See our complete list of top next-generation firewall vendors.
Bottom Line
Cisco’s biggest strength might be the breadth of security services it offers or integrates with its firewall, among them intrusion prevention, advanced malware protection, cloud-based sandboxing, URL filtering, endpoint protection, web gateway, email security, network traffic analysis, network access control and CASB. However, that broad protection comes with above average prices.
Company Description
Based in San Jose, California, Cisco is the world’s largest networking infrastructure vendor. It also has a broad security, server and storage portfolio.
Product Description
Gartner placed Cisco in its Challengers quadrant. Its main product line is Cisco Firepower NGFW, which exists alongside its older Adaptive Security Appliance (ASA) product line, as well as its Meraki range for SMBs. In addition, the company offers two virtual firewalls (ASAv and NGFWv). Features include URL filtering, cloud-based sandboxing and malware protection, as well as integration with endpoint security, network traffic analysis, web gateway, email security, and network access control. It supports control of over 4,000 commercial applications with its Layer 7 application firewalling. Its OpenAppID tool enables development of custom application detectors.
Features
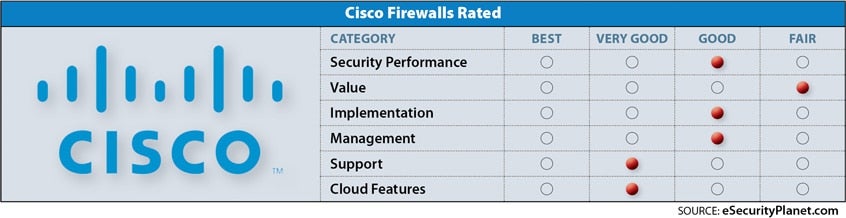
Security and performance: Good. NSS Labs gave the Firepower 4120 a 71.8% security effectiveness rating, behind the leaders but good enough for a Security Recommended rating, meaning the appliance offers good security at a higher price point. The device blocked 95.7% of attacks, but was ineffective against 3 of 190 evasion techniques. Performance was a solid 5,291 Mbps. Advanced threat protection across networks and endpoints is a strength.
Value: Fair. NSS Labs gave Cisco a pricier than average $28 TCO per protected Mbps, the second highest of solutions tested.
Implementation: Good. Some complexity, but users are generally happy once the system is up and running.
Management: Good, if complicated. As one user said, “Be prepared to spend time with the product in order to understand the processes and to truly get the features you desire functioning as desired.”
Support: Very good. An occasional complaint, but otherwise an area where Cisco shines.
Cloud features: Very good. Cisco’s virtual firewalls offer support for AWS, Azure and several virtual environments.
Security Qualifications
FIPS and HIPAA
Intelligence
IP, URL, and DNS threat intelligence
Delivery
Physical and virtual appliances, support for Amazon AWS and Microsoft Azure public clouds
Agents
Two endpoint agents are available:
- Cisco AMP for Endpoints (Cisco Firepower correlates endpoint and network threats)
- Cisco Umbrella, which enables both off-VPN DNS-based security plus the Cisco AnyConnect VPN client.
Pricing
Firewalls start at less than $1,000. Prices start as low as $35 per month with Cisco EasyPay leasing. The Firepower 4120 tested by NSS Labs sells for around $100,000.?







