OPSWAT continues to build out the capabilities of MetaAccess, their network access control (NAC) solution, and offers an attractive trial of up to 50 licenses for an unlimited duration. MetaAccess focuses on delivery of a virtual appliance that can be deployed with equal capability in local networks or in the cloud for robust, far-reaching capabilities. Below, we’ll explore more MetaAccess features, pros, cons, and pricing information.
To compare OPSWAT MetaAccess against competitors, see the complete list of top network access control (NAC) solutions.
Who Is OPSWAT?
OPSWAT is a cybersecurity company that offers two main security product platforms: MetaDefender (threat protection) and MetaAccess (cloud access control and endpoint compliance). More than 1,500 organizations worldwide use OPSWAT products to minimize risk of compromise, including 98% of US nuclear power facilities. OPSWAT maintains offices in North America, Europe, Australia, and throughout Asia and the Middle East and further extends its reach through a partner network. OPSWAT makes a variety of other products beyond NAC for application security, industrial cybersecurity, email security, malware analysis, zero trust access, and more.
OPSWAT MetaAccess
OPSWAT’s MetaAccess evolved from Impulse’s SafeConnect network access control solution and was rebranded after acquisition. The latest version of MetaAccess solution extends network access control to cover software-as-a-service (SaaS), cloud resources, and a wide variety of “headless devices” such as internet of things (IoT), operations technology (OT), industrial control systems (ICS), medical devices, and industrial IoT (IIoT).
The MetaAccess NAC functionality can be further extended with:
- MetaAccess OT, an appliance for controlling remote access to operational technology and industrial assets
- MetaAccess SDP for implementing software defined perimeters (SDPs) to replace insecure virtual private network (VPN) connections and secure cloud resources
- MetaAccess Zero-Trust access platform to add additional anti-malware scanning, anti-keylogging protection, anti-screen capture protection, and other features to implement zero trust network access (ZTNA)
Agents
MetaAccess provides agentless identification, profiling, and access control for all devices connecting to a network. It creates these profiles by pulling information from in-line network devices (firewalls, wireless routers, etc.), existing identity access management tools (Active Directory, etc.), dynamic host configuration protocol (DHCP) communication, as well as from the device itself such as MAC addresses, URLs, and web browser user agent identification.
OPSWAT also provides optional persistent (always-on) and on-demand OPSWAT Clients (agents) that deploy on Windows, macOS, Linux, iOS, and Android operating systems. For all OS, the client ensures device compliance, vulnerability and patch management status, and secure access. The Windows client adds capabilities to protect against malware, key-loggers, screen capture, and malicious removable media.
Applicable Metric
Each MetaAccess appliance scales up to 25,000 concurrent endpoints and can be assembled into appliance clusters for larger environments.
Security Qualifications
OPSWAT MetaAccess has earned certification for ISO 27001:2013 and is available on the US government GSA Multiple Award Schedule through 2024. OPSWAT also provides a white paper Regulatory Compliance Guide that explains how to use MetaAccess to achieve compliance with ISO 27001, HIPAA, PCI-DSS, and other compliance standards.
Features
- Access options for passive onboarding, bulk upload by MAC address, or self-registration
- Automated device remediation through self-service portals
- Bi-directional security tool integration with network feeds and network security solutions to enable quick reactions and to enact real-time quarantines for severe alerts
- Compliance device check to verify that Windows, macOS, and mobile devices meet corporate and regulatory standards regarding identity, device, and device status (patches, antivirus, etc.)
- Detailed device information extracted without agents such as username, IP address, MAC address, role, device type, location, access time, and device ownership
- Local or cloud-based deployment
- On-demand and automatable email reports that can be scheduled on a daily, weekly, or monthly basis or exported to external security tools
- Real-time discovery of new users and devices, including IoT
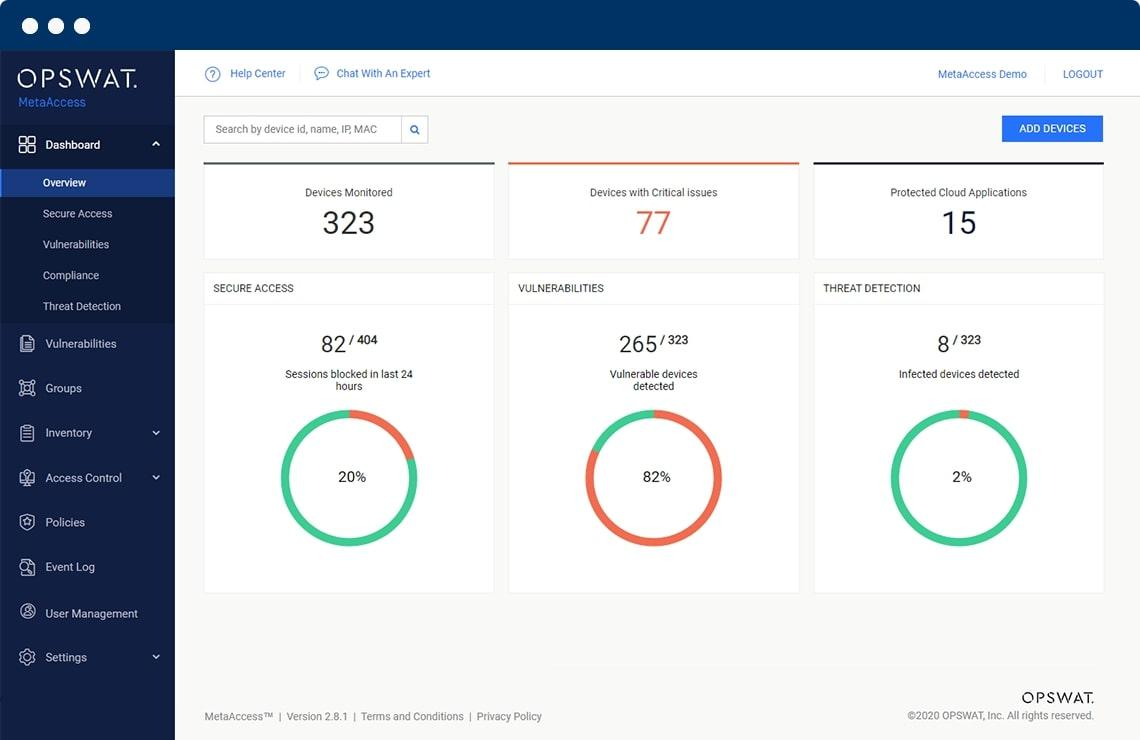
- Real-time and historical reporting for devices, users, and access
- Remote installation, training and deployment and automated NAC tool updates
- Secure guest access, vendor access, and other third-party access with granular access levels and approval processes
- Self-registration onboarding for guests and new devices through highly customizable portals
- Vendor independent deployment compatible with many network equipment vendors and a broader range of endpoints
Pros
- Integrated RADIUS server to authenticate users using the remote authentication dial-in user service (RADIUS) protocol and provide Layer 2 network control
- Optional Layer 3 policy-based routing and network control
- Port-level and role-based access control
- Restricted specific VLAN access based upon specific host and MAC address combinations
- Simplified installation and maintenance with a five-step implementation process and remote managed services that provide proactive monitoring and nightly configuration back-ups and updated device type lists
- Works for wired and wireless networks without any need to change network design or install agents
Cons
- Opaque capacity maximums and license requirements
- Does not publish pricing to help judge total cost of ownership
- Does not publish license information or options for perpetual licenses, subscriptions, or other purchase plans
- Integration and setup require expertise and isn’t for beginners, according to customers
- Can be difficult to configure based on challenges with server installation or third-party tool integration
- Updates can only be applied by the vendor — not the best solution for companies wanting full control
Intelligence
OPSWAT MetaAccess provides device intelligence through agentless and agent-based analysis to integrated third-party security tools. MetaAccess can also act on intelligence and alerts from third-party security tools to isolate systems.
Delivery
Virtual machine (VM) deployment supports VMWare, Hyper-V, and Azure. VM appliances can be paired in high availability mode with synchronized active and passive appliances and multi-appliance clusters can be created for environments with more than 25,000 devices.
Pricing
OPSWAT does not list pricing for their MetaAccess product, but it’s free to download for up to 50 licenses with no trial expiration. Once an organization determines that they want to expand their usage, OPSWAT encourages contact with their sales team or with resellers.
OPSWAT Customer Support Plans
OPSWAT offers five different customer support plans with improving service level agreements and included features, although they don’t publish the price for each tier:
- Silver
- No phone support, 7am to 7pm chat support, 7am to 7pm Portal Case Management System support
- 4-hour first response for high severity issues
- 3-business-day first response for low severity issues
- Gold
- 24-hour support on business days via phone, chat or Portal Case Management System
- 2-hour first response for high severity issues
- 2-business-day first response for low severity issues
- Platinum
- 24-hour support on business days via chat
- 24 x 7 x 365 phone and Portal Case Management System support
- 1-hour first response for high severity issues
- 1-business-day first response for low severity issues
- Adds an assigned customer success manager, quarterly reviews, yearly roadmap review, quarterly reports
- Platinum — US In-Country
- 8am to 9pm Eastern support on US business days via chat
- 24 x 7 x 365 phone and Portal Case Management System support for blocker cases
- 1-hour first response for high severity issues
- 1-business-day first response for low severity issues
- Adds an assigned customer success manager, quarterly reviews, yearly roadmap review, quarterly reports
- Diamond
- 24-hour support on business days via chat
- 24 x 7 x 365 phone and Portal Case Management System support
- Within-1-hour first response for high severity issues
- Within-1-business-day first response for low severity issues
- Adds to Platinum service: advanced replacement warranty for hardware, complete managed service, 24×7 alerting and resolution, active monitoring of hardware health, active monitoring of OPSWAT software, remote management for support, ongoing reporting
Bottom Line: Great for Smaller Teams of Experts
OPSWAT MetaAccess shows great promise as a NAC solution with robust capabilities and a simplified, non-invasive deployment that requires neither network adjustments nor agents. With an unlimited free trial of 50 licenses or fewer, many smaller organizations will be very interested, but the needed expertise for deployment and the unpublished prices will be a deterrent. However, the strong capacities of the basic license should make MetaAccess an option to explore, especially if for those that may also want to consider other OPSWAT options such as SDN, endpoint security, or email security.
This article was originally written by Drew Robb on July 7, 2017, and updated by Chad Kime on April 17, 2023.




