Single sign-on solutions are security software products that typically fall under the identity and access management (IAM) umbrella. SSO products help teams manage user identities, both employees and customers, and grant and limit their access to company applications. They play a critical role in protecting sensitive data and applications because SSO reduces password sprawl and limits the time window in which a threat actor could hack an application.
Here are our top six selections for the best SSO solutions:
- Okta: Best overall SSO solution for a mix of pricing and features
- OneLogin: Best solution for sandboxing and DevSecOps teams
- Microsoft Entra ID: Best SSO option for Windows environments
- JumpCloud: Best product for Linux users and multi-platform teams
- Ping Identity: Best for a mix of identity orchestration and access policies
- CyberArk: Best SSO solution for native user behavior analytics
Top Single Sign-On Solutions Compared
Below, we’ve given an overview of our top six picks and a few of their features, like privileged access management and templates for identity workflows, as well as pricing.
| Active Directory Integration | Privilege Access Management | Workflow Templates | 30-Day Free Trial | |
|---|---|---|---|---|
| Okta | ✔️ | ✔️ | ✔️ | ✔️ |
| OneLogin | ✔️ | ✔️ | ✔️ | ✔️ |
| Microsoft Entra ID | ✔️ | ✔️ | ✔️ | ✔️ |
| JumpCloud | ✔️ | ✔️ | ❌ | ✔️ |
| Ping Identity | ✔️ | ❌ | ✔️ | ✔️ |
| CyberArk | ✔️ | ✔️ | ✔️ | ✔️ |
Table of Contents
Featured Partners: Password Management Software

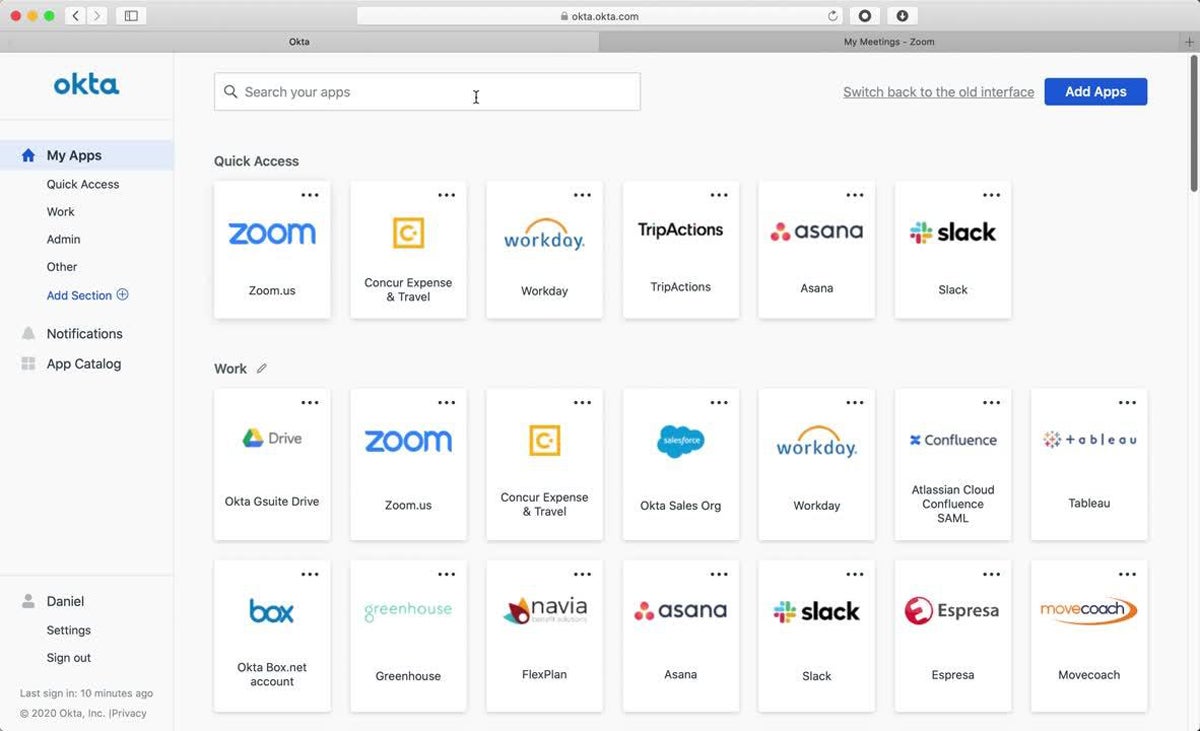
Okta
Best Overall SSO Solution for Pricing & Features
Overall Rating: 4.6/5
- Core features: 4.8/5
- Integrations: 5/5
- Advanced features: 5/5
- Usability and administration: 3.3/5
- Pricing: 5/5
- Customer support: 4.4/5
Okta is a well-established IAM and SSO provider offering a slew of identity management features, including temporary access and device assurance policies. Consider Okta if your business uses a lot of applications; because Okta offers thousands of prebuilt app connectors, it’s one of the best SSO solutions for protecting large software ecosystems. Okta also has a transparent pricing structure, allowing teams to pick and choose the features they need.
Okta is a fantastic IAM and single sign-on product for many businesses, but it may be too expensive for very small businesses. Consider OneLogin if you’re looking for a less expensive bundled feature set.
Pros & Cons
| Pros | Cons |
|---|---|
| Huge selection of IAM features | Lacks email support |
| Developer platform available | Doesn’t support Linux devices |
| Connects with over 7,000 applications | Prices for multiple features can quickly add up |
Pricing
- SSO: $2 per user per month
- MFA: $3 per user per month
- Lifecycle Management: $4 per user per month
- Workflows: $4+ per user per month up to 50 flows
- Annual contract minimum: $1,500
- Free trial: 30 days
Key Features
- Identity governance: Admins can approve users’ application access requests and view compliance-minded reports.
- Privileged access: Develop custom approval processes and integrate with Okta’s Access Request features.
- Device assurance policies: Create and manage policies to allow or deny specific devices based on criteria like applied patches.
- No-code custom branding: Customize your login pages so they fit your organization’s overall brand.

OneLogin
Best Solution for Sandboxing & DevSecOps Teams
Overall Rating: 4.5/5
- Core features: 5/5
- Integrations: 4.8/5
- Advanced features: 2.9/5
- Usability and administration: 4.5/5
- Pricing: 5/5
- Customer support: 4.4/5
OneLogin is an enterprise-grade IAM platform for both workforces and customers, offering MFA, advanced directory features, and mobile identity management. OneLogin is particularly suited to developer teams, with a command line tool, an API, and sandboxing that allow teams to test identity processes while they’re still in development. Consider OneLogin for your DevSecOps teams if they want to closely configure your company’s IAM processes.
OneLogin doesn’t have some features like temporary access and drag-and-drop workflows, so if your team needs those features, consider Okta instead. Like OneLogin, it also offers a developer program and sandboxing.
Pros & Cons
| Pros | Cons |
|---|---|
| Developer platform available | Lacks temporary access features |
| Wide range of core features | Lacks drag-and-drop workflows |
| Available as a managed service | Doesn’t support Linux devices |
Pricing
- Advanced plan: $4+ per user per month when bundled
- Professional plan: $8+ per user per month when bundled
- SMB pricing: Specialized pricing options available for businesses under 50 employees
- Free trial: 30 days
Key Features
- Sandboxing: Teams can test their IAM configurations before pushing final changes to end users.
- OneLogin Access: Sync access to your cloud and on-premises apps using OneLogin’s unified access management product.
- Onboarding and offboarding: Manage your user identity lifecycles, including deactivating their access to company apps.
- Smart Hooks: This product allows teams to customize their own identity workflows with serverless code.

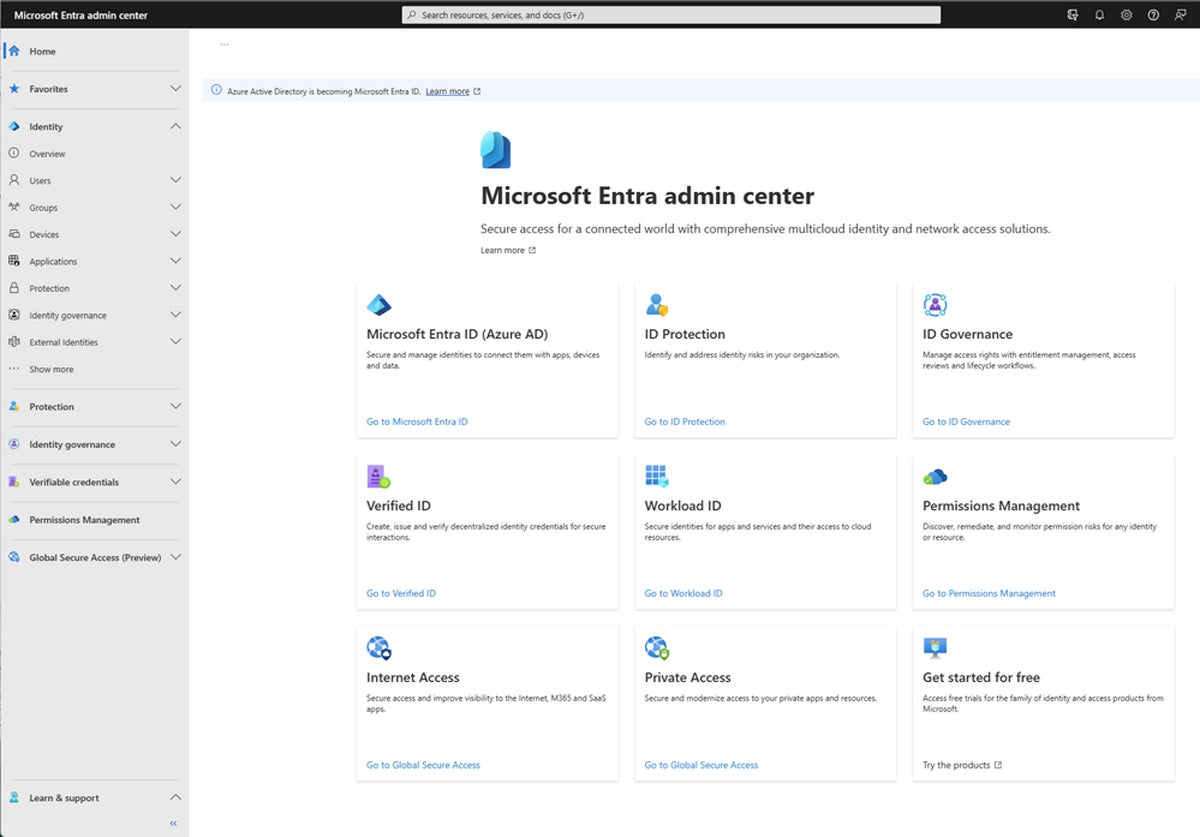
Microsoft Entra ID
Best SSO Option for Windows Environments
Overall Rating: 4.3/5
- Core features: 4.8/5
- Integrations: 4.7/5
- Advanced features: 4.3/5
- Usability and administration: 4.4/5
- Pricing: 5/5
- Customer support: 1.6/5
Microsoft Entra ID is an identity governance and management platform that’s particularly suited to existing Windows organizations. It natively integrates with other Microsoft products like Sentinel and Defender for Cloud, sharing information between the products so customers can sync their security data and reduce excessive cloud permissions. Key features to highlight include passwordless authentication, lifecycle management, and custom session length.
Microsoft isn’t as transparent about its customer support availability as some of the other vendors on this list. If you’re looking for multiple support channels, consider CyberArk — it also has drag-and-drop identity workflow options, like Entra ID.
Pros & Cons
| Pros | Cons |
|---|---|
| Plenty of core and advanced IAM features | Doesn’t support Linux devices |
| Available as a cloud-based service | Limited drag-and-drop workflow functionality |
| Support for both cloud and on-premises apps | Support team availability is unclear |
Pricing
- Free plan: Offers some partial IAM features
- Entra ID P1: $6 per user per month
- Entra ID P2: $9 per user per month
- Free trial: 30 days
Key Features
- Passwordless authentication: Use texts, keys, or biometrics to log into your business applications.
- Conditional access: Factors like location and session risk help Entra ID decide whether to allow application access.
- Privileged identity management: Limit application usage with just-in-time access and just enough access.
- User management: All employees have an interface that allows them to manage their own accounts, applications, and groups.

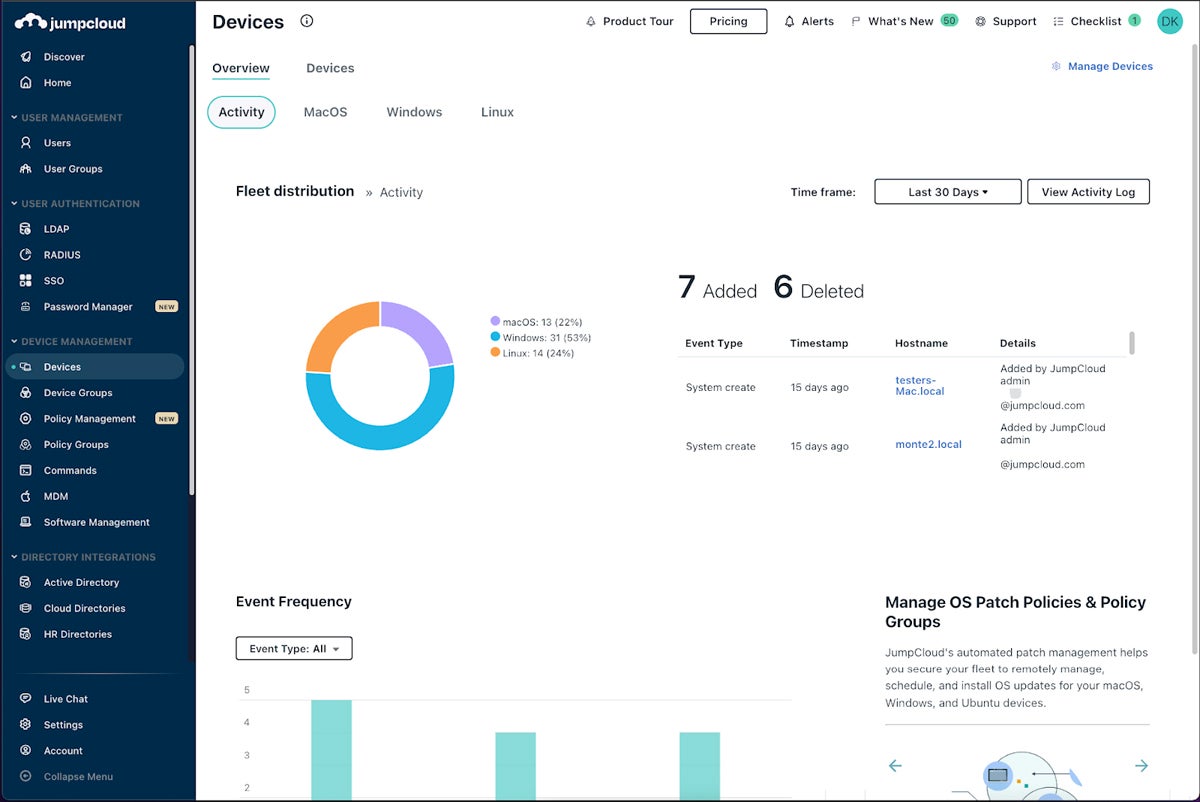
JumpCloud
Best Product for Linux Users & Multi-Platform Teams
Overall Rating: 4.2/5
- Core features: 4.3/5
- Integrations: 4.3/5
- Advanced features: 3.5/5
- Usability and administration: 3.3/5
- Pricing: 5/5
- Customer support: 4.9/5
JumpCloud is an SSO vendor with plenty of core identity and access management features and multiple customer support channels, including phone and email. As the only vendor on our list that supports Linux devices, it’s ideal for businesses that use all three major operating systems — JumpCloud can be installed on macOS and Windows too. JumpCloud also supports multiple mobile devices; consider it for teams that rely heavily on mobile and are frequently on the go.
JumpCloud doesn’t offer drag-and-drop workflows, so if that’s important to your security team, consider CyberArk — it also offers mobile device management features. But keep in mind that none of the other options on our list support Linux devices.
Pros & Cons
| Pros | Cons |
|---|---|
| Supports all three major operating systems | Lacks drag-and-drop workflow functionality |
| Mobile device management available for BYOD | Unclear whether it’s available as a service |
| Multiple support channels available | Integration catalog can be hard to search |
Pricing
- SSO: $11 per user per month, billed annually
- Core Directory: $13 per user per month, billed annually
- Platform: $19 per user per month, billed annually
- Platform Prime: $24 per user per month, billed annually
- Free trial: 30 days
Key Features
- Patch management: Teams can automate patching procedures for Windows, macOS, Ubuntu Linux, and web browsers.
- HRIS integrations: JumpCloud offers multiple HR software connectors, including Paylocity and BambooHR.
- Lifecycle management: Perform employee onboarding and onboarding and manage all remote users.
- Custom session length: Change your organization’s user session length based on your security requirements.

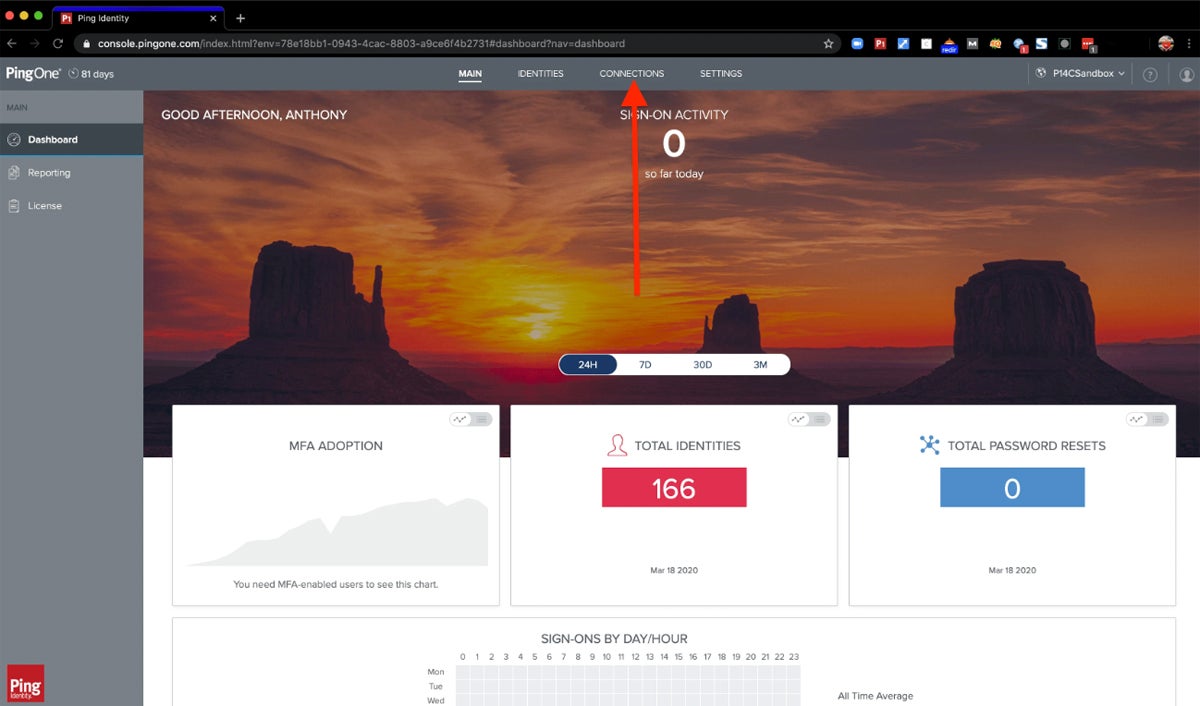
Ping Identity
Best for a Mix of Identity Orchestration & Access Policies
Overall Rating: 4.1/5
- Core features: 4.8/5
- Integrations: 4.3/5
- Advanced features: 3.3/5
- Usability and administration: 3.7/5
- Pricing: 3.8/5
- Customer support: 4.4/5
Ping Identity is an identity orchestration, SSO, and access management product for businesses of all sizes. Its key features include drag-and-drop identity management workflows, passwordless authentication, and customizable branding. Consider Ping if you want to deeply customize your business’s identity processes — its drag-and-drop configurations give both experienced and junior employees plenty of room to tailor workflows based on company needs.
Ping is a great choice for easy-to-use identity workflows, but it lacks privileged access management features. Consider CyberArk if your business needs both identity orchestration and privilege access management capabilities.
Pros & Cons
| Pros | Cons |
|---|---|
| Strong identity orchestration capabilities | Lacks privilege access management |
| Supports both cloud and on-premises apps | No temporary SSO access |
| 24/7 support for severe cases and outages | Doesn’t support Linux devices |
Pricing
- Essential: $20,000+ per year
- Plus: $40,000+ per year
- Premium: Custom pricing
- Free trial: 30 days
Key Features
- Identity orchestration: Use drag-and-drop to create identity workflows customized to your business’s needs.
- Passwordless sign-on: Businesses can use other authentication methods, like biometrics, to reduce password risks.
- Custom branding: Use Ping’s branding options to customize your team’s registration and verification pages.
- Conditional access: Through an integration with Azure Active Directory, grant conditional access to users.

CyberArk
Best SSO Solution for Native User Behavioral Analytics
Overall Rating: 3.8/5
- Core features: 4.2/5
- Integrations: 4.3/5
- Advanced features: 4.8/5
- Usability and administration: 2.6/5
- Pricing: 2/5
- Customer support: 4.9/5
CyberArk is an identity and SSO provider that offers no-code, drag-and-drop identity workflows for teams of any experience level. It’s a strong choice for businesses looking for a clear identity visualization product. Another area where CyberArk really shines is in its behavioral analytics product: It offers detailed reports for compliance and AI-based log assessments, and it’s a useful resource for security teams that want to perform advanced analytics.
While CyberArk has fantastic identity orchestration features, it lacks transparent pricing, so if you’re looking for a platform with analytics and more transparent pricing, consider Okta. It offers orchestration, security analytics, and detailed pricing information.
Pros & Cons
| Pros | Cons |
|---|---|
| Detailed behavioral analytics | Lacks transparent pricing |
| Extensive identity orchestration capabilities | Limited conditional access functionality |
| Multiple customer support channels | CyberArk’s encryption procedures are unclear |
Pricing
- Contact for quote: Custom pricing available
- Free trial: 30 days
Key Features
- Privilege access management: Manage policies that enforce security for all your privilege access accounts.
- Custom user sessions: Admins can adjust the length of an SSO session for increased or decreased security.
- Custom branding: CyberArk has multiple customization options, including background images and colors.
- User provisioning: Automated lifecycle management features include provisioning accounts and flagging unmanaged accounts.

Top 5 Features of Single Sign-On Solutions
SSO solutions often fall under identity and access management platforms, like many of the options in this guide, and have many similar feature sets. When shopping for SSO or IAM tools, look for capabilities like prebuilt integrations, user provisioning, branding and workflow customization, and usage reports.
Integrations
One of the top benefits of SSO products is their integration with a variety of business software, including CRM and sales platforms, project management tools, HR apps, and other cybersecurity products. The more apps an SSO solution supports, the better, and teams should look for SSO tools that support the majority or all of their business apps, whether through pre-built integrations or APIs. Broad app coverage helps protect the wider business network.
User Provisioning
User provisioning processes help teams more easily onboard new employees or third parties into an SSO product. In some larger IAM products, like many on this list, user provisioning falls under identity lifecycle management. Lifecycle management oversees the entire user identity process, from initial account activation to deprovisioning when the employee leaves the company.
Custom Branding
Ideally, single sign-on solutions should have custom branding options so businesses can add their own logos and styles to the main SSO page. This is particularly helpful for managed service providers or organizations offering SSO to their customers — their login pages will be specific to their business and look more professional.
Easy-to-Use Identity Workflows
SSO products should also have customizable workflows so security and IT teams can design identity lifecycles that work best for their business. Workflows are simply the recipes that designate how an IAM process works — for example, only allowing an admin to log into an IT management application during certain hours. One common usability feature is drag-and-drop functionality, so teams without coding experience can still design workflows.
Reporting
SSO products should offer usage reports so IT and security leaders can monitor overall identity and access trends, as well as any concerning anomalies. Reports can include factors like number of logins in a given period of time, average session length, or current credential status. Reporting is also important for presenting clear, straightforward information to business leaders who don’t know as much about cybersecurity patterns.
How We Evaluated the Best Single Sign-On Solutions
To select the best SSO solutions, we created a product rubric that analyzed software using six major categories. Each category had a specific weight and included subcriteria with their own weighting. Each SSO product’s total score was determined by how many subcriteria it met. The six products that scored highest on our rubric made the final list. The final scores and our broader product research helped us determine the use cases for our top options.
Evaluation Criteria
In our main six categories, we first evaluated core features, such as MFA, workflows, and mobile functionality. Then we looked at integrations, including prebuilt CRM, service desk, and cybersecurity connectors, and advanced features like temporary access. Usability and administration included criteria like documentation and vendor encryption. Lastly, we looked at availability of pricing plans and customer support channels.
- Core features (25%): We evaluated key features like MFA, workflow templates, and user provisioning.
- Criterion winner: OneLogin
- Integrations (20%): We rated products based on number of integrations, specific connector options, and Active Directory integrations.
- Criterion winner: Okta
- Advanced features (15%): Our selections for advanced features included passwordless authentication and temporary SSO access.
- Criterion winner: Okta
- Usability and administration (15%): We scored products based on functionality like support for mobile devices and different operating systems.
- Criterion winner: OneLogin
- Pricing (15%): We looked at pricing plan availability and transparency, billing options, and free product trials.
- Criterion winner: Multiple winners
- Customer support (10%): We considered factors like phone and email support and demo availability.
- Criterion winner: Multiple winners
Frequently Asked Questions (FAQs)
How Does SSO Work?
Single sign-on solutions use authentication tokens to verify a valid user session. If a user registers with an SSO or IAM solution, any application connected to the SSO product will recognize the user’s token. If the user has already logged in and their session is still active, the requested application will clear their authentication token and they can enter. If they haven’t logged in or their session is no longer active, the browser will prompt them to log in again.
Why Is SSO Needed?
SSO reduces the number of account passwords that business owners need to remember and allows them to easily log into multiple applications for only a set amount of time. Short session lengths reduce the opportunity for an attacker to hack a user account and do significant damage.
Other features adjacent to SSO, like identity lifecycle management and privilege access management, help businesses closely manage their users’ accounts and permissions. This reduces opportunities for threat actors, whether internal or external, to take advantage of sensitive applications they shouldn’t be accessing. It also increases business visibility of the ways and times users are accessing apps so they can more easily detect anomalies.
Is SSO a Security Risk?
Overall, SSO is designed to improve business security by streamlining application passwords and requiring knowledge that only the user should have or know. But in rare cases, if a threat actor breaches an SSO account, they’ll have access to all the user’s connected applications, not just one or two. SSO does pose risks, as any software solutions do, but its benefits outweigh potential security drawbacks. Just make sure you pair SSO with other security measures.
Bottom Line: SSO Is One Part of a Strong IAM Strategy
Single sign-on and other products within the broader IAM category help businesses manage large numbers of users and their ability to access applications and data. The more employees and applications you have, the more critical SSO is. While it’s a useful tool for reducing password sprawl and security issues, it’s most beneficial when used with a range of IAM features, like privileged access and identity lifecycle management.
Next, check out our buyer’s guide for identity and access management tools to learn more about IAM.
Drew Robb contributed to this article.








