Organizations are under pressure on both the cybersecurity and staffing fronts. They often struggle to fill vital security roles such as security analysts, leaving their data and infrastructure vulnerable to attacks at a time when cyber threats are soaring.
One way to alleviate the strain on security operation centers (SOCs) is to reinforce the security posture via a security orchestration, automation, and response (SOAR) platform.
What is SOAR?
SOAR is a threat management strategy that involves developing automated incident response activities toward cybersecurity threats. The strategy blends operations, automation, and response processes to reduce cybersecurity threats via automated security tasks, faster threat response, and better collaboration across departments and teams.
SOAR builds on SIEM (security information and event management) systems’ ability to ingest logs from hardware and software to look for threats and to provide a centralized management and response interface for security tools like EDR and firewalls.
And as cyber attackers become ever more sophisticated, so too have the technologies and tools that companies must buy to address rising threats, such as IDPS, UEBA, threat intelligence, patch management, encryption, DLP, DDoS protection, vulnerability management, and even mobile security management.
Securing a distributed enterprise wouldn’t be possible without a central layer speeding detection and response. The problem is that the gazillion security alerts generated by all those log and security sources are challenging to manage even after significant tuning has taken place. The obvious solution to that problem is to automate as much of alerting and response as possible, hence the rise of SOAR tools. Reducing human intervention also lowers operational costs, a tangential benefit from automation.
Gartner sees SOAR tools as using “alerts from the SIEM system and other security technologies—where incident analysis and triage can be performed by leveraging a combination of human and machine power—[to] help define, prioritize, and drive standardized incident response activities.”
There are also newer, similar approaches to centralized security management, like XDR (extended detection and response) and now the cybersecurity mesh, but SOAR is a more mature and better defined market and thus a prime tool for beginning the journey of security automation.
Also read: SIEM vs. SOAR vs. XDR: What Are The Differences?
Why Implement SOAR?
SOAR is a collection of security software that has the purpose of accelerating incident investigation and response. It helps raise the visibility of security data, streamline IT processes, reduce redundant and repetitive work, increase the level of collaboration among security tools, and add automation to a multitude of security-related manual tasks.
SOAR, then, brings coordination, execution, and automation to the many security tasks that exist on a broader security platform. By doing so, the speed of cybersecurity response is raised, which is handy in the face of cyberattacks and the barrage of security alerts that can be impossible to prioritize.
The Best SOAR Vendors
We examined the SOAR market to find the best tools by researching features, product maturity, analyst and user input, growth and more. We narrowed our selections to give you this list of the top 8 SOAR vendors.
Rapid7
InsightConnect is Rapid7’s security orchestration, automation and response solution. It enables security teams to accelerate time-intensive, manual incident response and vulnerability management processes. It also provides the security automation layer of the overall Rapid7 Insight Platform.
Key Differentiators
- 300+ integrations with IT and security systems to automate incident response and vulnerability management and patching
- Easy to import, build, and deploy automated workflows without coding
- Hundreds of available workflows in the Rapid7 Extensions Library
- Integration with Rapid7 XDR and Rapid7 vulnerability management tools to trigger automated management and communications of incidents and vulnerabilities
- Chat-driven automations
- Customers can contribute workflows back to the community
- ROI tracking for deployed workflows
Also read: Testing & Evaluating SIEM Systems: A Review of Rapid7 InsightIDR
Splunk
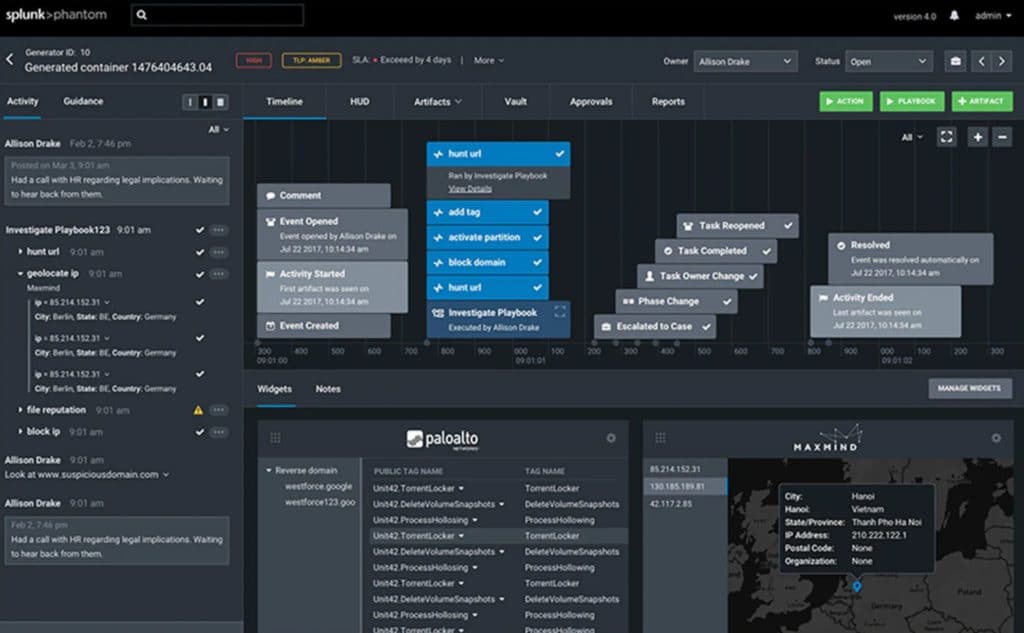
Splunk SOAR (formerly Splunk Phantom) allows analysts to improve efficiency and shorten incident response times. It heightens the scalability, performance, and speed of security automation with the ability to process 50,000 security events per hour. It also helps to knit security teams, processes, and tools together.
Key Differentiators
- Security teams can automate tasks, orchestrate workflows, and support a range of SOC functions including event and case management, collaboration, and reporting
- Executes automated actions across security infrastructure in seconds
- Teams can codify workflows into automated playbooks using the visual editor (no coding required) or the integrated Python development environment
- Acts as the connective tissue that lets existing security tools work better together
- Ensures each part of the SOC’s layered defense is actively participating in a unified defense strategy
- Abstraction allows teams to focus on what they need to accomplish, while the platform translates that into tool-specific actions
- Helps security teams investigate and respond to threats at machine speed, reduce malware dwell time, and lower mean time to resolve (MTTR)
Siemplify
Now part of Google Cloud, the Siemplify Security Operations Platform combines simplicity and a good user experience to help an SOC move beyond the daily cyber grind and concentrate on what matters most: building resiliency and investigating and remediating real threats fast.
Key Differentiators
- Siemplify and Google Chronicle provide the cloud-native workbench security operations teams need to respond at scale
- Builds playbooks that orchestrate hundreds of tools with drag-and-drop functionality
- Automates repetitive tasks
- Drives continuous improvement with machine learning-based recommendations and analytics for visibility of SOC activity
- Provides an intuitive analyst experience that boosts productivity with
customization capabilities
ManageEngine
ManageEngine Log360 gathers security data from various sources in the network including Active Directory (AD) users, groups, and organizational units; network devices such as firewalls, servers, and endpoints; and applications such as vulnerability scanners, data loss prevention software, threat applications, and more.
Key Differentiators
- Log360 provides security context to data to identify security events quickly and accurately
- Streamlines incident management with ITIL tool integrations
- Accountability for incident resolution by utilizing ticketing tool integration to assign detected incidents to security administrators
- Configuration of external help desk solutions, such as ServiceNow, ManageEngine ServiceDesk Plus, Jira Service Desk, Zendesk, Kayako, and BMC Remedy Service Desk
- Prebuilt workflows for common use cases
- Ensures no critical security incidents slip through the cracks
- Automatically executes a series of common remedial measures based on the type of security incident detected
- When alerts are triggered, automate response workflows mitigate network security incidents before they cause any damage or result in a breach
- Disables or deletes a potentially compromised AD user or computer in your AD environment
- Can terminate a process on a potentially compromised Windows device
Trellix
FireEye merged with McAfee Enterprise to form Trellix. It remains to be seen how this will impact the FireEye Helix SOAR product, which reduces security risk with security operations, automation, and reporting and automatically escalates higher priority incidents.
FireEye Helix is available stand-alone or with the purchase of FireEye’s subscription-based solutions. It works across all FireEye technologies and helps integrate non-FireEye security products.
Key Differentiators
- Applies workflow automation, customizable dashboards, and prebuilt playbooks that allow analysts to focus on high-priority tasks that reduce risk exposure
- Hundreds of third-party plugins to firewalls, antivirus, and ticketing systems
- Customizable and automated workflows to reduce analyst workloads
- 400+ prebuilt courses of action developed by FireEyeincident responders
- Integrates more than 150 third-party tools and data sources for single-pane management of the security stack
- Implements custom incident response workflow automation between security appliances
- Enables collaboration between analyst and incident response teams by storing correlated alerts and artifacts in a case management system
LogRhythm
LogRhythm RespondX, part of the LogRhythm SIEM platform, delivers the tools an SOC team needs to simplify complex processes, speed workflows, and make security operations more efficient. It streamlines security workflows by coordinating and automating multiple steps in the response workflow.
Key Differentiators
- Helps SOC teams collaborate, qualify, and manage incidents
- Provides drill-down, search pivoting, context enrichment, and other investigative capabilities
- Dissects complex use cases into manageable pieces that can be automated with LogRhythm SmartResponse automation
- By using standardized processes with Case Playbooks, the security team can execute tasks efficiently
- Reduces time to qualify and investigate threats
- Reduces manual security tasks and platform switching
- Captures incident response milestones and complete audit trails for reporting
IBM
IBM Security QRadar SOAR, formerly Resilient, is designed to help security teams respond to cyber threats with confidence, automate with intelligence, and collaborate with consistency. It guides teams in resolving incidents by codifying established incident response processes into playbooks.
Key Differentiators
- The open, agnostic platform helps accelerate and orchestrate response by automating actions and integrating with other security tools
- Visibility into incident progression and timely notifications
- Minimizes the duration and impact of cyberattacks by automating manual tasks, allowing security to focus on high-value investigations
- Automatically correlates security alerts against threat intelligence feeds for malicious indicators and integrates malware analysis into incidents after sandbox detonation
- Establishes a central hub that helps prepare for and respond to privacy breaches efficiently
Palo Alto Networks
Cortex XSOAR by Palo Alto Networks helps IT to orchestrate and automate incident response workflows and processes across the environment. It discovers, consumes, and shares orchestration integrations and automation innovations contributed by experts in the world’s largest SOAR ecosystem via the Marketplace.
Key Differentiators
- 750+ integrations and 680+ content packs for a range of security use cases
- Automation packs can be used out of the box or configured to your needs
- Scales to support hundreds of clients or teams
- Manage all security incidents from one location
- Full ticket mirroring with tools such as ServiceNow, Jira, and Slack to automate ticketing tasks and manage tickets from XSOAR
- Tie external threat intel to incidents in real time, and automate distribution to enforcement points at scale. It’s said to reduce time spent managing threat intel by 90%
- Machine learning-powered platform provides guidance based on past incidents and analyst actions
- Orchestrates and automates incident response workflows across all security areas (SecOps, NetSecOps, CloudSecOps) and products
- Security-focused case management with incident-specific layouts, real-time collaboration, customizable reporting, and a war room for each incident
Read next: Best Incident Response Tools and Software




