Strong encryption protects data securely from unauthorized access, but the specific algorithms that qualify as strong encryption change over time as computing power increases and researchers develop new ways to break encryption. In practice, security tools provide many encryption options that confuse uneducated users — including broken encryption options. Yet even the strongest encryption options depend upon key best practices to support effective encryption deployment.
What Makes an Encryption Algorithm Strong?
A strong encryption algorithm requires a strong encryption key, a strong mathematical algorithm, and a complex encryption process.
Strong encryption keys are passwords for encryption. The longer the password or the more complex the password, the more difficult it will be to guess. However, as binary numbers, encryption keys lack complexity and therefore require length. Most encryption algorithms require a minimum of 128 bits (a combination of 128 zeroes and ones).
Strong mathematical algorithms use the key to feed an algorithm made of simple mathematical processes. Current encryption algorithms use points on an ellipse, multiply large prime numbers, or implement exclusive OR (XOR) logical operations on portions of data as the basis for the algorithm.
A complex encryption process uses a complex combination of the encryption key and the mathematical algorithms on blocks of data over multiple rounds of encryption. For example, the Blowfish algorithm uses simple XOR functions and performs four actions within each of the 16 rounds of encryption:
- XOR the left half of the data with an 18 entry P-array.
- Use the XOR data as input for a F-Function (to transform data).
- XOR the F-function’s output with the right half of the data.
- Swap the left and right halves of the results to use as the inputs in the next round.
Individually, each element provides partial protection. The combination of the keys, the algorithms, and the encryption process provides the full strength of the encryption process. Keep in mind that encryption transforms the data to prevent discovery and doesn’t simply mask the data like in tokenization or provide an output to check for tampering such as in hashing.
When Strong Encryption Becomes Weak
Every type of strong encryption starts off unbreakable, but all encryption schemes become weak because of improved cryptographic analysis techniques and stronger computing power. This combination erodes the capability of older encryption algorithms but also powers the new algorithms that will be developed.
For example, the earliest government-endorsed encryption algorithm, DES, encrypted using 64-bit blocks, 16 rounds of encryption, and a key of only 56 bits. This 56 bit key originally taxed existing computing resources but became vulnerable to brute force guessing as computing power improved.
In 1997, AES encryption replaced DES with stronger encryption that increased block sizes to 128 bits, used 10 to 14 rounds of encryption, and increased key sizes to a minimum of 128 bits. The National Institute of Standards and Technology (NIST) currently promotes AES as a strong encryption standard but also acknowledges that quantum computing likely renders AES vulnerable sometime in the next 20 years.
Harnessing ever-more-powerful computing will challenge the effectiveness of encryption algorithms, but failed encryption processes currently expose more data than weak encryption algorithm strength. Best practice adoption protects the encryption process to avoid stolen, revealed, or guessable encryption keys.
6 Best Practices for Deploying Strong Encryption
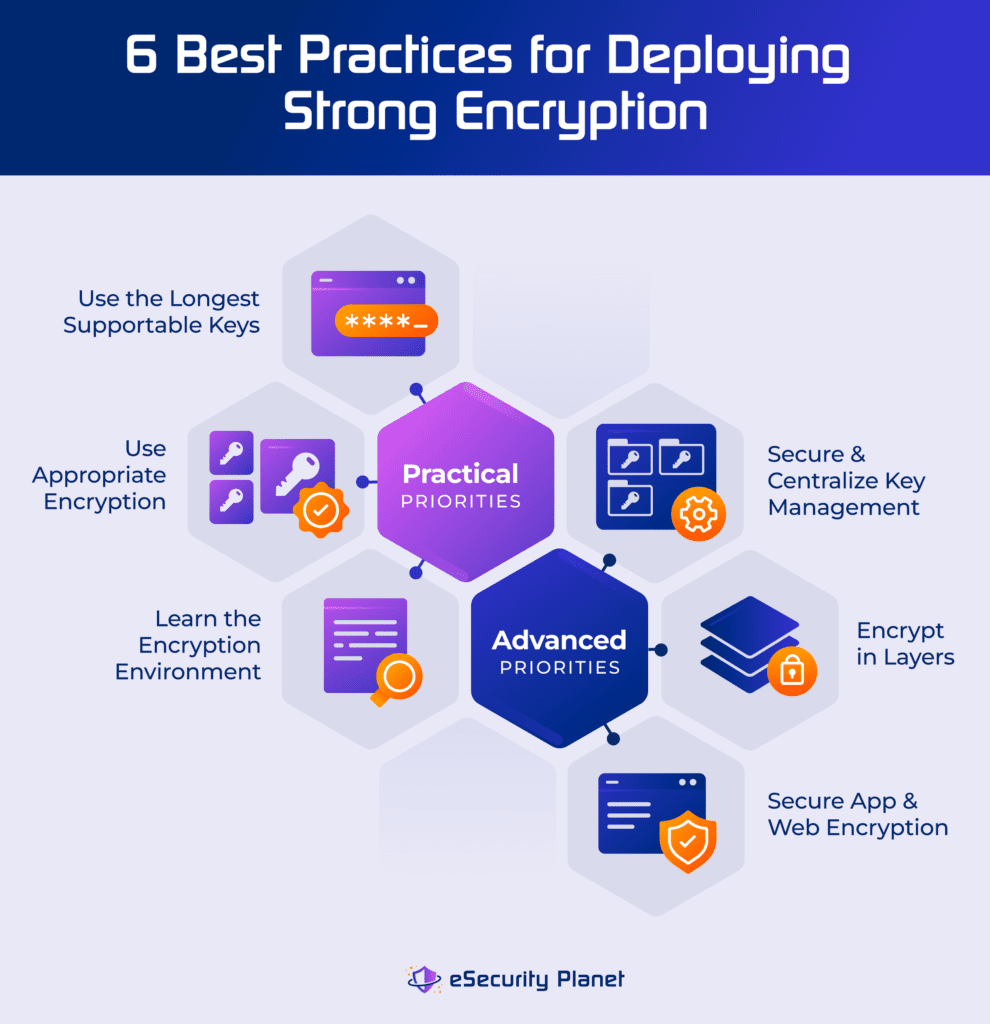
As with any other security tool in network or cloud security, improper deployment undermines even the strongest capabilities. While equal in importance, most organizations will discover a practical hierarchy for implementing the top six encryption best practices.
Security teams generally first use appropriate encryption, learn the encryption environment, and use the longest supportable keys. These best practices don’t require additional tools and deliver immediate benefits for security. Next, an organization will encrypt in layers, secure and centralize key management, and secure app and web encryption. This second triad of best practices delivers comparably critical importance and benefit to the first triad but often requires additional tools, resources, and buy-in to implement.
Use Appropriate Encryption
Eliminate known-bad or weak encryption and use the appropriate encryption for the task. Weak encryption algorithms (see below) no longer protect data because attackers easily break the algorithms or guess the keys using modern computing power. Security tools still include weak options to enable backward compatibility for previously encrypted data, but you should eliminate the current use of known-bad encryption.
Also, different types of encryption will be required for different uses. For example, asymmetric encryption uses public encryption keys to provide superior encryption for data transmission and data sharing, but asymmetric encryption will be too operationally intense to provide efficient and usable encryption for database fields, full-disk drives, or local files.
Learn the Encryption Environment
Assess and inventory encryption use throughout to replace obsolete protections and to ensure universal application of other encryption best practices. Just as with any other security practice such as asset discovery or data analysis, unknowns can’t be monitored or controlled.
Similarly, compare current encrypted data use against data use throughout the organization. Almost all organizations apply full disk encryption to servers to protect important data at rest, but sensitive data requires continuous protection and data use may require additional file, email, or database encryption.
Use the Longest Supportable Encryption Keys
Adopt password managers or centralized encryption management to offset the limited capacity of humans to memorize passwords and increase computing power to offset operational limitations. The longer the key, the stronger the security.
However, universally increased encryption keys increase costs and some organizations can’t afford using the strongest option for all data. The best approach usually restricts data to specific systems and then applies different key lengths for different purposes. For example, shorter keys protect less sensitive data on a laptop and longer keys protect sensitive data stored on a server.
Encrypt in Layers
Use multiple types and multiple layers of encryption to improve resilience against attacks. Just as with any other security technology, encryption requires defense in depth and multiple layers of encryption limit the damage possible from the failure of any single encryption solution – especially for the most critical data.
Each later hardens the environment and further resists unauthorized decryption attempts. For example, Microsoft recommends using disk encryption to encrypt data at rest, separate database encryption, and encrypted VPN gateways for data transmission.
Secure & Centralize Key Management
Use encryption experts and centralize encryption key management for improved security. Attackers target the weakest point and won’t need to spend resources to crack an encryption algorithm when the keys can simply be stolen. The more important the data, the more important it is that security professionals control and manage the encryption key process.
A fully trained security team can enact centralized key management to professionally generate, rotate, renew, and retire encryption keys. Centralized management enables higher security levels and improved security processes such as regular access or audit log reviews, encryption tracking within long-term backups, and secure access management of encryption resources.
Secure App & Web Encryption
Enable improved application and website encryption through professional tools and encryption education. The OWASP Top 10 lists the most serious and common vulnerabilities for developers (DevOps) and web application security. Cryptographic failures occupy second place on this list because of the poor management of encryption components, the use of weak encryption algorithms, or the improper deployment of encryption algorithms.
Weak encryption algorithms undermine security, but DevOps programmers don’t always possess the encryption expertise to recognize weak encryption. Security teams educate Dev teams with lists of approved and disallowed encryption algorithms or libraries to reduce weak encryption risk. DevOps further reduces this risk with application vulnerability scanners that detect inappropriate use of encryption.
Poor management of encryption components deviates from the principle of secured and centralized key management by leaking keys or improperly managing certificates. For example, maintain and secure web server secure sockets layer (SSL) digital certificates to facilitate encrypted connections and to prevent attackers from stealing and using corporate certificates in impersonation attacks.
Improper deployment of encryption tends to originate from programming mistakes or misunderstandings about how to execute complex encryption algorithm processes. Use an established encryption solution to avoid common issues such as failure to change variables, improperly generating random numbers for key generation, or using code that becomes vulnerable to malicious or unexpected inputs to the algorithm.
Strongest Encryption Options
With best practices in place, select the strongest encryption options. In many cases, encryption tools provide a selection that includes known-bad (covered below), good, and better algorithms. Yet the menu options rarely provide any clues as to which options provide in which category or which may be unsafe.
Encryption seen as good provides adequate protection, but select better encryption as time, capabilities, and budgets allow. The higher the risk of data theft or the more sensitive the data, the more urgently a transition to better encryption should be considered.
Currently, there’s no consensus for the “best” encryption because cost and use case play such a strong role in determining what any organization can deploy. Even newer quantum-resistant algorithms aren’t seen as superior solutions yet because they remain limited in commercial availability and simply haven’t been around long enough to be thoroughly tested.
Additionally, research the algorithms built into systems to determine if your organization needs to invest in stronger encryption options. For example, the bcrypt encryption library built into UNIX uses the Blowfish cipher (good encryption) and the Password-Based Key Derivation Function 2 (PBKDF2) uses RSA key standards (better encryption).
Good Encryption Options
Good encryption algorithms such as Blowfish, Triple DES, and WPA2 provide acceptable encryption, assuming that the organization also observes encryption best practices.
- Blowfish provides open-source symmetric encryption built into many Unix and Linux libraries for file and full-disk encryption; however, the use of a small block size limits its effective use to files under 4 GB.
- Triple DES (TDES or 3DES) can still be found used in older payment systems or to protect ATM pin codes but is considered vulnerable to the Sweet32 Birthday attack and was retired from Office 365 by Microsoft in 2019.
- Wi-Fi Protected Access Version 2 (WPA2) can be found in most wireless routers and provides reasonable protection for encrypted communications.
Retain less sensitive data currently encrypted using such protocols and allow less sensitive data to be transmitted using these encryption algorithms.
Better Encryption Options
Better encryption such as AES, ECC, RSA, Twofish, and WPA3 provide the current best-practice encryption options widely available and are superior to the good encryption algorithms (above).
- The Advanced Encryption Standard (AES), endorsed by NIST, supports encryption key sizes between 128 and 256 bits and uses both substitution and permutation transformations for encryption.
- Elliptic-curve cryptography (ECC) uses points on an ellipse to provide strong encryption with key sizes starting at 192-bits (default is 256 bits).
- Rivest-Shamir-Adleman (RSA) encryption uses large prime numbers as encryption keys that range between 512 and 4096 bits.
- Twofish encryption succeeds the Blowfish algorithm to provide improved encryption with key sizes between 128 and 256 bits.
- Wi-Fi Protected Access Version 3 (WPA3) provides improved encryption capabilities over WPA2 and should be adopted on supported wi-fi hardware.
Apply these better encryption standards to important, sensitive, and regulated data to provide stronger resistance to brute force and algorithm attacks.
Weak Encryption Examples
Professionals avoid broken or known-weak encryption standards such as DES, WEP, and WPA. Data previously encrypted using these standards should be actively re-encrypted using stronger algorithms (above).
- Data Encryption Standard (DES) provided the first NIST encryption standard, but the 56-bit keys are too short and vulnerable to brute force guessing attacks.
- Wired Equivalent Privacy (WEP) introduced wireless security as part of the IEEE 802.11 wireless standard, but severe algorithm design flaws render this algorithm obsolete and dangerous to use.
- Wi-Fi Protected Access (WPA) replaced WEP with improved encryption, yet remained vulnerable to spoofing attacks and was replaced by WPA2 and WPA3.
Many older computer protocols, such as secure sockets layer (SSL) and the original transport layer security (TLS) standards, also incorporate obsolete encryption algorithms. IT security teams must locate and disable the use of these older protocols throughout the organization.
Bottom Line: Evaluate Encryption Solutions Regularly
The strongest encryption of the 1970s didn’t survive replacement by stronger encryption in the 1990s. Yet those once-strongest encryption options of the 90s now show weaknesses to modern computing power. Fortunately, even as the increased computing power undermines older encryption standards, the computing power also enables the adoption of stronger, more complex encryption with larger key sizes.
Effective deployment of best practices creates a security environment that enables continuous management and evaluation of encryption processes. Upgrading encryption tools will usually be sufficient to maintain encryption as a fundamental layer in any security stack, but continue to evaluate encryption options regularly to remain secure.




