Database security solutions help protect sensitive business and customer information from external and internal users. They use customized security policies and rules, access controls, and data masking technologies to restrict data access to authorized users that absolutely need it. To help your business select a database security solution, I’ve evaluated multiple providers and their features and narrowed down the final list to the top products.
Here are the six best database security solutions for businesses:
- Oracle Data Safe: Best for Oracle Database environments
- IBM Guardium: Best enterprise-grade database security solution
- Satori Cyber: Best option for AI-focused data security
- DBHawk: Best managed database security platform
- Imperva Data Security: Best for a mix of support and pricing
- Thales CipherTrust: Best for encryption-specific needs
Featured PartnersFeatured Partners: Database Software
eSecurity Planet may receive a commission from merchants for referrals from this website
Top Database Security Software Comparison
The following table breaks down some differences between the top six products, including availability of certain features and a free trial.
| Data Logging | Data Masking | IAM Integrations | Encryption | 30-Day Free Trial | |
|---|---|---|---|---|---|
| Oracle | ✔️ | ✔️ | Native feature | ❌ | ✔️ |
| IBM | ✔️ | ✔️ | ✔️ | ✔️ | ✔️ |
| Satori | ✔️ | ✔️ | ✔️ | ❌ | ❌ |
| DBHawk | ✔️ | ✔️ | ✔️ | ❌ | ❌ |
| Imperva | ✔️ | ✔️ | ✔️ | ❌ | ✔️ |
| Thales | ✔️ | ✔️ | ❌ | ✔️ | ✔️ |
While different products on this list scored highly in different categories, Oracle Data Safe was the overall winner as our top database security solution. Continue reading to learn about each solution’s features, pros and cons, and pricing, or jump down to see how I evaluated these products.
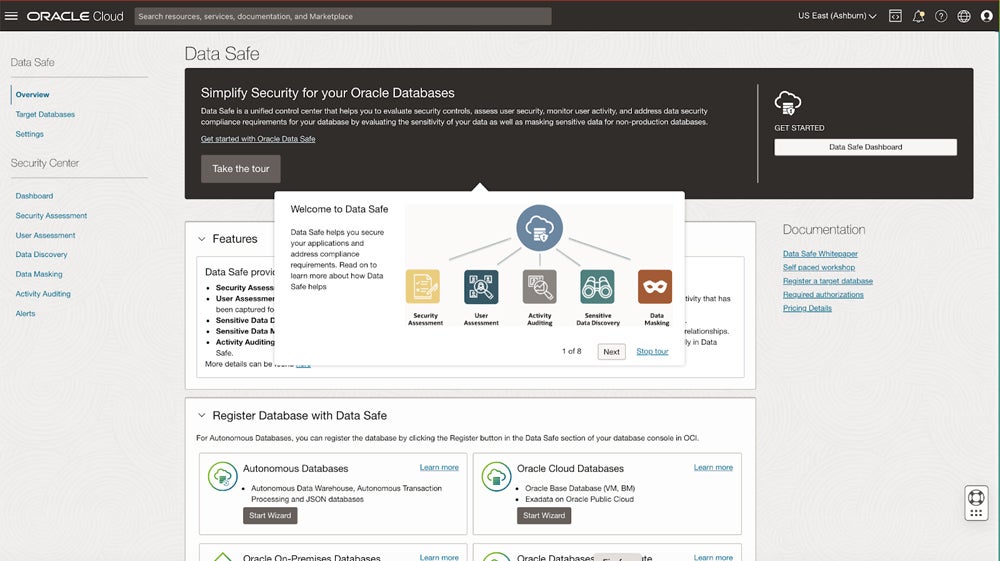
Oracle Data Safe – Best for Oracle Database Environments
Overall Rating: 4/5
- Core features: 3.9/5
- Usability and administration: 3.9/5
- Customer support: 4.5/5
- Advanced features: 3.8/5
- Pricing: 4.1/5
Oracle Data Safe is a full-featured database security product specifically for Oracle databases. Its features include alert policies based on rules, least privilege enforcement, and security compliance reports. It also offers an agentless option, which means data isn’t collected through a software agent. While Data Safe doesn’t support other databases, it’s a great choice for teams with existing Oracle databases and falls under Oracle Cloud Infrastructure (OCI).
Pros
Cons
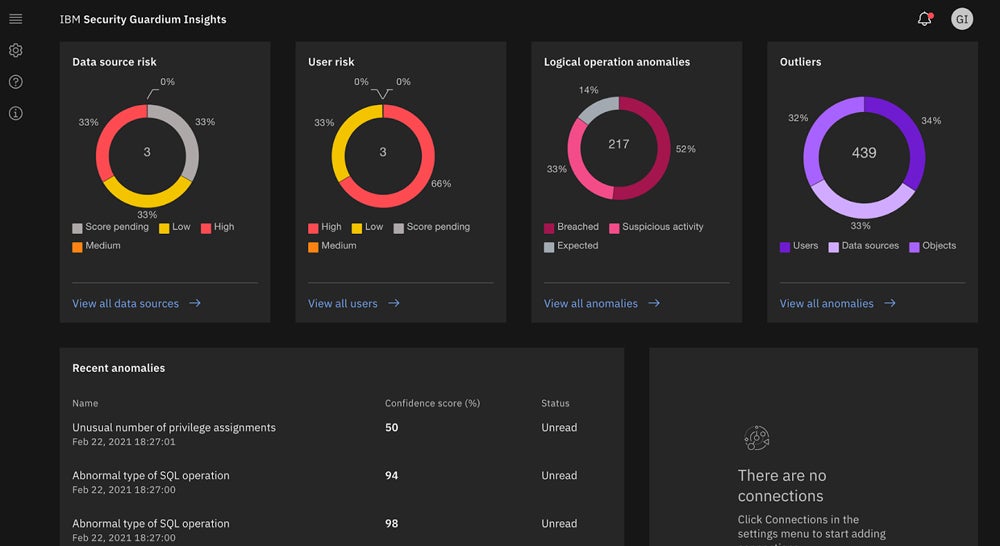
IBM Guardium – Best Enterprise-Grade Database Security Solution
Overall Rating: 3.8/5
- Core features: 4.1/5
- Usability and administration: 3.9/5
- Customer support: 4.1/5
- Advanced features: 3.5/5
- Pricing: 3.3/5
IBM Guardium is an enterprise-grade database security tool with a huge feature set, including data backup and encryption options. Some of Guardium’s capabilities include threat detection, data masking policies, and using both agents or agentless data connections. Guardium particularly stands out as a solution for larger businesses, since it offers so many features. Its backup capabilities also make it a strong choice for organizations with data centers.

Pros
Cons
Using a database security tool alone isn’t enough to have a thriving security strategy. Our list of database security best practices goes beyond software solutions to cover steps your team should take to protect your data.
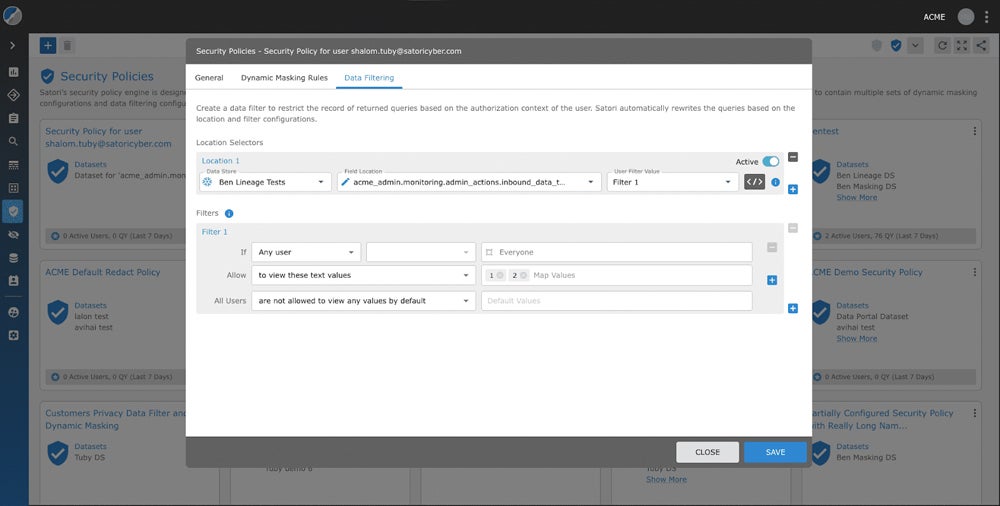
Satori Cyber – Best for AI-Focused Data Security
Overall Rating: 3.4/5
- Core features: 3.5/5
- Usability and administration: 4.5/5
- Customer support: 2.1/5
- Advanced features: 4.1/5
- Pricing: 2.9/5
Satori Cyber is a data platform focused on analytics and security for AI language learning models. Satori helps protect LLMs by setting access policies to determine which users can view and edit them. Admins can create data access workflows to easily determine who can view specific datasets, and Satori searches for sensitive data like financial information and classifies it. LLM activity monitoring allows teams to see what data is coming and going from models.
Pros
Cons
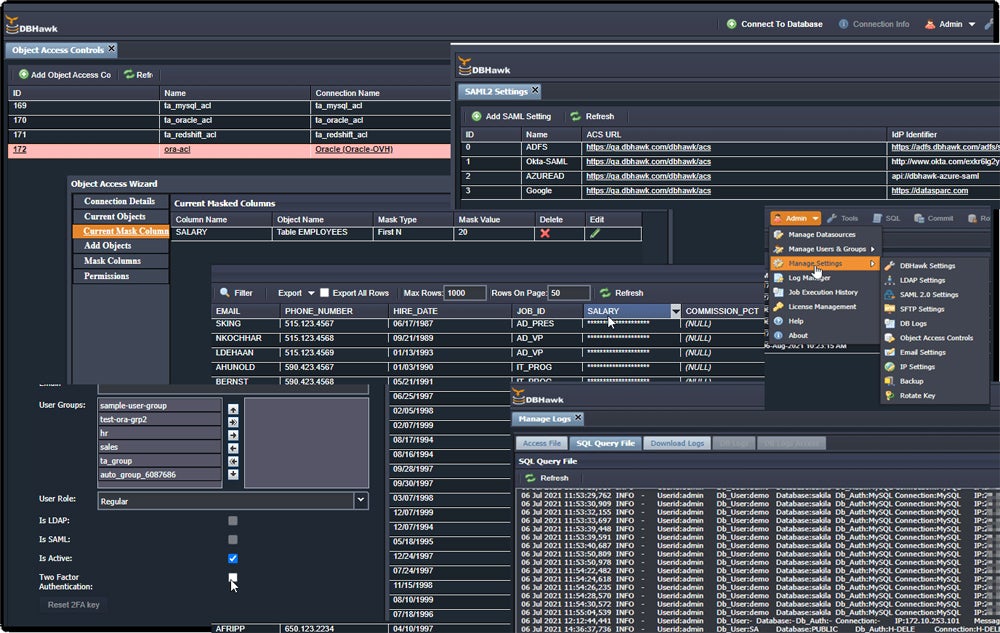
DBHawk – Best Managed Database Security Platform
Overall Rating: 3.4/5
- Core features: 4.2/5
- Usability and administration: 3.5/5
- Customer support: 3.2/5
- Advanced features: 1.9/5
- Pricing: 3.4/5
DBHawk is a managed database security provider that particularly shines for its selection of core security features. Highlights include data masking, role-based access controls, and activity logging. It also supports a huge variety of databases and database management systems, including Cassandra, MongoDB, and MariaDB. The SaaS plans’ features, like chart and dashboard building and SSO integrations, are helpful for smaller businesses and teams.
Pros
Cons
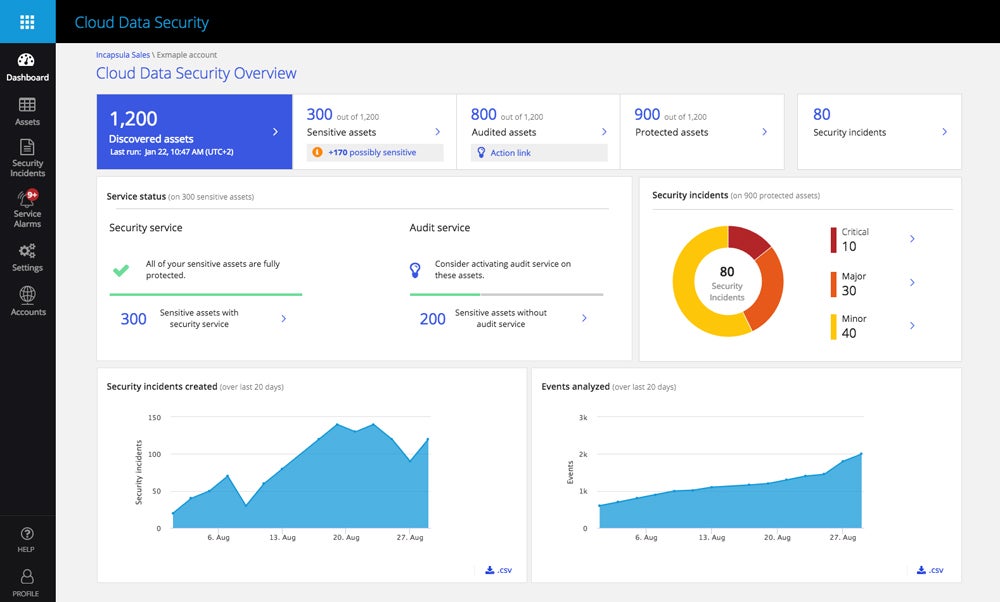
Imperva Data Security – Best for a Mix of Support & Pricing
Overall Rating: 3.3/5
- Core features: 2.6/5
- Usability and administration: 3.3/5
- Customer support: 5/5
- Advanced features: 2.2/5
- Pricing: 4/5
Imperva is a data security provider offering both a hybrid data security platform and protection for cloud databases as a service. The cloud data security product is specifically designed for AWS DBaaS. Imperva offers 24/7 phone and email support; constant availability is useful for smaller teams that need extra help. Imperva offers a pay-as-you-go pricing option through AWS, a base plan for up to 50 million events per month, and other plans for more events.

Pros
Cons
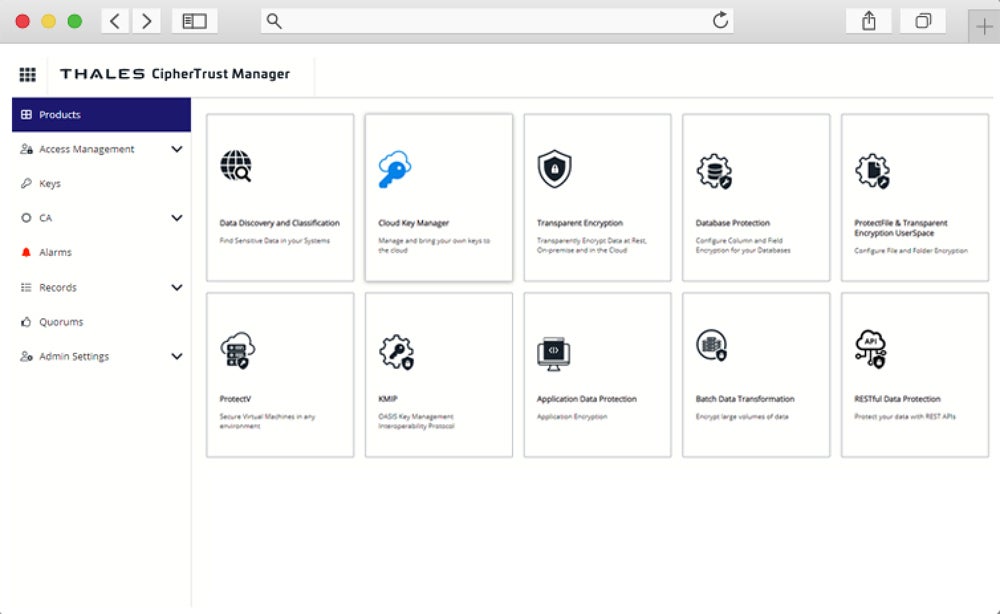
Thales CipherTrust – Best for Encryption-Specific Needs
Overall Rating: 3.3/5
- Core features: 2.4/5
- Usability and administration: 4.5/5
- Customer support: 5/5
- Advanced features: 1.4/5
- Pricing: 3.3/5
Thales Ciphertrust is an encryption and key management platform that offers database protection as part of its lineup. Its features include key rotation and per-column database encryption and access controls. If your business is particularly focused on encrypting sensitive data and controlling access to specific columns and cells, consider CipherTrust. It’s particularly beneficial for teams in industries like finance and healthcare that store lots of sensitive data.

Pros
Cons
5 Key Features of Database Security Solutions
Some of the most important features to look for in database security products include policy and rule management, access management, activity monitoring, and data masking. Also, look for database security platforms that support multiple databases, especially if you use data stores from a few different providers.
Policy Management
Storage and security teams must be able to define specific policies for accessing data within databases. Policies include identifying underutilized privileges, flagging suspicious access activity, and hiding data from users’ view. Customizability is an important function of policy management so your team can configure rules based on your business’s overall security expectations or compliance requirements.
Access Controls
Access controls and policy management go hand in hand — your team will use policies and workflows to define which users can access certain data. You might also need different access levels; for example, some users are able to edit data in a particular database column, while others are only allowed to view it. When properly assigned and developed, access controls limit the number of people who can see and manipulate sensitive information.
Database Activity Monitoring
Database security tools should constantly monitor databases to identify anomalous behavior or places where the database isn’t secure. Security policies determine how the database should operate, and once an activity doesn’t meet a policy or triggers an incident, the platform alerts administrators. Database security solutions should also collect activity logs so admins can see behavioral patterns, even if an alert hasn’t been triggered yet.
Data Masking
Data masking hides sensitive information from users who don’t need to see it. Tokenization is an example of masking — it shields the actual data by showing fake data in its place. Some platforms mask data granularly, such as by column; that’s helpful if users need to view customer information like email addresses but should not be viewing their credit card data, for example.
Database Support
Businesses with a variety of databases should look for a platform that can monitor and enforce policies for all those databases. While there are a few exceptions to this rule, like database-specific solutions for very popular DB products like Oracle, I recommend looking for wide product support if your business needs to protect multiple databases.
How I Evaluated the Best Database Security Solutions
To select the best database security products for businesses and rank them, I created a product scoring rubric with five major categories that buying committees should consider. Each of the five criteria received a specific weight based on importance, and each contained multiple subcriteria that were also weighted. How well each product met the subcriteria for database security solutions contributed to its final score.
Evaluation Criteria
I first looked at core database security features like policy management, activity monitoring, and access controls. Then I considered usability features, such as documentation and training videos, and customer support, which included support channels and 24/7 availability. Finally, I evaluated advanced features, like IAM and governance integrations, and pricing availability, including free product trials.
- Core features (30%): This criterion included the most critical database security features, like data logging and limited access to data.
- Criterion winner: DBHawk
- Usability and administration (20%): I considered features like plenty of documentation, as well as cloud and on-premises deployment options.
- Criterion winner: Multiple winners
- Customer support (20%): I looked at support channels like phone and email, support team availability, demos, and community forums for users.
- Criterion winner: Multiple winners
- Advanced features (15%): These additional capabilities, like integrations with identity providers and governance features, aren’t as common but are nice to have.
- Criterion winner: Satori
- Pricing (15%): I evaluated available pricing information, the option to pay per use, free trials, and availability of small business plans.
- Criterion winner: Oracle
Frequently Asked Questions (FAQs)
Who Uses Database Security Tools?
Any organization with a database can use a database security solution. They’re particularly helpful products for organizations that need to protect large volumes of data or that process sensitive data due to their industry. Examples of these industries include, but aren’t limited to, healthcare, finances, and government. But they’re helpful for any teams that use databases and want to more carefully protect the data stored there.
What are the Benefits of Database Security Software?
Database security solutions help teams take control of the ways people access their information. The products organize policies for handling sensitive information and hide it from users who don’t need to see it. Database security products are also a helpful compliance tool — some regulatory standards require your business to show exactly who can access data. This is particularly beneficial for data privacy regulations like PCI-DSS and CCPA.
How Can You Secure Your Database?
While extremely useful, database security software isn’t the only way to protect databases. Aside from setting user policies and access controls within the database, you should also install a firewall in front of the database to filter traffic requests to the database. This helps secure the network and the database. And if your database is hosted on your business’s premises, don’t neglect physical security — require key fobs to enter the building and server room.
Learn more about protecting your entire network from the security vulnerabilities and misconfigurations that threaten it.
Bottom Line: Database Security Is a Critical Step in Protecting Your Data
Securing large volumes of data is difficult, especially because data sprawl makes any sort of management a challenge. But don’t put off securing your business’s databases. A security solution can save you money in the long run by helping you comply with regulatory standards. Regardless of compliance requirements, database security helps you shield your customers’ and business’s data from everyone except those who absolutely need access to it.
If you need to build your business’s overall network security aside from protecting your databases, read our guide to securing your network next. It includes steps like configuring your firewall and running tests and audits.