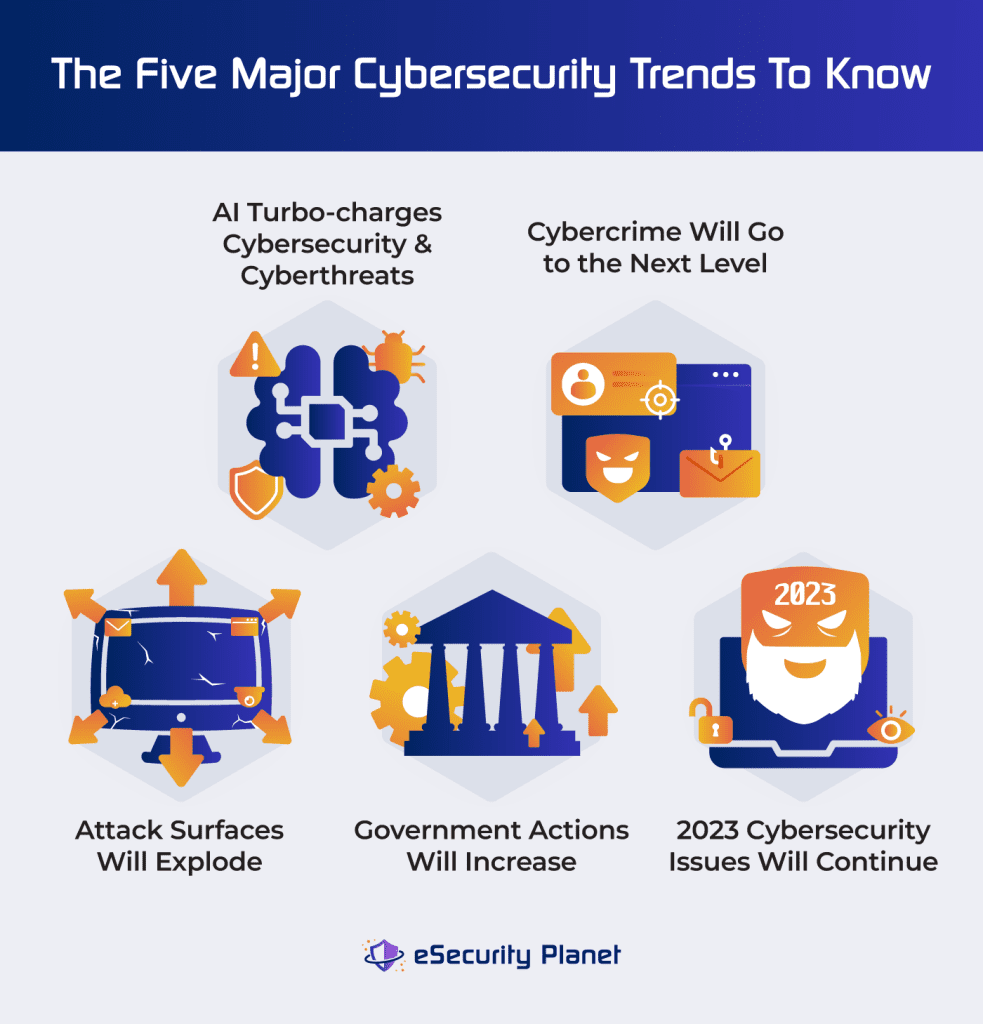
As we’ve made our way through 2024, it’s helpful to consider the events of the past couple years and developing trends in the cybersecurity industry. After receiving input from industry experts and doing my own analysis of the year’s driving forces, I identified five major cybersecurity trends. We need to consider how each of these trends may affect our organizations and allocate our budgets and resources accordingly:
- AI-charged cybersecurity and cyberthreats: Artificial intelligence (AI) will boost both attackers and defenders while causing governance issues and learning pains. Read more.
- Next-level cybercrime: Cyberattackers will implement improved skills, “shift left” attacks, and shifting strategies to adjust to evolving cyberdefense. Read more.
- Exploding attack surfaces: Cyberdefense complexity will compound as API, cloud, edge, and OT resources add to the list of assets to defend. Read more.
- Increased action from governments: Expect more government regulations, state-sponsored cyberattacks, and increased documentation required to protect CISOs. Read more.
- Last year’s security issues continue: Weak IT fundamentals, poor cybersecurity awareness, and ransomware will still cause problems and make headlines. Read more.
- Bottom line: Prepare now so you’re ready to manage your team’s risk. Read more.
AI-Charged Cybersecurity & Cyberthreats
For better or worse, the development of artificial intelligence (AI) has continued to accelerate. Various forms of AI, such as machine learning (ML) and large language models (LLM), already dominated headlines throughout 2023 and continue to present both overhyped possibilities and realized potential in 2024. Industry experts recognize that AI will require governance action, cause learning pains, and will be used to both improve and weaken cybersecurity.
AI Governance
Regardless of any positive, negative, or neutral attitudes towards AI, all organizations will need to develop an official stance, develop policies, and apply those policies consistently. Without guidelines, organizations risk unfettered use of AI, risks of data leaks, and no recourse for unethical AI use within the organization.
Sharad Varshney, CEO of OvalEdge, put AI use in a familiar framework. ”The same issue that faces generative AI-based innovations is the same for everything else: all roads in anything IT-related start and end with data — the most critical component of every system,” he said.
“Organizations faced similar security visibility and control challenges with SaaS apps like Box or Dropbox,” added Kunal Agarwal, founder and CEO of dope.security. “Organizations will look to understand what apps employees are using, evaluate whether they should be paid for by the company (to control), accept the risk, or block the app… the company can choose to educate (through a warning page) or block the app entirely.”
“AI-related innovations will create new possibilities we’re not even considering at the moment,” cautioned Manny Rivelo, CEO of Forcepoint. “Moving forward, organizations of all sizes will need to create and expand corporate AI policies that govern how employees can interact safely with AI. And AI security policies will need to extend beyond commercial AI tools to also cover internally-developed GPTs and LLMs.”
For more on governance and policies, check out our article on IT security policies, including their importance and benefits, plus tips to create or improve your own policy. Also consider learning about the top governance, risk, and compliance tools to identify the best one for you.
Dangers of Using AI
As with any emerging technology, many organizations should expect errors and growing pains as teams learn the nuances of applying the technology. Yet these dangers can be offset through training to minimize issues.
Phil Nash, developer advocate at Sonar, cautioned that “successes from using AI tools to write code will lead to overconfidence in the results, and ultimately a breach will be blamed on the AI itself.”
“Before companies can effectively and safely use generative AI tools, employees must be educated on utilizing best practices: writing prompts that achieve desired outcomes, keeping data security and privacy in mind when inputting data, identifying the quality and security of AI, verifying AI output, and more,” said Arti Raman, CEO of Portal26.
AI-Improved Security
Many vendors began marketing AI-enhanced products years ago, and experts see continuing development of AI as an advantage for improved cybersecurity.
Aiden Technologies CEO Josh Aaron predicted that AI will “enhance the effectiveness of software patch management among security professionals [by] leveraging AI for risk assessment and prioritization in patch management [and] a move towards systems that not only detect vulnerabilities but also autonomously determine the best ways to remediate them [by] employing machine learning algorithms.”
Similarly, Mike Anderson, CIO and CDO of Netskope, saw more general benefits. “In the coming year, I think we will see generative AI be used to analyze a company’s existing policies, regulatory requirements, and threat landscape to generate tailored security policies. I also think we will also see generative AI used to continuously monitor a company’s network and systems for policy violations and automatically respond to issues.”
AI-Powered Cybercrime
Despite the advancements in using AI to improve security, cybercriminals also have access to AI and language learning models. Expect cybercriminals to embrace the power of AI to enhance their threat capabilities.
Melissa Bishoping, director and endpoint security research specialist at Tanium, emphasized the importance of personal contact to avoid falling for deepfake scams. “If someone contacts you to perform a personal or professional transaction, it is always better to seek additional verification when you are unable to physically verify the individual over the phone,” she said.
“Often, just hanging up and calling a known, trusted contact number for the ‘caller’ who reached out to you can expose the scam. In business, establishing workflows that rely on more robust forms of authentication that cannot be spoofed by an AI – FIDO2 security tokens, multiple-person approvals and verifications are a good place to start.”
In addition to enabling cyberattacks, AI will also be used to create more believable disinformation to attack both governments and businesses. Andy Patel, researcher at WithSecure, said that “AI will be used to create disinformation and influence operations in the runup to the high-profile elections of 2024. This will include synthetic written, spoken, and potentially even image or video content.
“Disinformation is going to be incredibly effective now that social networks have scaled back or completely removed their moderation and verification efforts,” he added. “Social media will become even more of a cesspool of AI and human-created garbage.”
Next-Level Cybercrime
While cybercriminals have always shown strong adaptability and opportunism, experts expect attackers to further develop their capabilities and strategies throughout 2024. Some attacks will be aided by technology, while others will be more strategic in nature as companies strengthen cyberdefense against older attacks. Threat actor strategies include using the dark web, exploiting development environments, and capitalizing on both old and new vulnerabilities.
Improved Attacker Skills
In addition to the use of AI, we should expect cybercriminals to incorporate their access to dark web information to make attacks much more believable and widespread.
“While AI is still in the early stages of precisely answering questions, it has reached a sophisticated level in generating text in multiple languages, surpassing the well-known limitations of existing translators,” explained Alessandro Di Pinto, Director of Security Research, for Nozomi Networks. “The emergence of AI as a tool for crafting convincing text circumvents [grammar errors], significantly enhancing the likelihood of success in such attacks.”
Deepfakes will likely play a part in this AI-assisted approach to scams, too. “The use of deepfake techniques in fraudulent activities… will elevate the sophistication of phishing fraud, making it increasingly challenging for users to distinguish between legitimate services and scams,” said Ricardo Villadiego, founder and CEO of Lumu.
If AI models have access to dark web data, they’re much more prepared to be convincing. “By training such models with PII data that is readily available on dark web marketplaces, attack lures that are much more personal and enterprise specific can be created at scale,” concluded Eric George, the director of solution engineering for digital risk and email protection at Fortra.
“In addition to being more believable, detection evasion tactics ensure that the attacks only present themselves to the intended target and otherwise “play dead” for detection processes. This combined increase in plausibility and deliverability increases the attacker ROI as well as the damages incurred.”
The ability to detect AI-based attacks, particularly ones that use evasion tactics, will become a critical requirement for security services like EDR.
Cybercrime Shifts Left
As development and operations (DevOps) uses automation to transition to development, security and operations (DevSecOps) attackers find themselves with less human error to exploit. Recent successes with poisoned open-source libraries and other development channels to deliver malware will continue to influence attacks deeper into the development supply chain for both traditional and new technologies.
Mario Duarte, VP of Security at Snowflake, saw that “attackers are now looking for ways in through developer environments, because that’s where human mistakes can still be discovered and exploited, and we’ll unfortunately see this escalate as suspicious actors become increasingly mature in the coming year.
“Because the threats originate in the code, they’re that much more challenging to uproot. “It’s harder for security teams to defend against such attacks, and it’s even more challenging to create baselines for acceptable development activity than for an automated, well-managed production environment,” Duarte said.
Javed Hasan, CEO and co-founder of Lineaje, offered a blunt warning: “The best time to compromise AI is when it is being built.” He claimed it’s most vulnerable during the development phase.
“Like today’s software, AI is largely built using open-source components,” Hasan said. “Identifying who created the initial AI models, what biases are embedded, and which developers were involved with what intentions are crucial for closing gaps in an organization’s security posture.” Least privilege access is critical here — only a few people should be in charge of model development, and they should carefully document their work and be closely supervised.
Dmitry Sotnikov, CPO at Cayosoft, emphasized the effect of attacks on the software supply chain. “In the first half of 2024, we’ve witnessed how consequential software and service supplier downtime can be to businesses and lives dependent on their uptime,” he said.
“The most glaring example is Synnovis, a pathology service whose downtime in June has exposed 400GB of patient information and postponed thousands of London-based outpatient appointments and cancer treatments. The compromise of dealership management system provider CDK effectively crippled 15,000 car dealership operations across the US.”
Sotnikov also addressed the importance of secure identity systems in protecting supply chains. Identity systems are one of the biggest targets for attackers because they provide so much useful data to navigate and access company resources.
“If you are forced to do one thing to improve your resiliency here, the most impactful would be implementing a modern recovery system with a daily tested process to create and test a safe isolated standby replica of your Active Directory,” Sotnikov said about protecting identity systems from attacks. “This would allow you to instantly switch back to the standby, unaffected version of your Active Directory in the event of a successful attack.”
Shifting Strategies in Response to Shifting Security
As cybersecurity teams eliminate vulnerabilities and add security to block current attacks, cybercriminals will adjust to attack easier targets or change tactics. This includes exploiting older vulnerabilities as well as capitalizing on newer strategies. Recently, security researchers have found flaws almost two decades old that threat actors could still exploit if they chose to; they may aim for this low-hanging fruit as well as attacking newer systems.
Ricardo Villadiego, founder and CEO of Lumu, expects passwordless architecture adoption to increase as organizations work to fight phishing campaigns. “However, this disruptive change from traditional models will prompt a change in the focus of phishing campaigns to bypass these new architectures,” Villadiego said.
“In response, adversaries will increasingly target obtaining complex variables from the device’s environment, which they will use to bypass new authentication methods.”
Joe Payne, president and CEO at Code42, believes biometrics will trigger a shift to insider threats. “As organizations quickly adopt technologies like Okta Fastpass, which uses biometrics for authentication instead of passwords… we expect an increase in two areas: breaches caused by social engineering (already on the rise), and breaches caused by Insiders (already over 40% of all breaches).
“Insiders who have legitimate access to source code, sales forecasts and contacts, and HR data continue to take data from organizations when they depart for competitors or start their own companies,” Payne said. “As we reduce the ability of hackers to access our data using weak passwords, the focus on solving the insider problem will become more pronounced.”
Authentication continues to gain importance and technology continues to develop new MFA options and passwordless-options such as passkeys.
Exploding Attack Surfaces
Even as AI turbocharges attack and defense and cybercriminals expand their capabilities, the attack surfaces that security teams need to defend will grow at a rapid pace – well beyond standard network security. New and formerly overlooked technologies and connections will become targeted by specialized cybercriminals seeking poorly defended API, cloud, edge, and OT resources.
API Attacks
Application programming interfaces (APIs) provide automated and regularly trusted connections between applications and resources. Andy Grolnick, CEO of Graylog, cautioned teams about increasing attacks against them.
“In 2023, ransomware is still the dominant threat in the minds of security teams,” he said. “However, 2024 will be the year that API security preparedness and threats gain momentum. Security APIs are a challenge because they are:
- Simple to navigate and an easy attack
- Dark, hidden and hard to track unlike movements on the Web
- Internal responsibility is not always clear and CISOs haven’t largely set strategies and ownership.”
Cloud Risks
The continuing rise in cloud adoption will also expand the attack surface and increase interest for cybercriminals to attack cloud resources. Organizations will need to consider specialized cloud security tools and implement cloud security best practices.
Neeraj Singh, senior security researcher at WithSecure, saw “an increase in activities that introduce new technologies and processes that haven’t been thoroughly secured. Cloud services, with their new interfaces, APIs, and communication channels, offer additional targets for attackers, thereby expanding the potential attack surface.”
“Third-party risk will evolve as a big data-security-related challenge in the coming year as organizations of all sizes continue their transition to the cloud,” said Mike Scott, CISO at Immuta.
“It’s clear teams can’t accomplish the same amount of work at scale with on-prem solutions as they can in the cloud, but with this transition comes a pressing need to understand the risks of integrating with a third party [cloud provider] and [to] monitor that third party on an ongoing basis.
Cloud security has been a hot topic for years, but as more workloads shift to the cloud, the opportunities for threat actors increase. Before migrating data and applications to a third-party provider, teams will need to make sure their business is taking any necessary protective measures before moving the data. This includes asking probing questions about the cloud provider’s security processes.
Chen Burshan, CEO of Skyhawk Security, envisioned a “rise in cloud-native security incidents that have no perimeter and multiple attack vectors. This is going to shift the market perception because enterprises will realize that no matter how thoroughly they secure the perimeter, threat actors will get in,” Burshan said.
“Cloud security posture management and cloud native application protection will not prevent a breach, and it will not detect a threat in real time. This will increase the maturity of current security practices and accelerate the adoption of solutions like cloud investigation and response automation and cloud-native threat detection and response.”
Edge Exposure
Even as attackers pursue API and cloud attacks, more organizations push out computing to edge resources beyond any network controls. While many envision attacks on smart cars and surveillance cameras, servers exposed to the demilitarized zone (DMZ), such as MoveIT servers, also provide tantalizing edge targets.
Stephen Robinson, senior threat intelligence analyst at WithSecure, noted “the recent MoveIT compromise by the ransomware group Cl0p will begin to inspire more mass exploitation campaigns targeting edge data transfer servers in a similar vein. MoveIT was typically used for reliable transfer of large volumes of important files between organizations.
“Cl0p exploited MoveIT servers to gain access to and exfiltrate these important, valuable files,” Robinson said. “For a ransomware group, access to large volumes of valuable data is the end goal; they had no need to go further into the network than the exposed, vulnerable MoveIT servers. I expect to see more copycat attacks where the value is the exploited server itself, not the access it provides to the rest of the network.”
OT Exposure
Operational technology (OT) used to be unconnected and safely ignored by cybersecurity teams. However, the rise of connected industrial motors, sensors, and industrial control systems (ICS) now provides a tempting target with less mature security.
Edgard Capdevielle, CEO of Nozomi Networks, declared, “We’re at risk of the next Colonial Pipeline. Cyber attacks against critical infrastructure are too easy – we’re still vulnerable and unprotected. If this isn’t more widely spoken about or prioritized, there will be another attack on critical operational technology systems within the country, targeting an industry such as oil, energy, hospitals, or airports.”
The ransomware attack on Colonial Pipeline exposed overlooked OT security and the potential disruption to US infrastructure from a single failure. This event subsequently led to an executive order and guidance on ransomware in 2021.
Increased Action From Governments
As technology progresses at a rapid pace and cybercrime strikes out at an ever-expanding landscape of opportunities, governments will attempt to regulate, influence, and exert control over the cyber sphere.
Increasing Regulation
Decades of use and abuse of computer systems led to early regulation, such as Europe’s General Data Protection Regulation (GDPR) adopted in 2016 and California’s Consumer Privacy Act (CCPA) passed in 2018. This year sees the first enforcement of two new laws in the European Union: the Cyber Resilience Act (CRA) and The Network and Information Systems Directive (NIS2).
While the EU leads in regulation, the US will also exert regulatory influence. “In the next year, we expect a regulatory surge that CISOs must prepare for – which could include continued AI regulation, new post-quantum guidance, and, in late 2024, new legislation is expected around Know Your Customer (KYC) guidelines,” cautioned Jordan Avnaim, CISO at Entrust.
“Businesses should consider each of these a call to action to improve not only their own cybersecurity strategies, but also to consider the impact of new technologies, like AI, on their organization and their customers… CISOs and leaders will need trusted advisors, sound support, and secure solutions to successfully and safely forge ahead.”
Matthew Corwin, Managing Director of Guidepost Solutions, added that “security teams must navigate new breach reporting landscapes shaped by the SEC’s four business day rule for material cybersecurity incidents, state PII breach notification laws, and other regulatory requirements.
“These regulations underscore a shift towards rapid, transparent incident disclosure, emphasizing the need for advanced detection, streamlined reporting processes, and comprehensive incident response strategies.”
Incoming regulations have yet to be tested and well understood, but the well-established GDPR and similar regulations can provide a basic understanding of the methods needed for basic compliance requirements.
State-Sponsored Cyber Attacks
Even as administrations launch regulations designed to influence corporate behavior, other governments will sponsor cyberattacks to push their influence. Stephen Helm, product marketing director at Nisos, warned teams about what state-sponsored attacks will look like.
“As geopolitical waters become more turbulent, and with the US election season fast approaching, China, Russia, and Iran promise to redouble their efforts to sow confusion and discord across the globe as they further their own goals of expanded influence,” he said. “The use of sockpuppets, comment spamming, and bots to amplify narratives will continue to evolve to be more difficult to detect, thanks to AI and other tools.”
“Influence operations in Latin America in 2022-2023 demonstrate this evolution. The China News Service used to hijack permissions to invasively access and potentially take over subscribers’ Twitter, Sina Weibo, and Weixin accounts to push pro-Beijing content… Companies offering election manipulation services that leverage fake social media accounts, AI, and other digital assets now operate as legitimate businesses in some parts of the world.”
Over the past two years, attacks by Russia, China, Iran, and North Korea exploited vulnerabilities and created enormous challenges for public and private organizations of all sizes. Reading up on past attacks can provide hints for tactics and the speed at which nation-sponsored attacks can occur.
Increased Need for Regulatory Documentation
In addition to regulations and direct government actions, experts expect more enforcement from the US Security and Exchange Commission (SEC) and other agencies on recently passed legislation or rules. Cybersecurity teams need to improve documentation to defend themselves and their teams.
Nicole Sundin, CPO of Axio, predicted that “CISOs will need a system of record to protect themselves from the fallout of breaches. It’s no secret that the SEC now holds CISOs accountable for the risks organizations take. Currently, CISOs … make difficult choices, and act as they see necessary—but these may or may not be documented.”
Matt Wiseman, Senior Product Manager of Opswat, extended the warning to documenting third parties and the software bill of materials (SBOM). “Greater requests for SBOMs and more demand to understand tools at a deeper level will lead to increased requirements from regulatory organizations or government agencies,” Wiseman said.
“Given the growing concern for threats from vendors, third-parties, or nation-states, all software will be more thoroughly vetted before being deployed in critical areas.”
Last Year’s Cybersecurity Issues Continue
Some 2024 predictions simply acknowledge the continuing trends that started well before this year. The trends of weak security foundations, poor cybersecurity awareness, and ongoing ransomware attacks remain a major focus until these trends can be mitigated.
Weak Security Foundations
Even as vendors and technologies race ahead to tackle next year’s threats, many organizations lag in basic cybersecurity fundamentals such as asset management, identity, access management, defense in depth, and cybersecurity awareness and training.
“Some of the foundational requirements for securing an organization will continue to challenge InfoSec leaders – primarily, establishing comprehensive visibility into all assets and tight control over who can access them and with what level of privileges,” said Vinay Anand, Chief Product Officer of NetSPI.
Yaron Kassner, co-founder and CTO of Silverfort, added that “compromised identities will remain a favored weapon for cybercriminals. Countless organizations struggle to modernize their access systems amidst legacy constraints and a tangled web of identity providers.” It’s challenging to streamline access security when different teams have been using different strategies over decades.
“We are beginning to see a shift in cybersecurity investment strategies that better reflect the current threat landscape,” said Roman Arutyunov, co-Founder and SVP of products at Xage Security.
“Companies are recognizing that threat hunting and responding to endless detections and false positives uses too much of their precious security resources and they’re growing tired of chasing needles in a haystack. They are now turning their attention to reducing the attack surface by proactively protecting their assets.”
Poor Cybersecurity Awareness
Just as sexual harassment and anti-bias training continue to be a human resources priority, basic cybersecurity training must also become a regular fixture in the professional landscape.
Frank Gartland, chief product and technology officer from Skillable, reminded security teams that “eight-in-ten cyber-attacks occur due to human error, so providing people with regular cybersecurity training can make a significant difference to your cyber resilience.”
Nick Carroll, cyber incident response manager at Raytheon, noted an even broader need for a security culture. “Without a solid security culture at the foundation, security tools, such as expensive firewalls or endpoint detection and response (EDR), will ultimately become ineffective down the line,” he explained.
“If organizations haven’t already, they must begin to build cybersecurity awareness among employees and third-party partners, while also determining the best path for how to integrate security into the organization’s culture and operations.”
Continued Ransomware Attacks
Ransomware began dominating headlines during the pandemic and has only continued to be a problem. Desperate organizations, against the advice of law enforcement, continue to pay ransoms and fuel interest for cybercriminals.
Raffaele Mautone, CEO and founder of Judy Security, anticipated trouble for even small and medium-sized businesses. “Ransomware attacks will continue to diversify their targets, expanding beyond large enterprises to encompass small and medium-sized businesses, municipalities, and healthcare institutions. This trend will lead to a surge in attacks on SMBs, who may be more vulnerable due to limited cybersecurity resources.”
Kev Breen, director of cyber threat research at Immersive Labs, recommends preparing for the worst. “We should expect to see ransomware groups leveraging new techniques in endpoint detection and response (EDR) evasion, quickly weaponizing zero days and as well as new patched vulnerabilities, making it easy for them to bypass common defense strategies.
“As a result, security teams can’t rely on an old security playbook. Companies should not worry about how they can detect everything, and instead just assume at some point it will go badly [and] have plans in place to best respond.”
Ransomware requires access to endpoints to strike. While advanced attackers will seek novel evasion tactics, we can’t make their job easy by deploying sloppy cyberdefense. Consider implementing strong endpoint protection (antivirus, EDR, or XDR) as one of many layers of defense against ransomware and other attacks.
Ransomware has become a popular topic for media and podcasts. If you’re interested in hearing more about major security trends, check out our guide to the best cybersecurity podcasts for both amateurs and experts.
Bottom Line: Prepare Now Based on Risk
Predictions by experts deliver value only if acted upon. While none of these major trends for 2024 can be guaranteed, all of them are possible, and the continuing headaches already plague many organizations today.
Each organization must analyze each trend’s specific risk to the organization and its most valuable assets. The completed analysis will naturally define the trends most likely to cause issues and the ones most urgent to address.
For resources to help manage the risks your organization has identified, read our article on the best tools for risk management.




