Do you make online financial transactions from a Windows computer? If so, you may want to re-visit that decision.
It’s a given that almost all malicious software targets Windows. In my opinion, while it is possible to secure a Windows computer, the process is too hard, too time-consuming and/or technically over the head of most people.
A recent article at WashingtonPost.com described multiple organizations whose bank accounts were emptied by malicious software on their Windows computers. In one case, the Clampi Trojan sat undetected for a year on the computer of the Controller of a small business, before it decided to make withdrawals from their bank account.
According to recent news reports, “Fraudsters are taking advantage of the widely used but obscure Automated Clearing House (ACH) Network in order to pull off their attacks.” Businesses don’t have the same safeguards as consumers from this type of theft. Both articles describe serious losses and lawsuits.
In response to this, I wrote Defending against the Clampi Trojan, which applies to all Windows based malicious software (malware). In short, the advice boils down to this:
- ? Installing and maintaining one or two anti-malware programs that run constantly in the background.
- ? Periodically scanning with a few other anti-malware programs.
- ? Be sceptical of allemail attachments and don’t trust the FROM address of an email message when deciding whether to trust an attachment.
- ? Consider opening email attachments with alternative applications rather than the more mainstream software that is a larger target. For example, use Open Office rather than Microsoft Office or the Foxit PDF Reader rather than the Adobe Reader.
- ? Periodically run the Secunia online scanner to insure that you are up to date on bug fixes to Windows and the most popular software.
- ? Turn off autorun.
- ? Windows XP users should use DropMyRights to defend against drive by downloads.
- ? All Windows users should consider using Sandboxie for defending against drive-by downloads.
Is this more time and effort than you have available? Is the technical know-how necessary to carry out all these steps above you?
Here’s a test of technical competence. Try to run the Secunia Online Software Inspector. It’s a Java applet and requires Java version 6. If you have an old version of Java, don’t know what version of Java you have or can’t get Java version 6 installed, then you fail.
If the scan runs but finds out of date, vulnerable buggy software installed on the computer, you also fail. For extra credit, try to get a perfect score with the “thorough system inspection” option turned on.
I suspect that a large percentage of Windows users will fail. Anyone who fails should not do online financial transactions on a Windows machine. Consider instead, Macs and Linux, my preference being Linux.
Swimming offers an analogy
Windows is like an ocean full of sharks. Do you really want to swim where the sharks swim, even if you take some defensive measures? Macs are like a swimming pool, no sharks. But, the Mac pool is deep and often neglected. Linux also offers a swimming pool, but it’s shallower and better maintained (more later) than the Mac pool.
According to a recent blog posting by Graham Cluley of Sophos, AV-Test.org is detecting more than a million unique malware samples a month. That’s a lot of sharks.
Another factor to consider is that really malicious software hides and hides well. If a Windows user thinks their computer is infected because it’s acting strangely, then they’re in luck, the infection is not particularly sophisticated. It’s when nothing appears to be wrong that you may be most at risk. Software that wants a Citibank password from you is not going to announce its presence.
The sophisticated hiding techniques were a big reason behind my recent series of Best Way to Remove Viruses articles that focused on booting from a CD and scanning for malware from outside the suspect/infected system.
Add-ons
Then too, there is Internet Explorer itself. Rather than being a single entity, IE is a collective. Under the covers, Internet Explorer houses ActiveX controls, Browser Helper Objects, Toolbars and Browser extensions; each is a different mechanism for software to insert itself inside the web browser.
To see the software that hides in IE7 do Tools -> Manage Add-ons -> Enable or Disable Add-ons. Then explore each of the four categories of Add-ons. To see the extra software running inside IE8, do Tools -> Manage Add-ons, click on Toolbars and Extensions (on the left), then be sure show all add-ons (the drop-down box). When you do online banking with Internet Explorer you are trusting all this software.
The good news is that you can force IE7 and IE8 to run without any add-ons. In Windows XP, click on Start -> Programs -> Accessories -> System Tools -> Internet Explorer (No Add-ons). Better yet, make a shortcut for it.
Firefox also has extensions and can also be forced to disable them for a single session. Windows users should find a “Mozilla Firefox (Safe Mode)” entry in the list of installed software under the heading “Mozilla Firefox.”
A browser without any extra internal add-on software is a big step forward for security, but, in my opinion it’s not sufficient. You’re still swimming with sharks.
Alternative Operating Systems
In discussing his research on the Clampi Trojan Joe Stewart of SecureWorks concluded that “Businesses may even consider using an alternative operating system for workstations accessing sensitive or financial accounts.”
Bingo. For whatever reason, he didn’t suggest this for consumers. I do.
Macs are safer than Windows in part because they are a lesser target (thanks to fewer users) and in part because OS X derives from Unix/Linux. But Macs are expensive and Apple’s record on security issues is spotty.
Blogging at Computerworld, Preston Gralla has pointed this out a number of times recently:
- ?Mac OS X Java fiasco: Apple still doesn’t get security
- ?Researchers: Macs are less secure than Windows PCs
- ?Security pro: Five ways Apple fails on security
- ?Four things Apple can learn from Microsoft about security?
I think it’s fair to call Gralla a Windows guy, but that doesn’t make him wrong. Rob Enderle also asked if Apple security was an oxymoron.
This leaves Linux. Linux isn’t perfect either, but when it comes to online banking, running Firefox under Linux is, I think, the safest approach.
Linux is a lesser target than Macs (again, fewer users), free and amazingly flexible. A Windows user who has never seen either OS X or Linux before will probably have an easier time adapting to Linux than they will to OS X.
When I earlier called Linux a better maintained swimming pool, I was referring to the fact that the Linux self-update application updates all the installed software, something that Apple and Microsoft don’t do.
Wubi
Perhaps the easiest way for Windows users to run Linux is offered by Wubi, which lets you install Ubuntu and some other distributions under Windows. The installation is done within Windows. There is no Linux lingo to learn and no partitions to contend with. After Linux is installed, it appears in the Control Panel Add/Remove list of programs from where it can be easily removed. The entire Linux operating system appears to Windows as a single big file.
Wubi works like Apple’s Boot Camp. When the computer starts up, you chose which operating system to run. At any given time, the computer is running one OS or the other. Switching between them requires rebooting.
I’ve used Wubi a few times with mixed success. However, even when things went poorly, the un-install of Linux was perfect, so there is not much downside to trying it.
Virtual machines are another way to run Linux on a Windows machine, but VMs are complicated and complexity is always the enemy of security.
Linux Live CDs
A safe, simple way to run Linux is to put it on a CD and boot from it. Malware can’t be installed and passwords can’t be saved (to be stolen later). The operating system remains the same, usage after usage after usage. Also, there is no need to have a dedicated computer for either online banking or Linux. The total cost is that of a blank CD, mere pennies.
Firefox running on a read-only medium, such as a CD, is the safest approach to online banking.
There are a couple downsides, however. For one, running software off a CD is much slower than running it off a hard drive. And, from time to time, you’ll need to download and burn another Linux CD to pick up updates to both Firefox and the operating system.
Running Linux off a USB Flash Drive
But many distributions of Linux have another trick up their sleeve – they can also run from a USB flash drive.
Software running off a flash drive should be faster than running off a CD, and a flash drive is even more portable. USB flash drives also open up netbooks as potential hosts for your favorite Linux distribution.
There are a number of utilities that create bootable editions of Linux on a USB flash drive. When running such a utility you may be given a choice. One option is for Linux to logically treat the USB flash drive as a CD, that is, to make it read-only. This is not a hardware thing, you can still modify the flash drive when Linux is not running off it.
The other option is to let Linux save files on the flash drive. The upside is that you can save bookmarks and install bug fixes to the operating system and Firefox, avoiding the need to periodically burn a new CD. The downside is that malware can potentially save itself too. Then again, there isn’t much (any?) malware that runs on Linux.
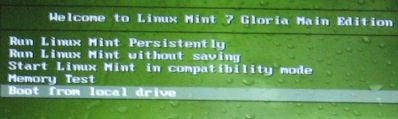
Mint offers the best of both worlds. When run from a USB flash drive, it offers options to run “persistently” or “without saving.” For online banking, run without saving. Then periodically, run in persistent mode to install bug fixes.
If you like the idea of booting Linux from a USB flash drive, a 4GB model should be more than sufficient to run any of the popular distributions. When shopping for USB flash drives, be aware that there is a large difference in speed among various USB drives.
For example, OCZ offers three classes or gradations which they call “extreme performance,” “performance” and “ultra-portable.” Their Diesel and CrossOver models are ultra-portable and the specs say nothing about speed. The ATV and Rally2 models are in the “performance” class but again, the specs omit speed ratings. Only the top of the line Turbo models have specs that lay out the read/write speeds. According to a Tom’s Guide review the OCZ Rally 2 Turbo was indeed speedy.
The same is true at Crucial, which offers three different 4GB USB flash drives. The specs for the $19 Gizmo has no speeds. The specs for the $39 Gizmo! Plus does have speed ratings. And the specs for the $58 Lexar JumpDrive Lightning show even faster speeds.
To evaluate other brands, Nirsoft has user contributed speed tests of many 4GB flash drives.
Regardless of the media (CD or USB flash drive), if you run a bootable copy of Linux on a machine with another operating system installed, then Linux may or may not see the files on the internal hard drive. This depends on a number of factors such as the version of Linux and the file system on the hard drive.
You’re safer going online with a copy of Linux that sees only its own files, not also those of another operating system. Malicious software or web sites can’t read or copy files that the operating system doesn’t even see. If your favorite Linux distribution defaults to making the internal hard drive visible, it should be a simple matter to dis-mount the volume (in Linux lingo) that is the internal hard drive.
Finally, be sure to change the password on your router. A router configured to use malicious DNS servers is the only thing that can defeat all this work.
ALSO SEE: The GNU/Linux Desktop: Nine Myths
















