-
Companies Get Better at Fighting Ransomware Despite Escalating Threats
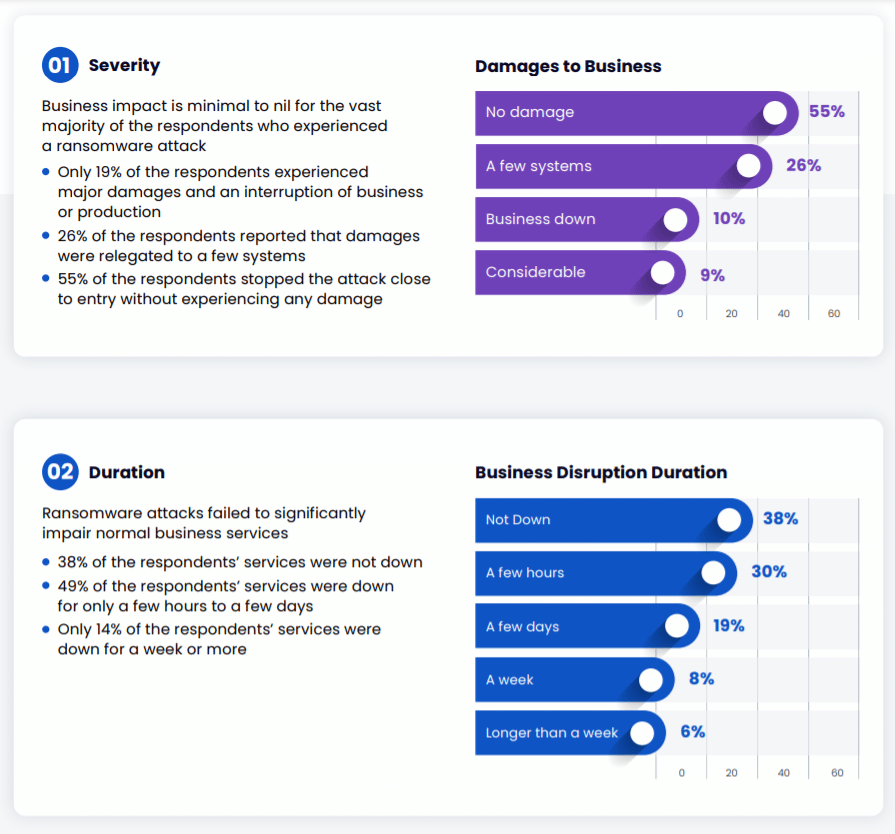
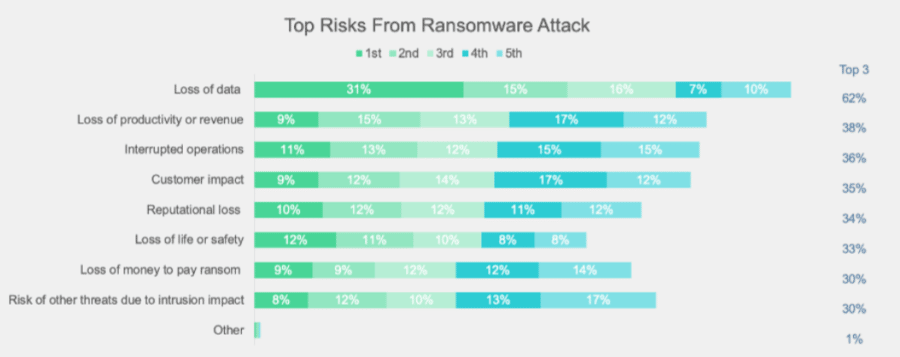
In a year in which ransomware attacks seem to get worse by the day, companies have made surprising progress defending themselves against attacks. But the attention paid to the malware by journalists, cybersecurity vendors and increasingly, government agencies, has pushed companies to improve their preparedness to defend themselves against ransomware gangs, according to a report […]
-
HTML Smuggling Techniques on the Rise: Microsoft
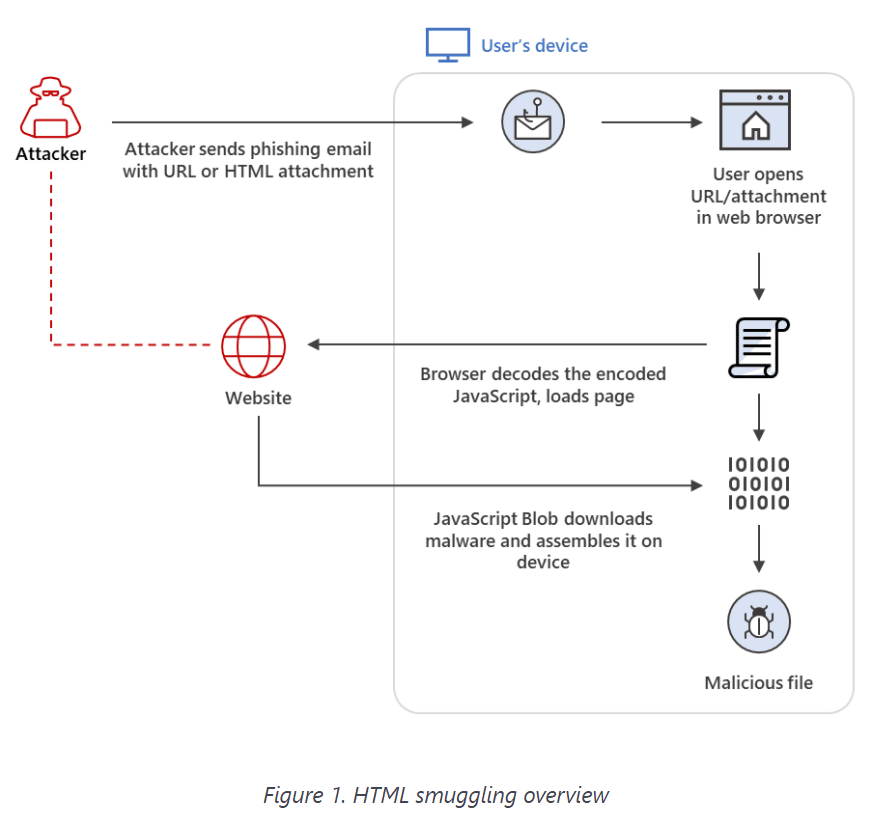
Bad actors are increasingly using a technique called HTML smuggling to deliver ransomware and other malicious code in email campaigns aimed at financial services firms and other organizations, according to Microsoft researchers. In a blog post, the company’s Microsoft 365 Defender Threat Intelligence Team wrote that the highly evasive technique, which is used to deploy […]
-
Hacker Compromises FBI Server to Send Fake Emails
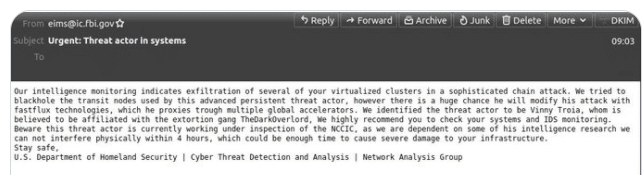
Hackers got into an email server at the FBI over the weekend to spread fake messages in an attempt to blame a cybersecurity expert for non-existent attacks, apparently in hopes of damaging his reputation. According to intelligence organization Spamhaus and subsequent reports, the hackers sent out emails with the false accusations in two waves to […]
-

Arrest in Kaseya Attack Highlights Government Ransomware Progress
U.S. law enforcement officials this week announced the indictments of a Ukrainian national and a Russian citizen in connection with ransomware campaigns by the recently shuttered REvil cybercriminal group, including the high-profile attack on IT software vendor Kaseya earlier this year. The indictments followed an announcement by European officials that they had arrested five REvil […]
-
U.S. State Department Puts $10 Million Bounty on DarkSide Ransomware Group
The United States government is putting a $10 million bounty on the leaders of the DarkSide cybercriminal organization, the ransomware group behind the attack earlier this year on Colonial Pipeline that caused major gas shortages and long lines at filling stations in the Southeast. The reward, announced this week by the State Department, is the […]
-
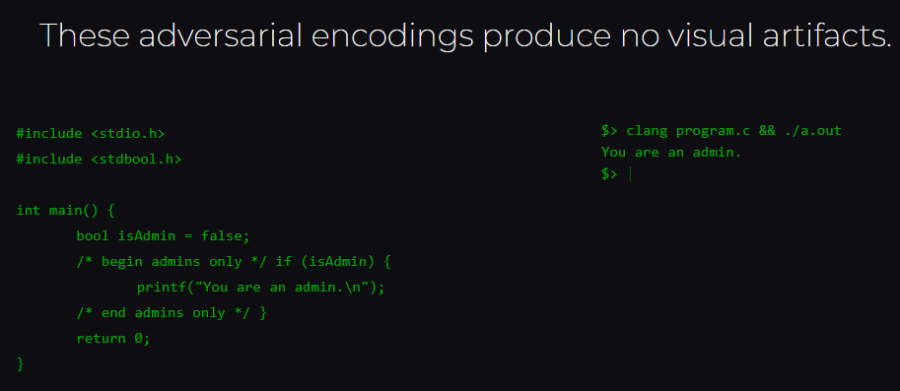
‘Trojan Source’ a Threat to All Source Code, Languages
Researchers have outlined a method that could be used by bad actors to push vulnerabilities into source code that are invisible to human code reviewers. In a paper released this week, two researchers at the University of Cambridge in the UK wrote that the method – which they dub “Trojan Source” – essentially can be […]
-

EU to Force IoT, Wireless Device Makers to Improve Security
The European Union is poised to place more demands on manufacturers to design greater security into their wireless and Internet of Things (IoT) devices. In an amendment to the EU’s 2014 Radio Equipment Directive (RED), the European Commission noted that as wireless devices, from mobile phones to fitness trackers to smart watches, become increasingly embedded […]
-

SolarMarker Attackers Use SEO Poisoning to Push Malicious Code
Cybercriminals leveraging the SolarMarker .NET-based backdoor are using a technique called SEO poisoning to drive malicious payloads into victims’ systems so they can gain access to the credentials and data within. According to researchers at Menlo Security, the SolarMarker campaign is one of two such efforts they’ve seen in recent months using SEO poisoning to […]
-

SolarWinds Attackers Targeting Resellers, Service Providers: Microsoft
The Russian-based cybercrime group responsible for the high-profile attack on software maker SolarWinds last year is continuing to take aim at the global supply chain, according to a warning issued by Microsoft this week. In a blog post, Tom Burt, corporate vice president of customer security and trust at Microsoft, wrote that the hacker group […]
-
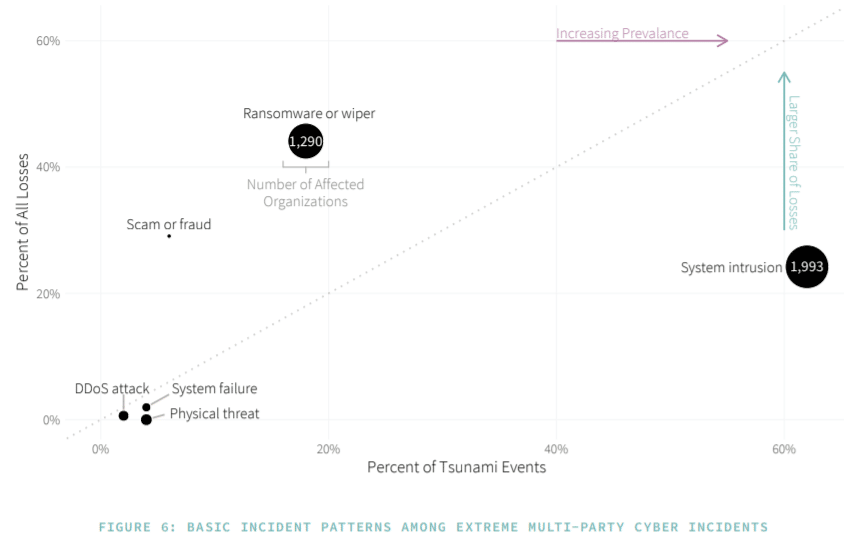
Multi-Party Cyberattacks Lead to Big Losses: Security Researchers
The attacks on SolarWinds and Kaseya over the past year put a spotlight on how an attack on a single company can have downstream consequences on the victim’s partners and customers. The attackers used the entry they gained into the companies to fan out into businesses and government agencies, stealing data and forcing some to […]
IT Security Resources
Top Cybersecurity Companies
Top 10 Cybersecurity Companies
Get the Free Newsletter!
Subscribe to Cybersecurity Insider for top news, trends & analysis





