Cloud security companies specialize in protecting cloud-based assets, data, and applications against cyberattacks. They offer a variety of tools, products, and strategies to manage access restrictions, reduce threats in cloud-based environments, insure users, and comply with industry requirements. To help you choose, we’ve analyzed a range of cybersecurity companies offering cloud security products and threat protection services.
Here are the six best cloud security companies:
- Trend Micro: Best overall for cost and services
- Qualys: Best for regulatory compliance adherence
- Palo Alto: Best for unified platform management
- Zscaler: Best choice for advanced threat protection
- Lacework: Best cloud-native app protection tool
- Tenable: Best for secure cybersecurity insurance
Featured Partners: Cybersecurity Software
Top Cloud Security Companies & Vendors Comparison
This table provides a comparison of the cloud solutions offered by our top vendors, their unified platforms monitoring capability, cyber insurance coverage, compliance, and free trial details:
| Cloud Solutions | Unified Platforms Monitoring | Cyber Insurance Coverage | Compliance | Free Trial | |
|---|---|---|---|---|---|
| Trend Micro | • Attack Surface Risk Management for Cloud • XDR • Workload Security • Container Security • File Storage Security | Yes | Yes | • ISO 27001 • SOC 2 • GDPR • HIPAA 2023 • PCI-DSS • FedRAMP | 30 days |
| Qualys | • CWPP • CNAPP • CDR • CSPM • XDR | Yes | Yes | • ISO 27001 • SOC 2 • GDPR • HIPAA 2023 • PCI-DSS • FedRAMP • NIST | 60 days |
| Palo Alto | • CNAPP • CASB • CIEM • CSPM • CWPP | Yes | Yes | • ISO 27001 • GDPR • PCI-DSS • FedRAMP • NIST | 30 days |
| Zscaler | • DLP • CASB • Secure Internet Access • Secure Private Access • Digital Experience • Posture Control | Yes | No info | • ISO 27001 • SOC 2 • GDPR • HIPAA 2023 • PCI-DSS • FedRAMP | 30 days |
| Lacework | • CWPP • CNAPP • CIEM • CSPM | Yes | No info | • ISO 27001 • SOC 2 • NIST • GDPR | 14 days |
| Tenable | • CSPM • CIEM • Cloud Security • Vulnerability Management | Yes | Yes | • GDPR • HIPAA 2023 • PCI-DSS • FedRAMP | 7 days |
Table of Contents

Trend Micro
Best Overall for Cost & Services
Overall Rating: 4.6/5
- Cloud-Specific Services: 5/5
- Hybrid Environment Services: 5/5
- Pricing: 4.7/5
- Customer Support: 3.3/5
- Third-Party Integration: 5/5
- Compliance & Insurance: 4.7/5
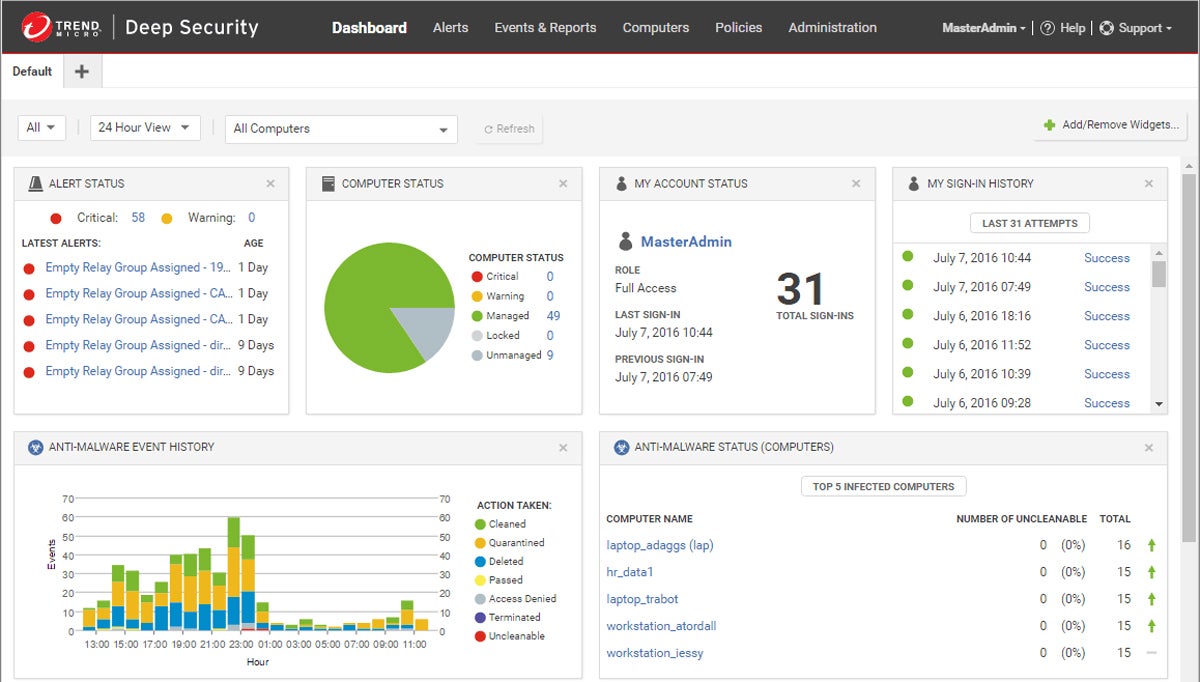
Trend Micro is a global leader in hybrid cloud security and provides an integrated and automated approach for protecting data, users, and applications. This unifies policies across both on-premises and public cloud deployments. It offers advanced security capabilities such as cloud workload protection, network security, file storage protection, application security, and open-source security. They provide visibility and control over the entire IT environment.
Trend Micro offers a wide range of cloud services and solutions, but if you’re specifically focusing on cloud-native application protection platform capabilities, see Lacework.
Pros & Cons
| Pros | Cons |
|---|---|
| Solutions are easy to scale | High costs of solutions |
| Runtime protection for workloads | Reporting functionality could be improved |
| Offers a range of free apps | VPN and password manager are for higher plans |
Pricing
- Free plan: Offers free apps for ID security, VPN, and network security
- Basic Windows security: Starts at $19.95 per year per user
- Premium security: Starts at $59.95 per year
- Custom plans: Contact for quote
- Free trial: 30 days
- Free demo: Contact to schedule
Key Features
- Integrated security: Integrates workload, storage, network security, and compliance capabilities through the Trend Micro Cloud One platform.
- Hybrid workloads: Extends the same policy and protection to on-premises, private and public cloud workloads with its workload security feature.
- Patching: Provides virtual patching for vulnerabilities to help limit risks as rapidly as possible.
- Templates: Codifies security with templates aligned with leading security standards and deployed with simple AWS CloudFormation templates.

Qualys
Best for Regulatory Compliance Adherence
Overall Rating: 4.4/5
- Cloud-Specific Services: 4.7/5
- Hybrid Environment Services: 5/5
- Pricing: 4.4/5
- Customer Support: 3.9/5
- Third-Party Integration: 3.9/5
- Compliance & Insurance: 4.7/5
Qualys is a cloud security and compliance software platform that helps enterprises identify and protect their digital assets. It provides a unified platform for security, compliance, and IT operations teams to identify all known and unknown assets in their global hybrid IT environment, providing a complete, categorized inventory. Qualys cloud platform has multiple modules that enable compliance, vulnerability scanning, malware detection, and cloud workload protection.
Qualys provides a good unified management platform, but for better platform integrations, explore Palo Alto Networks.
Pros & Cons
| Pros | Cons |
|---|---|
| Offers patch and vulnerability management | False positives |
| No-code, drag-and-drop workflows for fast fixes | Customer support needs improvement |
| Scalable solutions | Complicated interface for new users |
Pricing
- Free plan: Qualys Community Edition
- Custom plans: Contact for quote
- Free trial: 60 days
- Free demo: Contact to schedule
Key Features
- Vulnerability detection: Provides automatic scanning capabilities for web apps via the Web Application Scanning module to help detect and rank security vulnerabilities.
- Compliance: Offers multiple modules for compliance use cases, including the PCI-DSS module that scans all devices to identify compliance status.
- DevOps: Integrates with CI/CD toolchains such as Jenkins and Azure DevOps.
- Security: Includes a range of threat detection and response protections, web application firewalls, container security, and more.


Palo Alto Networks
Best for Unified Platform Management
Overall Rating: 4.1/5
- Cloud-Specific Services: 4.7/5
- Hybrid Environment Services: 4.4/5
- Pricing: 2/5
- Customer Support: 3.9/5
- Third-Party Integration: 5/5
- Compliance & Insurance: 4.2/5
Palo Alto Networks has one of the most comprehensive cloud native security platforms via Prisma Cloud, with deep capabilities to help organizations manage workload security. The company’s solutions are designed to provide visibility and control over applications, users, and content, reducing the risk of a data breach. Its unified platform management goes beyond traditional network security and includes cloud security, endpoint protection, and access control.
Palo Alto doesn’t provide pricing information on their website. For more transparent pricing information, check out Tenable.
Pros & Cons
| Pros | Cons |
|---|---|
| Continuously developing SASE, CNAPP, and cloud-delivered security services | Lack of transparent pricing |
| Protects hosts, containers, and serverless environments on any cloud platform | Customer support needs improvement |
| 700 pre-built cloud security policies | Limited optimization for SaaS applications |
Pricing
- Custom plans: Contact for quote
- Free trial: 30 days
- Free demo: Contact to schedule
Key Features
- Cloud native: Applies new Cloud Native Security Platform (CNSP) approach via Prisma Cloud platform.
- Broad protection: Integrates acquired components from multiple companies, including evident.io, RedLock, PureSec and Twistlock.
- Visibility: Provides full cloud workload visibility, including serverless functions with capabilities to secure an end-to-end cloud-native deployment.
- Cloud app protections: Offers vulnerability management and runtime protection against threats.


Zscaler
Best Choice for Advanced Threat Protection
Overall Rating: 4/5
- Cloud-Specific Services: 4.4/5
- Hybrid Environment Services: 5/5
- Pricing: 2.8/5
- Customer Support: 3/5
- Third-Party Integration: 4.3/5
- Compliance & Insurance: 4.3/5
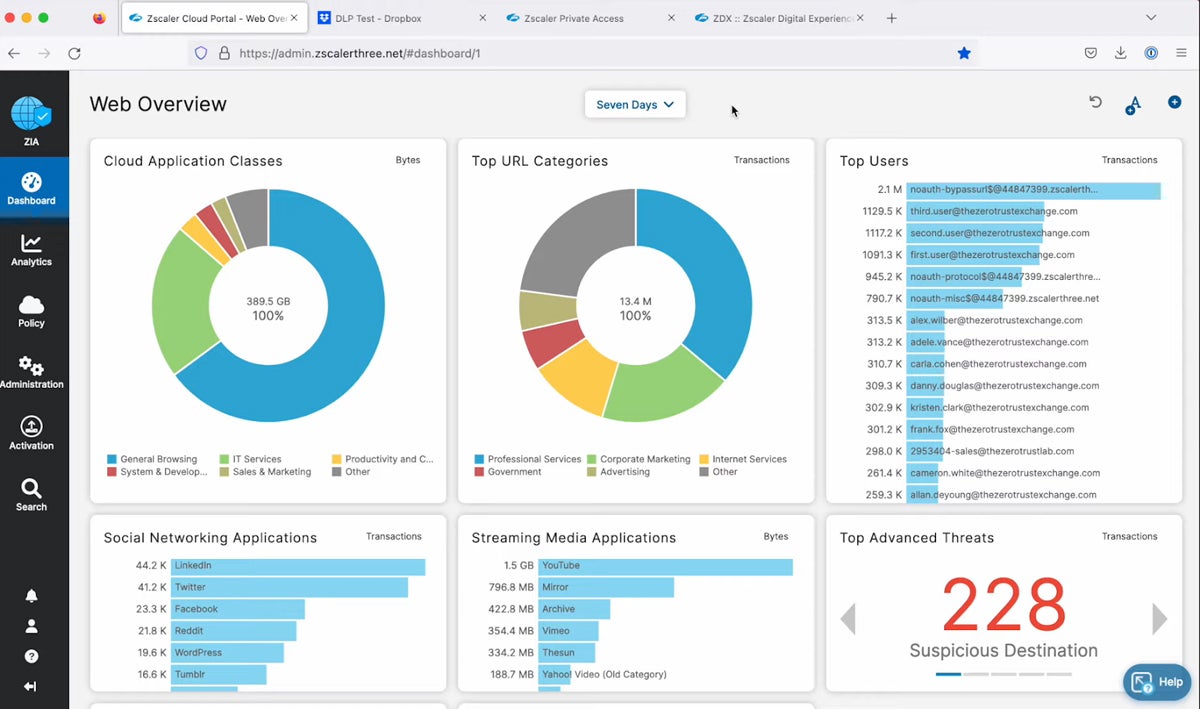
Zscaler is a cloud-based security company that protects users, data, and applications from cyberattacks. Its services cover the full spectrum of security needs, including advanced network security, web application firewalls, intrusion prevention, malware protection, zero trust, and DLP, to secure access for remote users and compliance with industry regulations. Zscaler provides secure web gateway (SWG), advanced threat protection (ATP), cloud sandboxing, and CASB services.
Zscaler is fully hosted online, thus limiting its on-premise services. If you’re looking for security solutions that cater to both on-premise and cloud, try Trend Micro.
Pros & Cons
| Pros | Cons |
|---|---|
| AI-powered advanced threat protection | Lacks transparent pricing |
| Strong deception technology | Reporting feature could be improved |
| Easy to use | Limited on-premise solutions |
Pricing
- Custom plans: Contact for quote
- Free trial: 30 days
- Free demo: Contact to schedule
Key Features
- Contextual alerts: Provides alerts that give insight into threat scores, affected assets, and severity.
- AI-powered phishing detection: Detects and blocks patient-zero phishing pages using advanced AI-based detection.
- Browser isolation: Allows users to create a virtual air gap between users, the web, and SaaS to mitigate web-based attacks and prevent data loss.
- Segmentation: Connects users directly to private apps, services, and OT systems with user identity-based authentication and access policies.

Lacework
Best Cloud-Native App Protection Tool
Overall Rating: 3.9/5
- Cloud-Specific Services: 4.7/5
- Hybrid Environment Services: 5/5
- Pricing: 1.6/5
- Customer Support: 4.4/5
- Third-Party Integration: 4.5/5
- Compliance & Insurance: 2.8/5
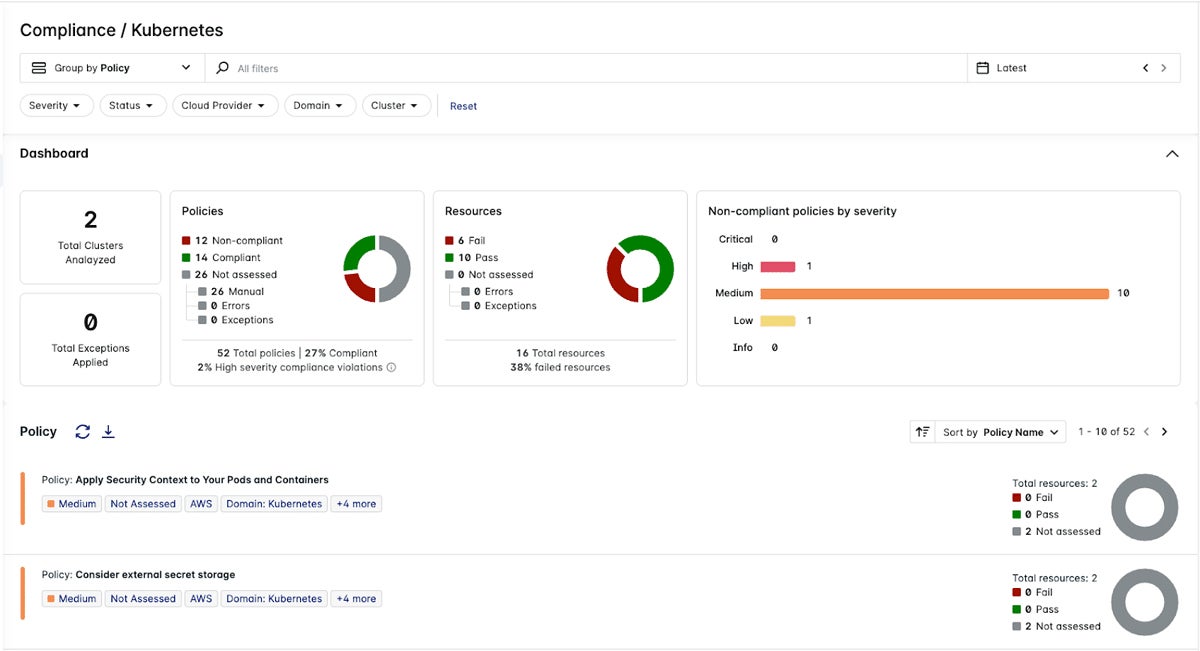
Lacework is a cloud-native application protection platform for modern IT environments. The Lacework Platform uses cloud security posture management (CSPM), infrastructure as code (IaC) scanning, cloud workload protection platform (CWPP), and Kubernetes security to help organizations protect their environment. It also provides cloud incident and event monitoring (CIEM) to quickly detect and respond to threats.
While Lacework adheres to ISO 27001, SOC 2, NIST, and GDPR standards, Qualys takes the lead in comprehensive IT regulatory compliance.
Pros & Cons
| Pros | Cons |
|---|---|
| Easy to use | No pricing information |
| Visually appealing dashboard | Reporting capabilities could be improved |
| Includes container image scanning | Alerts lack data for identifying malicious activity |
Pricing
- Custom plans: Contact for quote
- Free trial: 14 days
- Free demo: Contact to schedule
Key Features
- Contextual analysis: Offers the Polygraph feature for a visual representation of relationships across account roles, workloads, and APIs to deliver better context.
- Configuration assistance: Features configuration best practices support and guidance.
- Threat detection: Uses machine learning and analytics to detect threats in cloud-native environments.
- Vulnerability management: Utilizes risk-based prioritization to help you identify, prioritize, and remediate known vulnerabilities in your environment.
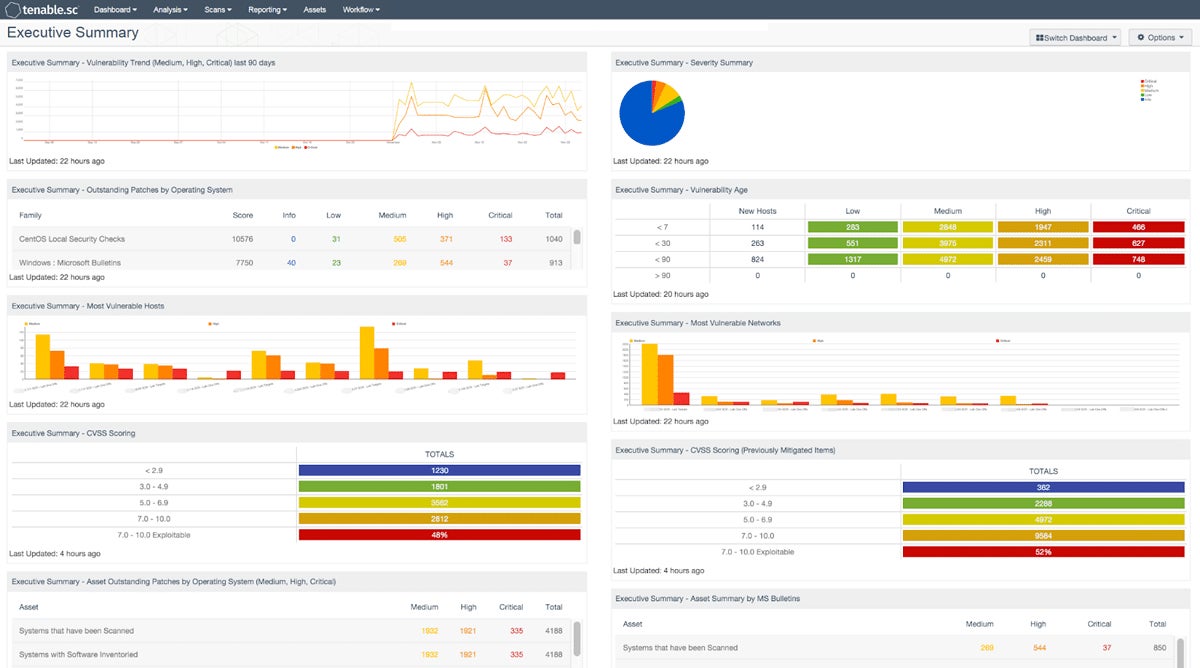
Tenable
Best for Secure Cybersecurity Insurance
Overall Rating: 3.9/5
- Cloud-Specific Services: 4.4/5
- Hybrid Environment Services: 4.3/5
- Pricing: 3.9/5
- Customer Support: 3.2/5
- Third-Party Integration: 4.4/5
- Compliance & Insurance: 3/5
Tenable provides cybersecurity software and services that help organizations better understand and reduce cyber exposure. It has a long history in the vulnerability management space, which now extends into the cloud to help organizations of all sizes protect their workloads. Tenable Portfolio provides transparent cyber insurance information and simplifies policy purchasing by improving the insurance companies’ review process.
Although Tenable offers solid vulnerability management, you might want to consider Zscaler’s more advanced threat protection.
Pros & Cons
| Pros | Cons |
|---|---|
| Easy to deploy | Reporting and insurance info could be improved |
| Clear and easy-to-navigate dashboard | Customer support could be better |
| Transparent pricing information | Asset management needs improvement |
Pricing
- Free plan: Nessus Essentials (formerly Nessus Home)
- Tenable.io Vulnerability Management: $2,934.75+ per year for 65 assets
- Tenable.io Web App Scanning: $3,846.35+ per year for 5 FQDNs
- Custom plans: Contact for quote
- Free trial: 7 days
- Free demo: Contact to schedule
Key Features
- Cloud protection: Has multiple services on its cloud-based tenable.io platform, including web application scanning, container security, and asset management.
- Vulnerability management: Identifies assets and vulnerabilities, giving organizations visibility into their cloud risk.
- Configuration management: Discovers potential misconfigurations.
- Broad coverage: Has assessed over 72K vulnerabilities with over 147K plugins.
Top 5 Cloud Security Companies Features
A reliable cloud security company provides comprehensive cloud platforms, multi-cloud security, unified platform monitoring, cyber insurance, and a zero-trust security model. Assess potential vendors based on their platform capabilities. Ensure that they meet your company’s needs for cyberthreat protection, continuous monitoring, and financial coverage.
Cloud Platforms
Cloud security companies offer a broad range of services, including cloud network security, CASB, CSPM, CWPP, CNAPP, and CIEM. They also provide encryption, threat intelligence, and serverless security. They seek to protect cloud-based assets, detect and mitigate risks, and assure compliance with security requirements in cloud settings.
Multi-Cloud Security
Multi-cloud security involves applying consistent security standards across many cloud platforms, integrating with native security services, and centralizing security administration. It provides consistent protection, addresses interoperability issues, and improves visibility and control across several cloud settings.
Unified Platform Monitoring
This combines security monitoring from multiple environments, analyzes security data in real time, and enables proactive threat hunting. It offers full visibility, simplifies incident detection and response, and streamlines security operations across cloud and on-premises infrastructure.
Cyber Insurance
A cyber insurance policy provides buyers with financial reimbursement for data breach expenses, business losses coverage, and access to cybersecurity specialists. It reduces the financial risks associated with cyber assaults, promotes cybersecurity best practices, and helps firms efficiently manage and recover from security disasters.
Zero Trust
Zero Trust includes thorough user and device authentication, ongoing monitoring of user activity, and cloud workload separation. It has a “never trust, always verify” security strategy to prevent unwanted access and mitigate the effects of security breaches.
How We Evaluated the Best Cloud Security Companies
We assessed a range of cloud security companies using a scoring rubric, creating six criteria with a list of subcriteria under them. Each subcriterion’s weight contributed to the overall product score. Based on the subcriteria ratings, the products obtained a five-point overall score. Our selection included the six highest-scoring cloud security companies, and the scores helped us determine the products’ use cases.
Evaluation Criteria
In evaluating the top cloud security companies, we created six distinct categories. These include cloud-specific services, hybrid environment services, pricing information, customer support, third-party integration, and compliance and insurance.
- Cloud-Specific Services (20%): We looked into the solutions and products offered by the company, such as cloud network security and CNAPP. We also included serverless security, encryption, zero trust, threat intelligence, multi-cloud security, and XDR security capabilities.
- Criterion Winner: Trend Micro
- Hybrid Environment Services (20%): We examined solutions for a hybrid environment, such as vulnerability management, web or cloud application security, unified platform monitoring, and incident and event management capabilities.
- Criterion Winner: Multiple winners
- Pricing (20%): In our pricing evaluations, we considered factors like free trial availability, pricing accessibility and transparency, flexibility in pricing models, and the availability of free plans and products.
- Criterion Winner: Trend Micro
- Customer Support (15%): We assessed the accessibility and effectiveness of customer service channels such as live chat and email, plus the quality of documentation, demos, and training materials. Additionally, we considered user reviews from platforms like G2 and Capterra.
- Criterion Winner: Lacework
- Third-Party Integration (15%): This included integration with DevOps toolchains (e.g., Azure DevOps, Jenkins), APIs, and cloud services. We also assessed integration with identity and access control systems, as well as collaboration and communication tools.
- Criterion Winner: Multiple winners
- Compliance & Insurance (15%): We considered adherence to standards like ISO/IEC 27001, SOC 2, PCI DSS, HIPAA, NIST, FedRAMP, and GDPR. We also looked into the cybersecurity insurance coverage information provided by each vendor.
- Criterion Winner: Multiple winners
Frequently Asked Questions
What Are the Different Cloud Security Technologies?
CASB, CWPP, CNAPP, and SaaS security are different solution categories offered by cloud security companies to help organizations reduce risk and improve security.
- Cloud access security brokers (CASB): This tool monitors activity and enforces cloud access security policies.
- Cloud workload protection platform (CWPP): Works with both cloud infrastructure and virtual machines, providing monitoring and threat prevention features.
- Cloud-native application protection platform (CNAPP): Combines cloud security posture management (CSPM) and CWPP in a single, unified solution to provide visibility and security control management across all cloud functions.
- SaaS security: Multiple types of security technologies are also delivered as a service from the cloud to help secure both on-premises and cloud workloads.
It’s also important to note that each of the major public cloud providers (Amazon Web Services, Google Cloud Platform, and Microsoft Azure) also has their own native cloud security controls and services that organizations can enable. Understand the shared responsibility model of these cloud security platforms to properly implement your security obligations.
How Do You Choose a Cloud Security Product?
When selecting a cloud security solution, several key considerations include scope, policy integration, and multi-cloud protection.
- Scope: Understand what’s at risk and what the organization is trying to protect. Often one or more services will be needed to protect an entire cloud deployment.
- Policy integration: Make sure that a given cloud security solution can integrate with existing policy systems, whether they are on-premises or in the cloud, to enable a uniform policy for an enterprise.
- Multi-cloud protection: Consider the ability to work across multiple cloud providers and different types of deployments.
When Do You Need a Cloud Security Product?
Cloud security solutions help protect sensitive data, ensure compliance, defend against cyberthreats, and manage access controls across cloud environments. It becomes essential as businesses rely more on cloud services for storage, apps, and infrastructure, which requires strong security measures to successfully mitigate risks.
Bottom Line: Choose the Right Cloud Security Company
As companies increasingly store and process critical data and assets in the cloud, it’s important that they have the right cloud security tools to secure those assets. Cloud security companies give businesses the security solutions to meet those needs, ranging from risk assessment, auditing, data encryption, user authentication, access control, and more. Explore the free demos and trial offerings so you’ll have an idea of how to best secure your cloud systems and data.
Discover the key distinctions among some of the popular cloud security solutions such as CSPM, CWPP, CIEM, and CNAPP.
Aminu Abdullahi contributed to this article.










