A network firewall is a security tool that employs policies to accept or deny traffic, preventing unauthorized access. It acts as the first line of defense, inspecting traffic to ensure compliance with security standards. Firewalls manage multiple network vulnerabilities. Using reliable network firewall solutions and additional tools, plus adhering to best practices, optimizes the benefits while minimizing its disadvantages, resulting in a stronger network defense.
Why Do You Need Network Firewalls?
Network firewalls provide security not only by monitoring and filtering internet traffic, but also by incorporating advanced features such as automation, integrations, and sandboxing. Modern firewalls can be placed in virtual settings to protect cloud data and remote branches while also incorporating threat information to guard against sophisticated cyber assaults.
By using network firewalls, you can:
- Secure branch offices: Provide critical security for small and home offices to ensure reliable internet connectivity and safeguarding sensitive data.
- Protect low-risk environments: Offer a cheap method of preventing illegal access and mitigating common hazards for businesses using minimal technology.
- Add a layer of defense: Increase the overall security of servers, endpoints, and network segments by adding another layer of protection.
- Control internal network segmentation: Isolate distinct network segments to allow you to regulate access, bandwidth, and prevent malware proliferation.
- Perform early high-throughput filtering: Reduce the load on more advanced security solutions like next-generation firewalls (NGFW) and web application firewalls (WAF).
How Network Firewalls Work
Successful network firewall operation relies on the exact configuration by the IT team, administrators, and endpoint users. The key tasks involve selecting a customized firewall solution. Following the firewall setup, IT teams and admins configure firewall rules and policies. Then, users will initiate steps to protect devices, establish firewall zones, implement access controls, conduct evaluations and tests, and upgrade device settings.
Here’s how you can ensure that your network firewall works effectively:
- Choose a firewall solution: Select the optimal firewall type by considering the client’s needs and previous security difficulties or threats encountered. Choose VPN-capable firewalls for remote access security.
- Secure the device: Assign unique administrator credentials and change simple network management protocol (SNMP) settings to improve your firewall security and overall network efficiency.
- Create firewall zones: Divide the network into zones with specific access rules to establish network security borders. Place your highly confidential data in internal zones to add an extra layer of security against unauthorized access.
- Develop and implement a firewall policy: Configure access control lists (ACLs) with specific parameters for each zone. Document policies so that clients and administrators can easily reference them.
- Test the firewall: Scan for vulnerabilities and perform penetration testing by simulating hacking efforts to confirm that your security measures and your firewall effectively prevent unauthorized access.
- Update the device: Regularly examine firewall logs and update software components to keep cybersecurity defenses up to date. Every six months, reevaluate the ACLs to verify they’re still effective and relevant.
Network firewalls have two categories: hardware and software firewalls. Hardware firewalls are physical components attached to network hardware, such as modems, that protect big networks from severe hacking efforts. Software firewalls are installed directly on computers to protect against low-level attacks by monitoring and filtering application-level traffic, with a focus on illegal login attempts.
When administrators properly manage traffic and set permissions, network firewalls then analyze traffic at the packet level, inspecting headers to ensure data integrity. This will serve as essential tools for securing businesses and devices against unwanted access and improving network security through strict access controls and configuration management.
What Vulnerabilities Do Network Firewalls Protect Against?
Network firewalls are security defenses against vulnerabilities such as backdoors, denial of service attacks, and email bombs. They also guard against macros, viruses, header manipulation, and zero-day vulnerabilities. Effective network protection requires strong settings as well as proactive security measures. The following are some of the most prevalent vulnerabilities that network firewalls guard against.
- Backdoors: Exploit hidden access points in firewall code to bypass security. Regular verification and change management prevent exploitation.
- Denial of service (DoS): Overwhelms servers with unanswerable requests, causing crashes and service unavailability.
- Email bomb: Floods email systems with messages, incapacitating them from handling legitimate emails.
- Header manipulation: Alters packet headers to deceive firewalls, allowing unauthorized traffic. Mitigate by validating and limiting exposure to HTTP header vulnerabilities.
- Macros: Execute harmful actions with malicious scripts in documents or applications, potentially crashing computers or compromising data.
- Remote logins: Compromise sensitive data. Hackers can access files on your device through unauthorized logins.
- Viruses: Self-replicate and cause extensive damage, from nuisance messages to complete system compromise.
- Zero-day vulnerabilities: Exploit unknown to vendors allows attackers to breach systems before patches are available.
What Are the Different Types of Network Firewalls?
Each type of firewall has distinct features tailored to certain security requirements, ranging from basic network firewalls to extensive application-level protection and advanced threat identification. Choosing the appropriate kind is determined by the network environment’s complexity and specific requirements.
- Traditional firewalls: Focus on header inspections. Include packet filtering, stateful inspection, session filtering, proxy service, and deep packet inspection to guard the endpoints and network segments.
- Unified threat management (UTM): Adds more capabilities than the traditional network firewalls. Offer more advanced scanning of the packet headers and perform basic application layer filtering.
- Next-generation firewalls (NGFW): Combine standard functionality with deep packet inspection and intrusion prevention, which are critical for advanced threat security in large companies and high-traffic networks.
- Application layer firewalls (WAF): Secure individual programs by filtering traffic at the application layer, which is critical for web applications and enterprises that handle sensitive information.
- Database firewalls: Apply specialized inspection of HTTP/HTTPS to prevent any database threats. Improve the data throughput and reduce the slowdown brought by large data flow or high traffic.
- Cloud-based firewalls: Offer specialized defense against cloud-based threats by mitigating unwanted access to private networks. Provide visibility and control of network and app traffic across the multi cloud environment.
- Container firewalls: Secure networks for container-based applications. Allow users the layer 7 (application) visibility into Kubernetes environments. Can be deployed with DevOps tools and establish a seamless CI/CD pipeline deployment.
- Firewall-as-a-Service (FWaaS): Provide centralized management of firewalls, delivered through a service subscription. They utilize NGFW capabilities via cloud and deploy agents to endpoint devices.
Firewalls have progressed from the traditional static packet filtering to dynamic packet and application-layer inspection. Now, more modern types of firewalls incorporate unified threat management to improve security against outbound threats such as command and control traffic. However, they can’t address all vulnerabilities, so it’s better to use additional security measures such as SASE, microsegmentation, and more.
Compare the traditional network firewalls with the other common types of firewalls and determine their best applications through our guide.
7 Advantages of Network Firewalls
Aside from their primary function of filtering network traffic, firewalls provide rapid data throughput, cost-effective deployment, and comprehensive protection mechanisms against external attacks and malware. Their capacity to manage network performance and protect cloud storage highlights their importance in modern cybersecurity approaches.
These are the most common network firewall benefits:
- Enhance specialized effectiveness: Improve specialized efficiency by excelling at certain security tasks such as filtering network traffic, enforcing access controls, and identifying malicious activity using established rules and criteria.
- Ensure high speed and data throughput: Process data quickly, reducing the impact of high speed data on network performance and promoting more efficient communication across networks.
- Enable rapid installation and setup: Deploy and configure rapidly, allowing enterprises to implement strong security measures while maintaining business continuity with less inconvenience.
- Protect against external threats: Prevent unwanted access attempts and secure login credentials from being intercepted by malicious actors outside the company, guaranteeing network integrity and privacy.
- Defend against viruses and malware: Serve as a firewall against internet-borne threats by analyzing incoming and outgoing traffic and blocking potentially hazardous content before it enters the network.
- Manage network performance: Monitor and maintain the overall network performance and availability by filtering out unnecessary or dangerous traffic to ensure more effective data processing.
- Secure cloud storage: Stop unauthorized access and safeguard sensitive data stored remotely, hence improving your overall data security and regulatory compliance management procedures.
6 Disadvantages of Network Firewalls
While network firewalls provide significant benefits for network security, they also have drawbacks that businesses must consider. These include limitations in blocking sophisticated attacks to user access restriction. Understanding these drawbacks encourages the use of complementary security solutions that effectively mitigate risks and provide robust protection against newer cyber threats.
- Occasionally fail to block complex assaults: Lack defense against advanced attacks targeting applications or HTML-based threats, leaving it exposed to exploitation.
- Can be misled by manipulated headers: Vulnerable to attacks that manipulate packet headers to evade firewall defenses, potentially allowing unauthorized access.
- Have restricted capacity: Struggle with high traffic volumes, which limits its usefulness in larger or busier networks and impedes smooth operation.
- Require large investment: Cost additional expenses for expert consulting and deployment, making budget allocation difficult.
- Remain vulnerable to malware attacks: Need extra security measures against advanced malware that evades firewall defenses.
- Restrict user access: Limit network access per user, which may slow down processes and lead to exploits that complicate network management.
8 Network Firewall Best Practices
Adopting recommended best practices optimizes firewall performance and overall network security. You can further strengthen your defenses by understanding, implementing, and frequently evaluating these measures. Configuring security settings, employing multiple firewall layers, microsegmentation, following the least privilege principle, monitoring logs, and ensuring reliable backups all give instant protection as well as long-term resilience.
Understand Your Firewall Policies
Start by examining current configurations and mapping network architecture to gain a better understanding of its history and regulations. Analyze the origins of existing regulations, including historical security issues and revisions. Create a comprehensive logging system to frequently analyze and update rules for relevance. Document configurations, network diagrams, and security policies for auditing in order to avoid conflicts and maintain efficiency.
Learn more about creating a firewall policy in our guide, which includes the steps and a downloadable template for your own use.
Configure Security Settings
Set strict rules that allow only pre-approved traffic, which ensures maximum security but may impede workflow. Alternatively, use less specified but rigorous parameters that are aligned with regular actions to balance usability and security. Both techniques seek to protect networks from unwanted access while supporting operational requirements to differing degrees of restriction.
Integrate with Secure Access Server Edge (SASE) Tools
Using SASE, you can combine firewall-as-a-service (FWaaS), cloud access security broker (CASB), and zero trust network access (ZTNA). It improves security event context in real time and lowers management overhead by unifying platforms. SASE, which Gartner expects to be extensively adopted in 2024, provides increased visibility and flexibility to maintain strong security regulations as remote work scenarios become more prevalent.
Use Multiple Firewall Layers
Implementing multiple firewall layers boosts your security posture by configuring perimeter, internal, and application-level to address distinct network threats. Use a firewall administration tool to centralize control and improve management efficiency. Regularly update rules to lower attack surfaces and strengthen defenses against various cyber threats.
Implement Microsegmentation
Microsegmentation restricts user access to specified network segments, limiting unauthorized traversal of the entire network. This improves security by separating important assets and mitigating the consequences of future intrusions. Unlike traditional firewalls, which focus on external threats, microsegmentation provides inside defense, preventing attackers from moving laterally around the network for comprehensive protection against external and internal threats.
Adhere to the Least Privilege Principle
Limit access to the minimum essentials for specified roles. Use NGFWs for identity-based controls to enforce rigorous access regulations. Conduct a firewall audit and update permissions on a regular basis to revoke superfluous access, lower the risk of illegal entry, and align firewall setups with best security practices to avoid future breaches.
Examine Logs & Monitor Activities
To capture and analyze network traffic, enable firewall logging and evaluate it on a regular basis. Set up automated alerts for crucial occurrences and keep logs protected for simple retrieval. Analyze logs to find anomalies, identify threats, and improve firewall configurations. This strategy enhances threat detection, troubleshooting, and overall security by allowing for informed judgments and optimizing firewall configurations.
Ensure Reliable Backups
Maintain consistent backups by routinely saving latest setups and firewall settings. Schedule frequent backups to reduce data loss during system failures or security breaches. Backups should be stored securely and restoration techniques should be tested to verify their usefulness. This method protects against faults, hardware failures, and malicious assaults. Reliable backups maintain continuity and respond quickly from severe events or cyber attacks.
Discover how to improve the security of your network firewall by reading our comprehensive guide to best practices for firewall management.
3 Network Firewall Solutions
Network firewall solutions enhance network monitoring and management accuracy. Leading solutions like Cisco Secure, FortiSASE solution, and Palo Alto Networks NGFW combine advanced network firewall features with other security tools to deliver strong security and comprehensive protection for small to large businesses.

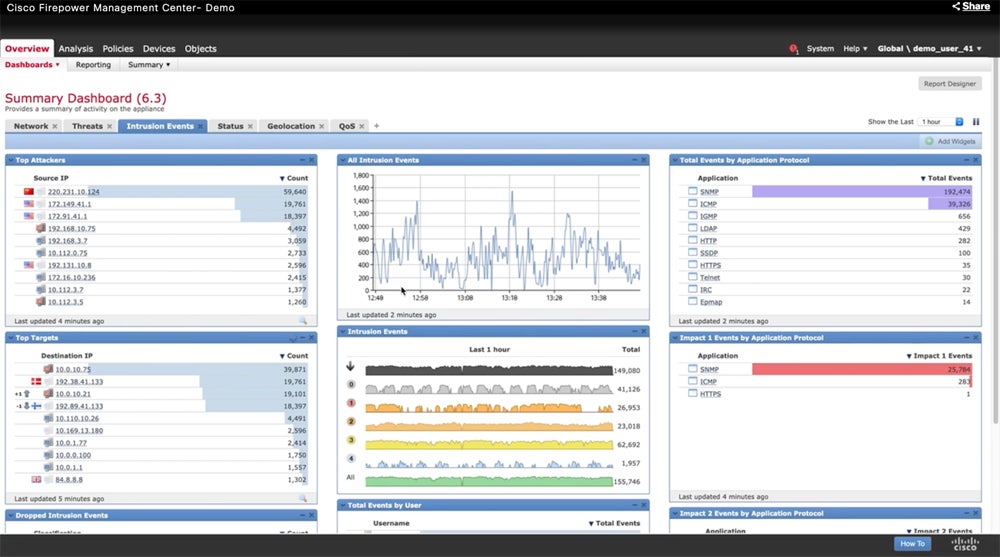
Cisco Secure Firewall
Cisco’s Secure Firewall solution offers advanced protection against emerging risks in data centers, branch offices, and cloud settings. It connects with your current network infrastructure, delivering strong security without sacrificing performance, particularly when inspecting encrypted communications. Cisco’s solutions include a 30-day free trial and a customizable price calculator via AWS Marketplace. Custom quotations are available through Cisco sales.
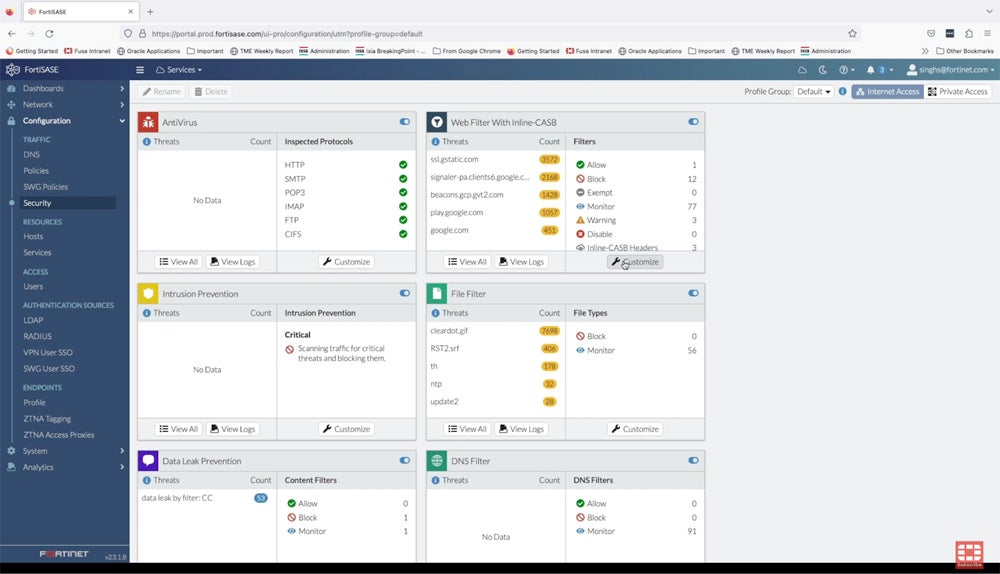
FortiSASE Solution
Fortinet’s FortiSASE solution combines several security features into a single product or modular solution, including FWaaS, NGFW, and secure SD-WAN. It enables secure access to the web, cloud, and apps for hybrid workforces. Fortinet SASE combines security features such as SWG, ZTNA, and CASB into a single OS with centralized control to provide full network protection. Cisco provides free live demos, and custom pricing is available upon request.
Dive deeper into our comprehensive review of FortiSASE to better determine its pros, cons, key features, pricing details, and more.

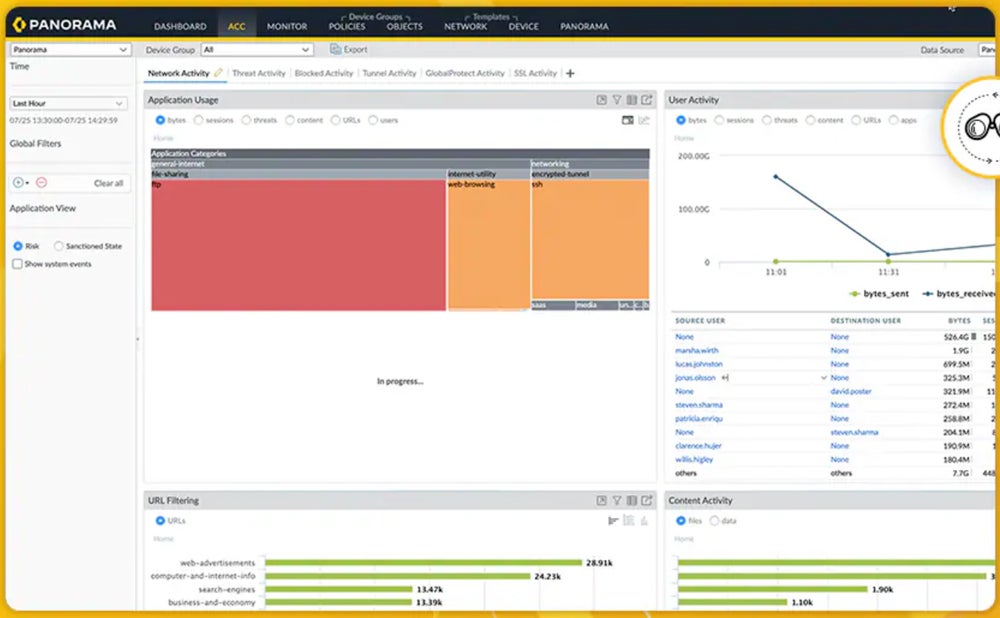
Palo Alto Networks Next-Generation Firewall
Palo Alto Networks NGFW safeguards enterprises through unified security and real-time deep learning. It categorizes all data, including encrypted traffic, based on application, user, and content to enable exact security controls. Its management tool, Panorama, streamlines administration by providing dynamic updates across firewalls, threat prevention, and more. The tool includes a 30-day free trial. You may estimate the pricing via Azure and AWS calculators.
Explore the leading NGFW solutions in our detailed review covering their key features, pros, cons, pricing, and more.
Bottom Line: Enhance Security with Network Firewalls
Traditional network firewalls have been effective, but evolving digital threats demand upgrades. Beyond threat prevention, the increasing network ecosystem, which includes both public and private clouds, presents issues. Network firewalls, including virtual ones in the cloud, are critical to perimeter security. They supplement a broader security approach that includes endpoint, application, data security, policy administration, and operations to provide complete protection.
Aside from firewalls, secure web gateways (SWGs) can also help in network parameters security. Discover their complementary roles and differences in our SWGs and firewalls guide.




