates with logs from other areas of the business infrastructure.
- Compliance reporting: Supported regulatory standards include HIPAA, PCI DSS, SOX, and ISO.
- Log analytics: SEM analyzes logs from multiple products, including Juniper devices and Microsoft Exchange.
- SIEM capabilities: SEM collects information about all network activity and inspects it for threats.


Trend Micro TippingPoint – Best for Threat Intelligence
Overall Reviewer Score
3.1/5
Core Features
3.3/5
Advanced Features
1.4/5
Deployment & Usability
3.4/5
Pricing
2.8/5
Customer Support
5/5
Trend Micro TippingPoint is a network security solution that helps guard against zero-day and known vulnerabilities with features like traffic scanning and threat blocking.
Tipping Point integrates threat intelligence from its Digital Vaccine® Labs so your business has a clearer picture of threats across your infrastructure. We recommend Trend Micro if you’re looking for deep threat intelligence and cybersecurity capabilities.
Pros
Cons
- Contact for quote: Custom pricing available; some pricing info available from resellers
- Vulnerability remediation: Integration with vulnerability tools and CVE mapping helps remediation.
- High availability: Fault tolerance features include watchdog timers, built-in inspection bypass, and hot swaps.
- Configuration recommendations: Out-of-the-box settings help develop threat protection policies.
- Traffic inspection: Deep packet inspection and reputational analysis of URLs improve visibility regarding traffic.
Alert Logic MDR – Best for Managed Enterprise Services
Overall Reviewer Score
3.1/5
Core Features
3.3/5
Advanced Features
1.8/5
Deployment & Usability
3.6/5
Pricing
2.8/5
Customer Support
4.2/5
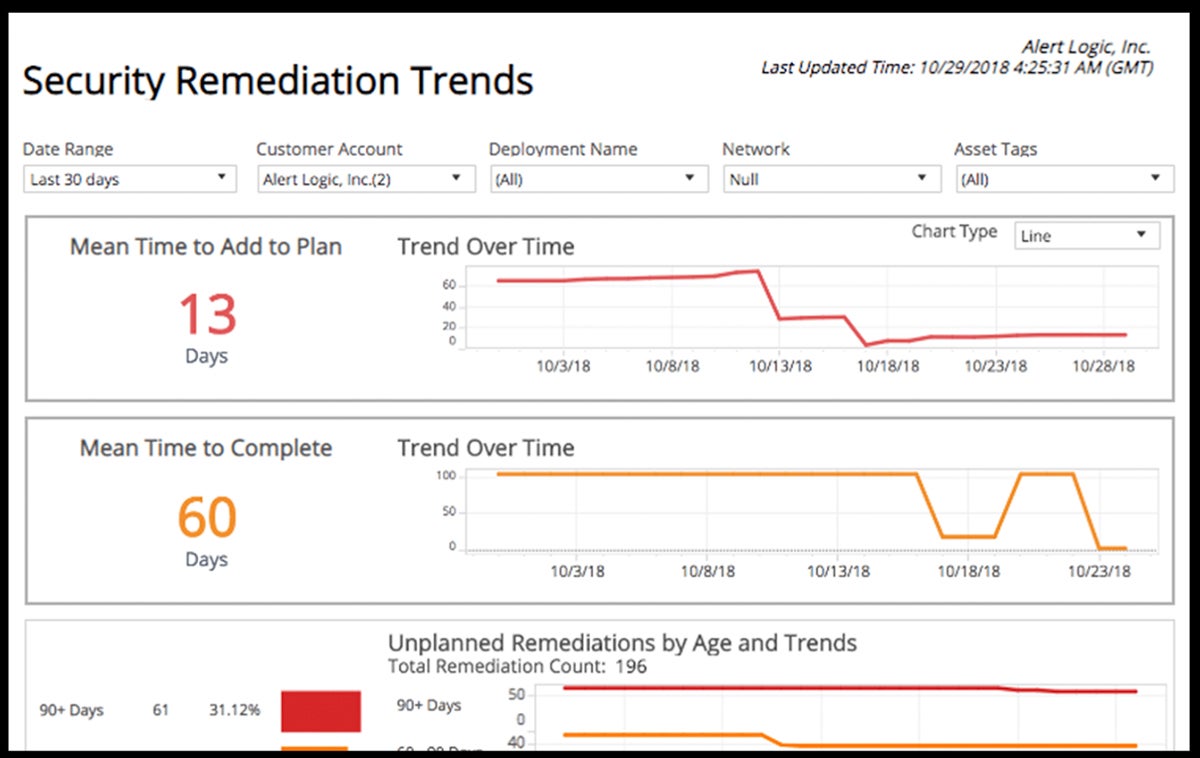
Alert Logic is a managed detection and response platform with managed network IDS, container security, threat detection, and vulnerability management. Alert Logic’s MDR platform can be deployed on-premises or as a cloud service.
The managed security service has industry-leading dashboards and analytics to provide insights about organizations’ network activity, threats, users, and configurations to improve proactive detection and response.
Pros
Cons
- Contact for quote: Custom pricing available
- Dedicated agent: Alert Logic’s agent monitors Windows and Mac endpoints using ML and behavioral analytics.
- Compliance reporting: Users can access reporting and integrated PCI DSS and HIPAA controls.
- Log review: Machine learning identifies overall trends and anomalies that result from those trends.
- Vulnerability scanning: Alert Logic connects data from cloud, on-premises, and hybrid systems.
Top 5 features of IDPS software
Our picks for top IDPS features include policy management, event alerts, reports, traffic analytics, and threat or incident remediation. Use this list of IDPS features as a benchmark as your team shops for potential products, and keep in mind a few specific features your business needs.
Policy management
IDPS solutions should allow teams to manage security policies, configuring and overseeing them in a central management console. Policy management capabilities that are easy and straightforward to use will help your teams learn the product faster and configure it more successfully.
Alerts
If you’re using a security product like IDPS, you’ll want to know immediately when a security event occurs. An IDPS solution should provide timely and clear alerts, and they should also be prioritized so your security team knows what to address or mitigate first.
Reporting functionality
It’s helpful for teams to share clear, understandable security data with each other and other employees, particularly leaders and executives. IDPS solutions should offer reporting so security personnel can make more informed, logical decisions from clearly presented data. Some products will offer both templates and customizable reports.
Traffic analysis
IDPS solutions should carefully analyze network traffic, detect anomalies, and determine when traffic doesn’t meet security policies. Traffic analysis can include packet inspection, which looks closely at the details of network packets and accepts or rejects them. This improves network security by filtering traffic based on your organization’s predefined policies.
Threat remediation
Because IDPS includes prevention capabilities, not just threat detection, products should be capable of fixing or mitigating threats instead of just locating them. While products’ remediation abilities will vary, they should assist teams in preventing and mitigating threats as quickly as possible once they’re found.
How we evaluated IDPS solutions
We evaluated multiple IDPS products with a product scoring rubric, which had five weighted categories composed of subcriteria with their own weighting. Each product we reviewed received an overall score out of five, which was based on all the final subcriteria scores and weights. The six products that scored highest in the rubric made our final list, and the scores plus the products’ overall capabilities helped us decide on their use cases.
Evaluation criteria
Our most significant product criteria included major IDPS features and advanced features like threat quarantine. We also considered usability, which measured the availability of managed services and deployment options. Finally, we looked at pricing information and customer support details, including demos and phone support availability.
- Core features (30%): We scored products based on the availability of core IDPS capabilities like policy management, alerts, and reporting.
- Criterion winner: Trellix
- Advanced features (20%): Advanced IDPS features included threat quarantine, sandboxing, and MITRE framework mapping.
- Criterion winner: Trellix
- Deployment & usability (20%): We reviewed products based on usability features like managed services, documentation, and multiple deployment options.
- Criterion winner: OSSEC
- Pricing (15%): We evaluated the transparency of vendor pricing, any available licensing information, and free trials.
- Criterion winner: SolarWinds
- Customer support (15%): We looked at availability of phone support, as well as support review scores and availability of demos.
- Criterion winner: Trend Micro
Frequently Asked Questions (FAQs)
What can IDPS protect against?
Intrusion detection and prevention systems protect IT systems from unauthorized access by monitoring users’ activities and looking for patterns that could indicate suspicious activity. IDPS can help protect teams from data theft, social engineering attacks, distributed denial-of-service attacks, and the modification of sensitive data.
What are the benefits of intrusion detection & prevention systems?
IDPS helps reduce technical downtime, mitigate breaches, and improve productivity by streamlining alerts and giving security teams more context about threats. While it needs appropriate policy management and reporting to be effective and logical, IDPS is a powerful tool once teams sufficiently configure and learn it.
Read more about the importance of IDS and IPS in the current security market.
What’s the difference between intrusion detection & intrusion prevention?
IDS tools were built to detect suspicious activity and log and send alerts. They’re not capable of preventing an attack, and the warnings they raise always require human intervention or an additional security system. IPS solutions respond based on predetermined criteria for types of attacks by blocking traffic and dropping malicious processes.
IPS tools may also lead to more false positives because they have inferior detection capabilities than IDS. However, IDPS solutions incorporate the strengths of both systems into one product or suite of products.
What are the types of IDPS?
IDPS generally has two types: host-based and network-based. Host-based IDPS is software deployed on the host that monitors traffic connecting to and from that host. It typically only protects a single, specific endpoint. In some cases, it may also scan system files stored on the host for unauthorized changes and processes running on the system.
Network-based IDPS is deployed in a location where it can monitor traffic for an entire network segment or subnet. Its functionality resembles firewalls, which can only prevent intrusions coming from outside the network and enforce access control lists (ACLs) between networks.
NIDS was built to detect and alert potential malicious internal traffic moving laterally throughout a network, making it an excellent tool for a zero-trust security framework.
How do intrusion detection and prevention systems enhance network security?
IDPS enhances network security by monitoring traffic in real-time through deep packet inspection and behavioral analysis. Unlike static firewalls, these systems detect anomalies by comparing traffic patterns against attack signatures and baseline network behavior, enabling organizations to identify sophisticated attacks that evade traditional defenses.
Prevention occurs through automated responses that block threats upon detection. When suspicious activity is identified, IDPS immediately terminates connections, blocks malicious IPs, or reconfigures network devices, minimizing dwell time and preventing attackers from establishing persistence within the network.
What are the common challenges in implementing IDS/IPS solutions?
While IDS/IPS solutions excel at network security, they could still have potential downsides during implementation. These challenges include:
- False Positives & Sensitivity Tuning: IDS/IPS systems frequently misclassify legitimate traffic as malicious, overwhelming security teams with alerts. This creates a direct trade-off between detection coverage and operational efficiency, as excessive tuning to reduce false positives often creates blind spots attackers can exploit.
- Performance Degradation: Deep packet inspection in IDS/IPS requires substantial processing power, especially at network boundaries with high traffic volumes. When traffic exceeds system capacity, security teams must choose between dropping packets (missing potential attacks) or accepting network slowdowns that impact business operations.
- Integration & Maintenance Complexity: IDS/IPS systems require seamless integration with firewalls, SIEM platforms, and network infrastructures — each with different protocols and configurations. This complexity compounds with the constant need to update detection rules for emerging threats, requiring specialized expertise that many organizations lack.
Bottom line: use IDPS in conjunction with other solutions
IDPS can help improve compliance and policy enforcement by enforcing policies that govern device connections to the network or internet, data transfer and storage for those devices, and data retention within systems.
While IDPS won’t be a sufficient standalone security solution for most enterprises, it’s a good product to have in the toolbox, especially if yours integrates with other tools, like NGFWs and endpoint detection and response. Use IDPS to support your security infrastructure as a whole, detecting intrusions and mitigating them more successfully with features like alerts, reports, and threat remediation.
If your business is considering other cybersecurity products, read more about the top cybersecurity companies next, including Palo Alto, Fortinet, and CrowdStrike.