Application security tools and software solutions are designed to identify and mitigate vulnerabilities and threats in software applications. Their main purpose is to protect applications from unauthorized access, data breaches, and malicious attacks.
These tools play a vital role in ensuring the security, integrity, and confidentiality of sensitive information, such as personal data and financial records. By employing application security tools, organizations can proactively identify and address potential security flaws, reducing the risk of exploitation and minimizing the impact of security incidents.
Here we’ll take an in-depth look at five of the top application security tools, followed by features buyers should look for and an examination of different approaches to application and code security.
Also read: Application Security: Complete Definition, Types & Solutions
- GitGuardian Internal Monitoring: Best for dedicated secrets scanning
- Veracode: Best for programming language support
- GitLab: Best for DevOps
- Qualys Cloud Platform: Best for vulnerability management
- Trend Micro Cloud App Security: Best for SaaS protection
- Other Application Security Vendors to Consider
- Key Features of AppSec Software
- Code Analysis and Testing Types
- AppSec vs DevSecOps
- How We Evaluated Application Security Software
- Bottom Line: Application Security Tools
| Application security tool | Key feature | Price | Best for |
|---|---|---|---|
| GitGuardian Internal Monitoring | Real-time automated public and private repositories monitoring | FreeBusiness: $477 to $3667Enterprise: Custom quotes | Dedicated secrets scanning |
| Veracode | Static, dynamic, and software composition analysis | Get a quote from their Contact Us page or visit authorized vendors CDW and AWS. | Programming language support |
| GitLab | Version control system and DevOps platform | FreePremium: $24/user Ultimate: $99/user |
DevOps |
| Qualys Cloud Platform | Vulnerability management | $300 for small businesses to $2,000 for larger packages | Vulnerability management |
| Trend Micro Cloud App Security | SaaS platform protection | Get a quote from Trend Micro’s online calculator found on their website. | SaaS programs |

GitGuardian Internal Monitoring
Best dedicated secrets scanning
GitGuardian, established in 2017, focuses on securing sensitive information and secrets stored in source code repositories. It specializes in detecting and preventing the exposure of API keys, credentials, certificates and other confidential data. It offers real-time scanning, integrations with popular version control systems like GitHub and GitLab, and alerts for potential security breaches related to sensitive data in code.

Key Features
- Real-time automated public and private repositories monitoring
- Internal Git repositories secrets detection
- Detection and remediation alerts
- Developer-driven incident response application
Pros
- Easy installation with a 30-minute quick-start guide
- Streamlined incident resolution and communication
- Focuses on critical issues, reducing remediation effort
- Automatic incident notifications for faster response
- GitHub integration for detecting code secrets and blocking merges
- Offers a free plan
Cons
- User interface could offer better usability and ease of access
- Sensitive data and new repository activities alerts could be better
- Needs more detailed reports with additional metrics and information
Pricing
| FREE | Business | Enterprise |
|---|---|---|
| $0 | $477 – $3667 | Custom Pricing |
| Individual developers and teams of 25 members or fewer | 26 developers to 200 developers | Contact sales team or book a demo |

Veracode
Best for programming language support
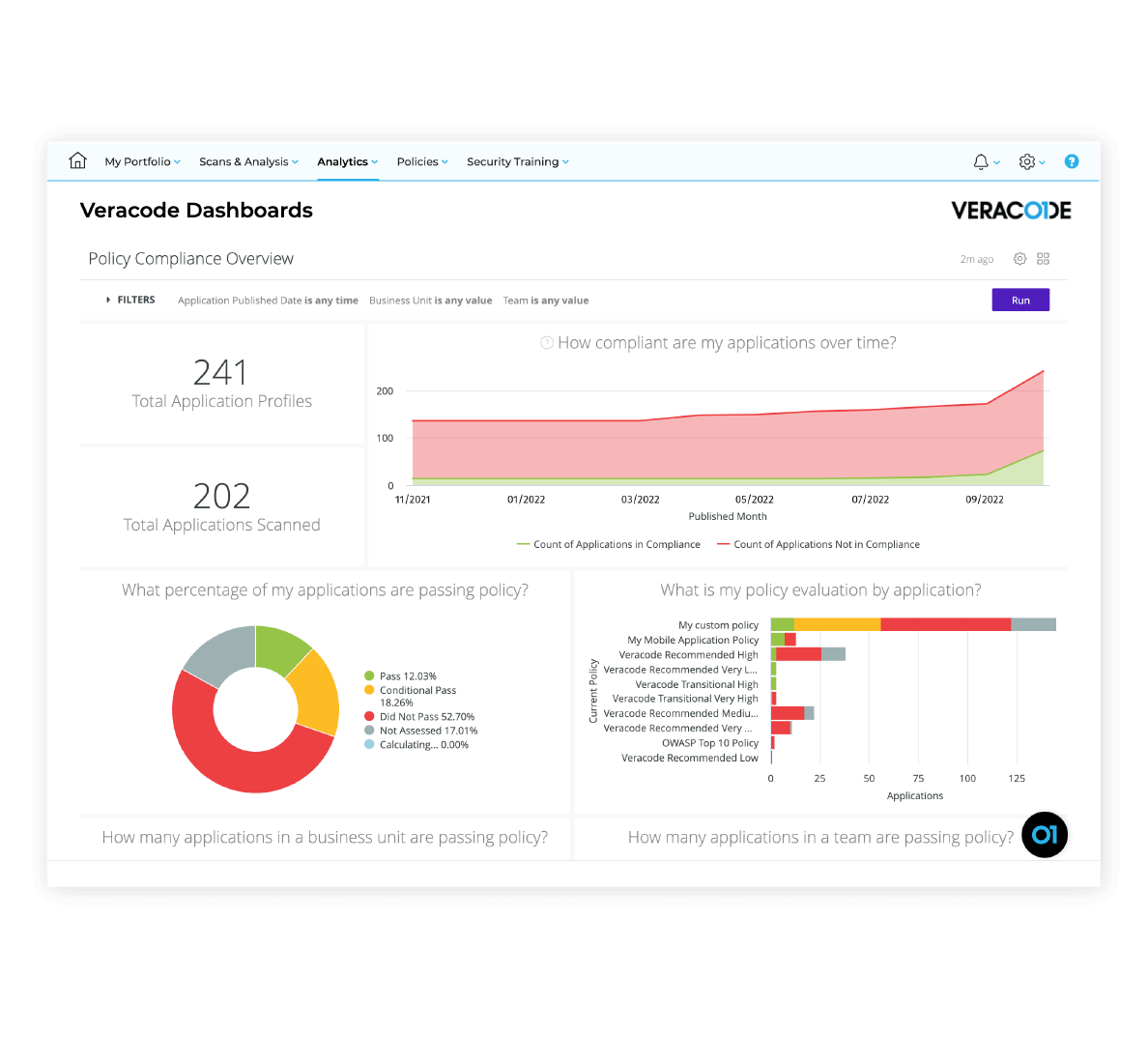
Veracode is a comprehensive application security tool that provides static, dynamic, and software composition analysis. It offers a wide range of security testing capabilities, including code scanning, vulnerability assessment, and penetration testing. Veracode supports more than a hundred programming languages and provides detailed reports on security vulnerabilities and weaknesses in applications.
Key Features
- Static Application Security Testing
- Dynamic Application Security Testing
- Software Composition Analysis
- Interactive Application Security Testing
- Security Development Training and eLearning
- Application Security Program Management
- Integrations and APIs
- Reporting and Analytics
Pros
- Accurate vulnerability scanning
- Highlights the risk level and severity of the vulnerabilities
- Comprehensive library of remediation guidance
- Comes with VisualStudio add-on
- Detailed reports on issues and fixes
- Excellent customer service
Cons
- The user interface can be challenging
- Users also report issues with slow performance and false positives
Pricing
Veracode customizes pricing based on the specific needs and features required by each business and does not publish pricing. CDW offers some pricing on Veracode plans and features, while AWS provides pricing for Veracode’s FedRAMP platform. To obtain a quote, contact Veracode’s sales team or visit their Contact Us page. Additionally, you can take advantage of a 14-day free trial.

GitLab
Best DevOps unified platform
GitLab is primarily known as a version control system and DevOps platform but also includes built-in application security features. It offers features like static application testing (SAST), dependency scanning, container scanning, and dynamic application security testing (DAST). GitLab integrates security testing into the development workflow, allowing for continuous security monitoring and mitigation.
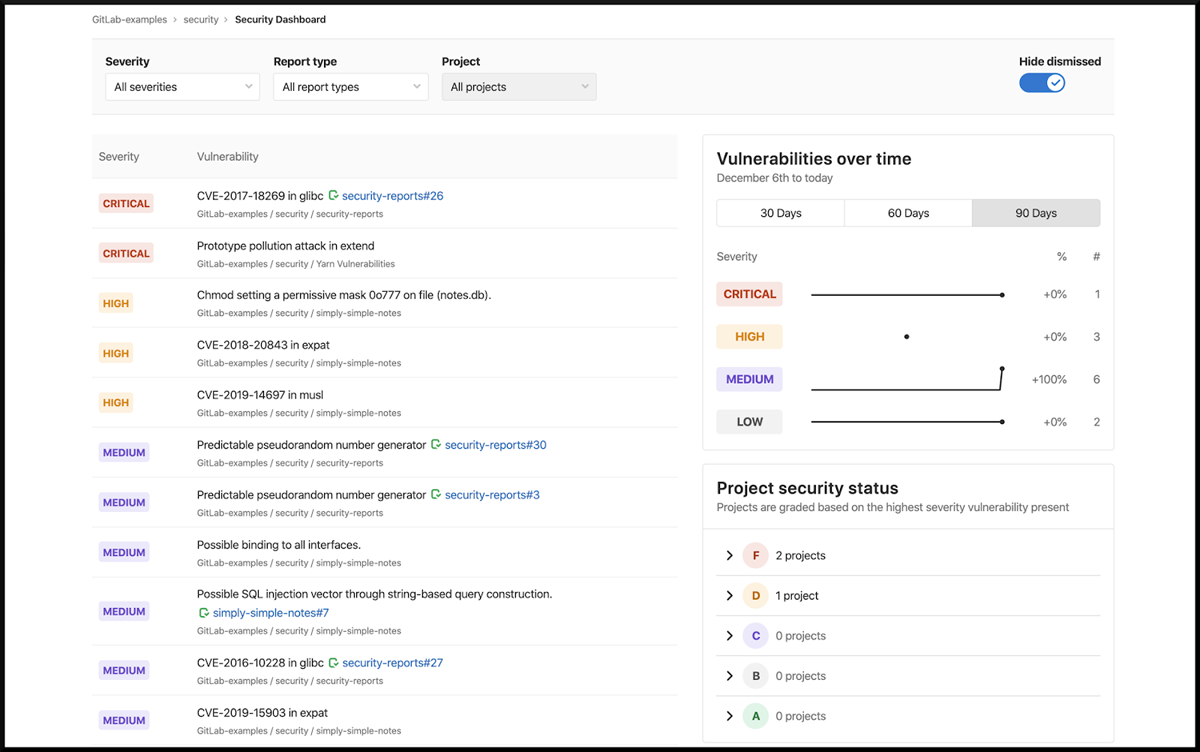
Key Features
- Static Application Security Testing
- Dynamic Application Security Testing
- Container Scanning
- Dependency Scanning
- License Scanning
- Coverage-guided Fuzz Testing
- API Security
Pros
- Version/source control
- User-friendly interface
- Streamlined Git CLI integration
- Seamless merge and merge requests
Cons
- Documentation could be more user-friendly and comprehensive
- Integration with third-party software could be better
- Can be challenging to navigate between branches within a repository
- Editing files in a browser can be challenging
- Error messages related to CI/CD could provide more detailed information
Pricing
| Free | Premium | Ultimate |
|---|---|---|
| $0/user | $24/user | $99/user |
| Limited features | Majority of GitLab’s features | All features |

Qualys Cloud Platform
Best for vulnerability management
Qualys is a cloud-based security tool that offers a suite of security and compliance solutions, including application security. It also provides web application scanning and vulnerability management tools. It offers scanning and assessment of web applications to identify vulnerabilities and potential security risks, with detailed reports and remediation. Perhaps more comprehensive than some organizations are looking for, Qualys’ security coverage is as complete as it gets.

Key features
- Continuous monitoring
- Vulnerability management
- Policy compliance
- PCI compliance
- Security assessment questionnaire
- Web application scanning
- Web application firewall
- Global asset view
- Asset management
- API, container and cloud data collection
Pros
- Automated web application scanning
- Automated reporting
- Cloud asset management
- Remediation guidance
- Patching
Cons
- 2FA options could be broader
- Adding domains and networks could be easier
- Discovery and scanning setup could be better integrated
- Module integration could be more seamless
Pricing
Qualys Cloud platform is licensed by customers on an annual basis, and the pricing is determined by factors such as the number of Cloud Platform Apps chosen, IP addresses, web applications and user licenses. Customers have categorized the pricing into three tiers: Express Lite, Express and Enterprise. While Qualys does not publicly disclose its prices, customers have shared that pricing packages can range from $300 for small businesses to $2,000 for larger packages. In addition, Qualys offers a 30-day free trial subscriptions to allow users to test services before committing to a purchase.
See the Top Vulnerability Management Tools

Trend Micro Cloud App Security
Best for SaaS platform protection
Trend Micro Cloud App Security focuses on securing cloud-based applications and services. It provides protection for SaaS platforms like Microsoft 365, Google Workspace, and others. It helps organizations ensure the security and compliance of their cloud-based applications, protecting sensitive data, preventing unauthorized access, and defending against threats.

Key features
- Workload security
- File storage security
- Container security
- Open source security
- Email, ransomware and malware protection
Pros
- Facilitates speedy application deployments
- Real-time protection and immediate blocking of unwanted activities during application runtime
- Prevention of malicious intrusions and protection against hacking or takeovers
- Safeguarding cloud applications from design and deployment issues
Cons
- Web support lacks clarity
- Remote endpoints with weak or intermittent internet connections often appear offline
- Settings are not well organized or clearly defined, requiring significant efforts to locate the desired option for modification
- Occasional false positives
Pricing
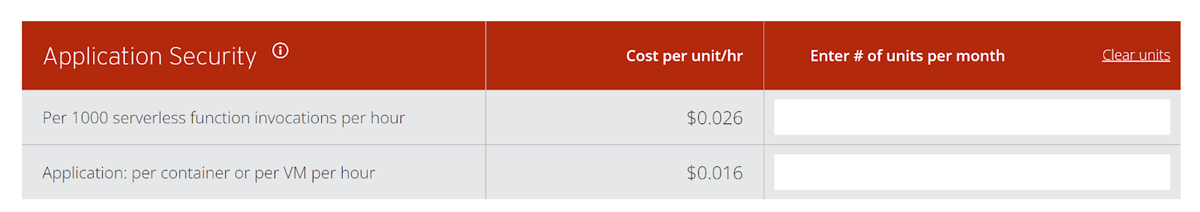
Trend Micro offers a user-friendly pricing calculator on its website, giving potential buyers a convenient way of determining an approximate cost tailored to their requirements.
Other Application Security Vendors to Consider
The application security market offers a broad range of tools to meet a variety of needs. Here are an additional seven names to consider, plus our lists of the top DevSecOps, code security, and vulnerability scanning tools.
- Acunetix
- Checkmarx
- Invicti (formerly Netsparker)
- Micro Focus Fortify
- Rapid7
- Snyk
- Synopsys
Also read:
- Top Code Debugging and Code Security Tools
- Best DevSecOps Tools
- Best DevOps, Website, and Application Vulnerability Scanning Tools
- Best Cloud, Container and Data Lake Vulnerability Scanning Tools
- Top Container Security Solutions
Important Features of Application Security Software
Application security tools offer a number of important features that contribute to the overall security posture of applications, protecting against unauthorized access, data breaches, and other security risks.
Authentication: Ensures that users or entities are verified and granted appropriate access based on their identity. It involves verifying credentials such as usernames and passwords, before granting access to applications. The tougher to steal, the better.
Authorization: Determines what actions and resources a user or entity is allowed to access or perform within an application. This enforces access control policies to prevent unauthorized access and restricts privileges based on roles or permissions.
Encryption: This protects sensitive data by converting it into a coded form that can only be accessed or decrypted with the appropriate key. Encryption ensures that data remains confidential and secure, even if intercepted or accessed by unauthorized parties.
Logging: Logs are records of events and activities within an application or resource that helps with monitoring and audits to identify common and unusual patterns of user behavior. Logging captures information about user actions, system events, and security-related incidents, providing a trail of evidence for troubleshooting, compliance, and forensic investigations.
Application security testing: Application security testing refers to the assessment and evaluation of applications for identifying vulnerabilities, weaknesses and security flaws. This includes different types of testing techniques such as static application testing, dynamic application testing, and interactive application security testing (more in the next section).
Auditing and accountability: Audit logs and accountability mechanisms help in compliance with regulations, detecting suspicious behavior and investigating security breaches. This tracks and monitors user activities and security-related incidents to establish accountability and traceability.
Vulnerability scanning: Vulnerability scanning identifies and assesses vulnerabilities within applications, networks, or systems. This allows organizations to proactively address potential security risks. Finding vulnerabilities in the open source dependencies that make up most modern applications is an increasingly critical feature.
Code security review: Code security review is an essential practice that helps identify and remediate potential security weaknesses and ensures applications are built with strong defenses against cyber threats.
WAF integration: Web application firewalls (WAF) are a crucial line of defense for web applications, inspecting traffic, enforcing security policies, and protecting against a wide range of web-based attacks such as SQL injection and cross-site scripting (XSS). Integrating WAFs with application security tools can provide critical information to developers and security teams, helping to protect applications from vulnerabilities until they can be fixed.
SIEM integration: Security information and event management systems (SIEM) collect and analyze security event data from various sources to detect and respond to security incidents. This provides centralized visibility, correlation of events, advanced analytics, and automated alerting, and can help identify application security issues.
Threat intelligence integration: Threat intelligence integrations enhance threat detection and provide real-time insights into emerging threats, including attack techniques and open source vulnerabilities, information that can help both dev and security teams.
Secure development lifecycle (SDL) support: SDL supports the integration of security practices and testing throughout the software development lifecycle, ensuring security is prioritized.
Learn more about Application Security
Featured PartnersFeatured Cybersecurity Software
eSecurity Planet may receive a commission from merchants for referrals from this website
Code Analysis and Testing Types
A key concept to understand in application security is that of the Software Development Lifecycle (SDLC). In that process, there are stages for code development, deployment and ongoing maintenance. As part of that lifecycle there are a number of critical application security approaches.
- Static Analysis: At the foundational level is the security of the application code as it is being developed, which is often an area where static code analysis tools can play a role. This area is called static application security testing, or SAST.
- Dynamic Analysis: For code that is running, dynamic application security testing (DAST) enables the detection of different types of security risks.
- Interactive Application Security Testing: Combining both DAST and SAST approaches is the domain of Interactive Application Security Testing (IAST).
- Software Composition Analysis (SCA): SCA addresses configuration issues, software dependencies and libraries that have known vulnerabilities, important issues in software supply chain security.
Also read: SBOMs: Securing the Software Supply Chain
AppSec vs DevSecOps
An interesting trend in the application security product market is that the many different kinds of tools — application security, code security, debugging, DevSecOps, and vulnerability scanning — have been coming together over time.
DevSecOps tools are perhaps the broadest of these products, encompassing developer tools, container implementation, monitoring tools, and more.
Vulnerability scanning, application security, and DevSecOps increasingly have considerable feature overlap, covering DAST, IAST, SAST, and SCA. There are some noteworthy differences however. DevSecOps tools typically have features for container, Ci/CD, and API management. Fuzzing is more likely to be a feature of vulnerability scanning tools, while AppSec will have a greater focus on Static Code Analysis.
See the Top DevSecOps Tools
How We Evaluated Application Security Software
In our evaluation of application security software, we assessed accuracy and effectiveness, breadth of features, ease of use, integration with development and security tools, automation capabilities, pricing, ideal use cases, and reporting functionality. Detailed reporting and vulnerability prioritization were two important factors, as they give dev and security teams the information they need to make risk-based decisions. Ease of use is generally important in this market, as non-security specialists are critical to the process. Integration capabilities are also crucial for the workflow, so the software should integrate and interact with existing development and security tools.
Bottom Line: Application Security Tools
When selecting an application security tool, it is important to prioritize your organization’s unique requirements and conduct a thorough search before making a purchase decision. To do this, prospective buyers should consider factors such as features and capabilities, supported programming languages, compatibility with existing infrastructure, scalability, ease of use, cost, and the level and quality of technical support provided. Additionally, it is important to involve key stakeholders such as IT security teams and developers in the decision-making process.
An application security tool is critically important for securing applications, the environments they run on, the data they contain, and the employees and customers who depend on them.
Read next: Software Supply Chain Security Guidance for Developers
This updates a November 2020 article by Sean Michael Kerner




