Linux has an extensive range of open-source distributions, and a number of those distros have been developed primarily for cybersecurity uses. Linux forensics and pentesting distros have been developed with pentesters, ethical hackers, network defenders and forensic investigators in mind.
These professionals use them in their work, whether for pentesting, digital forensics or other cybersecurity uses.
Each distro has a specific Linux kernel design and comes with its own package manager. They can be broadly classified as:
- Debian-based distros: These are based on the Debian Project such as Kali Linux and ParrotOS.
- Arch-based distros: These lightweight but technical distributions are aimed at experienced users, among whom they are very popular.
- Computer forensic distros: These Linux forensic distros are aimed at the challenging field of computer forensics and retrieving meaningful information from tons of data.
- Other pentesting OSes: While some of those above are used widely by pentesters, there are a couple of other Linux distros that are used by experienced pentesters.
Here are eight of the best Linux distros for cybersecurity use cases, for beginners through advanced users, along with some issues to consider as you select a Linux security distro or a Linux forensic distro.
Also see the Best Penetration Testing Tools and the Best Open Source Pentesting Tools
Kali vs. Parrot: Debian-based Distros
Both Kali Linux and Parrot OS are Debian-based distros that are often used for pentesting. The two systems can be employed by intermediate and experienced security professionals. They have a relatively fast learning curve, but their approach differs.
These Linux distros have specific variations, so make sure you pick the right one. You can leverage lite editions if you prefer minimal installations, but such versions might not contain the pentesting resources you’re looking for, and you’ll probably have to install them manually.
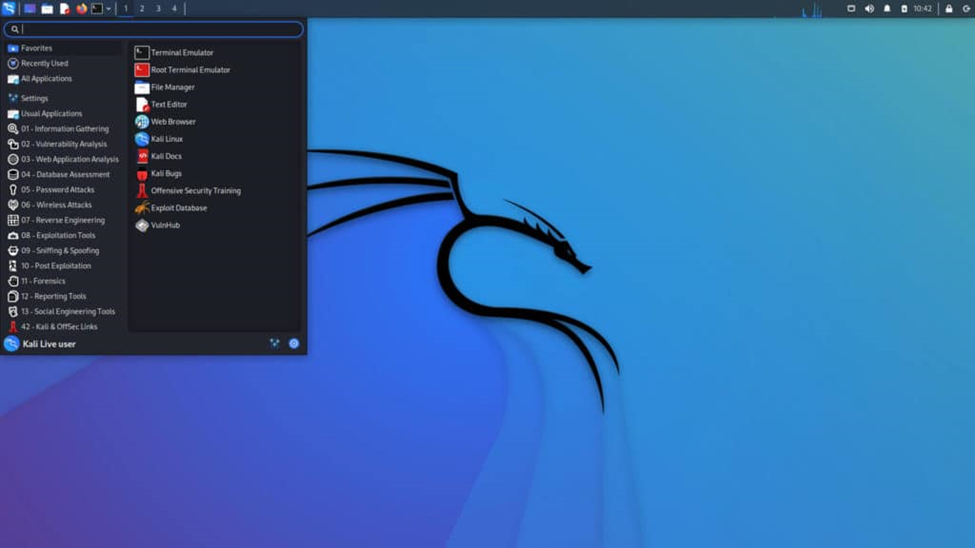
Kali Linux
Kali Linux is by far the most widely used Linux distro in cybersecurity and in security tests. Built on Debian, it provides a range of tools for pen testing, digital forensics, network analysis, ethical hacking, security evaluations and more. While Kali has good performance, some think it requires too much customization and is missing a few features that other distros possess. Kali should not be viewed as a primary or general Linux distro, but as a tool aimed at cybersecurity. Kali celebrated its 10th year earlier this year by adding defensive open source tools, increasing its utility for security pros.
Also read: Kali Linux Penetration Testing Tutorial: Step-By-Step Process
Pros
- The distro is easy to install.
- Kali Linux provides a high level of safety (e.g., custom kernel) and is actively maintained by Offensive Security.
- There are hundreds of pre-packaged tools for pentesting, security research, forensics, web app testing, and reverse engineering.
- Support is available for various architectures and platforms, such as x86, ARM, Cloud, Mobile Android, as well as multi-language support.
- Support is available for various modes of installation like bare metal, VM, live boot, containers, WSL.
Cons
- Kali Linux is not beginner friendly despite notable enhancements in recent versions.
- It can be slower than other distros like ParrotOS for some tasks, especially on low-end systems (expect some lags).
- It isn’t the most attractive interface and some complain that it needs too much customization.
- Can be resource intensive for certain tasks.
- Lacks pre-packaged IDEs for programming.
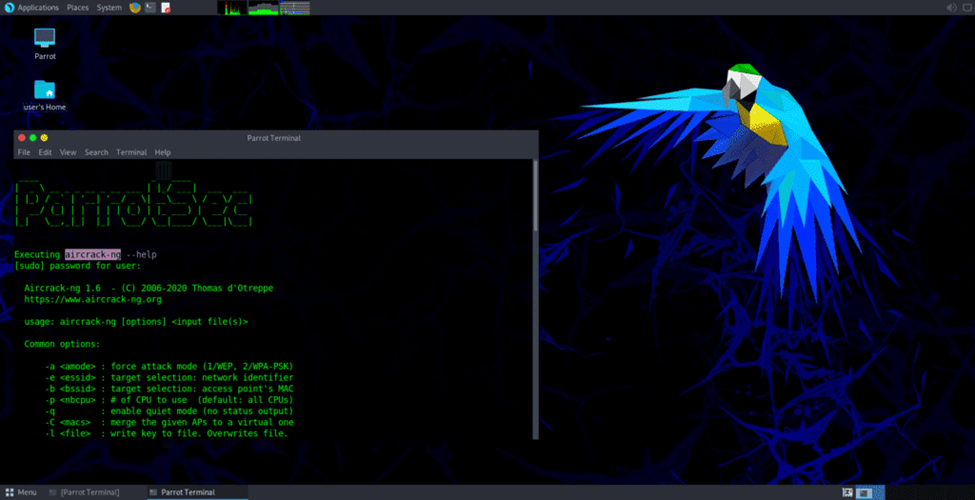
ParrotOS Security Edition
ParrotOS offers a Security Edition that is in some ways the mirror image of Kali: It’s user-friendly and manageable for beginners and is less resource-intensive on hardware than Kali. There are five editions to choose from depending on your needs, but the cybersecurity edition is the one that is most relevant. It is used heavily in pentesting and includes pretty much all the tools included in Kali plus a few others for threat prevention, security analysis, risk assessment and Wi-Fi cracking.
Pros
- Parrot OS is easy to install, user-friendly and beginner friendly.
- The distro is privacy-focused, with features like anonymization services, telemetry, logs and trackers disabled by default.
- Parrot OS contains pre-packaged IDEs for programming.
- It is lighter than Kali and requires less memory, free space, and RAM (also GPU is not required).
- Parrot OS is secure with features like sandboxes and regular updates.
Cons
- Parrot OS adds its own commands for generic operations like upgrading packages and that entails a learning curve for some.
- Doesn’t have as extensive community support as Kali.
Arch-Based Security Distros
Arch Linux standards are the reference for many professionals. While Arch requires a good amount of patience because of its complexity, ethical hackers and pentesters that learn it get to know a lot about how to use and abuse GNU/Linux. Arch Linux distros are flexible, light and easily customizable. Users have the freedom to pick and choose and adjust the look and feel as they desire. This makes it attractive to professionals and perhaps a little scary to novices.
Black Arch
Black Arch is a pentest distro based on Arch Linux. It can be challenging to learn but boasts a number of advantages for those who make the effort. There are full and slim versions: The full one contains all available tools and a complete OS; the slim version has a lighter OS and fewer tools.
Pros
- While it is minimalist, users will find lots of packages to install.
- An existing Arch Linux install can be upgraded to Black Arch.
- Black Arch leverages continuous updates, which is part of its philosophy.
- There is no bloat or unnecessary services.
- Black Arch is a good fit for those wishing to install and test bleeding-edge resources, offering a better package manager and release system.
Cons
- Black Arch may be difficult to install and use and is not beginner friendly.
- It functions more like a hacker OS than a pentest OS.
- It does not come with its own GUI.
ArchStrike
ArchStrike is an Arch Linux repository containing a variety of tools for professionals. Another one with a learning curve, it was developed specifically with ethical hackers in mind. It comes with extra packages for pentesting and ethical hacking. ArchStrike is powered by the Openbox window manager.
Pros
- ArchStrike can be installed on existing Arch installations to turn them into hacking environments.
- It is easy to install and remove (see the new ISO installer).
- ArchStrike is made by hackers for hackers.
- There are dedicated modules for investigations.
- A hardware detection facility is available.
- It requires only a lightweight install.
- Among the many pen testing tools available are the Argus network flow analyzer and the Wireshark network scanner.
Cons
- ArchStrike is not beginner friendly.
- It’s more of a hacking toolset than a full Linux distro.
Distros for Computer Forensics
Computer forensics can be particularly challenging, as retrieving meaningful information among tons of data can take many hours. Linux is especially popular in forensics due to its support for so many file systems. There are several Linux distros designed specifically for forensics. These Linux computer forensic distros have gained favor among those wanting to get to the bottom of breaches and incursions.
CAINE
CAINE (Computer Aided Investigative Environment) is one of the top Linux computer forensic distros. It comes with many built-in forensic investigation tools. Its investigative environment integrates with different software and forensic tools and has an easy to use graphical user interface.
Pros
- It has a user-friendly GUI.
- CAINE provides a complete investigative environment, including Autopsy and Sleuth Kit.
- It eases forensics significantly, especially memory analysis.
- All block devices are set to read-only mode by default.
- The live environment can be used to analyze running Windows installations.
- It can run via command line or GUI.
- Fulfills investigative processes like preservation, collection, examination and analysis.
Cons
- CAINE lacks documentation, which limits the kind of support users can receive.
- Some may find it challenging to install.
DEFT
DEFT stands for Digital Evidence and Forensic Toolkit. It is a distro employed by military, government officers, law enforcement, investigators, researchers, system admins, universities, and forensics specialists. The project is no longer actively maintained, but downloads can be found online in some places still. It is based on Lubuntu and has a GUI for forensic applications.
Pros
- It is user-friendly and easy to install.
- DEFT can help recover broken drives.
- Enhanced hardware detection is available.
- DEFT is especially good for advanced integrity checking, computer forensics, and incident response.
- It includes specific guides to learn how to use the environment.
- It ensures the integrity of data structures and metadata under analysis.
Cons
- Deft is not actively under development.
- Despite the guides, DEFT is not beginner-friendly and requires advanced knowledge to use it.
- Primarily aimed at forensic specialists as opposed to general IT personnel wanting to learn the basics of forensics investigations.
See more of the Best Digital Forensics Tools
Other Pentesting Distros
These last two distros may be lesser known, but they have some desirable features in their own right.
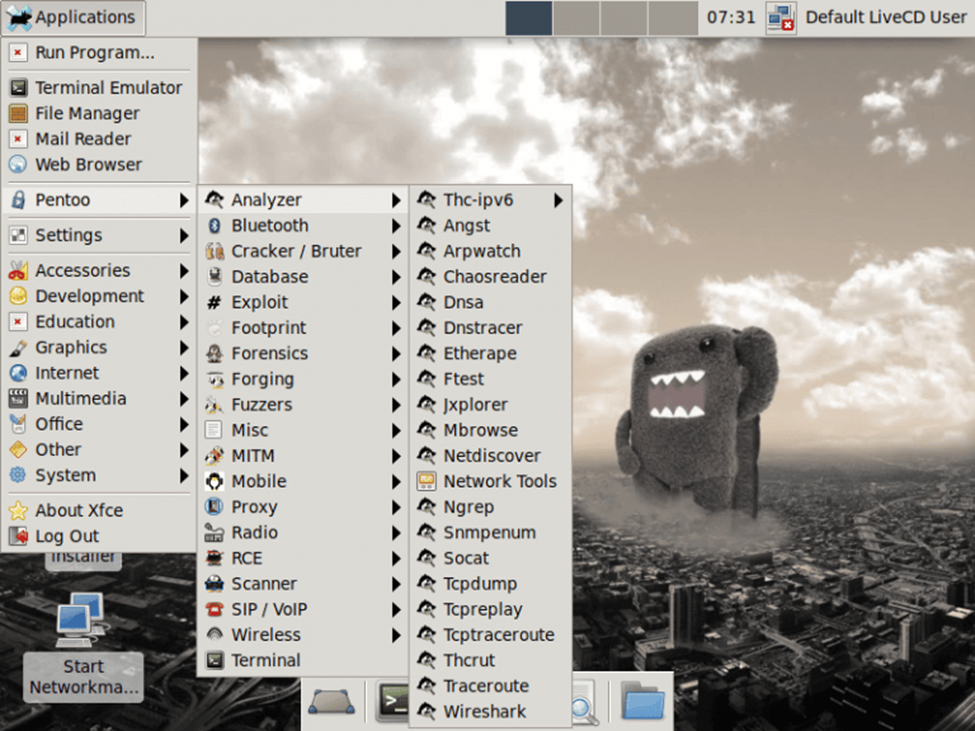
Pentoo
Pentoo is based on Gentoo Linux, a bare-bones minimalist distro for advanced Linux users. It has a distinct security focus and comes with various customized tools for Wi-Fi hacking, pentesting and security assessment.
Pros
- Pentoo is great for Wi-Fi hacking and hardware-accelerated cracking.
- It’s a relatively light distro.
- Pentoo is actively maintained, even if the project may look dead when you browse the website.
- It uses Portage as package manager, which compiles programs from sources instead of downloading binaries.
- Pentoo is worth installing on a live USB key as a complementary set of tools.
Cons
- It is not beginner friendly; good mainly for Linux enthusiasts.
- Pentoo may be difficult to install and use, but it is easier than Black Arch.
SamuraiWTF
SamuraiWTF aims to be “a complete Linux desktop for use in application security training.” WTF stands for Web Training Framework as it is a framework used to train people to learn security and penetration testing. It grew out of an Open Web Applications Security Project (OWASP) to boost cybersecurity skills on Ubuntu Linux.
Pros
- SamuraiWTF is maintained by the respected OWASP community.
- It is lightweight and easy to install, with various prebuilt images for virtual machines like Kali.
- Quick setup is possible with the CLI (command line interface), which utilizes custom “katana” commands.
- SamuraiWTF is perfect for web pentesting, with a focus on training users.
- It offers good documentation.
Cons
- SamuraiWTF is only helpful as an add-on tool.
- Once people are trained on it they will probably move on to advanced tools.
Also see the Best Vulnerability Scanning Tools and Best Open Source Vulnerability Scanning Tools
Choosing a Forensics & Pentesting Linux Distro
Choosing the right Linux forensics distro or pentesting distro is no easy task. There are many options and most can get the job done. The important factors to consider are compatibility and experience. Some distros are more compatible with various OSes and applications than others. Be sure to select a platform that fits your own environment.
Further, go easy on yourself. If you are familiar with Linux distros and Linux development, the advanced options should be fine. Even then, stick close to the distros that most align with the Linux environments you are used to working on. Also, be aware that some distributions demand a lot of performance and may struggle on aging machines.
Bottom Line: Getting Started with Pentesting and Forensics Distros
Whether you need a pentesting and forensic distro will depend on your needs and experience. Common operations like enumerating services, cracking passwords, intercepting HTTP requests, or even analyzing malware do not necessarily require a pentesting OS. Popular tools such as the Burp Suite, OWASP ZAP, Nikto, or BeEF are available as standalone apps and packages.
If you’re an absolute beginner, I would not recommend using a pentesting distro. Most pentesting distros have two major drawbacks: They can be overwhelming, and they require advanced knowledge.
You get hundreds of packages, scripts, wordlists, and other software, but it usually requires solid knowledge and experience to master each tool, prevent misuses and rabbit holes, and conduct tests in safe conditions.
You can totally use a classic distro like Ubuntu with a few packages and the right configurations and you’ll be able to achieve most tasks. Besides, if you’re new to Linux, it’s probably better to start with generic systems.
In any case, it is strongly recommended to use VMs (virtual machines). Do not install the above distros as your primary system unless you know what you are doing.
For example, if you need to test for ransomware, it’s better to have it on a VM and in a sandbox environment that can be compromised without affecting your personal files. Besides, you can take snapshots to quickly restore a working environment at will. The idea is to isolate your testing environment.
We have much more content on using open source pentesting and vulnerability scanning tools. Here are a few tutorials to get you started:
- Getting Started With the Metasploit Framework: A Pentesting Tutorial
- Nmap Vulnerability Scanning Made Easy: Tutorial
- Getting Started with the Burp Suite: A Pentesting Tutorial
- Testing & Evaluating SIEM Systems: A Review of Rapid7 InsightIDR
This updates an August 2022 article by Julien Maury




