Open-source penetration testing tools are freely available software that help pentest teams identify areas of weakness in their systems.
Teams often need a variety of tools to perform a full penetration test, so using the wide range of open-source pentesting tools helps them keep their costs down. And many pentesters are already familiar with well known tools like Nmap and Metasploit.
Many of the tools below are included in Kali Linux, a dedicated Linux operating system for pentesting and ethical hacking. Installing Kali can remove the hassle of downloading and installing these tools separately.
The emphasis here is on open-source pentesting tools, so pricing is free but we note where there are paid levels and services too. For commercial pentest tools offering greater breadth and support, see Best Penetration Testing Tools.
Also read:
- What Is Penetration Testing? Complete Guide & Steps
- How to Implement a Penetration Testing Program in 10 Steps
Top Penetration Testing Categories
We have grouped the tools below according to their function in a pentest exercise. Some may fall into multiple categories and there is some overlap between categories, but this list represents our assessment of the major function accomplished by each specific tool. Here are the major categories, which link to the best tools within each category.
- Best web app scanning tools: ZAP, Nikto2, W3af, WPScan
- Best password crackers: John the Ripper, Medusa, Ncrack, Rubeus
- Best pentesting frameworks: Burp, Metasploit, Fiddler
- Best wireless network scanning tools: Hashcat, Aircrack-ng, wifite
- Best exploitation tools: BeEF, SQLmap, SET
- Best sniffing tools: Ettercap, Tcpdump, Wfuzz
- Best network scanners and enumeration tools: Nmap, Wireshark, Gobuster, Amass
4 Best Web App Scanning Tools
These are open-source pentest tools used for testing the security of web-facing applications, servers, and other assets. The top four options include OWASP, Nikto2, W3af, and WPScan.
OWASP
The Open Web Application Security Project (OWASP) maintains Zed Attack Proxy (ZAP), which stands between the tester’s browser and a web application to intercept requests, modify contents, or forward packets, among other tasks.
Pros
- Actively maintained by OWASP teams
- Comprehensive and full of features, such as spider, passive and active scans, application programming interfaces (APIs), request editor, marketplace, plug-ins, and many more
- Supports multiple programming and scripting languages
- Provides graphical and command-line interfaces (CLIs) as well as good documentation
- Convenient for various levels, from beginners to security teams
Cons
- Can be harder to install and less comfortable than premium products such as the Burp Suite
- Needs additional plugins to provide some features
Nikto2
Nikto is a light web server scanner that works with command lines to identify common web flaws, such as server misconfigurations. It can be installed with Kali Linux or as a single package with the command sudo apt install nikto.
It performs tests against multiple items, including thousands of potentially dangerous files and common gateway interfaces (CGIs), and it checks for outdated versions of servers and version-specific problems on hundreds of servers. It also checks for configuration items such as the presence of multiple index files and HTTP server options and will attempt to identify installed web servers and software.
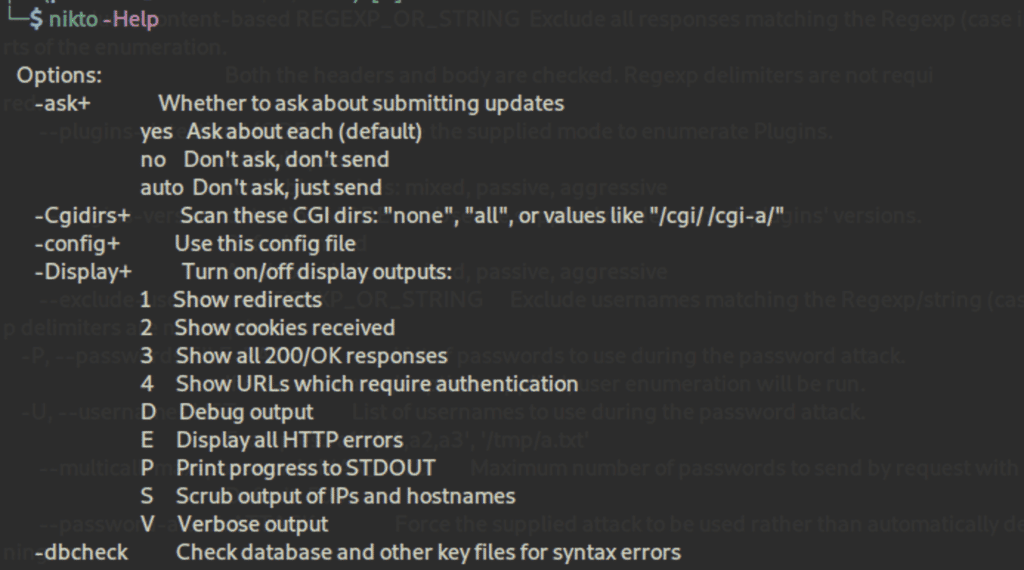
Pros
- Straightforward and covers common needs
- Can test intrusion detection systems (IDS)
- Supports files for input and output
Cons
- Beginners might get confused
- No graphical user interface (GUI)
- No known community or support
W3af
w3af, or Web Application Attack and Audit Framework, is a scanner with a framework to analyze applications and generate reports with its findings. Once the app is mapped, the tool sends crafted requests to trigger specific bugs in the code, such as SQL injections, and to report positive cases.
Pros
- Easy to learn and use
- Generates helpful reports
- Automates many tasks
- Provides a complete documentation
Cons
- The GUI can be challenging
WPScan
WPScan is a popular security tool for WordPress. It can be used with pentesting distributions like Kali Linux, with Docker, or as a binary.
A quick scan can reveal typical flaws of WordPress installations, such as the use of the XML-RPC protocol or outdated dependencies, but it can also perform brute-force attacks efficiently. Behind the scenes, the CLI tool uses the WordPress Vulnerability Database API to retrieve WordPress vulnerability data in real time.
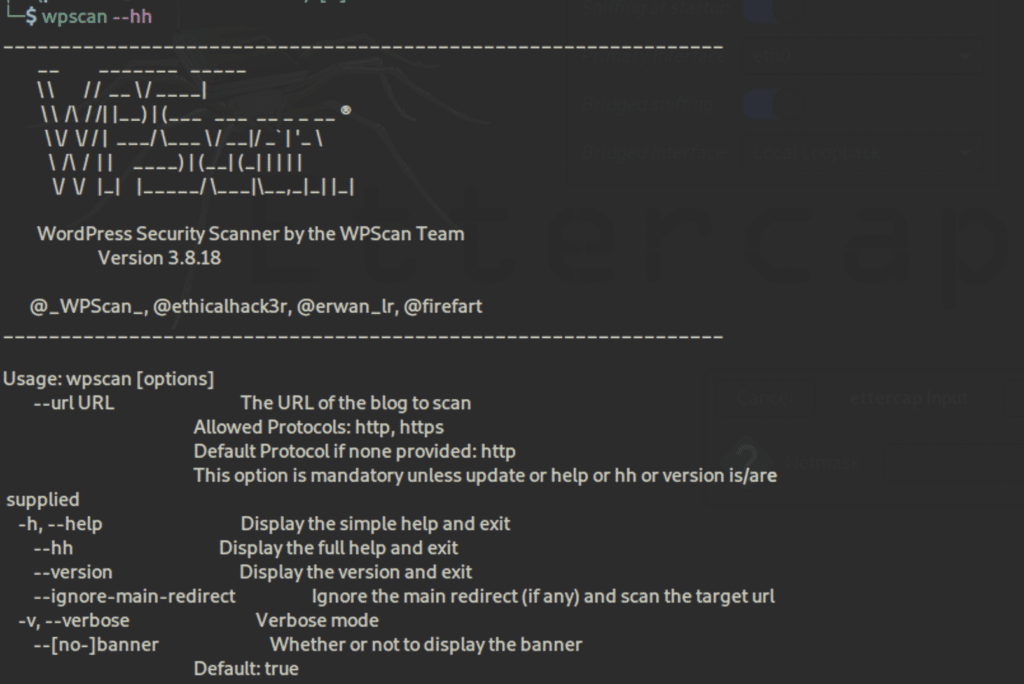
Pros
- Comprehensive with good documentation
- Entirely built for WordPress
Cons
- Free plan has limited API quotas
- A lot of prerequisites if users don’t use Kali Linux
- No GUI
Pricing Upgrades: The CLI tool is free but limited; premium small business and enterprise versions are available.
4 Best Password Crackers
Password cracking consists of retrieving passwords stored in computer systems. System administrators and security teams as well as hackers can use these tools to spot weak passwords. John the Ripper, Medusa, Ncrack, and Rubeus are the top password crackers.
John the Ripper
John the Ripper is one of the most popular free password crackers included in Kali Linux, but it also has a premium version. It combines several approaches to password cracking into one package.
It also supports hundreds of hash and cipher types, including for user passwords of Unix flavors, macOS, Windows, web apps, groupware, database servers, network traffic captures, encrypted private keys, filesystems and disks, archives, and document files.
Pros
- Supports multiple hash and cipher types
- Highly flexible configurations
- Can crack common variations such as mangling rules (e.g., Pa$$w0rd)
- Takes the best aspects of various password crackers and unites them into one package
Cons
- Can be hard to learn, set up, and configure
- Has the same privileges of the user running it, so cannot read shadow passwords
- Only penetrates passwords, nothing else
To learn how to use John the Ripper and hear more about its pros and cons, read John the Ripper: Password Cracking Tutorial and Review.
Medusa
Medusa is a powerful brute-force tool with interesting features included in Kali Linux. This command-line tool can also be installed as a Linux package using the command sudo apt install medusa.
Pros
- Easy to learn and use
- Fast and concurrent
- Supports thread-based parallel testing like simultaneous brute-force attacks
- Offers the ability to resume an interrupted Medusa scan
- Can be extended easily
Cons
- Supports fewer operating systems and platforms than other tools
- Lack of documentation
Ncrack
Ncrack, which is included in Kali Linux, can test all hosts and devices in a network for weak passwords. It’s a set of command lines that can scan large networks, allowing sophisticated brute-force attacks.
Pros
- Light yet powerful
- One of the most widely used by professionals
- Can be easily used along with Nmap and is maintained by the same creators
- Can save output in files
- Can resume an interrupted attackers with the –resume option
- Can attack multiple hosts
Cons
- No graphical interface
Rubeus
Rubeus is a C# toolset for raw Kerberos interaction and abuses. It is open-source and licensed under the BSD 3-Clause license.
It is especially aimed at ever-more popular Kerberos use cases, which is a ticket-based network authentication protocol used in Active Directory (AD) that is commonly misconfigured. Rubeus exploits the resulting vulnerabilities and performs functions such as crafting keys and granting access using forged certificates.
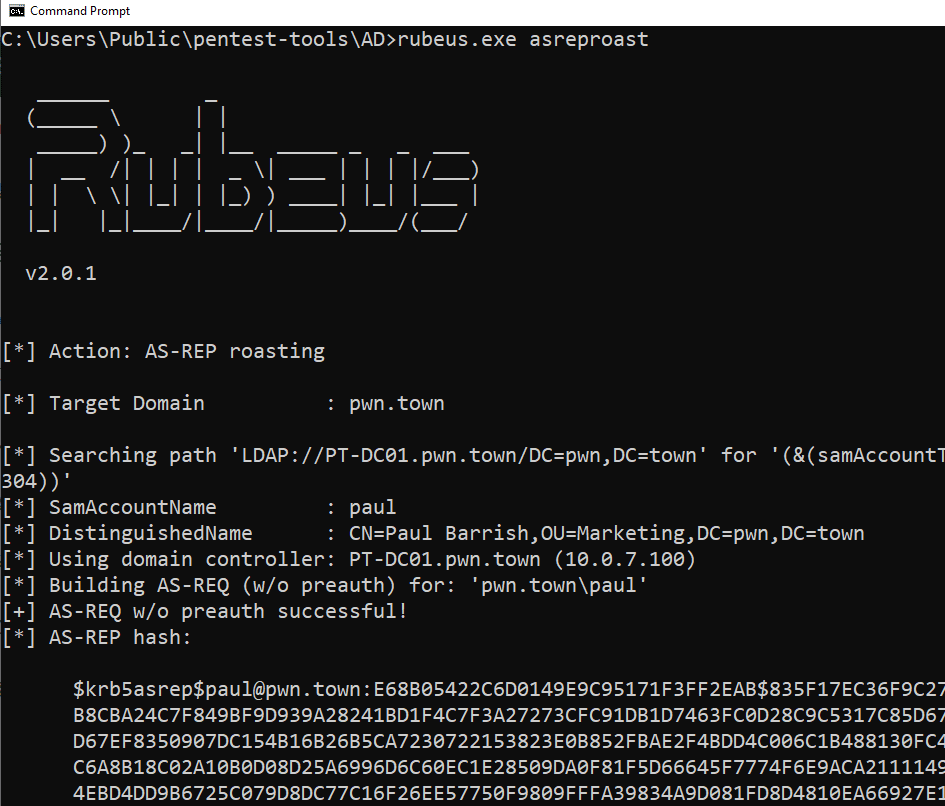
Pros
- Good for Kerberos flaws
- Includes modifications to Rubeus’ approach to Kerberoasting
- Versatile and dropped on the victim’s machine to perform various AD-related attacks
Cons
- Can be detected in a number of methods, either from the host, network, or domain perspectives
- Can be caught during initial weaponization of the code itself through the use of sensitive APIs
For an explanation on how to test your organization’s security services using Rubeus and other pentesting tools, read Testing & Evaluating SIEM Systems: A Review of Rapid7 InsightIDR.
3 Best Pentesting Frameworks
Pentesting frameworks are collections of security tools that can be used to run penetration tests. The best ones, including the Burp Suite, Metasploit, and Fiddler, cover both scanning and exploits.
The Burp Suite
Burp is a top-rated software suite for attacking that can be found in the Kali Linux community edition. It’s a tremendous tool in the pentesting arsenal that can do advanced scans, but one of the most classic uses is traffic interception, such as for HTTP requests.
The web vulnerability scanner within Burp Suite uses research from PortSwigger to help users find a wide range of vulnerabilities in web applications automatically. Burp Scanners crawl engine cuts through obstacles like CSRF tokens, stateful functionality, and overloaded or volatile URLs. It can handle dynamic content, unstable internet connections, API definitions, and web applications.
Pros
- Used by most security teams, researchers, and professionals as well as attackers
- Comprehensive
- Easy to use and configure
- Its embedded Chromium browser renders and crawls JavaScript
- A crawling algorithm builds up a profile of its target in a similar way to a tester
- Uses location fingerprinting techniques to identify hidden areas
Cons
- Harder to learn and master than other scanners
- Many features aren’t available in the community edition (free), and the enterprise edition is relatively expensive
- An all-in-one solution with tons of features that won’t be used by many businesses
- As it tries to be everything, it should be viewed as primarily a vulnerability scanner with some penetration tools that attack the exploits it uncovers. But it should be used in conjunction with other pentesting tools
Pricing Upgrades: In addition to the free community tools, PortSwigger offers pro and enterprise versions of Burp.
Metasploit
Metasploit, developed by Rapid7, is a well-known exploitation framework that’s also included in Kali Linux. It provides useful modules and scanners to exploit vulnerabilities.
With this modular exploitation approach, a particular vulnerability can be combined with a user-selected payload module and an automatically selected encoder module. Upon success, the user can adapt and customize their workflow by using one of the many post-exploitation modules provided by Metasploit Framework.
Further, Metasploit is backed by a huge open-source database of known exploits, and provides IT with an analysis of pentesting results, so remediation steps can be done efficiently.
Pros
- Used by most security teams, researchers, and professionals as well as attackers
- Comprehensive
- Convenient to emulate compromised machines
- Users can create infected payloads with a graphical interface with the payloads GUI or in the pro version
- Can be easily combined with Nmap
- Includes post-exploitation tools such as keyloggers, packets sniffers, or persistent backdoors
- Tests can be automated
- Everything is unified to provide a seamless experience for the user, particularly when compared with stand-alone public proof-of-concept code
- With an established Meterpreter or Secure Shell (SSH) session, users can send all traffic through one or more sessions depending on their Metasploit-global routing configuration
Cons
- It makes hacking a lot easier, including for beginners and script kiddies
- Paid versions are expensive
- Can be challenging to use at first
- May occasionally have scaling challenges in very large environments
Pricing Upgrades: In addition to the open-source framework, Rapid7 also offers a professional version.
Fiddler
Fiddler is a useful collection of manual tools for dealing with web debugging, web session manipulation, and security and performance testing. This includes:
- Watcher to observe browser interactions with a website, scan requests and responses, and flag potential vulnerabilities
- x5s to evaluate website vulnerabilities due to cross-site scripting bugs caused by character-set related issues
- intruder21 for fuzz testing of web applications, generating fuzzed payloads and launching them against a website
- Ammonite, which detects common website vulnerabilities including SQL injection, OS command injection, cross-site scripting, file inclusion, and buffer overflows
Pros
- Good web debugging proxy
- Can automate SSL decryption
- Users can choose to either decrypt all processes, only browser traffic, only non-browser traffic or remote clients
Cons
- Not designed to be a pentest tool but helps to scan for vulnerabilities
- Probably most useful for those deploying the paid version on the .NET framework, as that comes with many automation features
Pricing Upgrades: While Fiddler is free, a paid version by Telerik can be integrated into .NET applications.
3 Best Wireless Network Scanning Tools
Wireless network scanning tools test the security of wireless networks by cracking network passwords and testing the strength of encryption protocols. The top wireless network scanning platforms are Hashcat, Aircrack-ng, and wifite.
Hashcat
Hashcat provides advanced password recovery features and lets testers crack Wi-Fi passwords or password-protected documents such as ZIP files. It’s already included in Kali Linux, but users can install it as a package using the command sudo apt install hashcat.
Pros
- A typical hacker’s tool
- Not limited to brute-force attacks
Cons
- No GUI, but there are third-party integrations
- Requires relatively advanced technical knowledge
Aircrack-ng
Aircrack-ng is the go-to tool for analyzing and cracking wireless networks. All of the various tools within it use a command-line interface and are set up for scripting. Aircrack-ng’s main focuses include:
- Packet capture and export of data to text files for further processing by third-party tools
- Replay attacks, de-authentication, fake access points, and others via packet injection
- Check Wi-Fi cards and driver capabilities (capture and injection)
- Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access Pre-Shared Key (WPA-PSK) for WPA and WPA2 cracking
Pentesters can use it to attack and crack the WPA and WEP protocols. It is open-source and available from SecTools.
Pros
- Good tool for 802.11 wireless local area networks (LANs) to to sniff wireless packets, intercept them, and log traffic passing through, as well as manage wireless drivers and recover lost keys
- Has been extended beyond Linux to include Windows, OS X, FreeBSD, OpenBSD, NetBSD, Solaris, and eComStation 2
Cons
- Cannot monitor or conduct pentesting on non-wireless networks
wifite
Wifite is a wireless network auditor that deals with current or legacy attacks against WEP and WPA2. It can be used as an automated wireless attack tool.
Pros
- Good for retrieving the password of a wireless access point such as a router
Cons
- Mainly designed for use with pentesting distributions of Linux
- Wifite must be run as root by the suite of programs it uses
- Difficult to run downloaded scripts
3 Best Exploitation Tools
Exploitation tools can test everything from user susceptibility to phishing and spoofing to application and database security. BeEF, SQLmap, and SET are the most useful exploitation tools available.
BeEF
As many apps are web-based, adversaries use browser exploitation. BeEF, or Browser Exploitation Framework, makes classic tasks such as enumeration, phishing, or social engineering seamless.
This software provides testers a user-friendly GUI and practical client-side attack vectors to target different contexts and achieve various tasks, such as stealing credentials. BeEF also offers a user guide for anyone with questions from basic utilization to development.
Users can find it in Kali Linux, but it can also be installed as a package using the command sudo apt install beef-xss.

Pros
- Full of advanced features, such as fake password manager logins and redirect with iFrames
- Clever interface to visualize everything from the victim’s browser to the attacker’s logs
- Particularly convenient for demonstrations
- Provides prebuilt web pages for various traps such as fake login forms
- Can bypass a victim’s firewall
- Provides a comprehensive network module, such as for host discovery
Cons
- Basic phishing modules will perform poorly with cybersecurity-aware employees
SQLmap
SQLmap is included in Kali Linux, but it can also be installed from the GitHub repository. It automates the process of detecting and exploiting SQL injection flaws and database server takeovers.
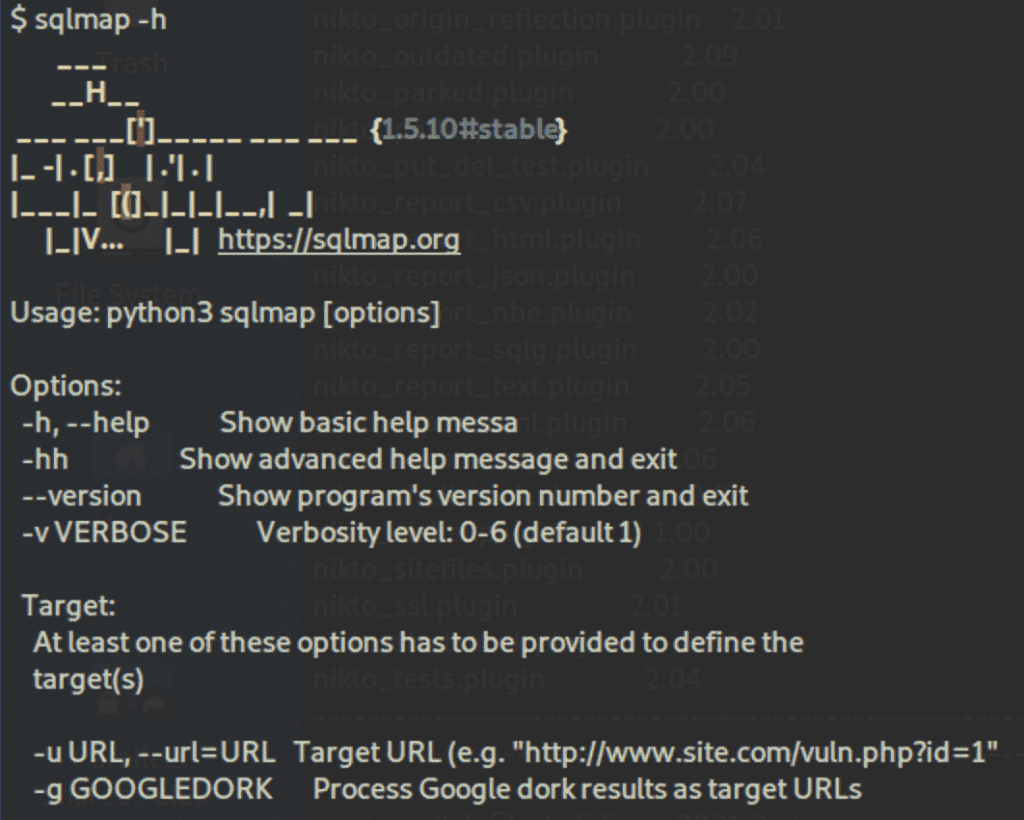
Pros
- Can detect various types of SQL injections
- Supports an extensive range of databases
- Provides advanced features, especially for search and enumeration
Cons
- No GUI; it’s CLI-only, but there are third-party integrations
SET
SET, or Social Engineer Toolkit, focuses on the human factor, as scanners won’t do social engineering pentests. Users will be able to create payloads, phishing pages like Google login, and other web attacks.
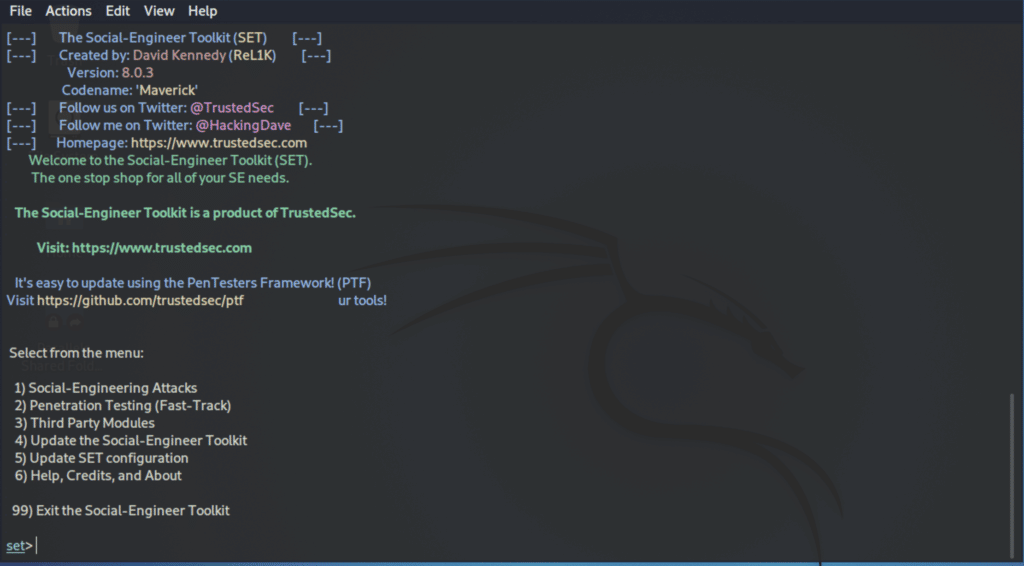
Pros
- The sets of command lines, used in place of a GUI, has a nice format
- Comprehensive
- Straightforward but powerful
Cons
- Based on human mistakes, which is often the weakest link, but some attacks don’t need this step
3 Best Sniffing Tools
Packet sniffers can analyze and intercept network traffic to steal data and passwords and launch man-in-the-middle attacks. When searching for a top sniffing tool, consider Ettercap, Tcpdump, and Wfuzz.
Ettercap
Ettercap is a packet sniffer that allows users to modify data on the fly and run man-in-the-middle (MITM) attacks. A common usage is to intercept passwords with ARP (Address Resolution Protocol) poisoning or spoofing, which attackers place between the victim and router to divert the traffic.
Ettercap can be used with Kali Linux or installed as a stand-alone software on a pen-testing distribution using the command sudo apt install ettercap-common.
Pros
- A typical hacker’s tool
- Will put security systems such as EDR (endpoint detection and response) to the test
- GUI and command lines
Cons
- Users need to be already inside the network to run the attack
- The interface could be more polished
- Can be hard to learn and master
Tcpdump
Tcpdump is a powerful command-line packet analyzer developed by the same people as libpcap, a portable C/C++ library for network traffic capture. It prints out a description of the contents of packets on a network interface, preceded by a timestamp.
Pros
- Can save packet data to a file for later analysis
- Reads from a saved packet file rather than reading packets from a network interface
- Can read a list of saved packet files
Cons
- Command line only
- Can impact performance at times
Wfuzz
Wfuzz is helpful to run brute-force attacks on various elements such as directories, scripts, or forms. Like many other tools in our list, it can be found in Kali Linux, but users can run it with the command sudo apt install wfuzz.
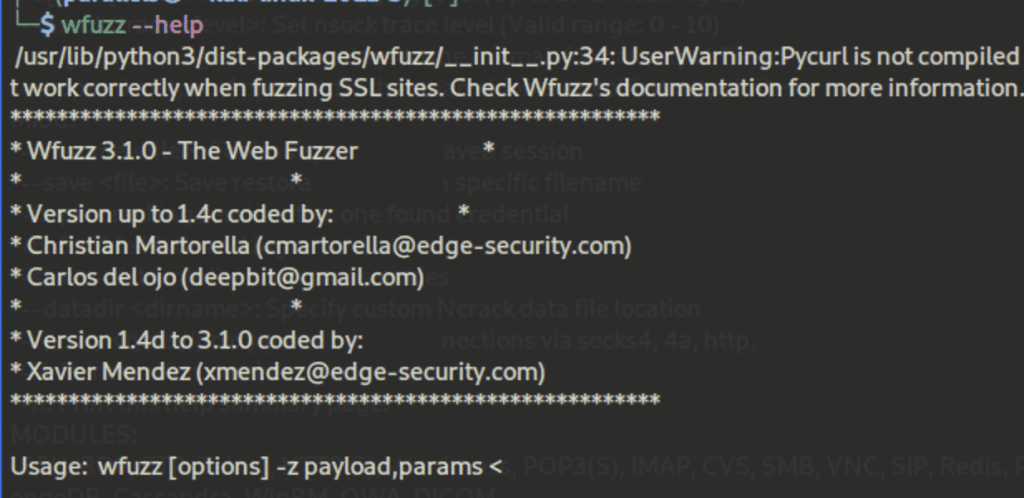
Pros
- Accepts wordlists
- Allows customized configurations
- Documented
Cons
- Significantly slower than other options
- Requires more central processing unit (CPU) power and random access memory (RAM)
4 Best Network Scanning and Enumeration Tools
Network scanning and enumeration tools probe networks and traffic for weaknesses and vulnerabilities. Nmap Free Security Scanner, Wireshark, Gobuster Directory Scanner, and Gobuster Directory Scanner are leading network scanning and enumeration tools.
Nmap Free Security Scanner
Nmap, included in Kali Linux and also available via nmap.org, is a free package of command lines that can be run in a terminal to achieve various tasks, such as discovering open ports, which allows users to detect vulnerabilities. This tool is helpful for scanning large networks fast.
Behind the scenes, Nmap uses raw IP packets to identify available hosts and services on the network. As well as a port scanner, it aids pentesting by flagging the best areas to target in an attack, which is useful for ethical hackers in determining network weaknesses.
Pros
- A comprehensive, free, and open-source solution
- Can be combined with a GUI such as Zenmap
- Full of advanced networking features
- Accepts custom scripts
- Can scale to scan huge networks but can also be deployed against single hosts
Cons
- Can be hard to configure and master, especially for those not familiar with Linux; however, it does run on other OSes
- The extensive range of commands and options can overwhelming
- Detection tools will likely spot and log Nmap scans
- Although Nmap is a scanner, it doesn’t probe for and penetrate vulnerabilities though it does point out where weaknesses might lie
Wireshark
Wireshark is probably the most popular network protocol analyzer. It’s a packer scanner, or sniffer, that can be found in Kali Linux, but users can also install it as a stand-alone software or package in most operating systems.
Wireshark is often used to point out what is happening with the network and to assess traffic for vulnerabilities in real time. By reviewing connection-level information as well and the constituents of data packets, it highlights their characteristics, origin, destination, and more.
Pros
- Rich interface with lots of panels and removable tabs
- Can see the finest details
- Assesses traffic vulnerabilities in real time
- Can be used to assess wireless networks
- Runs on Windows, Linux, Mac, and most other OSes
- Output can be exported to XML, PostScript, CSV, or plain text
Cons
- Harder to learn and master than other mappers
- Captures all requests on the network, so you have to know how to fine-tune it and use filters
- While it flags potential weaknesses, a pentesting tool is still required to exploit them
Gobuster Directory Scanner
Gobuster can be used with Kali Linux, but users can also install it as a package using the command sudo apt install gobuster. It is efficient software that can be used to enumerate hidden directories and files quickly.
Many web apps use default directories and filenames that are relatively easy to spot. As a result, the tool can use brute-force techniques to discover them.
Pros
- Accepts Wordlists and additional packages via the command sudo apt install seclists
- Can extract lots of information such as directories, subdomains, and virtual hosts
- Able to hide status and process such as with proxies and user agents
- Spots backup and configuration files
- Can save output results in files
Cons
- Some Gobuster modules have limited options
- Robust installations will likely make enumeration more difficult or perhaps block it
Amass
Amass is an open-source network mapper that is particularly efficient for DNS (Domain Name System) and subdomain enumeration.
Pros
- Actively maintained and updated to keep up with the latest techniques and methodologies
- Backed by OWASP
- Good documentation
- Combines various reconnaissance and gathering techniques
- Similar features as Nmap, even on the scripting language
Cons
- While the commands are straightforward, analyzing the data will be hard for beginners
Featured Endpoint Detection and Response (EDR) Software
Other Penetration Testing Technologies
There are a number of complementary technologies often used by organizations to address security holes. Breach and attack simulation, for example, can be something of an automated, continuous pentesting tool. Others include vulnerability scanning tools and vulnerability management solutions. And IT asset management and patch management are important tools for staying on top of known vulnerabilities.
Cyber criminals are constantly adjusting their tactics to maximize effectiveness. Hence, penetration testing is an evolving field. Here are some of the top trends, defenses and tactics to keep in mind:
- Testing the external attack surface is necessary, as more assets are exposed to the internet and are regularly changing.
- Greater test frequency is needed to align with software development sprints.
- Penetration testing as a service (PTaas) provides integration with organizational defect tracking systems and can programmatically submit vulnerabilities to be tracked and remediated through the development team’s defect tracking system.
- DevOps also needs to perform pentesting, as development and security have become intertwined.
- Automation should be used where possible to close the security gap and speed up the remediation process.
- Testing the supply chain is a necessary response to breaches such as SolarWinds and Kaseya.
Bottom Line: Open-Source Penetration Testing Tools
Penetration testing is a critically important practice for keeping networks safe from intruders. While there are some comprehensive paid offerings, many pentesting teams prefer the widely used open-source tools that they’re already familiar with. With a wide range of open-source tools to choose from, pentesters can accomplish comprehensive testing of their environments by using a number of free tools. But whether you use open-source tools, commercial tools, or even third-party services, pentesting is something every organization with a network needs to do regularly.
Also read:
- 10 Best Open-Source Vulnerability Scanners for 2023
- Nmap Vulnerability Scanning Made Easy: Tutorial
- Getting Started with the Burp Suite: A Pentesting Tutorial
- Getting Started With the Metasploit Framework: A Pentesting Tutorial
This updates a February 2022 article by Julien Maury.











