Digital forensics tools are products that help both business security teams and legal organizations uncover messy cases, from minor network security infractions to data privacy gaffes and major court cases. They offer features like data extraction, reporting, and anomaly detection to identify information in hard-to-access places. We analyzed the best digital forensics products, along with key features to consider and a breakdown of our evaluation.
Here are our picks for the best six digital forensics tools:
- Exterro FTK: Best overall forensics tool for a mix of pricing and features
- IBM QRadar SIEM & Forensics: Best for enterprise forensics and SIEM
- LogRhythm NetMon & SIEM: Best forensics software for customer support
- Cyber Triage: Best solution for cybersecurity-specific incident response
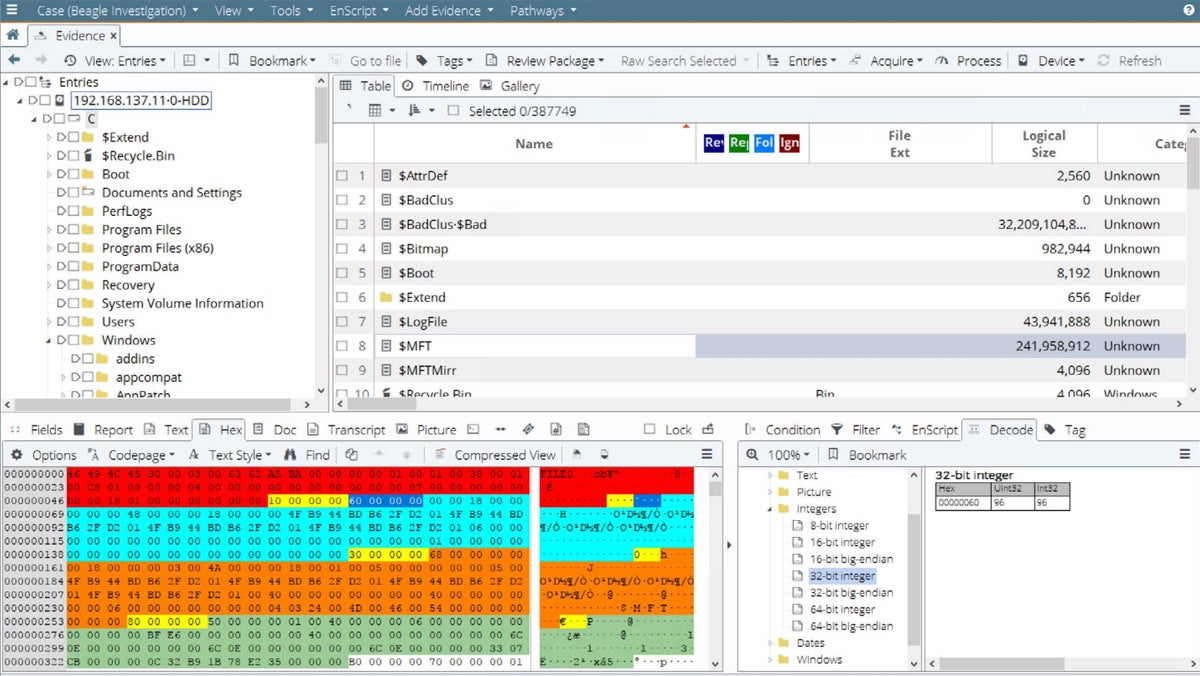
- Encase Forensic: Best solution for managed digital forensics services
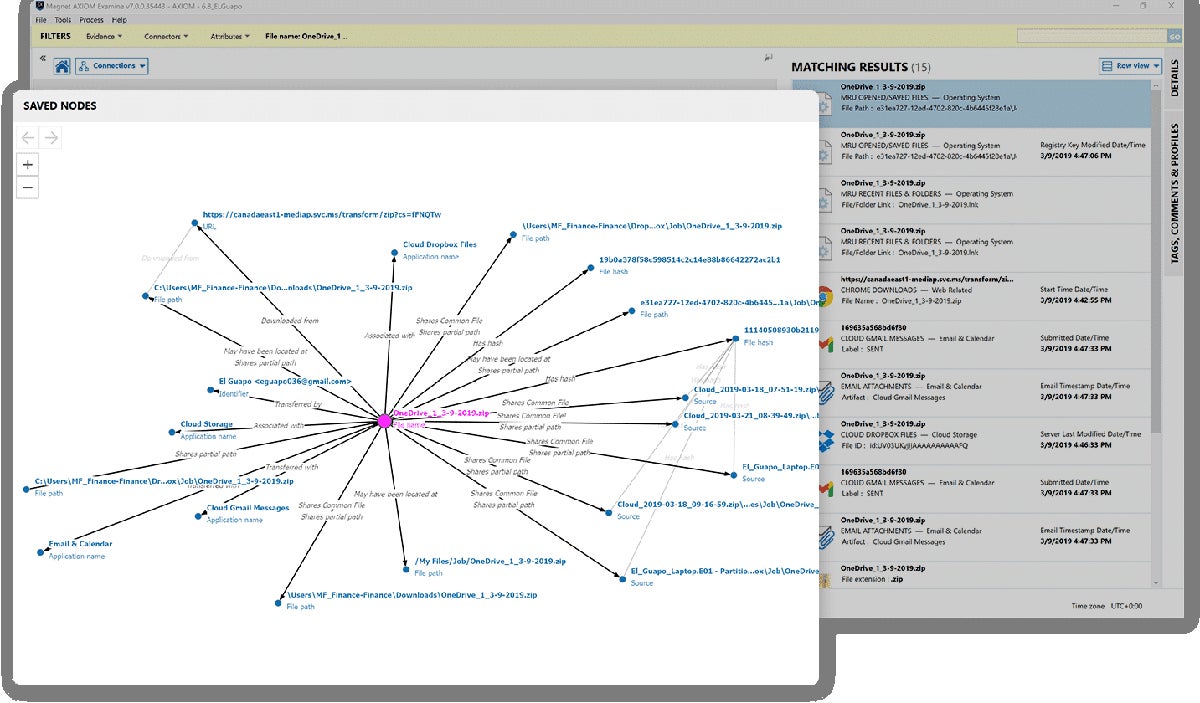
- Magnet AXIOM Cyber: Best solution for diverse deployment scenarios
Top Digital Forensics Software Compared
The following table gives a brief overview of our six top products, including features like data extraction and free trial availability:
| Data Extraction | Incident Response | Indicators of Compromise | Free Trial | |
|---|---|---|---|---|
| Exterro FTK | ✔️ | ✔️ | ✔️ | 30 days |
| IBM QRadar SIEM & Forensics | ✔️ | ➕ | ✔️ | ❌ |
| LogRhythm NetMon & SIEM | ❌ | ✔️ | ➕ | ❌ |
| Cyber Triage | ✔️ | ➕ | ✔️ | 7 days |
| Encase Forensic | ✔️ | ✔️ | ➕ | ❌ |
| Magnet AXIOM Cyber | ➕ | ✔️ | ❌ | Contact for length |
✔️=Yes ❌=No/Unclear ➕=Add-On
Table of Contents

Exterro FTK
Best Forensics Tool Overall for a Mix of Pricing & Features
Overall Rating: 3.9/5
- Core Features: 3.7/5
- Advanced Features: 4.3/5
- Deployment & Usability: 4.5/5
- Customer Support: 2.4/5
- Pricing: 5/5
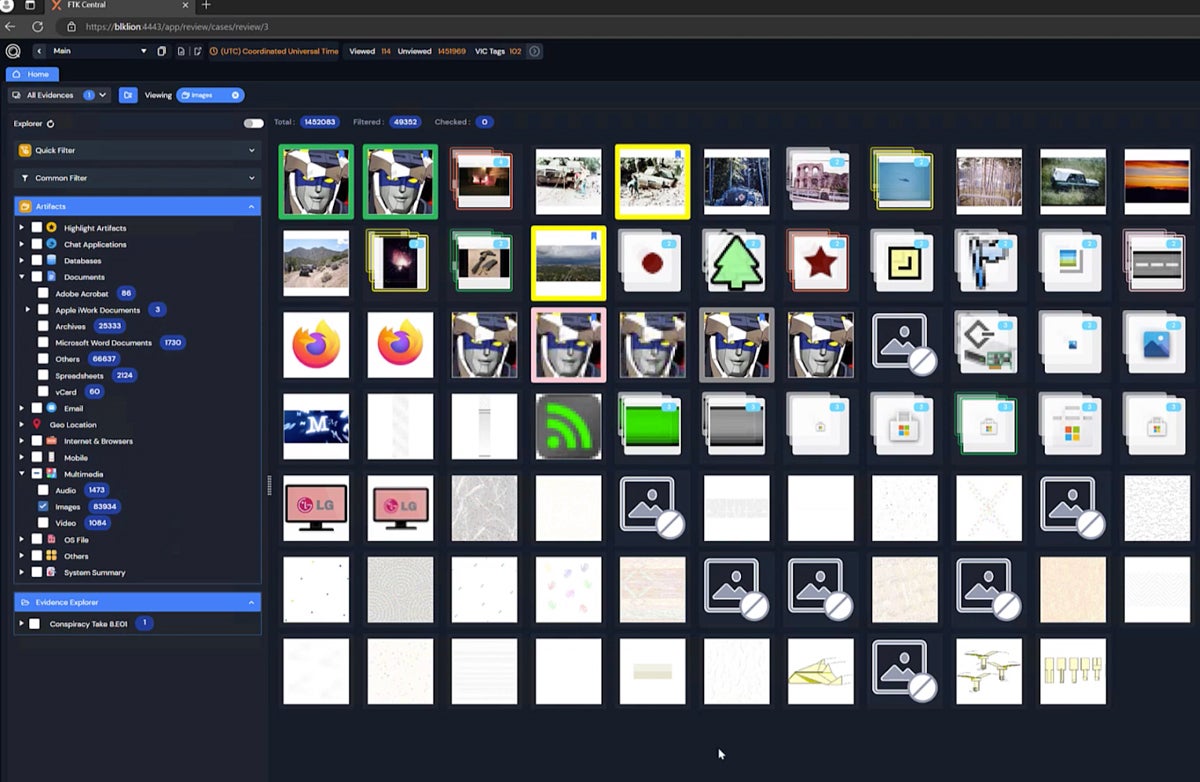
Exterro Forensic Toolkit (FTK) offers advanced digital forensics capabilities for both computer systems and mobile devices, including media thumbnail reviews and facial recognition. Other notable features include remote data collection and file recovery for deleted data. We recommend it for organizations of all sizes for its strong feature set and its pricing information — Exterro is transparent about licensing compared to the rest of the market.
Exterro is a fantastic all-around forensics product, but it’s not very transparent about customer support options. If that’s important to your team, look at LogRhythm instead — it also has plenty of key and advanced forensics features and was our criterion winner for customer support.
Pros & Cons
| Pros | Cons |
|---|---|
| Free trial lasts a month | Unclear customer support availability |
| Supports extractions from mobile devices | Command line interface not available |
| Tech partnership with Palo Alto Cortex XSOAR | Unclear level of cloud app support |
Pricing
- Physical FTK license: $5,999–$11,500, depending on sale prices
- Virtual FTK license: $5,999–$11,500, depending on sale prices
- Yearly renewal: Subscription charges and renews annually
- Free trial: 30 days
Key Features
- Portable cases: Send data about a case to external reviewers and receive feedback.
- Facial and object recognition: FTK identifies identical image content automatically.
- Mac data analytics: Process data like encrypted Apple file systems.
- Thumbnail review: Inspect and categorize multimedia images by hovering over them.

IBM QRadar SIEM & Forensics
Best for Enterprise Forensics & SIEM
Overall Rating: 3.5/5
- Core Features: 3.8/5
- Advanced Features: 3.5/5
- Deployment & Usability: 3.4/5
- Customer Support: 3.7/5
- Pricing: 3.2/5
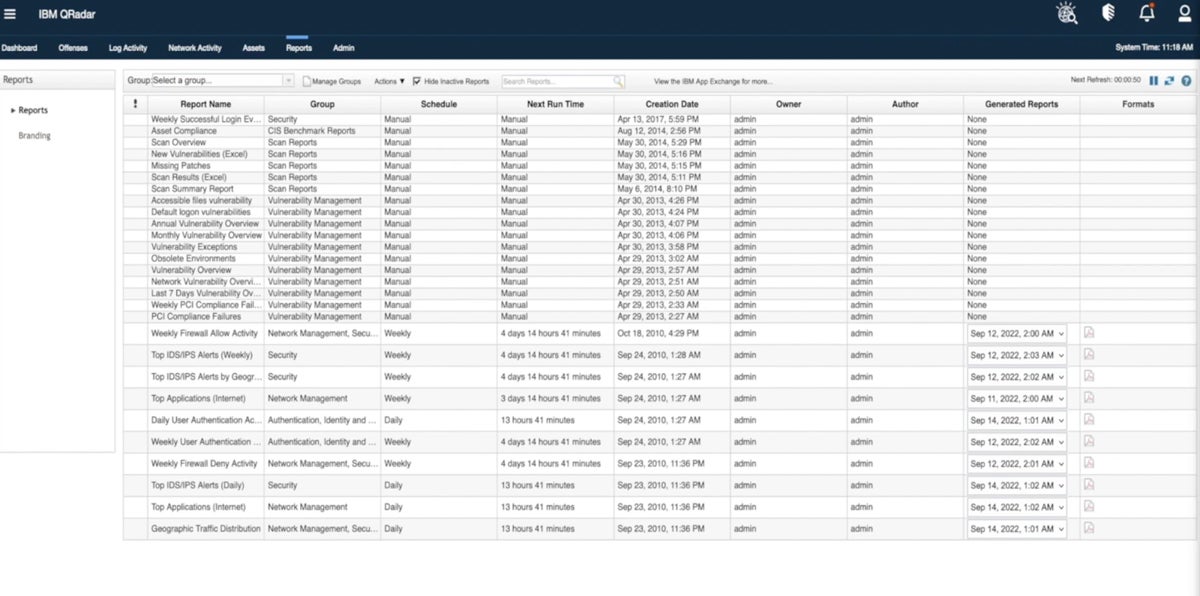
IBM QRadar SIEM is a security information and event management platform that offers capabilities like network analytics, threat response, and compliance audits. QRadar Forensics, which focuses specifically on digital forensics, can be a standalone product, but it’s also available as a SIEM module. Integrating the two is ideal for large enterprises that want to use a security management product and a digital forensics tool in conjunction.
QRadar is a strong enterprise solution, but it doesn’t support many cloud applications. Consider LogRhythm if you’re looking for cloud app support — it’s also a SIEM solution.
Pros & Cons
| Pros | Cons |
|---|---|
| Combines SIEM and forensics in one product | No free trial offered |
| Advanced response features like incident alerts | Can be hard to get initial info from sales |
| IBM provides a pricing calculator | Lacks support for cloud apps |
Pricing
- Usage model: Priced by events per second and flows per minute
- Enterprise model: Based on the number of managed virtual servers used
- Pricing calculator: IBM’s calculator helps estimate initial costs
- Contact for quote: Available add-ons, including Forensics
Key Features
- Network analytics: View network threat detections and dashboard visualizations.
- Compliance add-ons: Use QRadar SIEM extensions to comply with regulations.
- IBM X-Force integration: View recent threat intelligence data like malicious URLs.
- File recovery: The Forensics product finds raw capture data on specified devices.

LogRhythm NetMon & SIEM
Best Forensics Solution for Customer Support
Overall Rating: 3.3/5
- Core Features: 3.3/5
- Advanced Features: 3.6/5
- Deployment & Usability: 2.8/5
- Customer Support: 4.4/5
- Pricing: 1.8/5
LogRhythm’s next-gen SIEM platform integrates with LogRhythm NetMon, a forensics solution for networks that provides packet analytics, dashboards, and application recognition. This integration is another example of combined SIEM and forensics for teams that want those products connected. LogRhythm got particularly high marks in our rubric for its customer support availability, including phone support and a 24/7 platinum plan.
While LogRhythm SIEM is a strong network forensics product, it won’t be sufficient for all forensics cases. Consider Exterro if you need mobile and multi-platform forensics; it also finds indicators of compromise and offers incident response capabilities like LogRhythm.
Pros & Cons
| Pros | Cons |
| Incident response features through SIEM | No free trial and limited pricing info |
| 24/7 support plan available | Lacks mobile device support |
| Good choice for network-focused forensics | Lacks data extraction technology |
Pricing
- Contact for quote: Custom pricing available
Key Features
- Threat scores: A risk-based priority calculator helps teams determine risk significance.
- Application recognition: NetMon identifies more than 3,500 applications.
- Incident response: The SIEM solution helps teams find and remediate security threats.
- Deep packet analytics: Extract and view network packet data from OSI layers 2-7.

Read more about different types of network security, including threat intelligence and network access control.
Cyber Triage
Best Solution for Cybersecurity-Specific Incident Response
Overall Rating: 3.2/5
- Core Features: 3.3/5
- Advanced Features: 4.8/5
- Deployment & Usability: 2.5/5
- Customer Support: 0.9/5
- Pricing: 4.3/5
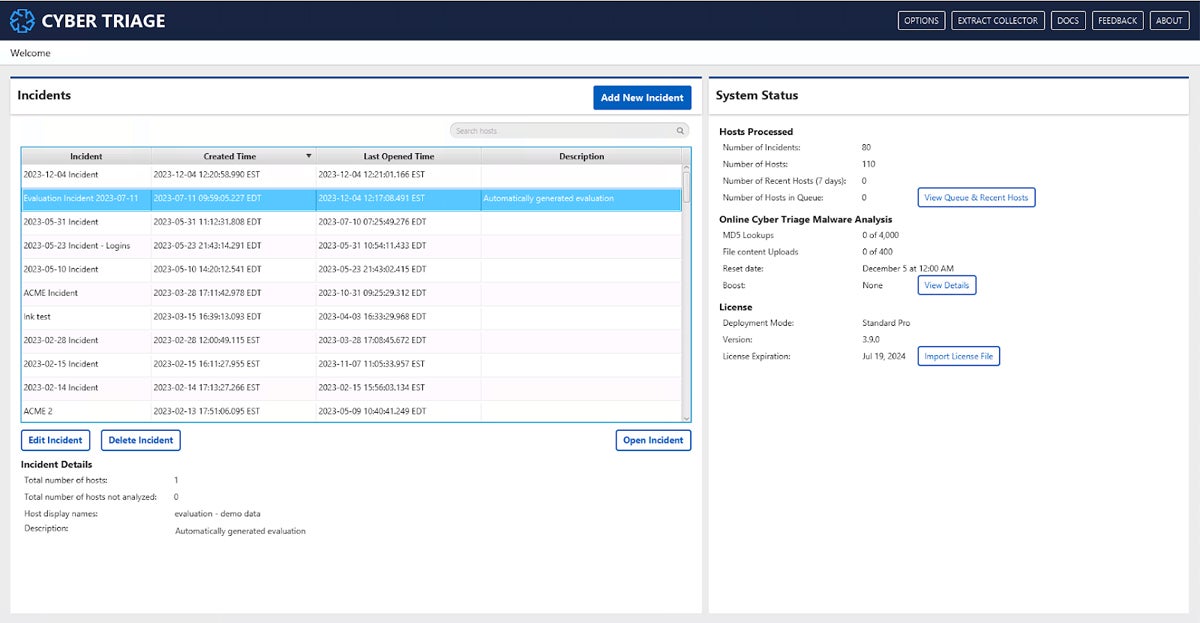
Cyber Triage is a combined forensics and incident response platform that’s great for teams that want to both manage incidents and explore attacks in detail. Key capabilities include malware scanning, artifact scores, and incident response recommendations. Cyber Triage also integrates with endpoint detection and response (EDR) and SIEM products like SentinelOne Singularity and Splunk; consider Cyber Triage if you want those major security integrations.
While Cyber Triage is a strong incident response solution, it doesn’t support mobile devices. Consider Exterro, which offers incident response integrations and collects mobile device data, if you’re looking for both IR and mobile capabilities.
Pros & Cons
| Pros | Cons |
|---|---|
| Can run on a laptop, in the cloud, or on-premises | Limited info on customer service availability |
| Combines incident response and forensics | No cloud app support |
| Integrates with SIEM and EDR | No mobile device support |
Pricing
- Standard plan: $2,500 per year
- Standard Pro plan: $3,500 per year
- Team plan: Custom pricing available
- Free trial: 7 days
Key Features
- Artifact scoring: Cyber Triage helps prioritize incident evidence by ranking it.
- Malware scanning: Over 40 scanning engines increase the chances of finding malware.
- Air-gapped labs: Export hash values into a text file format through offline mode.
- IOCs: Cyber Triage identifies indicators of compromise like signs of potential malware.

Encase Forensic
Best Solution for Managed Digital Forensics Services
Overall Rating: 3/5
- Core Features: 3.5/5
- Advanced Features: 2.2/5
- Deployment & Usability: 3.3/5
- Customer Support: 3.9/5
- Pricing: 2.3/5
Encase Forensic by OpenText is a well-rounded digital forensics tool with multi-platform support, including all three major operating systems and mobile devices. It collects data from social media sites as well as apps like LinkedIn and WhatsApp. Encase Forensic is available as an on-premises managed product. Consider Encase if your business is looking for a managed forensics solution or has a small or inexperienced team; it’s a good choice for small and midsize businesses (SMBs).
While Encase Forensic is a great multi-platform product, it doesn’t offer a free trial. Consider Magnet AXIOM Cyber instead if you need to try a forensics product before buying. Magnet also supports multiple platforms and offers an integration for mobile data, too.
Pros & Cons
| Pros | Cons |
|---|---|
| Investigates Mac, Windows, and Linux devices | No free trial |
| Verakey integration for mobile data extraction | Lacks SIEM integration |
| Remote data collection is available | Availability of some DF features is unclear |
Pricing
- Contact for quote: Custom pricing available; some pricing info available from resellers
Key Features
- Optical character recognition: OCR finds and extracts text data in images and PDFs.
- AI and ML: Identify incriminating content with machine learning and artificial intelligence.
- App activity collection: Supported apps include LinkedIn, Instagram, and Twitter.
- Browser and location data: Encase also collects internet and location history.

Magnet AXIOM Cyber
Best Solution for Diverse Deployment Scenarios
Overall Rating: 3/5
- Core Features: 2.8/5
- Advanced Features: 2.4/5
- Deployment & Usability: 4.4/5
- Customer Support: 3/5
- Pricing: 2.5/5
Magnet AXIOM Cyber’s digital forensics and incident response solution offers features like remote data collection and data visualization. It supports Windows, Mac, and Linux machines, and users can deploy it in both AWS and Azure. Through its integration with Verakey, AXIOM Cyber can receive extracted mobile data as well. For businesses with multiple operating systems and cloud environments, AXIOM Cyber is a great choice.
While AXIOM Cyber is a strong multi-platform forensics product, its data extraction capabilities are limited to other products. Consider Encase Forensic if you’re looking for native extraction; it also supports multiple platforms, including mobile devices.
Pros & Cons
| Pros | Cons |
|---|---|
| Supports Mac, Linux, and Windows computers | No incident alerts |
| Can be deployed in the cloud | Pricing info isn’t transparent |
| Both phone and email support are available | Length of the free trial is unclear |
Pricing
- Contact for quote: Custom pricing is available
- Free trial: Contact for length
Key Features
- Remote collections: You can collect data from off-network endpoint computers.
- Data visualization: AXIOM Cyber shows connections between various artifacts.
- Threat scoring: Integration with VirusTotal allows users to better prioritize threats.
- Incident response: AXIOM Cyber is a DFIR product and offers response and detection.
Top 5 Features of Digital Forensics Software
Digital forensics products vary somewhat in their feature sets, but there are a few core capabilities that your future product should have. Data extraction, reporting functionality, data recovery, prioritization, and integrations with security platforms are all critical to conducting a successful forensics case and tracking the most important information.
Data Extraction
Data extraction pulls information from places it would otherwise be hard to find. If a criminal deletes a file from their computer, it won’t be simple to collect by ordinary means. But a digital forensics product has special capabilities that help it reconstruct or recover data that’s been damaged or deleted, which is critical for cases in which a criminal tried to cover their tracks or information has simply been lost over time.
Reporting
Reporting functionality is important for almost every security product, but for digital forensics, it’s especially critical. Every piece of information could affect not only a company’s security but also a person’s life or livelihood. Reports help users present data clearly to business leaders, but they might also need to be provided to police and government officials.
Data Recovery
Some data appears to be lost, but forensics tools should be able to recover data that wouldn’t be found otherwise. That data could play a critical role in a case, and a threat actor or criminal might have attempted to hide the information. Digital recovery features are valuable and often necessary for a full forensics toolkit.
Threat Prioritization
Prioritizing alerts, threats, or other indicators of compromise take different forms, like threat scores, but a digital forensics tool should have some method of ranking potential issues. With prioritization features, teams will be better positioned to handle the most important alerts or potential cases first.
Security Integrations
Digital forensics tools should ideally integrate with at least one other security product, whether that’s a SIEM, EDR, or other type of incident response product. This product might also be a security management tool that centralizes multiple products. The best integrations depend on your business’s use cases and needs, though, so consider those before making a final selection.
How We Evaluated Digital Forensics Software
We used a product scoring rubric to compare a range of digital forensics tools, developing five main criteria with key characteristics of forensics products. The percentages below show how we weighted the criteria. Each criterion included multiple subcriteria with their own weighting. The total scores reflect how well each product ranked in our overall evaluation based on the criteria it met. After we scored the products, the six that scored best made our list.
Evaluation Criteria
The most important criteria we scored were core forensics features like data extraction and advanced features, like threat scores and SIEM integrations. We also considered deployment and usability, including product documentation, mobile device support, and supported operating systems. Lastly, we looked at customer support availability, including channels like phone and email, and pricing, like free trials and licensing details.
- Core features (30%): We looked at the most important forensics features, like data extraction and reporting functionality.
- Criterion winner: IBM QRadar
- Advanced features (25%): We reviewed products based on advanced capabilities like SIEM integrations and threat scores.
- Criterion winner: Cyber Triage
- Deployment and usability (20%): We evaluated ease of use and deployment with criteria like mobile device and operating system support.
- Criterion winner: Exterro
- Customer support (15%): We scored products based on the availability of phone and email, as well as demos, support hours, and composite user reviews.
- Criterion winner: LogRhythm
- Pricing (10%): We used criteria like free trials, pricing transparency, and license details to score our pricing category.
- Criterion winner: Exterro
Frequently Asked Questions (FAQs)
What Types of Cases Require Digital Forensics Tools?
Any legal investigation involving software, hardware, or networks can require a digital forensics tool to find data that otherwise wouldn’t be retrievable. Extraction capabilities help legal and security teams find information that may have been deleted from a computer system. Common examples of cases requiring forensics tools include embezzlement, extortion, identity theft, assault, or child exploitation, including pornography and any kind of trafficking.
Businesses may want forensics simply for their information security and cybersecurity, too, so they can track intruder and attacker behavior in a clinical way. It doesn’t have to be a legal case — an internal security incident might benefit from forensic data as well.
Are Digital Forensics Tools Difficult to Use?
Like any other software solution, digital forensics tools take time to learn. Some will be simpler to use than others, though. If your business is looking for a particularly easy-to-learn product, look for user reviews that mention usability and features like a central management interface. Any product will have a learning curve, but they differ in length.
What Are Common Digital Forensic Product Capabilities?
Broadly speaking, forensics software should be able to pull data from multiple, difficult-to-find locations and present it so teams can analyze it meaningfully. Many different features serve that purpose, like reporting, data extraction, and remote collection, but distilled into simple terms, your digital forensics product needs to access the right systems, find the necessary data, and help users make sense of it.
Bottom Line: Digital Forensics Software Is a Critical Investment
A digital forensics product can be a powerful tool to not only uncover cybersecurity data but also support your team in a legal investigation. It should suit your security, compliance, and legal teams’ skill sets, as well as give them research and response abilities that may not have been available to them before. If your organization frequently deals with criminal activity or investigations, a digital forensics tool is one of the most important investments you’ll make.
Is your organization looking for specifically Linux-based forensics capabilities? Read about our picks for the best Linux distros for pentesting and forensics next.






