Anyone who has used a computer for any significant length of time has probably at least heard of malware. Short for “malicious software,” malware is any piece of computer software designed to disrupt the regular function of a network or device, to gain unauthorized access to certain hardware or systems, or to send user data to others without that user’s consent.
Malware has been present in the digital space since the 1980s, with early prank malware like the Morris Worm or the (c)Brain. However, malware is not quite as amusing in a modern context. From ransomware attacks locking businesses out of their data until they pay potentially millions of dollars to spyware tracking users’ every move through their infected device, the effects of malware can be devastating.
Today, malware is a common network threat to the devices and data of anyone who uses the Internet. Since 2008, antivirus and cybersecurity software testers AV-TEST have kept track of the number of newly-developed malware worldwide, totaling at nearly 1 billion as of September 2022. An August 2022 Statista report counted 2.8 billion malware attacks worldwide in the first half of 2022 alone.
With so many attacks and unique types of malware out there, it’s important to have some idea of how malware works, how it can infect your devices, and what to do if you find yourself infected with it.
If you’ve been hit by malware and are looking for help, see How to Remove Malware: Removal Steps for Windows & Mac.
Table of Contents
How Does Malware Work?
Malware’s functions vary wildly depending on what type of malware you’re dealing with. Broadly, malware will somehow be injected into a device or network and, if it can gain access to the files or systems it needs to, it will begin its work.
For example, once it infects your device, a keylogger will start tracking every keystroke you make and sending a log of those keystrokes to the hacker, allowing them to reconstruct any sensitive information you might have entered after infection, such as your PIN, password, or social security number.
To better understand how malware works, however, let’s look at some common types of malware and see how they function and what parts of a device or network they usually affect. After that, we’ll offer some techniques and tips to help you prevent malware infection but also what to do if you end up infected.
Want to Learn More About Malware? Check Out The History of Computer Viruses & Malware
Common Types of Malware
Adware
Easily one of the most frustrating types of malware, adware is software designed to harass users with a torrent of unwanted or malicious ads. Adware is often smuggled onto a device, either by users who don’t know what they’re downloading or by hiding it in an otherwise innocuous piece of software like a search engine toolbar plugin for your browser.
This isn’t quite the same as a legitimate piece of software, such as a mobile game from a reputable developer, coming packed with online ads. Usually, those ads will be screened by the developer or whoever published the software online and don’t do anything unusual beyond wasting your time. Adware advertisements might appear in places where ads typically don’t show up; might be completely unrelated to the software or website you’re using, including the depiction of explicit material; and might even begin performing a number of unwanted tasks on your device.
These unwanted tasks can include:
- opening new tabs on your browser without you clicking on anything
- website links redirecting to completely different websites from what you expect
- fully crashing your browser.
Some signs of adware infection include:
- Your browser is noticeably slower than usual
- NSFW ads on otherwise SFW websites
- New toolbars, plugins, or extensions appearing on your web browser without you installing them
- Your browser’s homepage changing without your permission
Ransomware
One of the most dangerous kinds of malware for businesses, ransomware can slip into a network or device and encrypt sensitive files or lock down the entire device unless the victims pay the hacker a usually-sizable fee to unlock it – and even then, decryption fails most of the time. Modern ransomware hackers often double or triple up on the extortion by demanding additional fees to ensure that sensitive files are not leaked to the public.
Ransomware is one of the most virulent forms of malware on the modern Internet. A report from IBM claims that 21% of all cyber attacks the company remediated in 2021 were ransomware, making it the most common type of attack in the report. The method of infection can vary from attack to attack and can include social engineering strategies, such as phishing and email spoofing, or a fraudulent website masquerading as legitimate, among others.
Once a system is infected, ransomware attacks usually come in 3 stages:
- Surveillance: The hackers scan their target for more information on the system they are attacking. In particular, they’ll look for sensitive files which can be used for potential double-extortion attempts or additional access credentials with which to spread the ransomware across more devices.
- Activation: The ransomware begins encrypting sensitive files or locking down the system. In the former case, an attacker will utilize a process called asymmetric encryption to lock down these files, encrypting with a public key but keeping a private key for decryption. This means the files can’t be restored without the attacker’s help. To apply more pressure, the attacker might also encrypt backup files to render them inaccessible. In the latter case, the ransomware will freeze the device’s screen or apply so many pop-ups to the device that it’s rendered unusable.
- The Ransom Note: The ransomware notifies its victims of the infection via a .txt file on the infected device or a pop-up. This note will provide instructions on how to pay the ransom, usually through difficult-to-trace means like cryptocurrency.
If You Need to Learn More About How to Keep Your Data Safe, Take a Look at Ransomware Prevention: How to Protect Against Ransomware
Rootkits
Rootkits are essentially software toolboxes which allow hackers to infiltrate a device’s systems and gain remote control of it. This makes them incredibly difficult to detect and remove, though there are tools like rootkit scanners which can help.
Typically, attackers will use rootkits to spy on users and launch cyber assaults, such as a distributed denial of service (DDoS) attack, but the aforementioned software toolbox contains a variety of malicious implements. This can include programs with which the hacker can disable security software, install keyloggers, or steal sensitive information like passwords or credit card details.
There are a few viable ways to install a rootkit, but they will typically target some weakness in either an application installed on the target device or the target device’s operating system (OS). There are also several different types of rootkits to be aware of:
- Application Rootkits: Application rootkits replace a device’s files, altering common applications like Notepad. Whenever a user uses the infected file, it gives the attacker access to their computer.
- Bootkits: This type of rootkit targets a computer’s bootloader, the software responsible for loading the computer’s OS into RAM upon startup. Bootloaders are usually launched by a disc, USB drive, or hard drive, which tells the computer where its bootloader program is. Bootkits replace the legitimate bootloader with an infected version. This type of rootkit is especially difficult to detect and drive out, since it won’t typically show up in a user’s file system. Additionally, removal might further damage the computer if the bootkit has altered the device’s boot records.
- Firmware Rootkits: Firmware rootkits are usually used to infect a device’s hard drive or basic input/output system (BIOS), but they can be used to infect routers or intercept data written on hard discs as well. Firmware rootkits are also known as “hardware rootkits.”
- Kernel Mode Rootkits: One of the most complicated forms of rootkit, kernel mode rootkits target the core components of a device’s operating system, called a kernel. They often evade detection by operating at the same security level as the operating system itself, making them capable of especially devastating cyber attacks. However, kernel mode rootkits also require a high degree of technical competency, as any bugs or glitches within the rootkit can leave an easy trail for antivirus software to sniff out.
- Memory Rootkits: The final type of rootkit we’re covering will camouflage itself within a computer’s random-access memory (RAM). While there, they can inflict significant damage while also severely hampering a device’s performance by consuming massive amounts of RAM resources with whatever programs they have running. Memory rootkits are also often the shortest-lived type of rootkit, with most being erased when a computer reboots.
Need More Intel on Rootkits? Check Out Top 6 Rootkit Threats and How to Protect Yourself
Spyware
As the name implies, spyware hides on your devices in order to monitor and transmit your data to the hacker or hackers who deployed it. This information can range from what websites you visit to your download history to your bank PIN. This software can function similarly to Facebook or Google’s targeted ad technology which can track which websites you visit and provide ads based on that history, such as getting ads for cribs after looking up baby names.
There are innumerable methods of infiltration for spyware, from social engineering tactics to malicious software concealed in software bundles to exploiting security vulnerabilities in your device’s hardware or software. It’s one of the most infectious forms of malware out there.
Types of spyware are often classified based on what information they’re gathering. Keyloggers track your device’s keystrokes, password stealers’ function is in the name, and infostealers attempt to snatch a variety of sensitive information from its victims.
Trojans
Named for the Trojan Horse from Homer’s Odyssey and Virgil’s Aeneid, trojans function similarly to their mythological namesake by convincing users to install it on their device via social engineering schemes. This can come in the form of downloading free programs such as a game or a screensaver, visiting questionable video-hosting websites, or opening an attachment infected with the trojan.
Since its name more describes how it gets into a system than what it does there, trojans cover a broad range of malware:
- Spyware can often be injected into a device as a trojan.
- Once downloaded, a computer worm can automatically spread itself across connected devices, such as via the Internet or via local area network (LAN) to devastating effect.
- Remote access trojans (RATs) can provide hackers with backdoors into the infected device and allows hackers to control target computers via a remote network connection.
- Downloader Trojans can be used to download other forms of malware onto a device.
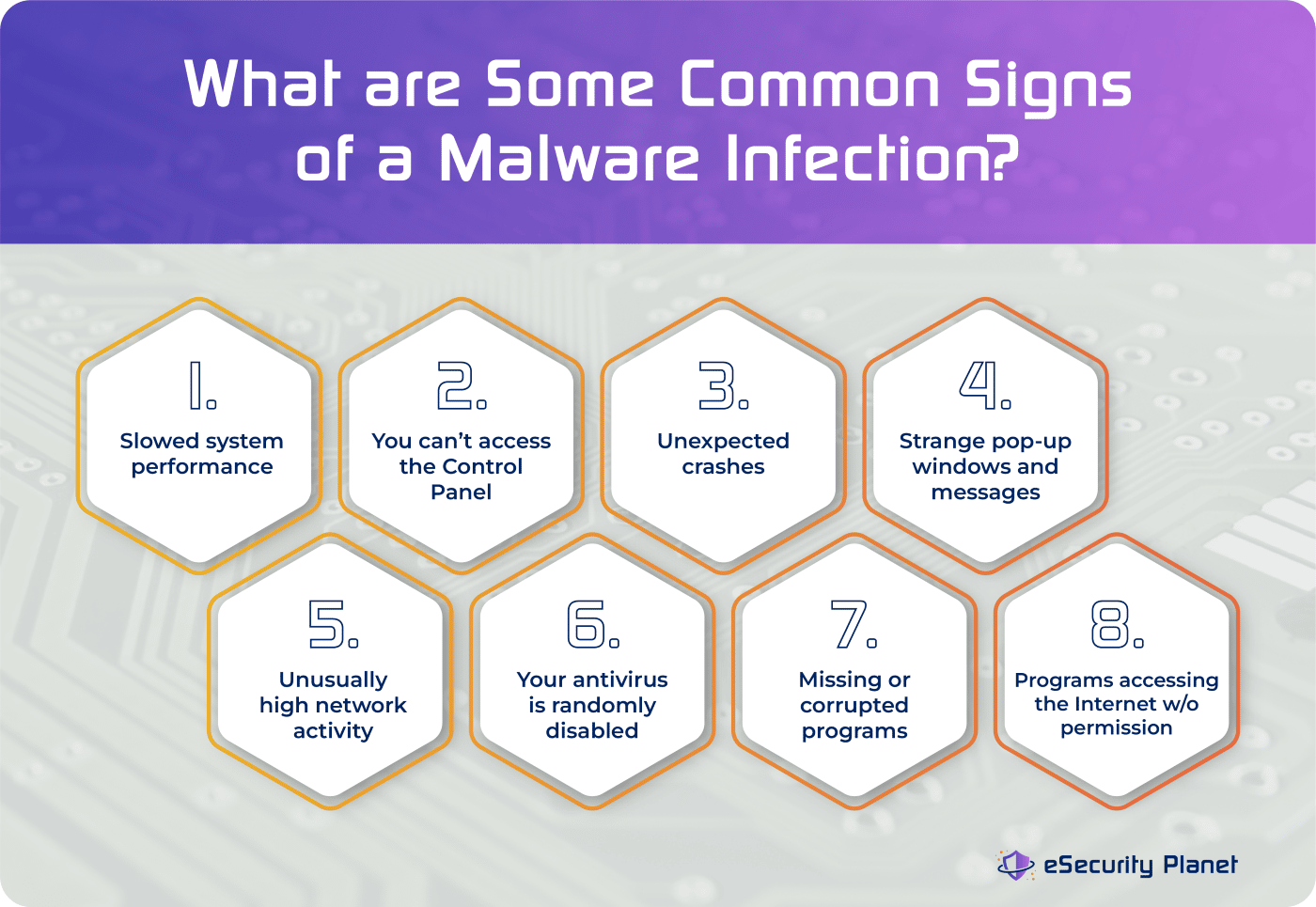
8 Common Signs of Malware Infection
While malware comes in a variety of different shapes and sizes, there are some factors which many of the various types can all share. The infographic below isn’t a comprehensive list, and even if your computer hasn’t shown any of these signs, there’s still a chance malware has infiltrated your machine.
Need to Know More About How Malware Can Infect Your Device? Take a Look at 8 Ways Malware Creeps Onto Your Device
Ways to Protect Your Network Against Malware
Thankfully, as scary as malware can be, individuals and businesses have ways to protect themselves against malware.
Both businesses and users alike can benefit from having good antivirus software onhand to detect and remove potential threats. Though, as digital rights group Electronic Frontier Foundation notes, “antivirus software is usually ineffective against targeted attacks.” While it’s still good to have antivirus software to deal with untargeted attacks (such as the links on a malicious website), ransomware and similarly-focused assaults will need additional protections.
An important piece of advice is to maintain a robust series of backups for all your important files and data, usually multiple backups using several different storage methods if possible. An offline storage solution, such as a hard drive or USB drive, is especially helpful, though not necessarily feasible if your business handles enough data to require, say, its own cloud storage solution. Still, maintaining and regularly updating your backups will help blunt a lot of the damage malware typically inflicts on its victims. And immutable backups are a particularly important ransomware protection.
Businesses can implement strategies like a zero-trust framework to help keep themselves safe, as well as adopt more sophisticated security solutions than individual users typically have access to. Examples include Intrusion Detection and Prevention (IDPS) tools to block potentially-malicious network traffic, network access control (NAC) to help maintain network safety with more and more employees working remote, and increasingly-vital next-generation firewalls (NGFW) for defending your data and applications from attack.
Finally, one of the simplest yet most effective tools for keeping yourself and your network safe against malware is personal vigilance. Avoid opening email attachments from accounts you don’t recognize, stay away from shady websites, make sure your passwords are secure and difficult to crack, and don’t download anything from sources you don’t absolutely trust. Indeed, malware can often be avoided by simply not clicking on infected links or files, making employee security awareness training one of the most critical defenses of all.
How to Identify and Remove Existing Malware
If you know your device or network is plagued with malware, there are a few steps you can take to get rid of it before it can do more damage.
- Disconnect from the Internet: Disconnecting can help prevent the malware from sending your data to the hacker who deployed it or from spreading to other devices on the network. If you must download a tool or software to begin removing the malware, disconnect as soon as it has finished downloading. Only reconnect once you’re sure the issue has been dealt with.
- Antivirus Scanning: A good antivirus or malware-scanning software will usually have programs in place to remove detected instances of malware, but that can’t always be relied upon to fix the problem.
- Reboot: If your software solution proves ineffective, the next step is usually restarting or rebooting your machine. It can be good to boot in Safe Mode. Some types of malware, such as memory rootkits, will disappear once your system reboots. How an OS enters safe mode differs between each system, but instructions can usually be found online, such as Microsoft’s instructions for Windows 10.
- System Recovery: If a restart fails to solve the problem, a full system recovery or reinstallation might be necessary to fully rid yourself of malware’s grip on your device. However, this can usually result in significant data loss, which is why maintaining backups for important data is so critical.
Bottom Line
Ultimately, no foolproof solution has yet been found for preventing cyber attacks, beyond disconnecting from the Internet and living up in the mountains away from civilization, but knowing more about malware, how it works, and how to get rid of it can be a big help in keeping your device and data safe.
Want to Learn More About Keeping Your Network Safe from Malware? Check Out How to Prevent Different Types of Malware





