Cisco is warning that nine significant vulnerabilities in its Small Business Series Switches could enable unauthenticated remote attackers to cause a denial-of-service condition or execute arbitrary code with root privileges on affected devices.
The vulnerabilities are caused by improper validation of requests sent to the switches’ web interfaces, the company said.
While the Cisco Product Security Incident Response Team (PSIRT) says it’s not aware of any malicious use of these flaws, it says proof-of-concept exploit code is available online.
Vulnerable products include 250 Series Smart Switches, 350 Series Managed Switches, 350X Series Stackable Managed Switches, 550X Series Stackable Managed Switches, Business 250 Series Smart Switches, Business 350 Series Managed Switches, Small Business 200 Series Smart Switches, Small Business 300 Series Managed Switches, and Small Business 500 Series Stackable Managed Switches.
Despite the severity of the flaws, Cisco says the last three products in the list above won’t be covered by software updates or by workarounds because they’ve entered the end-of-life process. “Cisco has not and will not release firmware updates to address the vulnerabilities described in the advisory for these devices,” the company stated.
Nine Independent Vulnerabilities
The flaws are not dependent on one another. “Exploitation of one of the vulnerabilities is not required to exploit another vulnerability,” the company explained. “In addition, a software release that is affected by one of the vulnerabilities may not be affected by the other vulnerabilities.”
The flaws, according to Cisco, include the following:
- CVE-2023-20159, CVE-2023-20160, CVE-2023-20161, and CVE-2023-20189 – four vulnerabilities with a critical CVSS score of 9.8 that could enable an unauthenticated remote attacker to execute arbitrary code with root privileges.
- CVE-2023-20024, CVE-2023-20156, CVE-2023-20157, and CVE-2023-20158 – four vulnerabilities with a high CVSS score of 8.6 that could enable an unauthenticated remote attacker to cause a denial-of-service condition.
- CVE-2023-20162 – one vulnerability with a high CVSS score of 7.5 that could enable an unauthenticated remote attacker to access unauthorized information.
Also read:
APT Group Targeting TP-Link Routers
Separately, the Check Point Research Threat Intelligence Team recently uncovered a malicious firmware implant for TP-Link routers that provides attackers with full control of infected devices.
The researchers say the implant’s firmware-agnostic design could allow it to be integrated into other brands of routers as well. “While we have no concrete evidence of this, previous incidents have demonstrated that similar implants and backdoors have been deployed on diverse routers and devices from a range of vendors,” the researchers noted.
Check Point attributes the custom MIPS32 ELF implant, named Horse Shell, to a Chinese state-sponsored advanced persistent threat (APT) group they’re calling Camaro Dragon.
The discovery was made while investigating a series of targeted cyber attacks against European foreign affairs entities, though the researchers noted that router implants are often installed arbitrarily in order to create a chain of infected nodes.
“We are unsure how the attackers managed to infect the router devices with their malicious implant,” the researchers wrote. “It is likely that they gained access to these devices by either scanning them for known vulnerabilities or targeting devices that used default or weak and easily guessable passwords for authentication.”
Ransomware Vulnerabilities Not Always Detected
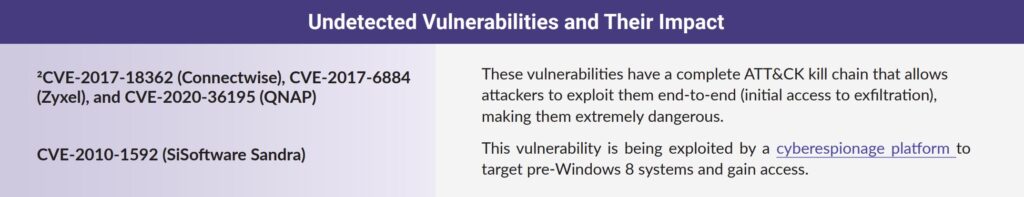
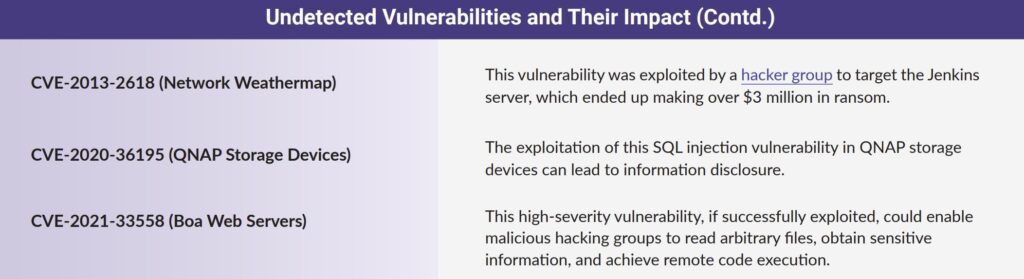
In other vulnerability news, researchers from Securin, Ivanti and Cyware said that vulnerability scanning solutions from Tenable, Nexpose and Qualys are not detecting 18 high-risk vulnerabilities exploited by ransomware groups (see images below).
They also noted that while the U.S. Cybersecurity and Infrastructure Security Agency (CISA) has prioritized 63% of vulnerabilities that are exploited by ransomware gangs in its Known Exploited Vulnerabilities (KEV) catalog, “there are still 131 vulnerabilities that are being exploited by ransomware that need to be included in the KEV catalog.”
Also read: How to Recover From a Ransomware Attack