The European Union is poised to place more demands on manufacturers to design greater security into their wireless and Internet of Things (IoT) devices.
In an amendment to the EU’s 2014 Radio Equipment Directive (RED), the European Commission noted that as wireless devices, from mobile phones to fitness trackers to smart watches, become increasingly embedded into everyday consumer and business life, they also become a greater security risk.
The goal of the amendment – called a “delegated act” – is to ensure that all wireless devices are safe before they are sold in the EU. Manufacturers will be required to adhere to the new cybersecurity safeguards when designing and producing these products. In addition, the amendment also will ensure greater privacy of personal data, prevent financial fraud, and improve resilience in European communications networks, according to EU officials.
“Cyberthreats evolve fast,” Thierry Breton, commissioner for the Internal Market, said in a statement. “They are increasingly complex and adaptable. With the requirements we are introducing today, we will greatly improve the security of a broad range of products, and strengthen our resilience against cyberthreats, in line with our digital ambitions in Europe.”
The U.S. has made some strides on IoT security at the federal level; it remains to be seen if the EU initiative will spur the U.S. to greater action or result in a general improvement in device security.
Common EU Security Standards
It’s also part of a larger EU effort to create a comprehensive set of common cybersecurity standards for products and services that come into the European market, Breton said.
That said, it will take a while for the market to see the results of the amendment, which was announced in late October. It will need the approval of the European Council and European Parliament and then undergo a two-month period of review and scrutiny. Once in place, manufacturers will have 30 months to begin meeting the new legal requirements, giving them until mid-2024 to bring the devices into compliance.
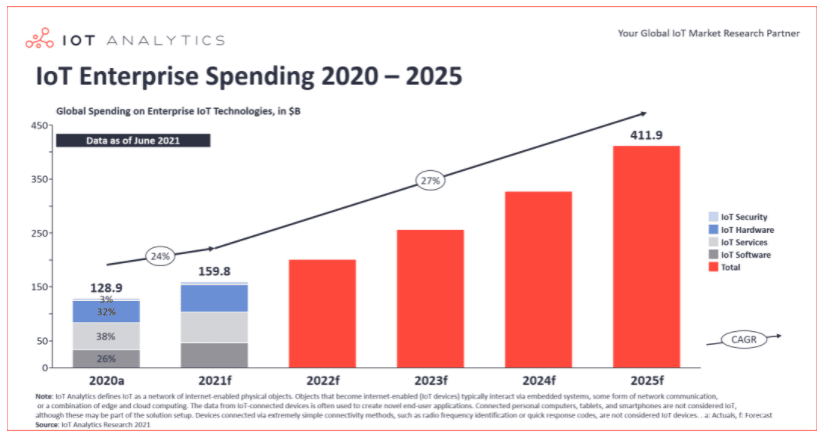
The amendment addresses the ongoing concern about security at a time when the use of wireless devices and the IoT market continue to increase sharply. According to market research firm IoT Analytics, global enterprise spending on the IoT – which includes tens of billions of intelligent, connected devices, from small sensors to large factory systems – is expected to hit $159.8 billion this year, a 24 percent year-over-year increase. In the coming years, it will expand more than 26 percent a year, the analysts said.
In addition, IDC analysts in July wrote that smartphone shipments in the second quarter increased 13.2 percent over the same period in 2020, with 313.2 million devices being shipped.
The adoption of 5G will bring new capabilities to mobile and IoT devices, further driving device growth – and raising new security concerns (see Cybersecurity Risks of 5G – And How to Control Them).
IoT Security Neglected
Many security experts have worried that device makers are more concerned with the features in the devices than with the security. EU officials noted in a statement that the COVID-19 pandemic increased the use of wireless devices for both professional and personal use, and that studies by the European Commission have found “an increasing number of wireless devices that pose cybersecurity risks. Such studies have for instance flagged the risk from toys that spy the actions or conversations of children; unencrypted personal data stored in our devices, including those related with payments, that can be easily accessed; and even equipment that can misuse the network resources and thus reduce their capability.”
None of that surprises John Bambenek, principal threat hunter with cybersecurity vendor Netenrich.
“Many manufacturers of IoT devices do not have experience in IT or system hardening,” Bambenek told eSecurity Planet. “The result has been devices with trivial vulnerabilities or flaws that have been solved for a decade or longer in traditional computing. This problem is compounded by the fact these devices act in the physical world, so the risks can be more profound.”
Also read: IoT Devices a Huge Risk to Enterprises
Device Maintenance Still Needed
Bud Broomhead, CEO at IoT security vendor Viakoo, told eSecurity Planet that while the EU’s initiative will ensure improvements in the initial security of a device, users will need to continue maintaining the systems over time.
“It’s never one and done,” Broomhead said. “New vulnerabilities are created every day by cybercriminals, leading to many IoT devices being installed with out-of-date firmware and other exploitable vulnerabilities.”
He pointed to a FireEye study showing the exploits have overtaken phishing attacks as the top threat to organizations. Given that, designing improved resilience into devices is increasingly important, Broomhead said.
Manufacturers should look at requirements like those in the EU RED amendment as an opportunity – rather than a burden – to build in more cybersecurity features. Bambenek agreed.
“Security has always been a cost to any product or technology,” he said. “Decades ago, we came to terms with the economic concept of externalization — dumping costs on third parties to maximize profits – and now we need to come to terms with risk externalization. No harm from these devices being hacked will fall to the manufacturer even though they are in the best position to address it.”
EU Amendment Applies to Many Devices
The new requirements in Europe will address a wide range of wireless devices, including mobile phones, tablets and other products that communicate over the internet, such as baby monitors and wearable equipment like smartwatches and fitness trackers. The devices will have to include features to ensure the protection of communications networks and ensure that the devices can’t be used to disrupt websites or similar services.
In addition, device makers will have to guarantee features are embedded that protect personal data and the protection of children’s rights will be a key part of the legislation. Other features that will need to be in place will have to minimize the fraud risk that comes with making electronic payments, such as better authentication control.
The amendment dovetails with the EU’s Cyber Resilience Act, which was announced recently by European Commission President Ursula von der Leyen, which would cover more products.
Both Bambenek and Broomhead said the rapid and automated update of device firmware should be required and that default or easy-to-guess passwords should be eliminated. Bambenek also said insecure remote access should not be allowed and there should be highly controlled restrictions on third-party apps. Access to user data also should be controlled and audited. Broomhead said the devices should be part of a zero trust model and that a way to deploy and manage certificates should be used to authenticate device identity.
He also said that both cyberthreats and the use of IoT devices are global issues and that a worldwide collaboration and sharing of best practices is needed to defend against bad actors. Bambenek added that the United States would do well to learn from what European lawmakers are doing.
“The EU has always had a stronger view of privacy than the U.S.,” he said. “Many of our tech leaders have openly said there should be no privacy rights. The U.S. needs to relearn the economic lessons of 100 years ago when it comes to letting corporations dump its costs on society.”
Further reading: Mobile Malware: Threats and Solutions








