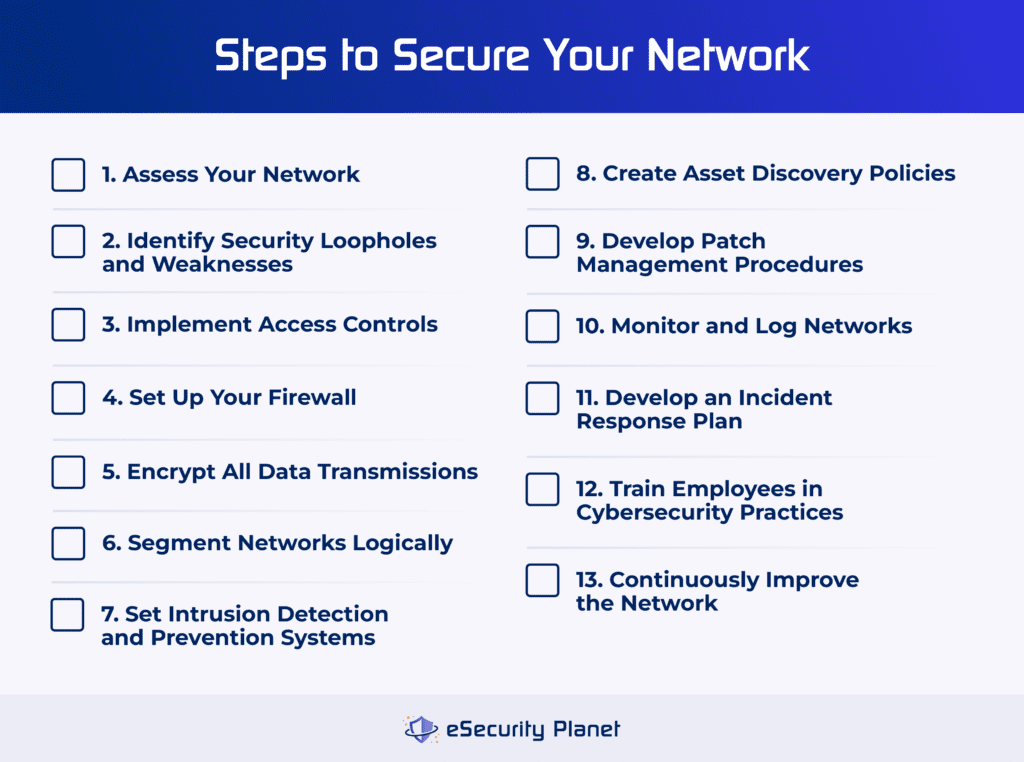
Truly securing your network infrastructure is one of the most critical choices your business can make to protect itself from threats. Technologies and tools like firewall rules, patch management, and incident response procedures help guard your sensitive data and applications. This process will vary depending on your business, but there’s a 13-step process, from assessing your network to improving security over time, that works for many organizations.
Click this image to download a detailed network protection checklist for your security and networking teams to use.
1. Assess Your Network
Before you implement any cybersecurity practices or procedures, you first need to know the current status of your network, which includes existing access controls, the status of your firewall and its rules, and current vulnerability management procedures.
Audit All Access Controls
Complete an audit of your current access controls, including usernames, passwords, passcodes, and any multi-factor authentication you currently have set up. To audit all access controls, go through each application or system that requires login credentials or permissions and document them, including whether they’re protected by password managers. Look at your current password requirements, too; do they force employees to set hard-to-guess passwords?
Examine Any Existing Firewalls & Firewall Rules
Take inventory of any existing network firewalls and the rules you currently have. Navigate to your firewall’s management panel, find the list of rules, and look for any unhelpful or inconsistent rules. Maybe one rule contradicts another, or an old rule breaks your business’s new security policies. This is also a good time to perform an initial firewall audit; it’ll reveal ways that the firewall doesn’t work well or if your rules no longer meet enterprise policies.
Document Your Vulnerability Management Practices
Before you overhaul your network’s cybersecurity infrastructure, document all your existing vulnerability management tools or procedures. Are there any that don’t work, and which can you change? Also, determine whether your security team can easily find vulnerabilities and mitigate them, or if it’s been a challenging process for them so far. You could even send them a survey with a few questions about vulnerability management and mitigation processes.
2. Identify Security Loopholes & Weaknesses
Identifying vulnerabilities goes hand in hand with assessing your network, so you may end up performing these steps at the same time. To find loopholes in your business’s security, you can implement strategies like vulnerability scanning and penetration testing.
Perform Vulnerability Scans
Test your network architecture so you know where any problems exist. Traffic volume tests or vulnerability scans catch misconfigurations, unapplied or incorrectly applied encryption, weak passwords, and other common issues before hackers can exploit them. You can also use vulnerability scans to detect sloppy encryption key management. While you can scan for vulnerabilities manually, I recommend using software, which is more efficient.
If your business would benefit from using vulnerability scanning software, check out our guide to performing a vulnerability scan.
Consider Penetration Testing
Vulnerability scans might detect common weaknesses, but active penetration tests determine if vulnerabilities pose a true risk or may be mitigated by other controls. Penetration tests can also determine if the existing controls will sufficiently stop attackers. You can perform penetration testing using tools, but you may have more accurate results if you deploy external experts. Talk to your security team lead about the possibility of hiring a pentester.
3. Implement Access Controls
Successful security includes restricting access to network resources, like hardware and management software. Implement appropriate access controls for every resource, depending on which employees need access at particular times. These include hard-to-guess passwords, Active Directory integrations, multi-factor authentication, least privilege access strategies, and access to cloud platforms.
Create Strong Credentials
Increase password strength requirements to add complexity, or enforce more frequent password rotation for all employee login credentials. Password managers help users meet more stringent requirements and can enable centralized control as well. Enterprises may also adopt single-sign-on (SSO) technologies to streamline access to cloud resources.
Use Active Directory if Needed
The smallest organizations might only worry about device access, otherwise known as login credentials — usernames and passwords. But as an organization grows, formalized and centralized control using Active Directory (AD) or an equivalent Lightweight Directory Access Protocol (LDAP) tool saves your business time and enables faster responses for change requests. Implementing AD or LDAP takes time but is valuable for larger organizations.
Implement Multi-Factor Authentication
Growing organizations face increased breach risk as the potential damages from stolen credentials increase with company size and reputation. To reduce this risk, many adopt multi-factor authentication to provide improved security over 2FA, especially when applications or tokens replace vulnerable SMS text as a factor. Biometric and passwordless solutions can be more expensive but difficult-to-spoof solutions.
Use the Principle of Least Privilege Access
Implementing a least privilege access strategy means that your network and security teams only give employees access to systems if they absolutely need it to do their job. In the past, employees had access “just in case” they needed it. But that opens the door further to threat actors and potential internal threats. Make sure only employees who need access to an application get it, and that they receive administrative or view-only access based on their roles.
Manage Access to Cloud Resources
Even smaller organizations now use cloud resources, but most internal network controls don’t extend to resources hosted outside of the network, such as Office 365, Google Docs, or segregated branch office networks. Cloud access security brokers (CASB) and secure browser applications can provide consolidated solutions to protect users in the cloud.
Make sure every user on a cloud account has appropriate permissions, whether they’re an admin or can only view a document. Also check that all your cloud instances aren’t exposed to the internet.
4. Set Up Your Firewall
The firewall implementation process will vary depending on whether your network already has one, but you can still use it as a checklist for items you haven’t yet completed. Follow this general process to install a firewall, create rules and zones, and test and manage the firewall over time.
Choose the Right Type of Firewall
If your business doesn’t have a firewall yet, you’ll need to choose one that makes sense for your network. Smaller businesses might want a relatively small appliance, but larger enterprises may want a next-generation firewall from one of the leading network vendors. Also consider firewalls as a service if your business doesn’t currently have the resources or personnel to support an on-premises firewall.
Secure the Firewall
For your firewall to work well, you’ll need to create specific rules that designate which traffic the firewall accepts and blocks. This will vary depending on your business’s needs; you can customize the rule lists to be more or less restrictive based on the applications and data that reside behind the firewall. Implement rules for both inbound and outbound traffic, which restrict the traffic entering your network and the data leaving it.
Read more about creating firewall rules and how they improve your business’s network security.
Create Firewall Zones & IP Addresses
Now divide your firewall into any zones that need to be separated, and assign necessary interfaces to each zone. Then designate firewall resources and servers with their appropriate IP addresses if they don’t already have them.
Make an Access Control List
The access control list (ACL) determines which resources or users are permitted to access the network. Admins may specify a list for the whole network or for certain subnets. Create an access control list in conjunction with your firewall rules so nothing in that list contradicts the other; it’s good to have them side by side while developing rules to accept or drop packets.
Test Configurations
Make sure any network configurations work. If you block traffic from a certain website, ensure that the firewall doesn’t allow that traffic through. Test the rules, too, especially for blacklists and whitelists; you can do this by connecting to the network and attempting to load a blocked website. If it still loads, your blacklist isn’t working.
Manage the Firewall Over Time
Firewalls need to be checked and reconfigured regularly. You also need team members responsible for handling regular firewall upkeep and maintenance, including updating rules to fit changing business policies. Assign team members to specific firewall management tasks, and create a schedule for auditing firewall rules. Make sure everyone on your team knows how they’re supposed to take care of the firewall, using clear, straightforward documentation.
5. Encrypt Data Transmissions
Encryption can protect assets directly throughout your entire IT infrastructure. You can protect endpoints using full disk encryption, databases using settings, and critical files using file or folder encryption.
Encrypt Endpoints
Encrypting an endpoint’s entire hard drive or SSD protects the entire device. Also, operating systems, such as Windows, offer options to change settings and require encrypted connections to specific assets or throughout the network. You can change other settings to prevent the transmission or storage of plain-text passwords and to ensure storage of salted password hashes.
Learn more about different types of encryption, such as full disk encryption and digital certificates, and when they’re useful.
Encrypt Databases
You can encrypt databases by entire application, by column, or through the database engine. Different encryption implementations will affect how fast you can query data within the database, so take that into consideration before encrypting anything.
Encrypt Files or Folders
You can encrypt data at either the individual file level or at the folder level. File-level encryption will typically take more time and allows you to encrypt individual files and choose not to encrypt others, if necessary. Folder-level encryption shields an entire folder’s data at a time, which is useful when you need to protect full folders of data at rest at a time.
6. Segment Networks Logically
Growing organizations need to allow different types of access, but they shouldn’t allow everyone to access everything in the network. Network segmentation can create networks for guests, quarantined networks for insecure devices, and even separate networks for vulnerable IoT, OT, and known obsolete technology. Use virtual LANs to create subnets, and implement zero trust strategies so users don’t have unnecessary access.
Set Up Virtual LANs
Virtual local area networks (VLANs) partition networks on a single piece of hardware and allow teams to split networks into smaller subnetworks. They’re helpful because they make network management processes easier and provide additional security since not all traffic is going to the same place. You can designate different types of traffic to go to different subnets, depending on your security needs.
Read more about setting up a virtual LAN, including configuring switch ports and connecting them to the VLAN.
Create Subnetworks
Your network segmentation should make sense based on the way your business routes traffic. For example, if two subnetworks, or subnets, reside next to each other on the larger network, you should put a firewall between them if one subnet is processing external traffic and the one next to it has sensitive data on it. It can also help to group similar technological resources on the same subnet for more logical routing.
Consider Zero Trust
I recommend implementing a zero trust framework for your entire network infrastructure. Zero trust, combined with network segmentation, requires users to prove they’re authorized to access each individual resource on the network. A zero trust framework uses the concept “Never trust, always verify.” Users on the network have to verify their right to use an application or log into a certain system, rather than having access to everything just because they got past the firewall.
7. Set Intrusion Detection & Prevention Systems
An intrusion detection and prevention system (IDPS) is one of the core functionalities of network security. You need to know what’s going into your network, what’s leaving it, and if there are any obvious vulnerabilities within the hardware and software that make up the network. Intrusion detection and intrusion prevention can function somewhat separately, but they’re often combined in security suites.
Configure Intrusion Detection Systems
Intrusion detection systems (IDS) are primarily responsible for identifying vulnerabilities and attackers. They alert network administrators when malware is detected in a system, a strange user logs into software, or internet traffic overwhelms a server unexpectedly. They’re useful for detecting malicious behavior, but they usually can’t fix security issues on their own.
Configure Intrusion Prevention Systems
Intrusion prevention systems don’t just observe vulnerabilities and attacks — they’re tasked with fixing them. This includes standard remediation actions, like blocking traffic or eradicating malicious software. Intrusion detection and prevention tend to be most effective when they’re bundled together, so you can identify issues and fix them on a single platform.
8. Create Asset Discovery Policies
Unauthorized devices can intercept or redirect network traffic through attacks such as connecting unauthorized computers to the network or deploying packet sniffers to intercept network traffic. Similarly, spoofed domain name system (DNS) addresses can redirect users from legitimate connections to dangerous websites. To protect your network, block or quarantine assets as needed, always scan for assets, and disable any network features you don’t need.
Block or Quarantine Devices
Network access control (NAC) solutions test for outdated or vulnerable software on endpoints and redirect devices to quarantine until remediated. Unauthorized devices may be blocked or quarantined. You can achieve some NAC capabilities by adding MAC address filtering or whitelists to firewalls and servers, but whitelists can be time-consuming to maintain.
Scan Assets Continuously
IT asset management (ITAM) tools can scan for devices connected to the network and send alerts or block unregistered devices. Organizations need to verify the types of assets they’re trying to detect. Some applications, cloud infrastructure, networking equipment, or Internet of Things (IoT) devices may require more sophisticated ITAM or additional tools to detect them.
Disable Unneeded Features
Any unused access port in a firewall, unneeded remote access (storage, printer, routers, etc.), and similar features will often be unwatched. Hackers will seek to find and exploit these opportunities. Better to simply disable them if they are unneeded. For this reason, organizations should also disable Universal Plug and Play (UPnP) capabilities once setup is complete because hackers have found ways to use the automation features to load malware.
9. Develop Patch Management Procedures
Securing network hardware and software requires security teams to consistently update their products to the most current version. This process includes patching as soon as possible, creating patch assignments, and keeping careful watch over your vendors’ security bulletins.
Patch Immediately
The more quickly your business patches hardware and software, the less time threat actors will have to exploit the vulnerabilities within them. If your business finds that you have limited time to patch resources, adjust processes and tasks so patching is a higher priority. If you implement security platforms with built-in patch management features, you’ll receive reminders about patches, which will help your team fix vulnerabilities faster.
Assign Patch Management Roles
Develop a patching schedule for standard version updates for all your networking resources. A patching schedule includes assigning team members roles so everyone knows who’s responsible for updating each appliance and software version. I recommend creating a simple document that clearly outlines who is responsible for patching each piece of hardware and software, as well as the days and times they’re supposed to be updated.
Monitor Vulnerability News & Releases
Part of a strong patch management strategy is being proactive about security issues by monitoring your vendors’ vulnerability information and global industry news in general. New vulnerabilities crop up every week, and often they appear within networking equipment and operating systems. The more quickly you’re aware of issues, the sooner you can patch them and avoid a zero-day exploit or similar attack.
10. Monitor & Log Networks
You may not immediately recognize network traffic as malicious, but monitoring it with a security information and event management (SIEM), security operations center (SOC), managed detection and response (MDR), or similar team may detect unusual behavior. These teams can also respond to alerts and remediate attacks that evade automated response. Sandboxing is also an option if you want to further analyze strange behavior on your network.
Designate Monitoring Resources & Teams
The cybersecurity industry has a plethora of products and services that monitor networks, and if your business leaders feel overwhelmed about which to choose, look closely at the functions of each:
- SIEM: Focuses on aggregating enterprise data and logs, often requiring a lot of monitoring and management.
- SOC: Manages daily security operations through a team of analysts and security personnel, either internal or external to your company.
- Endpoint detection and response (EDR): Finds and mitigates security threats specifically on endpoint devices.
- MDR: Provides managed detection and response services so your business can benefit from external analysts’ technology and insights.
Respond to Alerts
Responding to security alerts is either your job or the job of your operations center or managed service provider. Regardless of who’s doing this, you’ll need to designate exactly which team member is in charge of which part of the alert triage process. This improves responsiveness and increases the chance that your security team will handle threats more effectively.
Use a Sandbox
If you discover malware on your network and want to learn more about its patterns, consider a sandboxing product. These help your team watch the way malicious programs work in a safe, controlled environment. They often come in larger security suites, like managed detection and response solutions, but you can purchase them separately, too.
11. Develop an Incident Response Plan
Your business always needs an incident response plan to know how to handle security events, no matter how small your security team is. An incident response plan should clearly list every step, in order, that your team should take to mitigate threats. A few of the most common characteristics of an incident response plan include customization, flexible structure, and proper alert methodology.
Create Customizable Plans for Multiple Situations
It’s likely that you’ll need more than one iteration of an incident response plan, not just a single list of steps that works in every situation. Creating a general template and then a few different, more specific plans is often a good strategy for customizing an incident response plan for different types of security incidents. Responses will vary depending on the vulnerability or attack, and so will the specific plan for each.
Be Flexible When a Process Needs to Change
While incident response plans do need ordered steps, they also need to have some wiggle room in case a process needs to change last-minute. This could look like listing a couple of additional team members to take over if the point person for one step is on vacation or sick or providing some different mitigation options for a security threat in case one doesn’t work.
Develop Alert Procedures That Make Sense
Security teams have to sort through a lot of information, and not all alerts are accurate. Develop procedures for triaging alerts and separating the false positives from the issues you really need to investigate. Automation is helpful here — you’ll save your incident response team some work if they have accurate software telling them which alerts to prioritize.
12. Train Employees in Cybersecurity Practices
Users remain one of the most prevalent sources of security breaches because everyone makes mistakes, and most employees aren’t security experts. Employee training and penetration testing are two of the main tactics businesses use to keep their personnel up to speed on threats, but everyday conversations within teams play a key role in protecting the company, too.
Train Your Teams on Security Basics
Cybersecurity training courses for enterprises and SMBs provide fundamental instructions that enable employees to contribute to better security practices for the whole organization. They highlight issues like phishing attacks, malware, unsafe password practices, and compromised hardware like USB drives. They also decrease the chance that a cyberattack will take employees completely by surprise.
Perform Penetration Testing
In a penetration testing scenario, internal or external hackers attempt to breach the business’s network and find the vulnerabilities in it. But some pentesting strategies may also include social engineering that exposes where employees need to be trained. Be careful not to vilify employees who make mistakes, and encourage the most transparent discussions within your organization.
Have Regular Conversations
Don’t downplay the importance of frequent discussions about cybersecurity. The more employees, but especially leaders, talk with their teammates about threats and vulnerabilities, the more prepared you’ll be to handle those issues. Discussing security also discourages employees from making unwise decisions.
13. Continuously Improve the Network
No security is foolproof. Vulnerabilities, misconfigurations, mistakes, and skilled attackers can create breaches in network and other security. Even the most robust security stack and most resilient network will fall apart without maintenance. Updating software and default credentials, disabling obsolete protocols, and performing regular network security audits will help your organization stay on top of network improvements.
Update Systems Automatically
Often, you can set local network routers, firewalls, and other equipment to automatically download new updates so that the devices and the firmware aren’t vulnerable. However, be aware that power failures during updates — or buggy updates — might result in equipment failure.
Change Default Credentials
Routers and other equipment generally arrive with publicly-disclosed default settings and names, but these are a wide-open door for hackers. Network admins should change the default router passwords to protect against unauthorized access. The U.S. Federal Trade Commission (FTC) provides broader recommendations to secure home Wi-Fi networks and other tips for offices and consumers.
If you need to update your router’s security, read more about configuring it to use WPA2.
Don’t Use Obsolete Protocols
IT equipment ships with backwards compatibility, but this can be problematic because that includes support for obsolete and dangerous options. I recommend disabling insecure protocols and ports such as FTP or SMBv1 throughout the ecosystem to prevent future exploits. Use your network management console to disable any outdated protocols that you don’t want your network to permit anymore.
Audit Your Network
Perform regular audits on your entire network so you continually uncover vulnerabilities and weaknesses over time. Audits should cover both hardware and software, so your switches, routers, operating systems, computers, and servers are all being tested and reviewed for security and performance.
Are you considering auditing your entire firewall? Use our guide to performing a firewall audit to inform your process.
Bottom Line: Securing a Network Is an Ongoing Process
Networks form a bridge between users and their computers on one side and the assets they need to reach on the other. Network security protects the bridge, but to ensure safety, each end of the bridge must also be protected by security for users, applications, data, and assets. Each component of a security strategy reinforces and protects the organization as a whole from the failure of any specific component.
IT security teams need to not only maintain awareness of their current and future needs, but they also must communicate those needs clearly to non-technical stakeholders to obtain budgets and other support.
To learn more about specific types of threats, read our guide to network security threats, which includes operational technology issues, malware, and human error.
Chad Kime contributed to this article.




