-

8 Best Business Continuity Software Solutions
Even a single hour of downtime can cost businesses over $1 million, and costs can quickly add up, considering the average downtime for ransomware attacks is 22 days. Unfortunately, many organizations don’t have business continuity solutions in place to help them avoid major spurts of downtime. Business continuity software can point out vulnerabilities in a […]
-

Complete Guide to Phishing Attacks: What Are the Different Types and Defenses?
As web security improves, email security has become a bigger problem than ever. The overwhelming majority of malware attacks now come from email — as high as 89 percent, according to HP Wolf Security research. And with many employees getting multiple emails per day, it’s easy for spam emails to slip their notice and potentially […]
-

How to Protect Company Data & Assets When Employees Leave
The Great Resignation has left many companies reeling, experiencing a higher turnover rate than ever before. And while this is causing major problems for HR, it could also lead to underlying security issues. Employees carry with them a lot of knowledge about how to access company systems, and that knowledge doesn’t just go away when […]
-

Best Internet Security Software & Suites
Malware is one of the biggest threats businesses face, and with nearly a third of all malware coming through the internet and email, businesses and consumers alike need ways to protect themselves. The best internet security software comes in several different forms, giving businesses all of the protection they need to identify and stop malware […]
-

WireGuard vs. OpenVPN: Comparing Top VPN Protocols
Virtual Private Networks (VPNs) provide secure access to business files for remote workers, making them a crucial part of an enterprise’s technology stack. But they need the right protocols to run properly. A VPN protocol creates the tunnels that your traffic travels through when you use a VPN to keep your communications private. WireGuard and […]
-

Cybersecurity Employment: Solving the Skills Gap
As we enter 2022, the shortage of cybersecurity pros hasn’t gotten better. In fact, it’s gotten worse. There are currently about 435,000 cybersecurity job openings available in the United States, up from approximately 314,000 in 2019. The move to remote work in response to the COVID-19 pandemic increased the workloads for skilled IT professionals, and […]
-

How to Comply with GDPR, PIPL and CCPA
Compliance issues can be tricky, especially when there are so many data privacy laws. Find out how to comply with GDPR, PIPL, and CCPA.
-

Twitch Breach Shows the Difficulty of Cloud Security
Cloud security is a delicate balancing act of keeping the freedoms that make migration worthwhile while also keeping a company’s data secure. A recent breach of Twitch, an Amazon-owned company, showed businesses just how difficult cloud security really is. And it’s critically important, with the average cost of a data breach in hybrid cloud environments […]
-

Application Security is Key to Stopping Ransomware, Vendor Says
Recent news headlines have shown how vulnerable even large companies with many resources at their disposal are to ransomware. While these attacks may feel inevitable, there are measures that businesses can take to protect themselves. One vendor says application security may be the key to stopping ransomware. Preventing Ransomware with Application Security How ransomware accesses […]
-
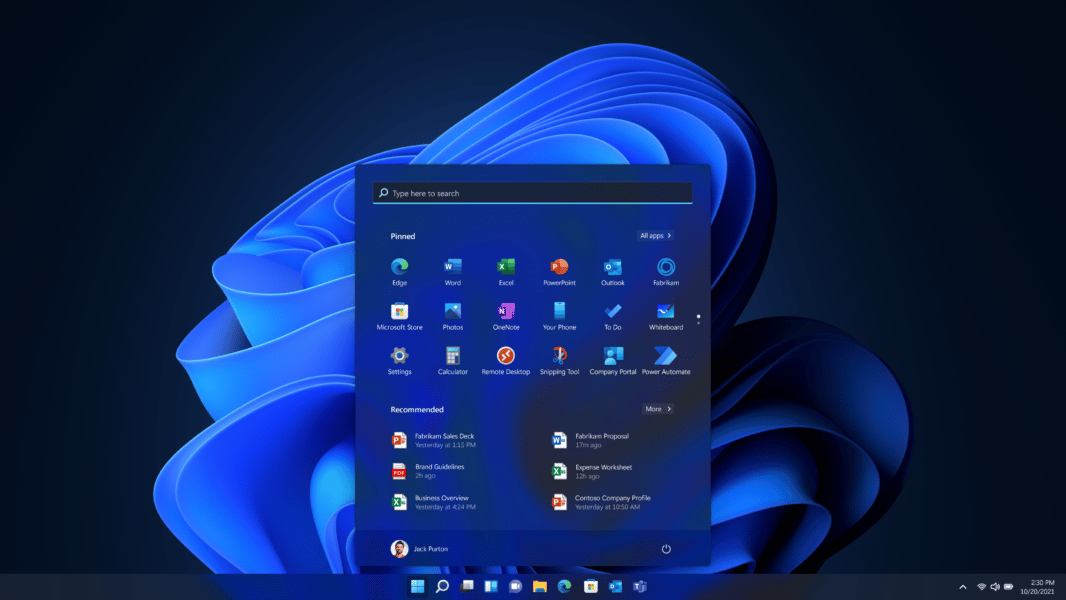
Windows 11 Security Features & Requirements
Windows 11 started rolling out on October 5 for personal devices, but most businesses are unlikely to get access to the upgrade until the middle of 2022. Regardless of when you get Windows 11, you’ll need to know what security features are included and available, so you can effectively implement it across your organization. The […]
IT Security Resources
Top Cybersecurity Companies
Top 10 Cybersecurity Companies
Get the Free Newsletter!
Subscribe to Cybersecurity Insider for top news, trends & analysis





