TORONTO – The security business is full of different terms and methodologies for describing the threat model. In a presentation at the SecTor conference this week, Chris Pogue, director of Digital Forensics and Incident Responce at Trustwave, explained his firm’s simple four-step model for defining cybercrime.
“As difficult as people want to make cybercrime, there really are only really a few steps,” Pogue said. “The bad guy has to get in, the bad guy has to move around, the bad guy has to steal some stuff, and then the bad guy has to make a getaway.”
Trustwave calls this process flow “the Breach Quadrilateral.”
Infiltration is the point at which the attacker gets into an organization.
Propagation is where the bad guy pivots, as the initial point of entry isn’t always where they want to be.
Aggregation is when the attacker finds and collects all the data that is being sought.
Exfiltration is about getting out without being detected.
“That is cybercrime in a nutshell,” Pogue said. “It’s always the same.”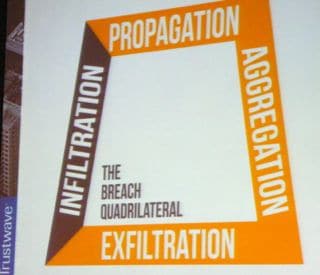
Pogue stressed that it’s important to understand the Breach Quadrilateral as the basis for security analysis and defense.
“We know what we’re fighting, this isn’t a surprise,” Pogue said.
He added that it doesn’t matter if an attack is malware or an application that is vulnerable because they all still plug into the Breach Quadrilateral.
“We know what the enemy is going to do, we just have to defend smartly,” Pogues said. “The bad guys are all playing by the same rules and we have the playbook.”
MLAT
Knowing what bad guys will do and then being able to engage with law enforcement are two different things.
In the case where attackers are coming from outside the U.S., there is something called the Mutual Legal Assistance Treaty (MLAT).
After a security professional has done an investigation and identified a threat actor, the information can be handed off to the proper authorities. In the U.S., for example, that could include the involvement of the U.S. Secret Service. The Secret Service in turn needs to go to the U.S. Attorney’s office to examine the case to see if an arrest warrant can be issued. If the threat actor is outside the U.S., the U.S. Attorney’s office passes a request to the State Department. The State Department can then issue an MLAT request to the country of origin for the threat actor.
Then the third party country needs to operate through their own legal system to allow a U.S. law enforcement official to come and make an arrest.
“It’s a very long process, so we have to hope that the bad guys don’t get tipped off,” Pogue said.
Sean Michael Kerner is a senior editor at eSecurity Planet and InternetNews.com. Follow him on Twitter @TechJournalist




