The top-ranked IBM X-Force Exchange threat intelligence platform (TIP) integrates enterprise-grade external security threat information with the tools a security professional needs to analyze how the threat might impact the organization. This article provides more in-depth information on the product and its features.
For a comparison with other TIP products, see the complete list of top threat intelligence companies.
Product History
Internet Security Systems developed X-force in 1996 and ISS was later acquired by IBM in 2006, after which the X-Force brand became part of IBM Security. The X-Force Exchange threat intelligence platform (TIP) was launched in 2015 to open up the wealth of threat intelligence collected by IBM X-Force to the public to support collaborative defense.
Product Description
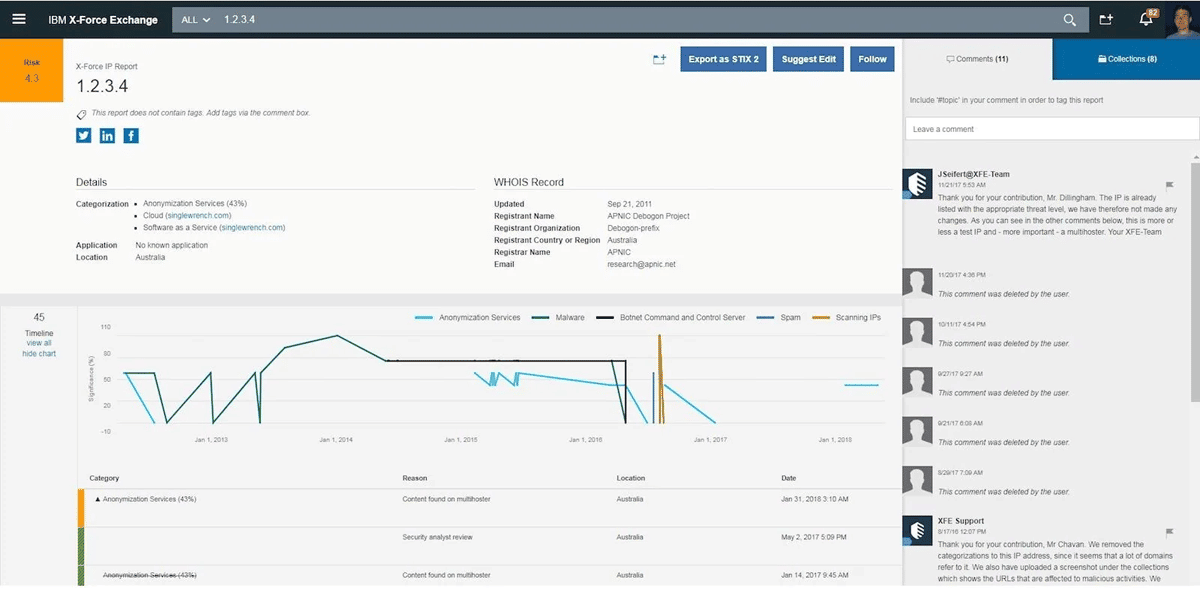
IBM X-Force Exchange provides collaborative threat intelligence through a cloud-based platform that enables security analysts to research threat indicators and accelerate responses to attacks. It offers intelligence on:
- IP and URL reputation
- web applications
- malware
- vulnerabilities
- spam
Users can then enhance their security insights with machine-generated intelligence and curated human-generated insights from IBM X-Force researchers available via public case file collections on the latest malware campaigns and threats.
“Users can collaborate with peers to validate threats and develop response plans using private groups and shared collections, and strengthen their existing security solutions with threat intelligence delivered through open standards,” said Sam Dillingham, Senior Offering Manager, IBM Security.
Agents
X-Force Exchange is a cloud-based platform, and does not deploy via agents.
Markets and Use Cases
In 2015, when IBM launched the X-Force Exchange it noted that six of the world’s top 10 retailers and five of the world’s top 10 banks were part of the 1,000+ organizations contributing to the X-Force Exchange threat database. In 2016, IBM also announced shared threat intelligence feeds with Check Point. With integrated workflow support through private groups and Collections, X-Force Exchange appeals to organizations that need to support a streamlined security investigation process.
One retailer, noted Dillingham, replaced multiple threat intelligence feeds with X-Force Exchange to dramatically reduce their investigation time. This retailer is using shared collections to gather threat intelligence, letting the security team focus on applying the intelligence rather than on the mechanics of gathering it.
However, for organizations that want to incorporate multiple feeds, external feeds can also be fed into an organization’s X-Force Exchange dashboard. The TIP will then generate a consolidated threat feed based on all information sources.
Applicable Metrics
As a cloud based platform, X-Force Exchange scales to support any size organization. Customersare allowed unlimited queries via the platform itself per month or through the Advanced Threat Protection Feed. The X-Force Exchange Commercial API supports usage-based billing. As noted above, additional third-party threat intelligence feeds can be brought into X-Force Exchange using the Threat Feed Manager once a user provides their credentials or API key for those feeds via the platform.
Security Qualifications
Depending upon the chosen edition, the IBM X-Force Exchange can meet the standards necessary to satisfy global compliance standards such as: ISO 27001, ISO 27017, ISO 27018, and both the EU-US Privacy Shield and Swiss Privacy Shield frameworks.. As a threat intelligence platform, X-Force Exchange can provide automated threat feeds to other qualified security systems such as firewalls, network intrusion detection (IDS) and prevention systems (IPS or IDPS), etc.
Intelligence
Users can enhance their network security insights with machine-generated intelligence. Threat intelligence from X-Force Exchange is also used by IBM QRadar Advisor with Watson so security analysts can leverage machine learning on the QRadar SIEM platform and the QRadar SOAR (Security Orchestration, Automation and Response) product.
All threat intelligence produced is cross-correlated against relevant sources used by X-Force Exchange, and this analysis is automated into reports that provide real-time visibility into risk score, activity history, geography, associated indicators, categorization and other pertinent threat intelligence. Customers of the X-Force Exchange Commercial API and the X-Force Exchange Enterprise API can also access additional reports and Indicators of Compromise (also available for the Advanced Threat Protection Feed) produced by X-Force IRIS (Incident Response and Threat Intelligence Services).
Delivery
X-Force Exchange is a cloud-based solution, accessible via a web browser or through an API interface to interface directly with existing security solutions.
Pricing
IBM X-Force Exchange is free to use via a guest login through the web interface at xforce.ibmcloud.com. A free X-Force Exchange non-commercial API is also available for limited use. For commercial use, IBM publishes information on four editions, but requires direct contact to obtain a quotation.
- X-Force Exchange
- Cloud based intelligence sharing platform
- Unlimited record access
- Limited Support
- Advanced Threat Protection Feed
- Unlimited Record Access
- Threat feed for internal security tool integrations
- RESTful API in JSON format
- X-Force Exchange Commercial API
- For integration with commercial applications
- Perform bulk-queries for IPs and URLs
- Usage Based records
- RESTful API in JSON format
- Includes X-Force IRIS (incident response service) reports and indicators of compromise
- X-Force Exchange Enterprise API
- Unmetered bulk usage of threat feeds and premium content
- Unlimited Records
- RESTful API in JSON format
- Includes X-Force IRIS (incident response service) reports and indicators of compromise
This article was originally written by Drew Robb on July 18, 2017, and updated by Chad Kime on February 1, 2023.






