LastPass is a popular business password manager for teams that want an easy-to-use product and a large range of core features. Password management solutions like LastPass store multiple passwords and centralize logins so users only have to remember one master password. LastPass has had some major security hiccups in the past, but it continues to hold one of the top spots in the password manager market, and many businesses use it.
What You Need to Know About LastPass
| LastPass is an easy-to-use password manager with a strong selection of features for both small and large businesses. But its weak security, evidenced by multiple breaches over the last decade, have somewhat dampened its popularity and its perceived effectiveness in recent years. | ||
| Overall Rating: 3.8/5 • Core features: 4.7/5 • Usability and administration: 4.2/5 • Security: 3.3/5 • Pricing: 3.2/5 • Customer support: 4/5 • Extra features: 2.4/5 | Pros | Cons |
| ✔️ Strong set of core and enterprise features | ❌ Multiple security breaches | |
| ✔️ Multiple support channels available | ❌ Passkeys aren’t an active feature yet | |
| ✔️ Overwhelmingly high reviews for ease of use | ❌ Lacks a couple extra capabilities | |
Continue reading about LastPass’s ideal use cases, its pricing and standout features, and its support, or jump down to learn more about our scoring methods for LastPass.
Table of Contents
Featured Partners: Password Management Software
Who Should Use LastPass?
LastPass is particularly attractive for smaller teams and businesses that don’t have a lot of prior experience with password managers. But it’s also an option for large businesses that need a quick PM rollout.
The following list provides examples of businesses that could benefit from LastPass:
- Companies that prioritize user experience: A user-friendly product like LastPass will attract SMBs and enterprises looking for a straightforward solution and implementation process.
- Teams looking for a strong roundup of core features: LastPass has plenty of password management capabilities suitable for both small and large businesses.
- Businesses that need multiple support options: LastPass offers multiple support channels, as well as a dedicated customer service manager for some plans.
Who Shouldn’t Use LastPass?
While LastPass will suit multiple businesses’ needs, it’s not a good choice for security-focused organizations. It’s also missing a couple nice-to-have features and is quite expensive if you need unlimited MFA and SSO functionality.
Examples of organizations that probably shouldn’t consider LastPass include:
- Teams needing specific advanced features: While LastPass excels in core and enterprise capabilities, it’s missing some features, like customizable session timeouts and guest accounts. It also doesn’t support passkeys yet.
- Security-focused organizations: While password managers are a security product, some businesses will need more protection than others. If that’s you, LastPass is not a good option due to its multiple breaches.
- Businesses on a tight budget: If you’re okay with minimal features, the Teams plan might be sufficient, but full MFA and SSO functionality is only available through the Business plan and costs an additional $3 per user per month.
If LastPass doesn’t sound like a good fit for you, skip down to see some of our other password manager options.
LastPass Pricing
This table compares LastPass’s business pricing plans and some of the perks and features you’ll receive in each plan. LastPass also has an enterprise plan, but you’ll have to request a custom quote to receive information about its features and capabilities.
| Teams | Business | Enterprise | |
|---|---|---|---|
| Annual Billing Price | $4/user/month | $7/user/month | Contact for quote, free trial information, and feature details |
| Free Trial | 14 days | 14 days | |
| Key Features | Single admin console, passwordless login, password generator, offline mode, dark web monitoring | Everything in Teams, authentication for SSO and cloud apps, employee SSO portal, API access, directory integrations | |
| Number of Customizable Security Policies | 25 | 100+ | |
| Accounts for Employees’ Families | None | 5 additional licenses |
5 Key Features of LastPass
LastPass offers core password management features like sharing, recovering master passwords, and multi-factor authentication, as well as standout features such as dark web monitoring and integrations with security information and event management solutions.
Password Sharing
To share passwords with their coworkers, LastPass users can create folders with one or multiple sets of credentials. They’re also able to set permissions for each user, determining how much of the folder’s contents individual employees can view. LastPass also syncs revisions to logins within shared folders, so you don’t have to change multiple instances of the same password.

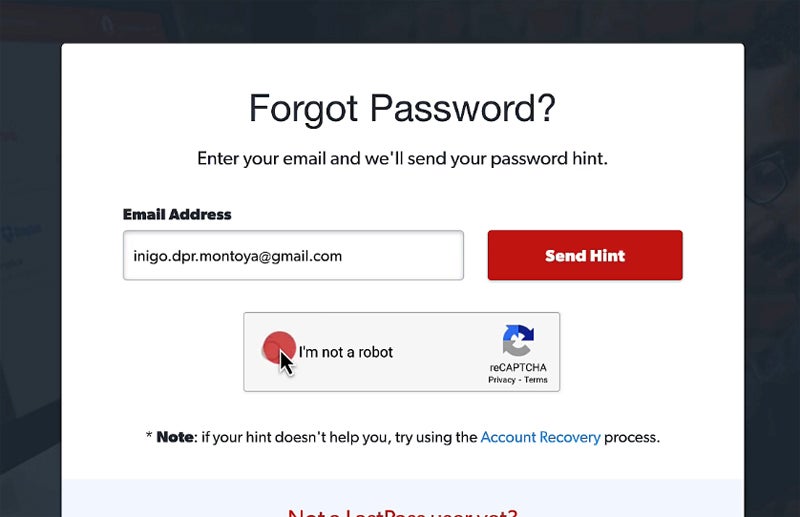
Account Recovery
LastPass offers a few different account recovery options, including setting up face or fingerprint recovery on the mobile app, SMS account recovery, and master password hints. However, these all must be set in advance as protective measures; you won’t be able to set them in hindsight if you forget your master password. For security reasons, LastPass isn’t able to reset a master password for users; it doesn’t store decrypted passwords on its servers.
Multi-Factor Authentication
LastPass’s multi-factor authentication options include SMS options, fingerprinting and face scanning, one-time passwords, and voice recognition. Users can apply MFA methods to multiple types of access points, including virtual private networks (VPNs), cloud applications, and workstations.

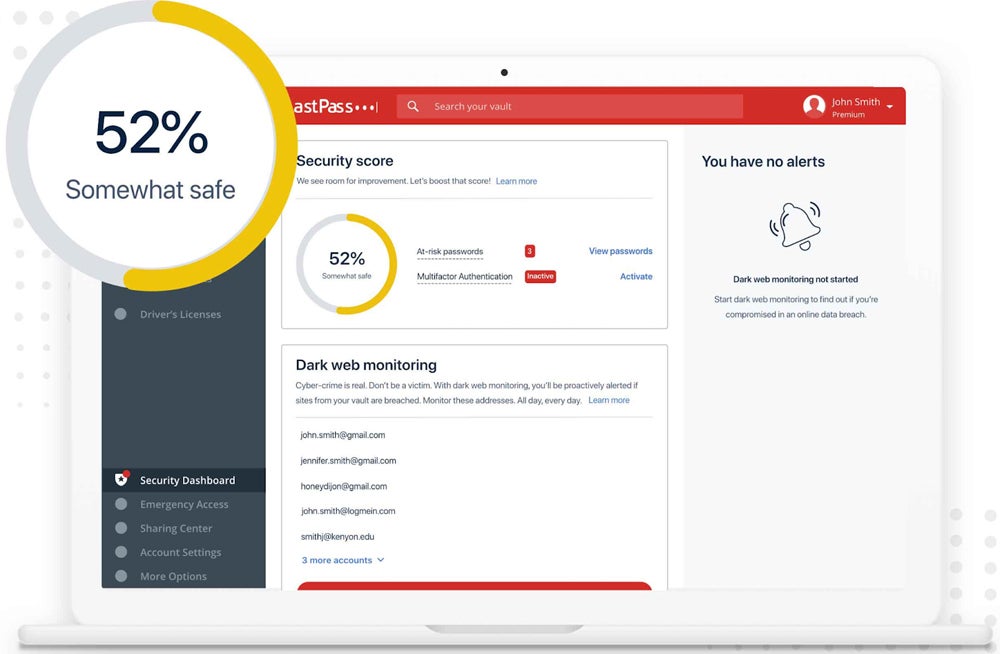
Dark Web Monitoring
Using a database that stores a list of breached credentials, LastPass monitors your email addresses and alerts you if your email is compromised on the dark web. To enable this feature, your team must turn on the monitoring option for any email address you want to check. LastPass informs businesses of the specific account that’s been compromised.
SIEM Integrations
LastPass integrates with Splunk and Microsoft Sentinel, syncing its data to security information and event management systems that can alert admins to threats. SIEM integrations also provide advanced reporting, allowing LastPass users to see an overall picture of their password management environment. Consistent, thorough reporting also improves your business’s compliance posture because you can produce regulatory reports.

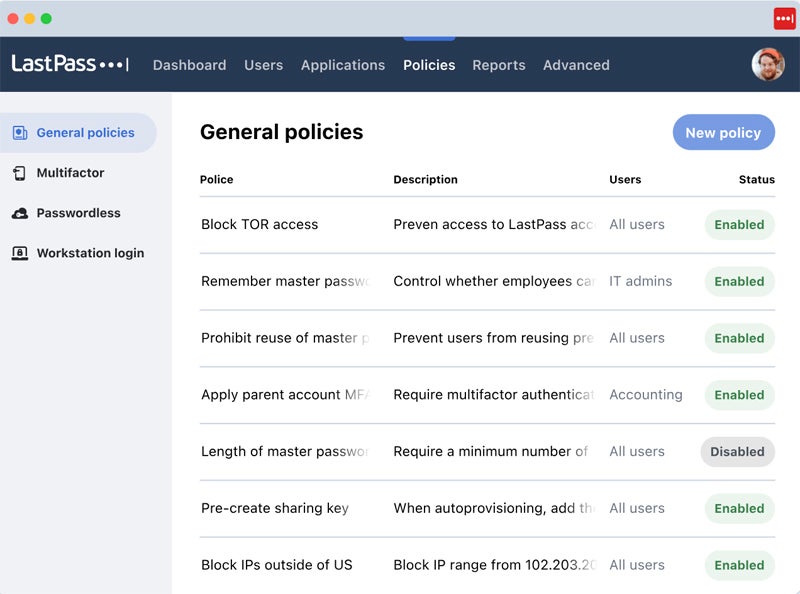
LastPass Ease of Use
LastPass offers a command center for centralized user management, where business leaders can customize LastPass admins’ access based on their roles. The command center also facilitates integrations with employee directory software. Other usability features include security policy management and documentation. While LastPass’s documentation isn’t as attractive as competing password managers’, it’s thorough, with plenty of articles for self-service.
Overall, LastPass is a popular product; customer reviews applaud its ease of use, including on mobile devices and the syncing process between devices. One user complaint that did show up frequently in reviews was autofill issues, like passwords not autofilling or LastPass filling unwanted fields. In general, user sentiment about LastPass is highly positive, with a few small bumps here and there.
LastPass Customer Service
LastPass’s customer service options include 24/7 phone and web support for all of its paid plans, including the personal ones. It stands out amongst its competitors for offering phone support, especially around-the-clock. If you’d like to see LastPass before signing up for a free trial, it also offers a product demo by request.
LastPass offers businesses a dedicated customer service manager during the onboarding process; this service is available through the Business plan but not Teams. It’s available for enterprises as well. Customers also have access to self-help articles and to the LastPass community, where they can ask questions and contribute to discussions.
| Teams | Business | Enterprise | |
|---|---|---|---|
| 24/7 Phone Support | ✔️ | ✔️ | ✔️ |
| 24/7 Web Support | ✔️ | ✔️ | ✔️ |
| Dedicated Customer Service Manager | ❌ | ✔️ | ✔️ |
Is LastPass Secure?
One of the most frequently asked questions about LastPass is whether it’s still safe to use. I recommend your business take this question seriously based on LastPass’s breach history and your own security requirements. While cybersecurity is important for every organization, your business may have differing levels of security prioritization based on your industry and the type of data you store and transfer.
LastPass has had multiple breaches over the past eight years. The most recent one occurred in 2022 and began when LastPass noticed strange activity within its dev environment. At first, LastPass said that no customer data was impacted. However, later in the year, threat actors breached its third-party cloud storage provider, which led to potential compromise of LastPass’s customer data.
Alternatives to LastPass
While LastPass is a popular password management solution for businesses, its history of multiple breaches means that overall, I don’t recommend it for business use. 1Password, Bitwarden, and Keeper are other password manager options with better security history.
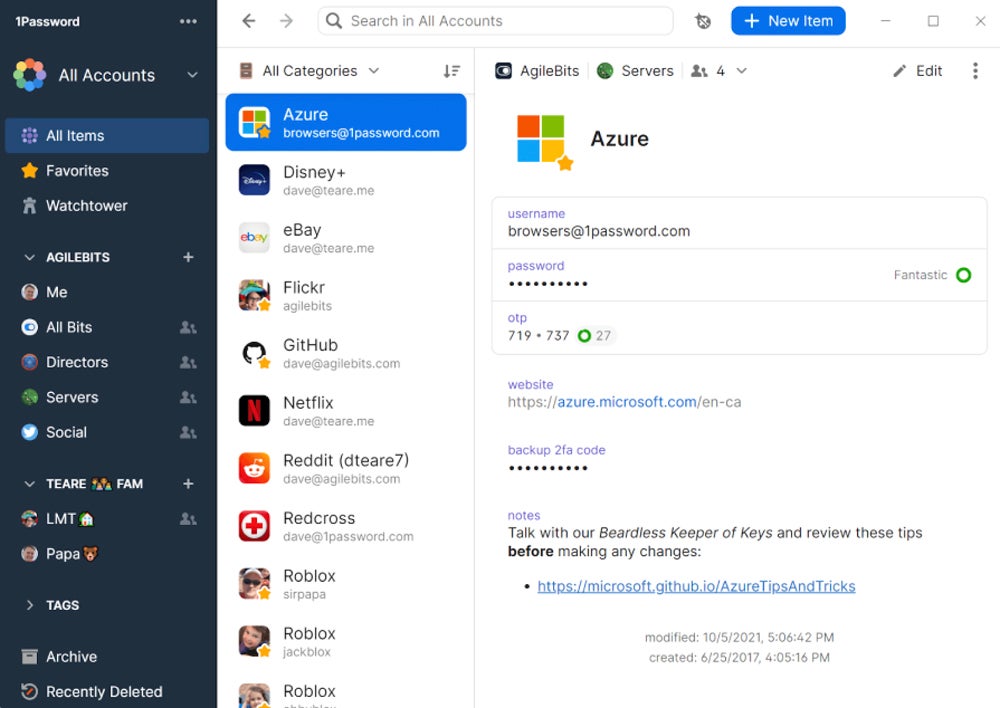
1Password
1Password is a popular enterprise-grade password manager with robust security. It offers a zero-knowledge storage format, like LastPass, but unlike LastPass, it has no successful breaches. If you’re looking for a password manager with a comparable feature set but better security, there are few options as good as 1Password.
1Password is priced comparably to LastPass at $7.99 per user per month for its Business plan. While 1Password receives some mixed reviews about ease of use, its strong security and clean breach history make it a good choice for organizations focused on protecting sensitive data.
Read more about the differences and similarities between these two products in our article comparing LastPass and 1Password.
Bitwarden
Bitwarden is another popular password management solution with a clean breach history. It scored highly for security in my evaluation of Bitwarden, and it uses zero-knowledge encryption procedures. Bitwarden also has features like customizable session timeouts and passkeys — at the time of this writing, LastPass’s passkey feature isn’t yet active.
Bitwarden offers similar pricing to LastPass, with Teams pricing at $4 per user per month and Enterprise pricing at $6 per user per month. While Bitwarden lacks some of the support channels that LastPass offers, users speak highly of the support team’s quick responses and knowledge.
If you’re interested in learning more about Bitwarden, read more about how it differs from LastPass in our comparison article of Bitwarden and LastPass.
Keeper
Keeper is a password manager for businesses of all sizes, including managed service providers. Similar to LastPass, it receives positive overall user reviews for usability and has dark web monitoring capabilities. It also offers advanced add-on features like compliance reporting, enterprise-level security alerts, and secure file storage.
Keeper’s Business plan costs $3.75 per user per month, comparable to LastPass’s pricing but a little less expensive. Keeper also offers an MSP product, designed to handle password, secrets, and privileged access in one solution designed specifically for managed service providers.
We cover other recommended password management products in our article on alternatives to LastPass.

If you’re interested in learning about more password managers, read our guide to the best password manager products next. This list also includes RoboForm and NordPass, in addition to the options above.
How We Evaluated LastPass
To evaluate LastPass, its ideal use cases, and its final score, I created a rubric with six major categories. Each category contained multiple subcriteria, which all received their own weighting. LastPass received its final score of 3.8/5 based on how many subcriteria it satisfied and how each criterion and subcriterion were weighted.
Evaluation Criteria
My first major evaluation criterion included core and enterprise features, the backbone of a successful password manager. I also examined usability and administration, including documentation and user management features. Next, I looked at security practices and transparency, pricing and free trials, and customer support availability. Finally, I evaluated nice-to-have extras like guest accounts, travel mode, and dark web monitoring.
- Core features (25%): I considered important PM features, including secure sharing, multi-factor authentication, and browser support.
- Score: 4.7/5
- Usability and administration (20%): Ease of use analyzed documentation and user and policy management, as well as overall reviews and admin reporting.
- Score: 4.2/5
- Security (15%): I evaluated LastPass’s transparency about security practices and audits, as well as its breach history.
- Score: 3.3/5
- Pricing (15%): The pricing category scored LastPass based on pricing compared to the market in general, as well as availability and length of a free trial.
- Score: 3.2/5
- Customer support (15%): I examined availability of support channels like email and phone, as well as support team hours.
- Score: 4/5
- Extra features (10%): I looked at nice-to-have capabilities like guest accounts and travel mode, as well as passkeys.
- Score: 2.4/5
Bottom Line: LastPass’s Usability Comes with Risks
LastPass is widely used in many businesses, and with good reason — it offers plenty of basic password management features, as well as some enterprise-grade capabilities. Its easy-to-use interface adds to its popularity. However, its breach history is cause for concern. Despite that, LastPass is one of the best-designed products in the industry, with plenty of password management features for SMBs and enterprises alike.
Passwords are only one of many threats to organizations. Read more about overall network security and how to implement secure systems in your business.








