Network security tools incorporate hardware and software technologies, methods, and policies to preserve network integrity and prevent potential breaches. These tools offer a comprehensive network security strategy by combining various functions for encryption, firewalls, intrusion detection systems, access control, and regular security audits. We’ve reviewed leading network security tools to assist you in selecting the best fit for your business’s security needs.
These are the seven best network security tools:
- ESET: Best overall network security tool
- Palo Alto: Best for zero trust security
- Cisco: Best for network access control
- Nessus: Best for vulnerability detection
- Fortinet: Best for core and NGFW features
- Splunk: Best choice for unified security
- Malwarebytes: Best for malware defense
Featured PartnersFeatured Partners: Network Monitoring Software
eSecurity Planet may receive a commission from merchants for referrals from this website
Top Network Security Tools Comparison
We’ve compared the following tools’ capabilities on threat detection, unified platforms monitoring, data loss prevention, multi-OS support, and the availability of free trial.
| Threat Detection | Unified Platforms Monitoring | Data Loss Prevention | Multi-OS Support | Free Trial | |
|---|---|---|---|---|---|
| ESET | ✔️ | ✔️ | ➕ | ✔️ | 30 days |
| Palo Alto | ✔️ | ✔️ | ✔️ | ✔️ | 30 days |
| Cisco | ✔️ | ✔️ | ✔️ | ✔️ | 30 days |
| Nessus | ✔️ | ✔️ | ✔️ | ✔️ | 7 days |
| Fortinet | ✔️ | ✔️ | ✔️ | ✔️ | 30 days |
| Splunk | ✔️ | ✔️ | ✔️ | ✔️ | 14 days |
| Malwarebytes | ✔️ | ✔️ | ❌ | ✔️ | 14 days |
✔️=Yes ❌=No/Unclear ➕=Add-On
ESET – Best Overall Network Security Tool
Overall Rating: 4.4/5
- Core features: 4.7/5
- Pricing and transparency: 4.8/5
- Infrastructure characteristics: 4.7/5
- Compliance certifications: 4.3/5
- Ease of use and admin: 4.5/5
- Customer support: 3.2/5
ESET is a global digital security business that detects and neutralizes zero-day threats, ransomware, and targeted assaults before they’re launched. Their unified cybersecurity platform, the ESET PROTECT plan, completely protects endpoints and other potential threat vectors such as mobiles, email, online, and cloud apps. With its automated, all-in-one defense, ESET leads our choices for network security solutions for cloud and on-premises deployment.

Pros
Cons
Palo Alto Networks – Best for Zero Trust Security
Overall Rating: 4.3/5
- Core features: 4.6/5
- Pricing and transparency: 2.4/5
- Infrastructure characteristics: 5/5
- Compliance certifications: 5/5
- Ease of use and admin: 4.5/5
- Customer support: 4.3/5
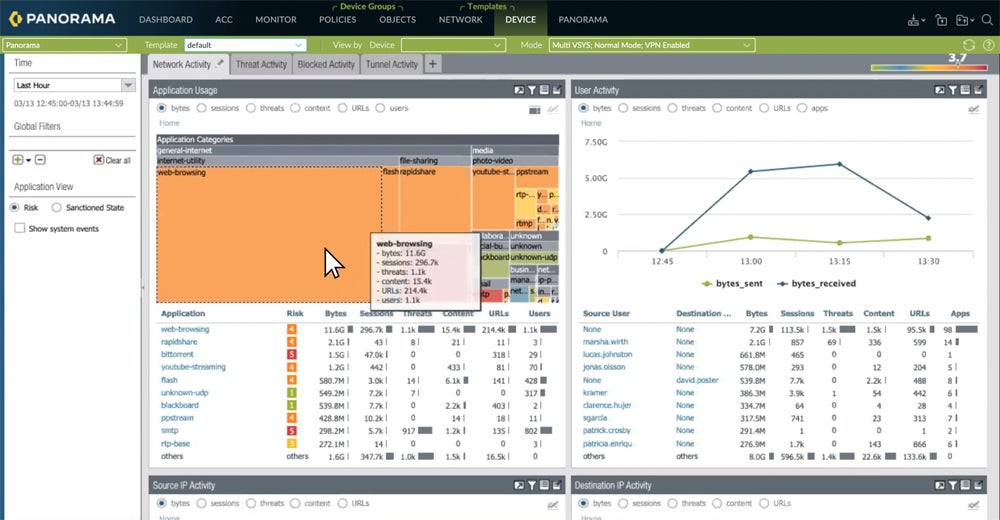
Palo Alto Networks provides a suite of technologies that enable enterprises to achieve zero trust security through microsegmentation. They implement zero trust by authenticating identities, requiring least privilege access, and continually monitoring network traffic. Palo Alto Networks continues to innovate with virtual, physical, and containerized firewall deployment choices, network security management, cloud-delivered security services, and more.

Pros
Cons
Cisco – Best for Network Access Control
Overall Rating: 4.2/5
- Core features: 4.9/5
- Pricing and transparency: 2.3/5
- Infrastructure characteristics: 5/5
- Compliance certifications: 5/5
- Ease of use and admin: 5/5
- Customer support: 3.4/5
Cisco provides network access control (NAC) via Identity Services Engine (ISE). This tool enables network visibility and access management by enforcing policies on devices and users. It uses the data across your stack to enforce policies, manage endpoints, and provide trusted access. Cisco also offers IDPS and breach and attack simulation solutions. You can integrate solutions conveniently into your network management dashboard via Cisco Networking.

Pros
Cons
Nessus – Best for Vulnerability Detection
Overall Rating: 4/5
- Core features: 3.6/5
- Pricing and transparency: 4.3/5
- Infrastructure characteristics: 5/5
- Compliance certifications: 3.5/5
- Ease of use and admin: 4.5/5
- Customer support: 3/5
Tenable Nessus is a vulnerability scanning tool for network security that originated as an open-source project. It now offers extensive capabilities to skilled security teams via detecting default passwords, accessing denial attempts, opening mail relays, and identifying potential hacker entry points with exceptional accuracy. Nessus discovers software issues, missing updates, malware, and misconfigurations across several operating systems and devices.
Pros
Cons
Fortinet – Best for Core & NGFW Features
Overall Rating: 3.9/5
- Core features: 5/5
- Pricing and transparency: 2.6/5
- Infrastructure characteristics: 5/5
- Compliance certifications: 2.8/5
- Ease of use and admin: 4/5
- Customer support: 2.7/5
Fortinet has long been a firewall provider for SMBs and enterprises, delivering office hardware, virtual machines, and cloud applications (FWaaS). Fortinet’s FortiGate solutions include SSL inspection, automated threat protection, security fabric integration, and security effectiveness validation. Fortinet offers a comprehensive set of core features that includes powerful threat protection, firewall capabilities, and business-scalable solutions.
Pros
Cons
Splunk – Best Choice for Unified Security
Overall Rating: 3.8/5
- Core features: 4.4/5
- Pricing and transparency: 2.4/5
- Infrastructure characteristics: 5/5
- Compliance certifications: 3.5/5
- Ease of use and admin: 4.3/5
- Customer support: 3/5
Splunk is an enterprise solution for large organizations that need insight across a wide range of security tools and activities. Splunk stands out for its unified network security, thanks to recent advancements in Splunk Mission Control, and Observability Cloud. Businesses can now streamline workflows and enhance security analytics (Enterprise Security), automation (SOAR), and threat intelligence. This simplifies threat detection and response within a unified platform.

Pros
Cons
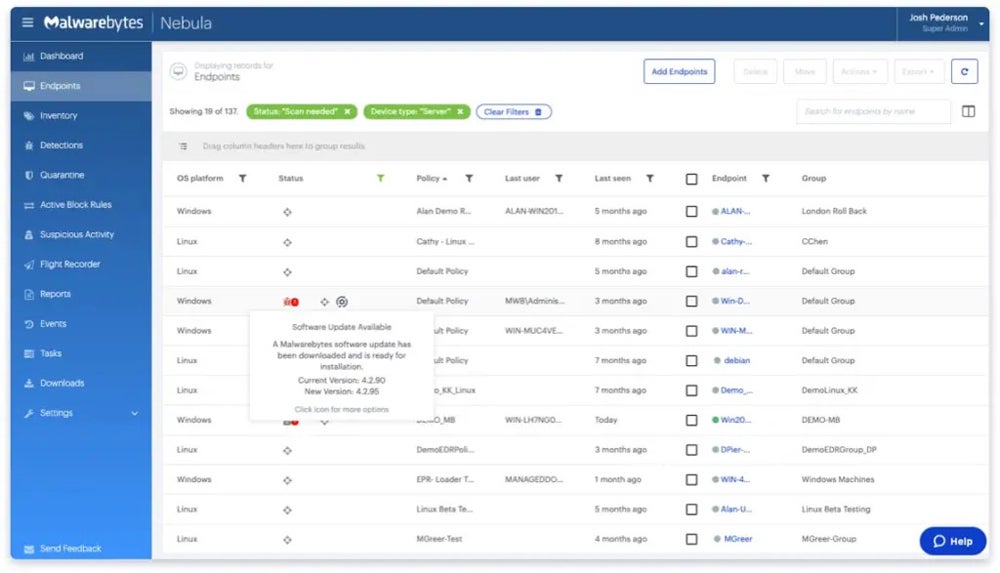
Malwarebytes – Best for Malware Defense
Overall Rating: 3.8/5
- Core features: 3.6/5
- Pricing and transparency: 3.3/5
- Infrastructure characteristics: 5/5
- Compliance certifications: 3/5
- Ease of use and admin: 5/5
- Customer support: 3/5
Malwarebytes offers high-level network security along with comprehensive anti-malware protection. Its endpoint security solutions leverage many layers of protection, threat intelligence, and human expertise to protect businesses from ransomware, viruses, and other threats. Malwarebytes’ Identity Theft Protection provides trustworthy security by quickly alerting users to any identified information breaches, enabling swift remediation.

Pros
Cons
Top 5 Features of Network Security Tools
Network security relies on a variety of tools for comprehensive protection. Among its most important key features are breach and attack simulation, endpoint detection and response, identity and access management, intrusion detection and prevention, and network access control.
Breach & Attack Simulation (BAS)
Breach and attack simulation mimics real-world cyberattacks, similar to manual pen testing and red teaming. Administrators can quickly respond to developing threats across varied infrastructure environments, including cloud and SD-WAN frameworks, thanks to real-time warnings and visibility, ensuring proactive protection and security posture augmentation.
Endpoint Detection & Response (EDR)
EDR is similar to vulnerability management as it identifies and mitigates threats at user entry points. It provides comprehensive security similar to IAM, NAC, and privileged access management (PAM) tools, but with extra capabilities including data loss prevention (DLP), patching, and application whitelisting for added protection.
Identity & Access Management (IAM)
IAM is a system that manages access policies dynamically. IAM works with all identity protocols and connects smoothly with CASB, EDR, and WAF systems, providing insights into device, session, and identity data to guarantee reliable security and effective access management across various environments.
Intrusion Detection & Prevention Systems (IDPS)
IDPS scan systems for intrusions using signature or anomaly-based detection techniques. IDPS provides threat detection, intelligent alerting, and automated blocking tools to quickly identify and neutralize security threats, ensuring strong protection against malicious activity.
Network Access Control (NAC)
NAC is a policy management solution that ensures proper endpoint setups. NAC, which is integrated with SIEM, NGFW, and other systems, assesses endpoints, allows access, and enforces security policies, hence improving network security by verifying and controlling device network access. NAC’s function includes enforcing compliance rules, improving network visibility, and limiting risks associated with illegal devices.
How We Evaluated the Best Network Security Tools
We assessed the top network monitoring tools using a standardized scoring method that included six fundamental criteria. Under each criterion, we identified subcriteria that were used for our assessment and scoring, contributing to the products’ total score. We picked the seven tools that scored the highest. Through the results, coupled with broader research, we determined each product’s use cases.
Evaluation Criteria
We prioritized six essential criteria to objectively evaluate the top network security tools. Core features weighted the highest due to their fundamental importance. Pricing and network security infrastructure followed, for practicality and extended capabilities. Compliance, ease of use and administration, and customer support quality were also valued for operational efficiency.
- Core features (25%): We checked each network security tool’s essential functionalities such as breach and attack simulation, Cloud Access Security Broker (CASB), EDR, IAM, IDPS, Mobile Threat Defense, and more.
- Criterion winner: Fortinet
- Pricing and transparency (20%): This criterion considers factors such as the availability of free trials, the accessibility and clarity of pricing, pricing model flexibility, the provision of free plans, and the availability of free demos.
- Criterion winner: ESET
- Network security infrastructure characteristics (20%): We checked each tool’s characteristics based on its system integrations, compatibility across several platforms, unified platform monitoring, zero trust security, scalability, and backup and recovery.
- Criterion winner: Multiple winners
- Compliance certifications (15%): We looked at certifications like ISO 27001 and 9001, HIPAA, PCI DSS, GDPR, SOC2, NIST, and the availability of specific compliance frameworks.
- Criterion winner: Multiple winners
- Ease of use and admin (10%): This category is measured by the intuitiveness of the user interface, the provision of a centralized admin panel for streamlined operations, and ratings from platforms like G2 and Capterra for simplicity of use and setup.
- Criterion winner: Multiple winners
- Customer support (10%): This criterion measures service quality, including the availability of live chat, phone, and email assistance, the adequacy of documentation, demos, and training materials, and user-rated support quality on G2 and Capterra.
- Criterion winner: Palo Alto Networks
Frequently Asked Questions (FAQs)
What Is Enterprise Network Security?
Enterprise network security is a broad term covering a range of technologies, devices, and processes. Some experts define it simply as a set of rules and configurations that protects the integrity, confidentiality, and accessibility of data in an enterprise network. It entails deploying software and hardware to minimize vulnerabilities and respond quickly to security threats, with a focus on effective response mechanisms and prevention efforts against cyberattacks.
What Are These Network Security Tools Used For?
Network security products perform several functions by protecting the organization’s network infrastructure, data, and assets from various cyberattacks. These tools work together to form a multi-layered security approach that protects the company network from a wide range of cyberthreats and vulnerabilities. In addition to the top network security tools above, here are some network security tools and their functions:
- Data loss prevention (DLP): Monitor and manage data movement throughout the network to prevent illegal transfer or leaking of sensitive data.
- Virtual private networks (VPNs): Encrypt network traffic, ensuring safe communication between remote users and the corporate network while protecting sensitive data from interception.
- Firewalls: Serve as a barrier between the internal network and external threats, managing incoming and outgoing traffic according to specified security rules.
- Antivirus and antimalware software: Detects and eliminates dangerous software (malware) from systems, preventing unwanted access and data breaches.
- Security information and event management (SIEM): Collects, analyzes, and correlates security event data from diverse sources in order to detect and respond to security incidents more efficiently.
- Cloud access security broker (CASB): Monitors and manages access to cloud services, ensuring data security, compliance, and threat protection.
- Mobile threat defense: Focuses on protecting mobile devices from threats such as malware, phishing, and network attacks while also ensuring data and user privacy.
What Are the Common Challenges in Using Network Security Tools?
Common challenges when adopting network security solutions include integrating them into your current systems, difficulty in choosing from an extensive range of accessible tools, and managing complexity as your business expands.
- Integration with other systems: Many businesses already have established IT systems, such as network infrastructure, endpoint devices, and cloud services. It might be difficult to integrate new security tools with current systems.
- Tool overload: The cybersecurity market provides a diverse range of tools and solutions, each addressing a distinct area of network security. However, an abundance of options can cause confusion and uncertainty for enterprises.
- Complexity management: As enterprises expand and evolve, their network security environments might become more complicated. Managing several security tools, configurations, and rules across various network infrastructures adds to the complexity.
Bottom Line: Enhance Your Defense with Network Security Tools
Maintaining the integrity of network security is a critical consideration for every organization. Organizations must blend various technologies to achieve optimal protection within budget constraints. Access control, threat intelligence, intrusion detection and prevention, data loss prevention, email security, endpoint security, vulnerability scanning, and patch management all play a role in protecting the network and its data.
With almost every aspect of business becoming more digital, network security software minimizes the impact of cyberattacks. Consider your security priorities and utilize the available free trial and free plans to gauge which tool is most suitable for you.
No single tool guarantees complete security, but you may want to start your network security strategy by implementing firewall best practices, as these are often the first line of defense against cyberthreats.