To defend against attacks, ransomware protection software and removal tools employ a variety of methods like backups, network segmentation, incident response, and endpoint security. Effective ransomware protection and removal allow organizations to resume operations without interruption, regardless of the severity of the ransomware assault. To assist you in selecting the most suitable one, I’ve examined the leading ransomware protection and removal tools.
Here are the six best ransomware protection and removal tools:
- Malwarebytes: Best overall ransomware removal tool
- Bitdefender: Best ransomware remediation tool
- Trend Micro: Best for pricing and extra security capabilities
- ESET PROTECT: Best for real-time endpoints visibility
- Sophos: Best for customer support and cyber insurance
- Avast: Best free ransomware scanner and prevention tool
Featured PartnersFeatured Partners: Cybersecurity Software
eSecurity Planet may receive a commission from merchants for referrals from this website
Top Ransomware Protection & Removal Tools Comparison
Here’s a comparison chart for the six best tools, outlining their key ransomware protection and removal capabilities and their pricing details.
| Ransomware Detection | Ransomware Decryptor Tools | Expert Support for Rescue & Restoration | Cyberthreat Insurance | Lowest Tier Pricing Per Device | |
|---|---|---|---|---|---|
| Malwarebytes | ✔️ | ✔️ | ➕ | ➕ | $6/month |
| Bitdefender | ✔️ | ✔️ | ✔️ | ➕ | $4/month |
| Trend Micro | ✔️ | ✔️ | ➕ | ✔️ | $4/month |
| ESET PROTECT | ✔️ | ✔️ | ➕ | ➕ | $13/month |
| Sophos | ✔️ | ✔️ | ✔️ | ✔️ | Contact sales |
| Avast | ✔️ | ✔️ | ➕ | ➕ | $13/month |
✔️= Yes ➕= Limited/Add-On
While several products excelled in individual categories, Malwarebytes leads among the options due to its overall ransomware protection and removal capabilities. However, Bitdefender and Trend Micro are very close contenders. Read more below to see each tool’s performance in pricing, features, and key use cases, or head directly to my evaluation methodology.
Note: All per-endpoint prices are based on a one-year commitment unless otherwise noted.
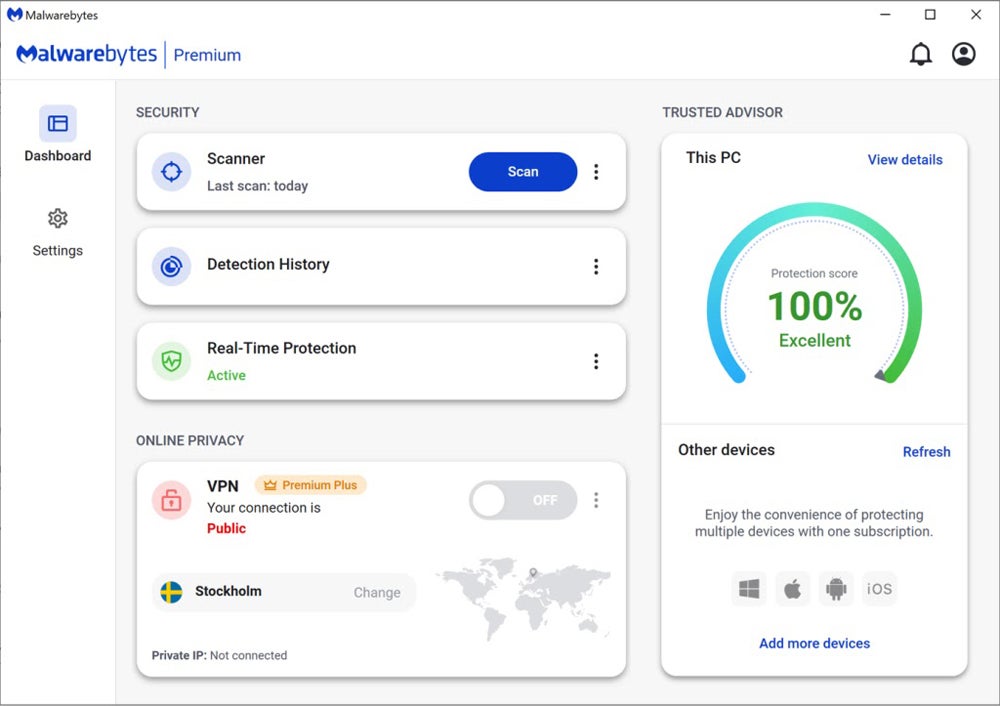
Malwarebytes – Best Overall Ransomware Removal Tool
Overall Rating: 4.4/5
- Core features: 4.6/5
- Extra security capabilities: 3.8/5
- Pricing and transparency: 4.6/5
- Ease of use and admin: 5/5
- Customer support: 3.4/5
- Compliance and data privacy: 4.7/5
Malwarebytes leads our list of the top anti-ransomware tools with its wide array of core features, intuitive UI, and easy deployment. Malwarebytes Premium actively prevents ransomware attacks and includes robust features including threat advisory services, multi-platform compatibility, suspicious website blocking, and detection with rollback capabilities. It also employs AI and machine learning to give more complete protection against emerging threats.

Pros
Cons
Bitdefender – Best Ransomware Remediation Tool
Overall Rating: 4.3/5
- Core features: 4.4/5
- Extra security capabilities: 4.5/5
- Pricing and transparency: 3.9/5
- Ease of use and admin: 5/5
- Customer support: 2.9/5
- Compliance and data privacy: 4.7/5
Bitdefender’s GravityZone is a unified platform that offers a ransomware remediation tool to secure against ransomware attacks by automatically backing up items such as documents, photos, videos, and music. When Bitdefender detects a ransomware attack, it stops all relevant processes, starts the cleanup process, and alerts the user. This enables the recovery of encrypted data without the need to pay a ransom, protecting data from loss or destruction.

Pros
Cons
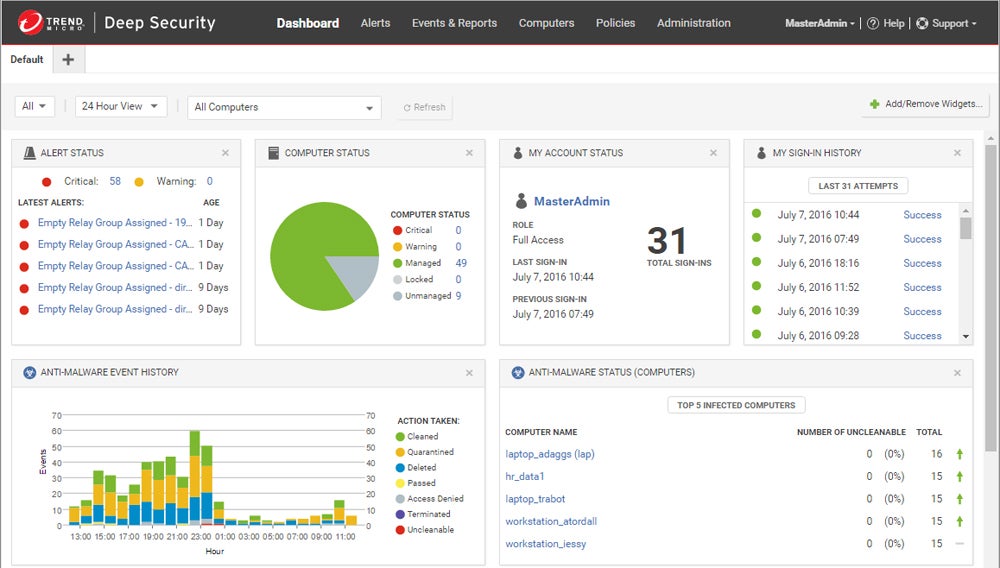
Trend Micro – Best for Pricing & Extra Security Capabilities
Overall Rating: 4.2/5
- Core features: 4.1/5
- Extra security capabilities: 4.3/5
- Pricing and transparency: 5/5
- Ease of use and admin: 3.8/5
- Customer support: 2.8/5
- Compliance and data privacy: 5/5
Trend Micro Deep Security’s ransomware protection tool offers additional security features such as a data/file shredder, interaction with security tools, a vulnerability scanner, and access to cyberthreat insurance for total protection. It provides cloud and on-premises deployment options, antivirus, ransomware detection, and a list of decryptor tools you can use. They provide transparent pricing details for all their plans so you can gauge the most suitable plan for you.

Pros
Cons
ESET PROTECT – Best Real-Time Endpoints Visibility
Overall Rating: 3.8/5
- Core features: 4.4/5
- Extra security capabilities: 3.2/5
- Pricing and transparency: 3.9/5
- Ease of use and admin: 4.4/5
- Customer support: 2.5/5
- Compliance and data privacy: 4/5
ESET PROTECT provides real-time visibility of all endpoints via a user-friendly online portal available on-premises or in the cloud, offering extensive monitoring and administration capabilities. The Advanced edition protects against ransomware and sophisticated threats by combining endpoint security, complete disk encryption, and cloud sandbox analysis. It uses advanced ML and behavioral inspection to accurately prevent ransomware-like processes.

Pros
Cons
Sophos Intercept X – Best Customer Support & Cyber Insurance
Overall Rating: 3.7/5
- Core features: 4.3/5
- Extra security capabilities: 3.7/5
- Pricing and transparency: 2.2/5
- Ease of use and admin: 4.8/5
- Customer support: 3.5/5
- Compliance and data privacy: 4/5
Sophos Intercept X offers global expert support via Sophos X-Ops to provide rapid, effective enterprise-level ransomware security. Through their latest CryptoGuard 5 technology, the tool protects endpoints and servers against ransomware by preventing illegal encryption and then restores data. Combining the tool with Sophos MDR, users can reduce their cyber risk via Cysurance’s enhanced ransomware protection and up to $3.2M insurance coverage.

Pros
Cons
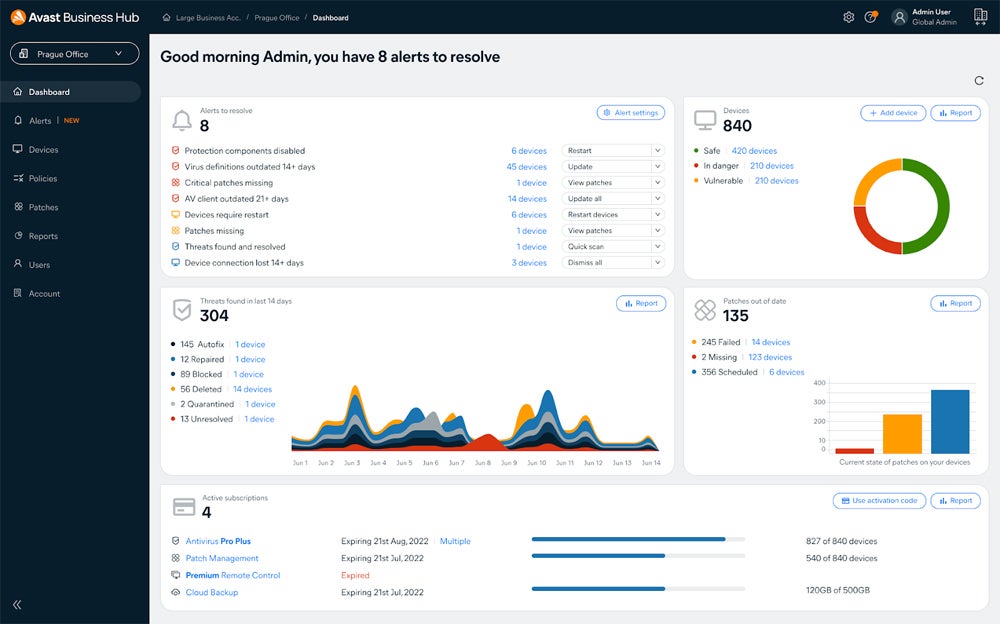
Avast – Best Free Ransomware Scanner & Prevention Tool
Overall Rating: 3.7/5
- Core features: 4/5
- Extra security capabilities: 3/5
- Pricing and transparency: 4.2/5
- Ease of use and admin: 4.3/5
- Customer support: 1.9/5
- Compliance and data privacy: 3/5
Avast provides a reliable and free ransomware detection and prevention tool, supported by a large community of over 435 million members. Its free antivirus tool, Avast One, prevents viruses and malware, detects threats in real time, scans for Wi-Fi weaknesses, and protects personal files from encryption. Their paid plans offer advanced protection, including a sophisticated firewall to prevent data theft and Avast SecureLine VPN for encrypted browsing.

Pros
Cons
Top 5 Features of Ransomware Protection & Removal Tools
Ransomware detection, decryptor tools for file recovery, and expert restoration assistance are all essential features of ransomware protection and removal tools. A good tool should also provide real-time antivirus protection to avoid attacks and should incorporate cyber insurance for financial protection against ransomware assaults.
Ransomware Detection
The ransomware detection feature quickly identifies and warns users about ransomware threats before they encrypt files or affect systems. It uses complex algorithms and behavioral analysis to proactively detect ransomware-like activity, allowing users to take timely action to neutralize the danger and avoid potential data loss or extortion efforts.
Decryptor Tools
Ransomware decryptor tools are specialized software that reverses the encryption that ransomware uses on files or computers. These tools use a variety of approaches, including brute-force attacks and exploiting encryption weaknesses, to recover encrypted data without paying the ransom, allowing users to safely restore access to their files and computers.
Rescue & Restoration Expert Support
This offering delivers immediate assistance during ransomware outbreaks. Ransomware solutions often include support services from cybersecurity professionals who guide customers through recovery methods, decrypt files, and reduce damage, providing quick system restoration and little downtime, protecting data integrity and business continuity.
Real-Time Antivirus Protection
Real-time antivirus protection continually watches for harmful actions that could indicate a ransomware encryption attempt. Using an antivirus tool prevents file encryption by quickly detecting and fighting ransomware in real time, reducing the risk of data loss and financial extortion. It then ensures that users retain control of their systems.
Cyber Insurance
Cyber insurance protects against the financial losses resulting from ransomware attacks. It includes expenses such as data recovery, legal fees, and regulatory fines. By having a cyber insurance service, you reduce the financial effect of assaults while allowing your firm to recover swiftly and continue operations with minimal disruption.
How I Evaluated the Best Ransomware Protection & Removal Tools
To conduct an extensive review, I classified six main criteria of ransomware protection and removal tools. Each category includes subcriteria — a list of specific features and functions, all weighted and scored based on their availability. Based on the overall scores, I identified the top six tools. Lastly, I determined each tool’s specific use cases by taking into account their highest scores and supplemented it with my research on user reviews and other relevant resources.
Evaluation Criteria
In this evaluation, I prioritized assessing the core features required for ransomware prevention and removal. Following that, I evaluated the extra security features to determine their added significance. Next, I considered the pricing transparency, as well as ease of use and administration. Finally, I conducted a comparison of the tools’ customer service quality, their data privacy policies transparency, and their compliance procedures.
- Core features (25%): Identifies the available fundamental features in ransomware protection and removal tools such as detection, decryptor tools, threat insights, backup, storage, and more.
- Criterion winner: Malwarebytes
- Extra security capabilities (20%): Checks the additional features that make a tool more robust in security, including integrations, vulnerability scanning, and cyberthreats insurance.
- Criterion winner: Bitdefender
- Pricing and transparency (20%): Compares the availability of free trial and demo, pricing transparency, flexibility in pricing models, and lowest to highest subscription costs.
- Criterion winner: Trend Micro
- Ease of use and admin (15%): Evaluates features such as intuitive user interface, centralized management console, non-disruptive operations, and user reviews from different platforms.
- Criterion winner: Multiple winners
- Customer support (10%): Assesses the availability of live chat, email or contact information, and 24/7 phone support, and user reviews on customer service from platforms like Capterra and Gartner.
- Criterion winner: Sophos
- Compliance and data privacy (10%): Checks the transparency of privacy policies and the adherence and certifications to major security compliance like ISO 27001/9001 and SOC2.
- Criterion winner: Trend Micro
Frequently Asked Questions (FAQs)
How Do Ransomware Removal Tools Work?
Ransomware removal tools isolate the affected device from networks to prevent further spread. They then identify the ransomware type and create eradication measures. They use antivirus software to scan for and remove ransomware. Restoration entails recovering a clean backup or using a decryption tool. They also offer advice on recommended practices for preventing such attacks and ensuring system security through regular updates.
Are Ransomware Removal Tools Effective Against All Types of Ransomware?
Although ransomware removal solutions can be useful, they can’t eliminate all types of ransomware. Prevention is the key to reducing these threats. While removal techniques may be effective in some circumstances, certain ransomware strains may resist removal. Focus on strong preventative methods to reduce the possibility of malware, particularly ransomware, accessing network systems.
Do Ransomware Removal Tools Interfere with Existing Antivirus or Security Software?
Ransomware removal tools typically supplement existing antivirus or security software, working together to improve protection. However, compatibility difficulties or competing functionalities may occur, thereby affecting system performance. It’s essential to check tool compatibility and review any potential conflicts ahead of time.
Bottom Line: Protect Your Assets with Ransomware Protection & Removal Tools
If your files are encrypted with highly secure ransomware, recovery is extremely difficult. I don’t recommend paying the ransom as it has no guarantee of file recovery. While ransomware removal tools don’t always decrypt files, decryption tools can certainly help with recovery for some strains. Conduct regular backups to reduce the need for ransomware recovery and use free versions and trials to check that the solutions you choose meet your needs.
To reduce your worries about ransomware attacks, invest in a dependable endpoint detection and response (EDR) solution for proactive threat detection and rapid incident response.