
The last few years have brought about dramatic changes in IT, and with those changes have come an equally dramatic increase in cybersecurity risks. The good news is that despite an economic slowdown and a steep drop in venture funding, cybersecurity startups continue to innovate to address those risks.
Through the development of cutting-edge technologies like artificial intelligence and sophisticated encryption techniques, these startups are finding creative ways to counter a wide range of cyber threats, from critical application vulnerabilities to advanced attack groups and even post-quantum encryption threats, both in the cloud and within traditional networks.
We’ll look at the top 68 cybersecurity startups to watch in 2023, their innovations in new and emerging technologies, length of operation, funding rounds, scalability, and more, followed by a discussion of broader trends affecting buyers, startups, and investors.
We’ll begin with the top 21 startups overall and then look at other noteworthy startups in a number of markets, including threat detection, identity, DevSecOps, cloud security, and attack surface management.
Also read:
Table of Contents
- Top 21 Cybersecurity Startups
- Best Threat Detection Startups
- Best DevOps and AppSec Startups
- Best Cloud Security Startups
- Best Cyber Asset and Attack Surface Management Startups
- Best Identity & Access Management Startups
- Best Remote Access Security Startups
- Best Compliance & Governance Startups
- Other Top Cybersecurity Startups
- Investor Considerations for Cybersecurity Startups
- Cybersecurity Startup Trends
- Top Startup Selection Criteria
- Graduated Startups
Featured Cybersecurity Software
Top 21 Cybersecurity Startups
While several of these top security startups have crossed the $100 million revenue threshold and thus could be considered more “private company” than “startup,” we’ve resisted the urge to make major changes to this list at this time because public markets and other traditional startup investor “exits” have been greatly curtailed in the last year. We did, however, move several startups that have been acquired, including BluBracket, Confluera and Perimeter 81, to our “graduated” list at the bottom of this article. And a few companies like Snyk and Wiz have grown so big that they’ll probably IPO at some point, so you’ll find them in our graduated list too. In their place are promising upstarts like SandboxAQ and Traceable AI.
| Startup | Key Feature | Founded | Headquarters | Staff | Funding (in millions) | Round |
|---|---|---|---|---|---|---|
| Apiiro Security | Application Security Risk Graph | 2019 | Tel Aviv, Israel | 113 | $135.0 | B |
| Bishop Fox | Offensive Security Services | 2005 | Phoenix, AZ | 382 | $154 | B |
| Blackpoint Cyber | Security services | 2014 | Ellicott City, MD | 95 | $190 | C |
| Cado Security | Forensic Cloud Security Service | 2020 | London, UK | 53 | $31.5 | B |
| Cycode | Application Security Posture Management (ASPM) | 2019 | Tel Aviv, Israel | 131 | $80.6 | B |
| Deepwatch | Manage Detection Response | 2015 | Tampa, FL | 400 | $256 | C |
| Drata | Security and Compliance Automation | 2019 | San Diego, CA | 427 | $328.2 | C |
| Fortanix | Complete Confidential Computing Environment | 2016 | Silicon Valley, CA | 268 | $135.3 | C |
| Huntress Labs | Automated Detection and Human-Powered Threat Hunting | 2015 | Ellicott City, MD | 310 | $120 | C |
| Immersive Labs | Cybersecurity Training Platform | 2017 | Bristol, UK | 325 | $189 | C |
| Thoropass (Formerly Laika) | End-to-end Compliance Solution | 2019 | New York, NY | 188 | $98 | C |
| NetSPI | Pentesting/Attack Surface Management | 2001 | Minneapolis, MN | 349 | $500 | Private Equity |
| NordSecurity | Streamlined VPN Service | 2019 | Netherlands | 14 | $100 | A |
| Open Raven | Cloud Native Data Discovery and Classification Software | 2019 | Los Angeles, CA | 42 | $40 | B |
| Salt Security | API Security Solutions | 2016 | Silicon Valley, CA | 202 | $271 | D |
| SandboxAQ | AI + Quantum Technology Solutions | 2016 | New York, New York | 195 | $500 | A |
| Saviynt | Identity Management Platform | 2011 | Los Angeles, CA | 989 | $375 | Debt |
| Socure | Digital identity verification solutions | 2012 | Incline Village, NV | 545 | $741.9 | Debt |
| Traceable AI | API security | 2018 | San Francisco, CA | 154 | $80 | B |
| Vanta | Trust Management Platform | 2017 | San Francisco, CA | 439 | $203 | B |
| Versa Networks | Automated Security Monitoring Platform | 2012 | San Francisco, CA | 660 | $316.3 | Private Equity |
Apiiro
Apiiro is a four-year-old Tel Aviv-based startup that offers a Cloud Application Security Platform (CASP) that helps organizations secure their applications from design to production. The platform combines Cloud Security Posture Management (CSPM), Application Security Posture Management (ASPM), and Application Orchestration and Correlation (ASOC) capabilities to provide a comprehensive view of application security risks.
Apiiro’s platform uses a graph-based approach to model application security risks, allowing it to understand the relationships between different security risks and prioritize remediation efforts. It also provides context-aware risk scoring, taking into account the specific configuration of an application and the environment in which it is running.

Bishop Fox
Bishop Fox, based in Washington, D.C., offers offensive security services, research, and training. Founded in 2005 by Vincent Liu, a former Microsoft security engineer and penetration tester, the company provides services such as penetration testing, red teaming, security assessments, research on emerging threats, and training courses.Bishop Fox is one of the oldest companies on this list, but a recent surge in funding shows that venture investors see plenty of opportunity in the company. The company is expanding into new markets, developing new products and services, and actively hiring new security professionals. Overall, Bishop Fox is well-positioned to continue growing and succeeding in the cybersecurity industry.

Blackpoint Cyber
Blackpoint Cyber, founded in 2014 by Jon Murchison, offers services to protect businesses from cyber threats. Their flagship product is a managed detection and response (MDR) service, which uses a combination of human expertise and artificial intelligence to detect and respond to cyber threats in real time. The company also offers security consulting, incident response, and penetration testing.

Cado Security
James Campbell and Chris Doman established Cado Security in 2020, with a forensic cloud investigation platform called Varc (Volatile Artificial Collector) at the heart of the company’s offerings. Varc offers threat-hunting techniques like the ability to painstakingly search data and quickly detect rogue IPs to speed threat response.
Cycode
Four-year-old Cycode’s goal is to help businesses secure their software from the inside out by analyzing software code for security vulnerabilities, providing developers with the information they need to fix them early on in the development process. Comprehensiveness and ease of use are two standout features of this Application Security Posture Management (ASPM) platform, which goes beyond static analysis tools to include dynamic analysis and machine learning capabilities.

Deepwatch
Deepwatch focuses on offering complete managed security services to help businesses quickly and efficiently identify and address threats. The MDR service uses a combination of machine learning, artificial intelligence, and human expertise to monitor and respond to security incidents in real-time. Key features of Deepwatch MDR include 24/7/365 monitoring, automated detection and response, and a team of experienced security analysts.

Drata
Drata is a security and compliance automation platform that aids businesses in achieving and maintaining compliance with industry standards like SOC 2, HIPAA, and GDPR. It automates manual tasks like risk assessments, control testing, and evidence collection. The comprehensive platform covers a wide range of compliance standards, is easy to use, and can be scaled to meet the needs of businesses of all sizes.

Fortanix
Fortanix is a leader in the relatively new field of confidential computing, which allows data to be processed and analyzed while it is encrypted, a critically important security capability for companies processing sensitive data. These solutions are based on the Intel SGX platform, a hardware-based security technology that provides a trusted execution environment (TEE) within the CPU. The company’s customers include Google, Microsoft, and Visa, as well as government agencies and financial institutions.

Huntress Labs
Huntress Labs provides small and medium-sized businesses (SMBs) with automated detection and human-powered threat hunting services. Kyle Hanslovan and Chris Hass launched the business in 2015, and it employs machine learning, artificial intelligence, and human knowledge to recognize and address cyber threats. The platform is intended to assist SMBs in defending themselves against a variety of dangers, such as ransomware, malware, and phishing assaults. The security team at Huntress Labs collaborates with SMBs to create incident response strategies, analyze and address threats, and recover from cyberattacks.

Immersive Labs
Immerse Labs, led by CEO and Founder James Hadley, has been making waves in the cybersecurity industry since its launch in 2017. The Bristol, UK-based business offers a cybersecurity training platform to provide people and companies with the skills and knowledge necessary to guard against cyber attacks. The platform uses gamification features like leaderboards, badges, and challenges to motivate users. Hands-on labs allow users to learn and practice cybersecurity skills in a real-world environment. The platform covers a wide range of cybersecurity topics, including application security, cloud security, incident response, and offensive security.

Thoropass (formerly Laika)
Thoropass, formerly known as Laika, is an emerging compliance technology company based in New York City. The company specializes in providing end-to-end compliance solutions, streamlining processes, and reducing risks to help businesses navigate the complex regulatory landscape. Thoropass rebranded from Laika to reflect its evolving mission and expanded capabilities.
The company’s platform offers a range of tools and resources to help organizations identify and assess their compliance obligations, develop and implement compliance programs, automate compliance tasks, and monitor their compliance posture. Thoropass also provides professional services such as expert guidance, gap assessments, and audit preparation. The cloud-based platform is user-friendly and suitable for organizations of all sizes and technical expertise. Thoropass’s platform integrates with other popular security and compliance tools, making it easy to integrate into existing security ecosystems.

NetSPI
Founded in 2001, NetSPI is more established than most in this article, but $410 million in funding a year ago raised this company’s profile anew. NetSPI offers penetration testing, attack surface management, and breach and attack simulation, thought a combination of services and solutions. NetSPI claims nine of the top 10 U.S. banks as customers, four of the top five cloud providers, and four of the five largest healthcare companies.

NordSecurity
NordSecurity was a well-known name before landing its first funding round last year, a $100 million investment that rocket the company’s valuation past the $1 billion “unicorn” status. Nord Security provides a variety of products and services such as NordLayer, NordVPN, NordPass, and NordLocker. The Netherlands-based company has carved out a niche for itself by offering a simplified VPN service that prioritizes customer privacy and security.
Open Raven
Open Raven is a cloud-native data discovery and classification platform that helps organizations discover all data and resources in their cloud environment, classify data assets by identifying personal, sensitive, and regulated data, and monitor and protect data using policies and alerts. The platform is designed to work at scale and can be used across multiple cloud providers. Open Raven uses various techniques to discover and classify data, such as pattern matching, machine learning, and data fingerprinting. Automated discovery and classification and continuous monitoring are standout features.
Salt Security
Silicon Valley-based Salt Security, established in 2016, offers API security software that detects and inventories all APIs, including shadow and zombie APIs, allowing businesses to identify and track them. It also performs API vulnerability evaluations, which involve scanning APIs for vulnerabilities such as broken authentication, injection flaws, and insecure direct object references.
In addition, the platform analyzes API traffic in real-time to detect and prevent attacks utilizing techniques such as anomaly detection, machine learning, and behavioral analysis. The platform also delivers thorough analytics and reporting on API traffic and security posture, allowing enterprises to spot patterns, track progress, and respond to problems.

SandboxAQ
SandboxAQ, founded in 2016, is positioned at the crossroads of AI and Quantum Technology. The Alphabet spin-out offers cryptographic vulnerability scanning and remediation to help enterprises and government organizations protect sensitive data, communications, and transactions from classical and quantum-based cybersecurity threats. The company’s Security Suite provides discovery and continuous inventory of vulnerable cryptography, encryption remediation and supervised enforcement.
Also read: SandboxAQ Open Sources Cryptography Management Tool for Post-Quantum Era
Saviynt
Saviynt offers a converged identity platform that manages user, device, and application identities across cloud and on-premises environments. Saviynt’s growth is driven by the increasing demand for identity and access management solutions, as organizations look for ways to federate identity management regardless of location or platform.

Socure
Socure offers identity verification and fraud detection solutions, using various data sources and machine learning algorithms to verify user identities and detect fraudulent transactions. The company is well-positioned, with a strong revenue stream and a high customer satisfaction rating.
Traceable AI
Traceable AI offers an API security platform that identifies APIs, evaluates API risk posture, stops API attacks, and provides deep analytics for threat hunting and forensic research. With an API Data Lake at the core of the platform, Traceable applies distributed tracing and machine learning models for API security across the development lifecycle. With visual depictions of API paths, Traceable offers insight into user and API behaviors to understand anomalies and block API attacks.

Vanta
Vanta, founded in 2019 by Christina Cacioppo and Brendan Schneider, offers a platform that automates security compliance for businesses of all sizes, including those requiring SOC 2, ISO 27001, and HIPAA compliance. The platform also provides tools to manage security risks and build a robust security posture. Vanta, valued at $1.6 billion, has over 5,000 customers, demonstrating strong traction for its compliance automation technology.

Versa Networks
Versa Networks is an upstart taking on well-established names in network security markets like firewalls and SD-WAN solutions that help businesses enhance their WAN connectivity while retaining security. And Versa has done well at that seemingly difficult challenge, with products that have scored well for both security and value. Their technology offers centralized visibility and control over network traffic, as well as the ability to enforce security policies throughout the whole network.
Read more: 34 Most Common Types of Network Security Solutions
Best Threat Detection Startups
| Startup | Est | Headquarters | Staff | Funding | Round |
|---|---|---|---|---|---|
| Anvilogic | 2019 | Palo Alto, CA | 71 | $39.4 | B |
| Cyble | 2019 | Alpharetta, GA | 123 | $38 | B |
| SenseOn | 2017 | London, UK | 85 | $26.4 | A |
| SnapAttack | 2021 | Columbia, MD | 28 | $8.0 | A |
| Stairwell | 2019 | Palo Alto, CA | 64 | $69.5 | B |
| Cyera | 2021 | San Mateo California, USA | 104 | $164.5 | B |

Anvilogic
Anvilogic’s namesake platform offers continuous assessment, detection automation, and hunt, triage, and response capabilities for security teams. Designed to automate SOC operations and reduce alert noise, Anvilogic is a no-code, user-friendly solution with out-of-the-box policies aligned to the MITRE ATT&CK framework.

Cyble
Powered by machine learning and human analytics, Cyble is a threat intelligence startup offering solutions for attack surface management, third-party risk scoring, and monitoring for brand reputation and dark web exposure. Cyble Vision can integrate with an existing SIEM or SOAR and provide incident response, threat analysis, and vulnerability management.
SenseOn
SenseOn is a cybersecurity startup with an “AI Triangulation” technology that emulates actual security analyst behavior for detection, investigation, and response. SenseOn products are available as a network appliance, lightweight endpoint agent, or cloud-hosted microservices, with an Enterprise solution for deployment across multiple global sites.

SnapAttack
SnapAttack is a threat hunting and detection startup recently spun out from Booz Allen’s DarkLabs incubator. SnapAttack seeks to empower clients with proactive threat intelligence, behavioral analytics, and attack emulation through a collaborative platform. Enterprise and service providers are currently available, with a free community subscription coming soon.

Stairwell
Stairwell is an advanced threat detection startup presenting its Inception platform for threat intelligence, SOC functionality, and incident response capabilities. Inception helps collect files across environments, analyze historical and real-time data, investigate abnormal behavior, and connect security systems through the Inception API.

Cyera
Cyera offers a data-centric security platform to protect organizations’ sensitive data from unauthorized access, use, and disclosure. The platform uses machine learning and artificial intelligence to identify and classify data, creating and enforcing security policies.
Also read: Top Endpoint Detection & Response (EDR) Solutions
Best DevOps and AppSec Startups
| Startup | Est | Headquarters | Staff | Funding | Round |
|---|---|---|---|---|---|
| Evervault | 2018 | Dublin, Ireland | 29 | $19.4 | A |
| GitGuardian | 2017 | Paris, France | 30 | $56.0 | B |
| Satori | 2019 | Tel Aviv, Israel | 78 | $25.3 | A |
| Ubiq Security | 2019 | San Diego, CA | 28 | $6.4 | Seed |
| Wabbi | 2018 | Boston, MA | 17 | $2.2 | Seed |

GitGuardian
GitGuardian is a developer favorite offering a secrets detection solution that scans source code to detect certificates, passwords, API keys, encryption keys, and more. Ranked as the top-downloaded security app on GitHub, GitGuardian’s products include solutions for internal repository monitoring and public repository monitoring for prompt remediation.
Evervault
Evervault is on a mission to make encrypting sensitive data seamless with its security toolkit for developers. The developer-friendly startup offers Relay to encrypt field-level data and codes to isolate and process code as needed. With robust encryption policies, Evervault can help reduce insurance premiums and offers PCI-DSS and HIPAA compliance automation.
Satori
Satori is a data access startup for monitoring, classifying, and controlling access to sensitive data. Satori’s platform creates a layer of protection and visibility between data users and data stores to guard against vulnerabilities related to transferring sensitive data. Ultimately, Satori aims to provide data access control, visibility into usage and traffic, and compliance fulfillment.

Ubiq Security
Ubiq Security offers an API-based platform that integrates data encryption directly into application development. Without the need for experienced developers, encryption expertise, or excessive manual hours, Ubiq Security makes securing applications during the development process seamless, allowing personnel to focus on what’s most important.
Wabbi
Wabbi offers a continuous security platform for managing vulnerabilities, application security policies, and release infrastructure. As rapid software development is the new norm, Wabbi aims to help organizations securely deliver software to clients and achieve continuous authority-to-operate (ATO).
Also read: Top Code Debugging and Code Security Tools
Best Cloud Security Startups
| Startup | Est | Headquarters | Staff | Funding | Round |
|---|---|---|---|---|---|
| Araali Networks | 2018 | Fremont, CA | 15 | – | Seed |
| DoControl | 2020 | New York, NY | 65 | $43.4 | B |
| Grip Security | 2021 | Tel Aviv, Israel | 63 | $66.0 | B |
| Isovalent | 2017 | Mountain View, CA | 81 | $29.0 | A |
| Mitiga | 2019 | Tel Aviv, Israel | 96 | $45.0 | A |
| Privafy | 2019 | Burlington, MA | 84 | $22.0 | Venture |
| Strata.io | 2019 | Boulder, CO | 45 | $42.0 | B |
| Valence Security | 2021 | Tel Aviv, Israel | 40 | $32.0 | A |
Araali Networks
To secure cloud-native workloads, Araali Networks offers identity-based threat management to prevent malicious communications and data leaks. With a trio of products, customers can choose from Lens for visibility into cloud infrastructure, Sense for actionable alerts and risk prioritization, and Shield for protecting vulnerable applications.

DoControl
DoControl is a startup specializing in SaaS data access control with a platform offering cloud asset management, automated security workflows, and continuous cloud infrastructure monitoring. As organizations increasingly rely on SaaS applications for data storage and transfer, DoControl helps guard against unauthorized access of sensitive data.

Grip Security
Grip Security boasts a solution that beats traditional cloud access security brokers (CASB), providing clients with a complete SaaS inventory upon deployment for visibility, governance, and data security. No matter the device or location, Grip’s solution helps enhance and automate security policy enforcement across an organization’s cloud infrastructure.
Isovalent
Isovalent’s flagship product, Cilium, is powered by the open-source eBPF kernel technology and offers infrastructure services for networking, monitoring, and security for organizations. Isovalent’s solutions were designed with scale in mind to secure mission-critical and complex workloads in cloud environments, including Kubernetes.
Mitiga
To accelerate investigation, response, and time to recovery, Mitiga is the cloud incident response company offering emergency IR, ransomware readiness, and incident readiness and response. By capturing and processing cloud forensic data, Mitiga’s IR experts can help clients proactively manage vulnerabilities and breaches from a central crisis management dashboard.

Privafy
Privafy aims to serve a valuable corner of the market – securing data in motion. As up to 80 percent of data breaches occur while data moves between cloud networks, Privafy offers security for cloud infrastructure as well as a list of edge computing solutions to securely deploy IoT devices and edge networks in the years to come.
Strata Identity
Strata Identity offers an identity orchestration solution, the Maverics Platform, which aims to solve enterprise organizations’ complex identity and access management (IAM) problems. By integrating identity systems across the modern infrastructure, organizations can easily create and replicate orchestrations for apps.

Valence Security
Valence Security’s focus is the third-party integration risks presented by a universe of cloud applications used for business workflows. With the rise of the SaaS to SaaS supply chain, as Valence calls it, organizations need visibility into application interactions. Through its platform, Valence brings workflows, permission scopes, API keys, and OAuth access tokens to light.
Also read: Best Cloud Native Application Protection Platforms (CNAPP)
Best Cyber Asset and Attack Surface Management Startups
| Startup | Est | Headquarters | Staff | Funding | Round |
|---|---|---|---|---|---|
| Horizon3 | 2019 | San Francisco, CA | 106 | $78.5 | C |
| JupiterOne | 2018 | Morrisville, NC | 159 | $119.0 | C |
| Noetic Cyber | 2020 | Waltham, MA | 50 | $15.0 | A |
| Sevco Security | 2020 | Austin, TX | 45 | $21.7 | A |
| SpiderSilk | 2019 | Dubai, UAE | 39 | $2.8 | Seed |

Horizon3.Ai
Horizon3.ai presents its solution, the NodeZero, as Autonomous Penetration Testing as a Service (APTaaS) for identifying an organization’s potential attack vectors. Whether on-premises, cloud, IoT, internal, or external attack surfaces, NodeZero can identify vulnerable controls, maximize security infrastructure, and leverage the latest threat intelligence.
JupiterOne
JupiterOne is a cyber asset management startup providing clients with a cloud-native solution for insights into relationships, governance and compliance, and empowering security engineering. JupiterOne helps aggregate cyber assets for central visibility and faster investigations with increasing complexity in security operations and assurance.

Noetic Cyber
Noetic Cyber offers a continuous cyber asset management and controls platform to give clients a comprehensive view of systems, policies, and the relationship between entities. Real-time visibility means organizations can identify and act on misconfigurations and coverage gaps and maximize existing infrastructure with a proactive remediation strategy.
Sevco Security
Sevco Security is a cloud-native cyber asset and attack surface management platform offering a real-time inventory of assets, multi-source correlation, and asset telemetry to support incident response workflows. With robust visualizations of network devices and traffic, Sevco’s agentless asset intelligence platform gives network administrators the visibility to identify and remediate coverage gaps.

SpiderSilk
SpiderSilk offers an impressive proprietary internet scanner that maps out a company’s assets and network attack surface to detect vulnerabilities. Over the years, SpiderSilk’s research has informed several high-profile breaches, and for clients, the vendor can simulate cyberattacks to ensure organizations take preventive measures before the real thing.
See the Top Breach and Attack Simulation (BAS) platforms
Best Identity & Access Management Startups
| Startup | Est | Headquarters | Staff | Funding | Round |
|---|---|---|---|---|---|
| Authomize | 2020 | Tel Aviv, Israel | 70 | $22.0 | A |
| Cerby | 2020 | San Francisco, CA | 53 | $32.5 | A |
| Deduce | 2019 | New York, NY | 35 | $17.3 | Seed |
| SafeBase | 2020 | San Francisco, CA | 33 | $18M | A |
| Securden | 2018 | Delaware, OH | 62 | $11.7 | A |
| Truora | 2018 | Cali, Colombia | 147 | $18.7 | A |
Authomize
Authomize is the cloud identity and access security platform designed to map all identities and assets across XaaS environments. Putting observability first, Authomize continuously monitors security policies to identify exposed assets, entitlement escalation paths, and hidden and unmonitored permissions. Authomize utilizes an AI-based engine to manage and automate remediation for clients’ Authorization Security Lifecycle.
Cerby
Cerby is on a mission to wrangle unmanageable applications, otherwise known as shadow IT — or the universe of apps employees use without permission from the IT department. Through application APIs and robotic process automation (RPA), Cerby helps automate access corresponding to managed identity platforms like Okta and Azure AD while monitoring for application misconfigurations that violate security policies.

Deduce
Deduce is an identity-focused cybersecurity startup with two core solutions: Customer Alerts for protecting users and their data from account takeover and compromise, and Identity Insights for validating legitimate users and stopping fraud. Deduce offers actionable identity intelligence through event-level telemetry to act against abnormal user activity.
SafeBase
SafeBase is a trust-focused security platform streamlining the third-party risk management process between companies. Through the Smart Trust Center, companies can quickly share their private documents, compliance policies, risk profile, and product security details. SafeBase’s stack of features covers enterprise authentication, role-based access, security questionnaires, and auto-populated NDA templates.
Securden
Securden is a privileged access governance upstart offering companies password management, privilege management for endpoints and servers, secure remote access, and endpoint application control. Designed for least privilege and zero trust security architectures, Securden specializes in privilege management for Windows-centric organizations and data centers.
Truora
A leading startup hailing from Latin America, Truora offers a stack of solutions to simplify and secure user interactions. On top of solutions for chatbots, electronic signatures, and employee background checks, Digital Identity by Truora helps organizations quickly and safely verify online identities by validating documents, email, and phone, facial recognition, and more.
See the Best Zero Trust Security Solutions
Best Remote Access Security Startups
| Startup | Est | Headquarters | Staff | Funding | Round |
|---|---|---|---|---|---|
| BastionZero | 2019 | Boston, MA | 22 | $6.0 | Seed |
| Tailscale | 2019 | Toronto, Ontario | 54 | $115.0 | B |
| Talon Cyber Security | 2021 | Tel Aviv, Israel | 99 | $143.0 | A |
| Twingate | 2019 | Redwood City, CA | 76 | $59.0 | B |

BastionZero
BastionZero is the Infrastructure Access as a Service company helping organizations configure, manage, and secure access controls to hybrid infrastructure targets. Through a central cloud console, engineers can authenticate and access all servers, containers, clusters, and databases. Designed to remove the hassle of VPNs, BastionZero offers passwordless access, identity-aware logging, SSO, and MFA.
Tailscale
Building off the open source WireGuard protocol, Tailscale is a VPN service that utilizes a peer-to-peer mesh network, or “tailnet,” and removes the central gateway server for network traffic. Tailscale allows companies to integrate existing SSO and MFA solutions, define role-based access controls for sensitive targets, and ensure network traffic meets compliance policies through log audits.

Talon Cyber Security
As organizations increasingly adopt remote personnel, Talon Cyber Security addresses web and browser-based threats with a secure, corporate browser. Based on Chromium OS, Talon’s browser-centric security solution aligns with its larger strategy to protect the distributed workforce and enable secure access to hybrid infrastructure. Talon may soon join our “graduated” section at the bottom of this article, as Palo Alto Networks is reportedly in talks to acquire the company.

Twingate
In the race to replace traditional VPNs, Twingate offers a secure zero-trust network access (ZTNA) for computers, servers, and cloud instances. Twingate allows network administrators to map resources, approve users for resources, and connect to any device from anywhere. Easy to integrate into existing infrastructure, Twingate includes identity-indexed analytics, universal MFA, and built-in split tunneling.
Best Compliance & Governance Startups
| Startup | Est | Headquarters | Staff | Funding | Round |
|---|---|---|---|---|---|
| Dasera | 2019 | Mountain View, CA | 30 | $9.0 | Seed |
| Ethyca | 2018 | New York, NY | 39 | $27.5 | A |
| Strike Graph | 2020 | Seattle, WA | 52 | $18.9 | A |
| Unit21 | 2018 | San Francisco, CA | 159 | $47.0 | B |

Dasera
Dasera is the data governance platform offering continuous policy enforcement, automated audits, and access to more data to inform decision-making. Monitoring for misconfigurations, cloud data stores, and change management across hybrid infrastructure, Dasera reduces manual workloads and ensures security while sharing data with necessary stakeholders.
Ethyca
Ethyca is compliance-focused as regulatory enforcement becomes an essential part of data privacy. With Ethyca, clients get a bundle of tools for privacy by design in the development process. Ethyca can automate compliance tasks, including real-time data mapping, automated subject requests, consent management, and subject erasure handling.

Strike Graph
Strike Graph is a cybersecurity compliance startup helping companies meet a long list of security frameworks, including SOC 2, ISO 27001 and 27701, HIPAA, GDPR, CCPA, and PCI DSS. From certification readiness to dedicated Audit Success Managers, Strike Graph can help companies automate evidence collection, streamline security questionnaires, and challenge vulnerabilities through penetration testing.
Unit21
Boasting a simple-to-use API and dashboard, Unit21 is a hot startup for enterprise organizations looking to mitigate fraud and money laundering risks without needing extensive engineering personnel. Unit21 is a no-code platform with operations and case management solutions, transaction monitoring, identity verification, and analytics and reporting for compliance.
See the Top Governance, Risk & Compliance (GRC) Tools
Other Top Cybersecurity Startups
| Startup | Est | Headquarters | Staff | Funding | Funding Type |
|---|---|---|---|---|---|
| BreachQuest | 2021 | Dallas, TX | 30 | $4.4 | Seed |
| Cape Privacy | 2018 | New York, NY | 30 | $25.0 | A |
| Cowbell Cyber | 2019 | Pleasanton, CA | 246 | $123.3 | B |
| Havoc Shield | 2019 | Chicago, IL | 13 | $5.2 | Unknown |
| Hook Security | 2019 | Greenville, SC | 16 | $7.1 | A |
| Nucleus Security | 2018 | Sarasota, FL | 66 | $23.1 | B |
| Shift5 | 2019 | Arlington, VA | 89 | $72.5 | B |
| SolCyber | 2017 | Dallas, TX | 24 | $20.0 | A |
| Torq | 2020 | Portland, OR | 112 | $78M | B |
BreachQuest
BreachQuest is a digital forensics and incident response (DFIR) startup preparing to launch its Priori Platform for active continuous monitoring, detection, and recovery capabilities. With plenty of cybersecurity experience at the helm — including NSA, DoD, and U.S. Cyber Command — BreachQuest has client preparedness for attacks top of mind.
Cape Privacy
Cape Privacy addresses secure communication between organizations by building machine learning models on encrypted data. Currently ideal for industries like financial services managing sensitive data, Cape Privacy’s Snowflake is an innovative multi-party computation (MPC) platform that prevents single points of failure and ensures compliance.
Cowbell Cyber
Cowbell Cyber is a dedicated cyber insurance company that relies on continuous risk assessment, AI data analytics, and real-time underwriting to give clients pre- and post-breach services. The risk management startup offers visibility into exposures dubbed Cowbell Factors, giving clients opportunities for potential remediation and better coverage.
Havoc Shield
Designed for small businesses, Havoc Shield offers clients a suite of cybersecurity tools to manage cybersecurity programs with confidence. In a single bundle, Havoc Shield’s stack covers asset inventory, vulnerability management, endpoint protection, patch management, email security, cyber awareness training, and vendor risk management.
Hook Security
The eponymous Hook Security specializes in phishing testing and security awareness training to transform workforce culture surrounding cybersecurity. Available as a managed service or self-managed solution, Hook Security’s solutions include a customizable phishing simulator, learning management system, reporting, and a catalog of available awareness training content.

Nucleus Security
Nucleus Security is a risk-based vulnerability management platform offering risk scoring and reporting, asset management, and vulnerability intelligence. Sitting at the intersection of threat intelligence, asset management, and vulnerability scanning data, Nucleus offers a central hub with over 100 security integrations to optimize visibility into cybersecurity coverage gaps.

Shift5
In the vendor’s own words: “We protect planes, trains, and tanks from cyber attacks.” Specializing in cybersecurity solutions for operational technology (OT), Shift5 offers protection for the world’s transportation infrastructure and weapons systems. Shift5 continuously monitors data intake from hardware and software to visualize critical insights, detect anomalies, and prevent intrusions.
SolCyber
SolCyber is the newest managed security service provider (MSSP) on the block to reduce cyber risk, wastage, and complexity. Led by a C-suite with solid industry and technical experience, SolCyber currently offers foundational and extended coverage to meet varying needs in building out cybersecurity systems and adequate SOC capabilities.

Torq
Torq is the no-code security automation platform for building and integrating workflows between cybersecurity systems. With a long and impressive list of potential use cases, teams can utilize Torq to automate security workflows related to cloud security posture management, email phishing response, application security, data security, and more. For example, companies with existing EDR, XDR, and SIEM systems can automate threat hunting workflows with Torq.
Also read: Choosing a Managed Security Service: MDR, Firewalls & SIEM
Investor Considerations for Cybersecurity Startups
Potential To Scale, Lean R&D
Scalability will always be one of the most critical factors for investing in a successful startup. When there are growth opportunities, startups should and usually do capitalize on them.
Investors are also looking for startups that can continue to improve their products without the need for substantial capital investment. Lean research and development (R&D) show efficiency, even with limited resources. Investors can evaluate how the product and business model evolve before investing more capital. This fact makes any startup’s quality of personnel and leadership a critical factor in the organization’s success.
A Solid Business Plan
Another factor investors have always looked for is an air-tight business plan. They want assurance that there is a marketable problem that the product solves. Investors also want to see financial reports and revenue growth projections backed up by market analysis.
Compliance Mindset
Regulatory compliance, such as HIPAA, GDPR, and CCPA, is essential for organizations collecting and protecting user information, including virtually all enterprise-level companies. Investors will be looking for startups that can ensure customers will maintain compliance.
Remote Work Experts
Remote work is and will continue to be, for the foreseeable future, a top-of-mind factor for venture capitalists. Even with vaccines, a largely remote workforce is likely here to stay.
Startups that can immediately impact the remote worker ecosystem will garner much attention. Specifically, startups with SaaS (software-as-a-service), those that provide automation, and products that include endpoint protection will fall into this category.
Cybersecurity Startup Trends
As organizations, clients, and end-users increasingly rely on cyberinfrastructure, the need to protect these systems will only deepen.
Given the relative newness of IT industries at large, cybersecurity remains a budding marketplace with plenty of opportunities for new vendors. Some of the best cybersecurity companies are longtime technology stalwarts. Still, many have proven the right solution and service can catch on fast with eager investors ready to help worthy startups scale. While new buzzwords like AI and post-quantum abound, even the newest cybersecurity solutions tend toward familiar product categories.
Most Popular Cybersecurity Startup Solutions In 2023
- Application Security
- Attack Surface Management
- Cloud Security
- Cyber Asset Management
- Digital Forensics and Incident Response
- Identity and Access Management
- Governance, Risk, and Compliance
- Risk Scoring and Assessments
- Software Development Lifecycle (SDLC)
- Threat Detection (EDR, XDR)
Endpoint Security And Protection Against Ransomware
Endpoint security, including traditional endpoint detection and response (EDR) and increasingly, its advanced iteration, extended detection and response (XDR), continue to be in high demand in light of the boom in remote work.
Products like EPP, EDR and XDR solutions secure the devices spanning a remote ecosystem and will continue to be invaluable. The healthcare segment alone saw significant investment in cybersecurity due to the adoption of telehealth and teleworking models.
Most Popular Headquarters For Cybersecurity Startups
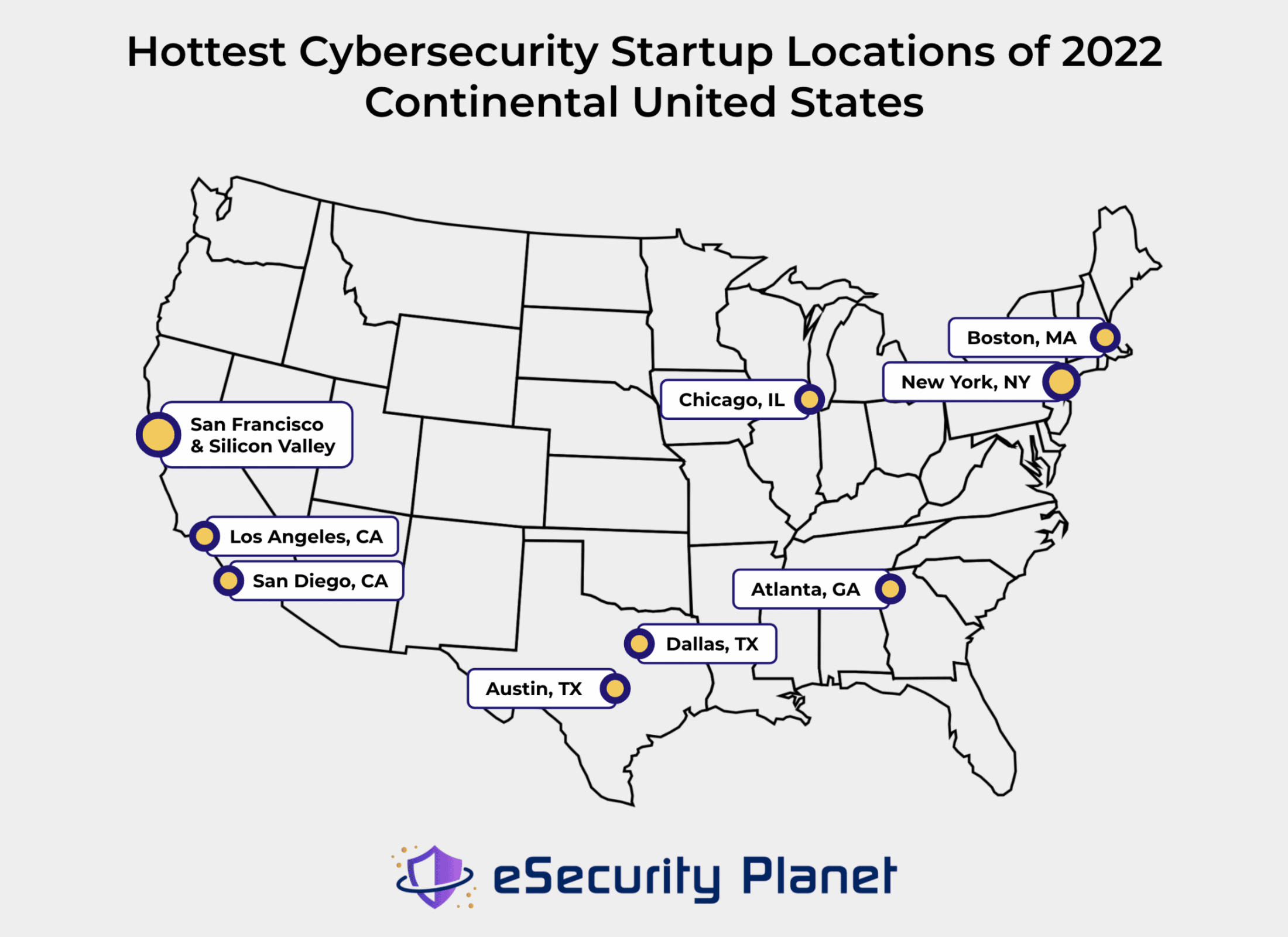
The United States, Israel, Canada, and the United Kingdom continue to be popular national locations for cybersecurity startups, with most of the funding directed between the first two.
Within the United States, the San Francisco Bay Area remains the hottest region for startups. The second-largest contingent of cybersecurity startups is a continent away from Palo Alto, in New York City. The industry newcomers benefit from the proximity to partnerships, skilled IT personnel, and funding opportunities.
Though it’s hard to compare to the presence of San Francisco and New York, other U.S. cities holding multiple top contenders this year include:
- Atlanta, GA
- Austin, TX
- Boston, MA
- Chicago, IL
- Dallas, TX
- Los Angeles, CA
- San Diego, CA
Top Startup Selection Criteria
For this list we’ve generally favored companies that have been around for 5 years or less and are still in their first few rounds of funding, although older companies receiving renewed investor interest have also made this list. Sources include our observations and analysis of the cybersecurity market and startup databases such as Growjo and Crunchbase.
Our top startups are independent companies with innovative cybersecurity products or services, with a viable business plan with evidence of scalability.
We look for evidence of solid growth and traction, but once companies become too big to be called “startups” anymore — more than $100 million in revenue has been one criteria for “graduation” — we move them to our “graduated” list below.
Graduated Startups
Several security companies making previous eSecurity Planet top startup lists continue to be prominent vendors heading into 2023, whether as well-funded growing companies or the newest acquired team for other top IT service providers. These companies include:
| Startup | Founded | Headquarters | Staff | Funding | Stage |
|---|---|---|---|---|---|
| Abnormal Security | 2018 | San Francisco, CA | 492 | $284.0 | C |
| Axis Security | 2018 | San Mateo, CA | 140 | $99.5 | Series C |
| BluBracket | 2019 | Palo Alto, CA | 30 | $19 | Acquired by HashiCorp |
| Bitglass | 2013 | Campbell, CA | 70 | $150.1 | Acquired by Forcepoint |
| Cato Networks | 2015 | Tel Aviv, Israel | 532 | $596.0 | Venture |
| Confluera | 2018 | Palo Alto, CA | 49 | $29 | Acquired by XM Cyber |
| Cybereason | 2012 | Boston, MA | 1,308 | $750.6 | Series F |
| Darktrace | 2013 | Cambridge, UK | 2,208 | $230.5 | IPO: “DARK” on LSE |
| Ermetic | 2019 | Palo Alto, CA | 171 | $97.3 | Acquired by Tenable |
| Illumio | 2013 | Sunnyvale, CA | 578 | $557.5 | Series F |
| Immuta | 2015 | Boston, MA | 269 | $158.2 | Series D |
| JupiterOne | 2018 | Morrisville, NC | 159 | $119.0 | Series C |
| Lightspin | 2020 | Tel Aviv, Israel | 81 | $20.0 | Acquired by Cisco |
| Neosec | 2021 | Palo Alto, CA | 59 | $20.7 | Acquired by Akamai |
| OneTrust | 2016 | Atlanta, GA | 3,340 | $926.4 | Series C |
| Orca Security | 2019 | Los Angeles, CA | 405 | $632.0 | Series C |
| Perimeter 81 | 2018 | Tel Aviv, Israel | 238 | $165.0 | Acquired by Check Point |
| Randori | 2018 | Waltham, MA | 87 | $29.8 | Acquired by IBM |
| SECURITI.ai | 2018 | Santa Clara, CA | 413 | $155.0 | C |
| SentinelOne | 2013 | Mountain View, CA | 1,676 | $696.5 | IPO: “S” on NYSE |
| Snyk | 2015 | Boston, MA | 1,294 | $849.5 | G |
| Sysdig | 2013 | San Francisco | 926 | $744 | G |
| Tanium | 2007 | Kirkland, WA | 2,060 | $1,171 | Round 16 |
| Vdoo | 2017 | Tel Aviv, Israel | 31 | $70.0 | Acquired by JFrog |
| Wiz | 2020 | Tel Aviv, Israel | 470 | $900.0 | D |
Bottom Line: Cybersecurity Startups
Despite the economic headwinds and tighter venture capital funding environment in the last year or two, there’s still demand for innovative startups that can help solve some of the pressing cybersecurity problems confronting organizations today.
Those headwinds will likely continue a while longer, but startups with a promising future that can conserve cash will be well prepared for the eventual rebound.
Next: See the Top Network Security Companies and the Top Cloud Security Companies
This article was first published in 2019 and most recently updated on Sept. 25, 2023. Includes additional research by Sam Ingalls and Paul Shread.










