The Anomali ThreatStream threat intelligence platform (TIP) integrates hundreds of threat information feeds with the analytics a security professional needs to understand how a specific threat might impact the organization. This article provides more in-depth information on the product and its features.
For a comparison with other TIP products, see our list of the top threat intelligence companies.
Company Description
Anomali was created in 2013 and has since grown to 250+ employees. It is privately held with several venture capital investors. It has offices in Redwood City, Belfast, Singapore, and Dubai. Anomali’s series D funding raised $40 million in 2018, raising the total funding to more than $96.3 million since launch.
Product Description
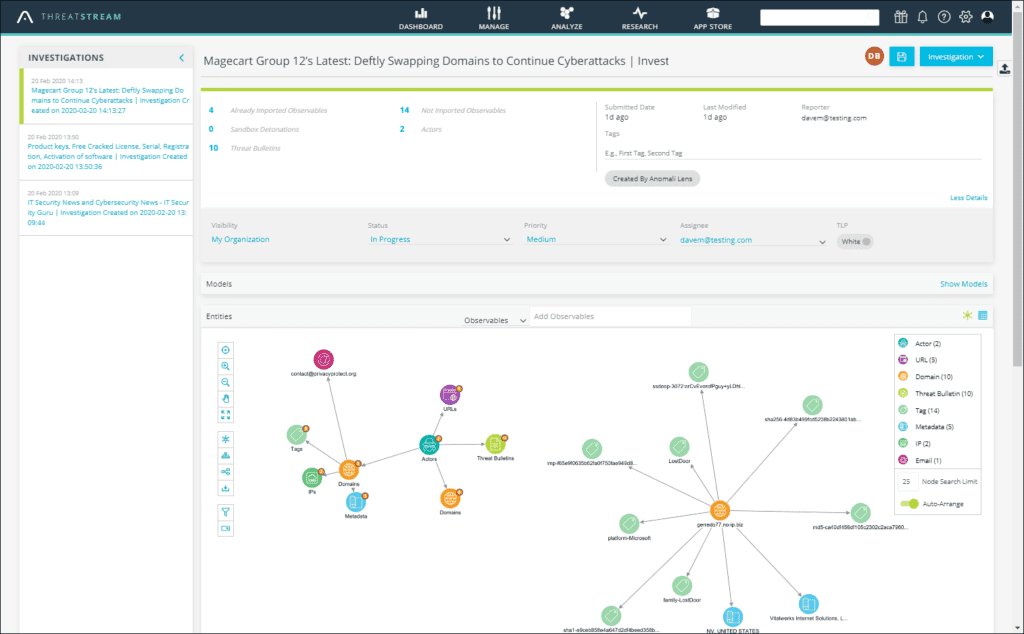
The Anomali suite of threat intelligence solutions empower organizations to detect, investigate and respond to active cybersecurity threats. The ThreatStream threat intelligence platform (TIP) aggregates and optimizes millions of threat indicators and integrates with internal infrastructure to identify new attacks, discover existing breaches, and enables security teams to quickly understand and contain threats before affecting the whole network.
Other Anomali tools include:
- STAXX, a free tool to collect and share threat intelligence using STIX and TAXII standards for machine-readable information formatting
- Lens, a commercial product that uses Natural Language Processing (NLP) to scan unstructured data to identify threats
Until August 14, 2022 Anomali provided a free, out of the box intelligence feed, Anomali Limo. Anomali indicates a replacement may be in development, but has not yet provided any details. However, Anomali continues to provide secure threat sharing for ISACs and threat sharing networks.
Anomali ThreatStream features include:
- Automated collection of threat data from hundreds of sources and in multiple formats – notably Anomali Labs, open-source OSINT feeds, and information sharing and analysis centers (ISACs)
- Threat data is contextualized with relevant actors, campaigns, as well as tactics, techniques, and procedures (TTPs)
- Normalization, enrichment, de-duplication of data, and removal of false positives at scale
- Threat intelligence scoring using machine learning (ML) algorithms to rate confidence in the score that reflects the severity of the threat
- Global intelligence feed ROI optimizer to assess sources
- Turnkey threat feed integration for security tools such as SIEMs, SOARs, firewalls, IPS, endpoints, etc.
- Security tool integration for inbound data ingestion and outbound response orchestration
- Flexible integrations using RESTful API and SDKs
- Workflows and functionalities to analyze and share data
- Brand monitoring (automatic search for typosquatted domains & compromised credentials)
- Sandboxing (research malicious indicators directly within the ThreatStream platform)
- Extracting data from suspected phishing emails for immediate blocking
- MITRE ATT&CK mapping of global threats
- Visual link analysis to connect indicators to associated higher-level threat models
- Integrated sandbox to investigate suspicious files
- Share threat visibility and identification with more than 2,000 other organizations in ThreatStream Trusted Circles
- Threat bulletins and other finished intelligence products for publishing reports to stakeholders
- Flexible deployment options: cloud-native, virtual machine, on-premises private instance, or even ThreatStream AirGap – a completely stand-alone instance
Additional optional features can include commercial threat feeds and other applications available from the Anomali App Store (some include trial periods).
Anomali describes ThreatStream as “a central platform for collecting, managing, and sharing threat intelligence. Integration with common security solutions ensures that organizations can identify and respond to the threats relevant to their environment.”
Agents
Anomali ThreatStream does not use agents.
Markets and Use Cases
Anomali says it provides value for any organization across any industry vertical that is looking to leverage threat intelligence. Anomali’s ThreatStream Platform is used by many the Fortune 100 companies and and banks.
Applicable Metrics
ThreatStream consumes both structured and unstructured data from hundreds of threat intelligence feeds, processing millions of Indicators of Compromise (IOCs).
Intelligence
Anomali’s ThreatStream platform utilizes MACULA, a machine learning algorithm, to score and weight indicators and remove false positives. The ThreatStream platform automates traditionally manual data curation tasks. It also integrates with other security products, including SIEMs, firewalls, endpoint products and more.
ThreatStream Trusted Circles enable an organization to share threat visibility and identification with more than 2,000 other participants. Organizations can also acquire premium threat feeds in the Anomali App Marketplace.
Delivery
ThreatStream is available as a SaaS, for virtual machines, on-premises, or even as an air-gapped solution. On-premises and air-gapped solutions allow customers to acquire threat information without sharing data or permitting internal threat information from leaving their network.
Pricing
Pricing for the ThreatStream Platform varies based on the customer environment. Anomali does not publish pricing on their own website, but the AWS marketplace shows a 12 month subscription to Threatstream Enterprise for 3,500 employees is $150,000.
This article was originally written by Drew Robb on July 18, 2017, and updated by Chad Kime on February 8, 2023.




