What is a CASB?
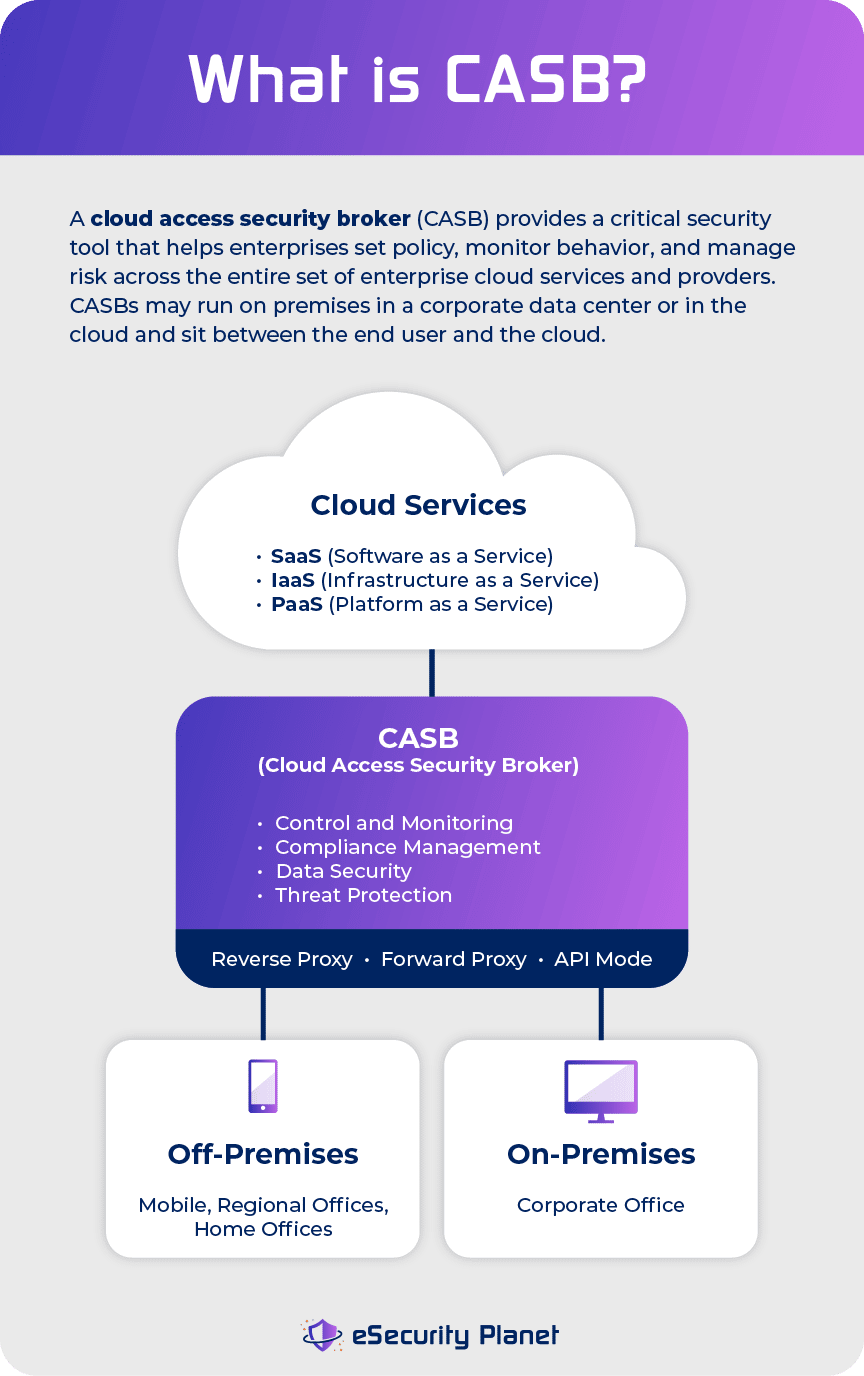
A CASB provides enterprises with a critical control point for the secure use of cloud services across multiple cloud providers. Software as a service (SaaS) apps are becoming pervasive in enterprises, which exacerbates the frustration of security teams looking for visibility and control of those apps.
CASB sales have soared as cloud security concerns have grown, especially the use of “Shadow IT” cloud services that IT security teams don’t know about.
See our picks for top CASB solutions and top cloud security products
CASB solutions fill many of the security gaps in individual cloud services and allow information security professionals to do it across cloud services, including infrastructure as a service (IaaS) and platform as a service (PaaS) providers. As such, CASBs address a critical enterprise requirement to set policy, monitor behavior, and manage risk across the entire set of enterprise cloud services being consumed.
 A CASB can consolidate multiple types of security policy enforcement. Examples of security policies enforced by a CASB include authentication, single sign on, authorization, credential mapping, device profiling, encryption, tokenization, logging, alerting, and malware detection and prevention.
A CASB can consolidate multiple types of security policy enforcement. Examples of security policies enforced by a CASB include authentication, single sign on, authorization, credential mapping, device profiling, encryption, tokenization, logging, alerting, and malware detection and prevention.
A CASB vendor also gives enterprises visibility into authorized and non-authorized cloud usage. It can intercept and monitor data traffic between the corporate network and cloud platform, assist with compliance issues, offer data security policy enforcement, and prevent unauthorized devices, users, and apps from accessing cloud services.
In the all-important area of data security, a CASB provider enforces corporate data security policies to prevent unwanted activity based on data classification, data discovery, and user activity monitoring. Policies are applied through controls, such as audits, alerts, blocking, quarantine, deletion, and encryption, at the field and file level in cloud hosting services.
CASB solutions include control and monitoring, risk and compliance management, threat protection, and cloud data security.
CASB use cases
A CASB has multiple use cases for the enterprise.
Secure shadow IT
One major use case is to discover, monitor, and secure shadow IT — the unauthorized use of cloud services by line-of-business staff. Because IT teams are not aware of shadow IT, it is not subject to corporate security, compliance, and governance policies. This exposes enterprises to significant security risks.
According to a recent survey of more than 2,000 IT pros by Intel Security, almost 40 percent of cloud services are now commissioned without the involvement of IT. As a result, 65 percent of IT professionals think shadow IT is interfering with their ability to keep cloud usage safe and secure. More than half of respondents said they have tracked malware from a cloud application.
Despite cloud security worries, 62 percent of respondents store sensitive customer information in the public cloud. Also, the number of companies using private cloud only has dropped from 51 percent to 24 percent over the past year, while hybrid cloud use has increased from 19 percent to 57 percent.
Govern device usage
CASBs can monitor and control user activities when users are accessing cloud services from a mobile or desktop app or sync client, govern access to public cloud services by device ownership class, monitor privileged accounts and prevent unauthorized activity in the cloud, monitor and control user activities with collaboration tools and social media without blocking those services, and monitor and control advanced or cross-service activities in real time.
Secure data
In terms of securing data, CASBs can prevent data exfiltration from a sanctioned to an unsanctioned cloud service, enforce different policies for personal and corporate instances of the same cloud service, enforce a policy at the activity or data level across a category of services, enforce conditional activity-level policies, enforce layered policies, and apply encryption.
Block malware
To protect against threats, CASBs can block or remediate malware in sanctioned cloud services and to and from unsanctioned cloud services, detect and alert enterprises about user login anomalies, detect anomalies such as excessive downloads, uploads, or sharing with both sanctioned and unsanctioned cloud services, and prevent data infiltration involving new employees.
Where CASBs run
CASBs may run on premises or in the cloud. Logically, CASBs sit between the end user and the cloud, but physically a CASB has to be located in one of two places: in a corporate data center or in the cloud itself. That means you have a choice between using a cloud access security broker as a service or hosting one on a physical or virtual appliance.
The SaaS option is easier to manage and is the more popular option, according to Gartner, but in certain industries you may have to use an on-premises system for compliance reasons.
How CASBs work
There are two key ways that a CASB can work. It can be set up as a proxy — either a forward or a reverse proxy — or it can work in API mode, using cloud providers’ APIs to control cloud access and apply corporate security policies. Increasingly CASBs are becoming “mixed mode” or “multi-mode,” using both proxying and API technology. That’s because each approach offers pros and cons.
Forward proxy
For example, a forward proxy can be used for all types of cloud applications and all data passes through the proxy, but to use a forward proxy you need to install self-signed certificates on every single device that accesses the proxy. This can be difficult to deploy in a distributed environment or one with a large number of employee-owned mobile devices.
Reverse proxy
A reverse proxy system is easier in that respect because it is accessible from any device, anywhere, without the need for special configuration or certificate installation. The drawback is that a reverse proxy can’t work with client-server type apps, which have hard-coded hostnames.
API-based systems
API-based systems are also easy to deploy. One drawback, however, is that the range of cloud applications they can work fully with is more limited because not all cloud applications provide API support.
“Proxy or API architectures from CASB have different abilities to perform different actions, which have various implications for how that provider delivers the four pillars for a specific cloud service,” Gartner says.
But over the next few years, Gartner expects many cloud service providers to develop their APIs significantly. “In the long term, APIs have the potential to obviate having to intercept traffic with proxies if they mature to the point where real-time visibility and control become possible,” it says.
One CASB may not be enough
The capabilities of CASBs — forward proxy based, reverse proxy based, API based or multimode — vary. It’s important to understand that just because a particular application is supported by a CASB, it doesn’t mean that it is supported to the same extent as another CASB.
It’s also the case that the range of applications supported by a CASB varies. That makes choosing a cloud access security broker that supports the applications you use now, and are likely to use in the future, a challenge. Back-office apps like CRM, HR and ERP are generally well supported, but industry-specific apps (for example for the health care industry) are less so.
Gartner’s advice? “Be cautious when entering into long-term contracts. Build in flexibility, because you may need more than one CASB or you may need to transition from your current provider to one delivering a complete set of your use cases during the next two years.”
CASB market size and vendors
There has been significant growth and activity in the CASB market over the last few years. The CASB market is expected to grow from $3.4 billion in 2015 to $7.5 billion in 2020, at a compound annual growth rate of 17.6 percent, according to a report by MarketsandMarkets.
The increasing adoption of cloud-based applications, such as Office 365, Salesforce, Google Apps and Box, by enterprises is playing a major role in fueling the growth of the market, according to the report.
More than a dozen CASB startups have launched since 2010, and a number of the major CASB vendors have recently been acquired by bigger players in the enterprise security and IT markets.
For example, in 2015, Microsoft gobbled up Adallom and then launched its Cloud App Security unit to complement its other identity and security products, such as Azure Active Directory, Microsoft Advanced Threat Analytics, and Azure Information Protection. Also in that year, Palo Alto Networks acquired CirroSecure, Blue Coat acquired Perspecsys and Elastica, Deloitte partnered with Bitglass, Check Point Software partnered with FireLayers, and IBM launched its Cloud Security Enforcer product.
In 2016, security powerhouse Symantec acquired Blue Coat for a staggering $4.65 billion in cash, indicating the value of CASB vendors to enterprises. Symantec decided to keep Blue Coat as a separate unit rather than incorporate its capabilities into Symantec’s product offerings the way Microsoft handled Adallom. Also in 2016, IT behemoth Cisco bought CloudLock for around $300 million, Proofpoint acquired FireLayers for $55 million, and Oracle bought Palerra for an undisclosed consideration.
In 2017, Raytheon, through its Forcepoint unit, acquired Skyfence from Imperva for an undisclosed consideration. For its part, Imperva acquired Skyfence in 2014.
Major CASB vendors include:
- Bitglass
- Blue Coat (owned by Symantec)
- CipherCloud
- CloudLock (owned by Cisco)
- Forcepoint (through Skyfence acquisition; owned by Raytheon)
- Microsoft (through Adallom acquisition)
- Netskope
- Skyhigh Networks (acquired by McAfee)
For more information, see our list of the top CASB vendors.
According to a recent Forrester Wave report on the CASB market, Blue Coat and Skyhigh Networks are market “leaders,” with strong offerings across a range of capabilities. Blue Coat integrates a cloud security gateway with its on-premises secure web gateway, while Skyhigh Networks offers shadow IT detection and extensive application support.
CipherCloud and CloudLock are “strong performers,” with CiperCloud offering “robust” structured data protection and on-device encryption, while CloudLock provides an intuitive product with “great reporting features.”
Bitglass, Netskope, and Skyfence are “contenders,” with Bitglass having an “easy-to-use” solution, Netskope offering extensive data loss prevention and pattern matching algorithms, and Skyfence providing extensive IaaS support and a large partner network. Microsoft is at the back of the pack as a “challenger,” with application programming interface monitoring, but with more features scheduled for deployment as of the fourth quarter of 2016.
The CASB market has evolved rapidly since its recent beginnings and has become a necessary cloud security control technology, regardless of the industry vertical, for enterprises adopting multiple cloud services and transferring sensitive data to the cloud.
This article includes previous reporting by Paul Rubens




