Quick response (QR) codes are a convenient format for storing all kinds of information in a readable and secure way, at least when correctly implemented. With the ongoing COVID-19 pandemic, for example, governments have recently implemented QR codes to create Digital COVID Certificates for vaccination, tests status and other reasons.
QR technology isn’t new, and security features like two-factor authentication (2FA) or multi-factor authentication (MFA) often invite users to generate such codes to secure their access to mobile apps. And like other authentication technology, it’s also attracted the attention of hackers looking to exploit any weaknesses; just last month, the FBI warned about potential misuse of QR codes.
Here’s how QR codes work, how hackers can use them against you, and how to defend yourself and your organization.
How QR Codes Work Behind the Scenes
Technically speaking, a QR code is similar to a barcode, but it usually carries more information. While to humans, they may seem like an odd connection of black pixels on a white background, the format is remarkably readable for machines.
Computers understand QR codes as matrices of 0 for the white spaces and 1 for the colored spaces, but as it’s not a human-readable format, it’s neither a left-to-right nor a top-to-bottom order. The three squares in the generated image determine the alignment, and many areas are just internal parameters QR code readers use to calibrate.
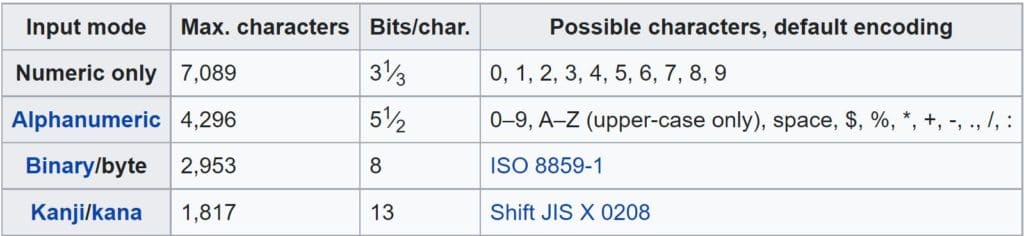
In fact, only a tiny part of the QR code contains your information, and a mathematical algorithm is applied to make it redundant. QR code readers will read your information in 8-bit blocks, a specific character set used during encoding and decoding.
Despite how complex they may seem, QR codes are relatively easy to generate. For example, in Python, you can use the QRcode package to make custom QR codes:

The above example only uses simple text, but you can open links and add contact cards, so users only have to scan your QR code to browse a website or save your contact information on their devices.
Threat Actors Love QR Codes
While QR codes offer a great way to store and access information, they come with a fair amount of risk.
Counterfeit Codes
Because QR codes can open links automatically, hackers can use them to redirect users to forged websites and thus improve the success rate of their phishing campaigns, for example. And since QR codes can’t be read by humans, users won’t be able to identify malicious codes, which bad actors can use in place of legitimate codes.
QRL Highjacking
QR logins (QRLs) are QR-code-based authentication methods designed to improve users’ login experiences. Rather than typing in your name and password, you scan a QR code.
While this makes logging in to websites quick and easy, poor implementation, such as not regenerating QR codes each time a user logs in, creates vulnerabilities. Hackers can use sneaky techniques like QRL hijacking to initialize a QR session, clone the QR code, and redirect the victims to a phishing page, allowing attackers to ultimately steal access.
See the Top Vulnerability Management Tools
Hacking with Malicious QR Codes
The excellent usability of QR codes explains why they are almost everywhere, but it also extends the attack surface for outdated software and devices.
As QR codes can contain a lot of information, there is more than enough space to insert malicious code, as in this Wikipedia example:
Attackers can encode tricked payloads in QR codes, waiting for users to scan them to execute the malware.
Also, many open source packages and libraries can generate malformed QR codes and encode common exploits, such as cross-site scripting (XSS), local file inclusion (LFI), directory traversal, or SQL injection.
Also read: How to Defend Common IT Security Vulnerabilities
Flawed Implementations Can Be Devastating
In 2020, Omer Shafiq explained how he spoofed an encrypted QR code containing COVID test reports that was supposed to be digitally signed and unforgeable.
The software architect demonstrated it could be achieved in a reasonable time using open-source tools to inspect the app used to generate and validate QR codes.
While it may not be feasible for those without a technical background, the exploration revealed the app used hard-coded encryption keys and symmetric AES encryption, allowing someone to generate verifiable QR codes after a few manipulations.
Some experts say QR codes are flawed by nature. Moreover, Sophos revealed in 2019 that the creator of QR codes did not envision all possible security implications and even declared that “QR codes need security revamp.”
But that might be going further than necessary; the problem is in the usage and implementation.
QR Code Hacking Protections
Developers should not use static QR codes for user logins or during financial transactions, as hackers can exploit their vulnerabilities to intercept payments or steal credentials. Instead, they should use dynamic QR codes and force users to regenerate them, even if the same user logs in for the second time.
In addition to classic phishing prevention, security awareness must include QR codes and recommend that people not share their personal information on pages opened with such shortcuts unless it’s a trusted source. Check the URL carefully for even slight misspellings, and wherever possible, don’t navigate directly to a website or download an app from a QR code. And don’t download a QR code scanning app — your phone camera can likely perform that function by default.
Even if QR codes are not human-readable, sensitive information must be encrypted to protect users’ privacy, and developers need to follow best practices for secure development.
Read next: Best Cybersecurity Awareness Training for Employees in 2022